research note
Moravec's Paradox: Towards an Auditory Turing Test
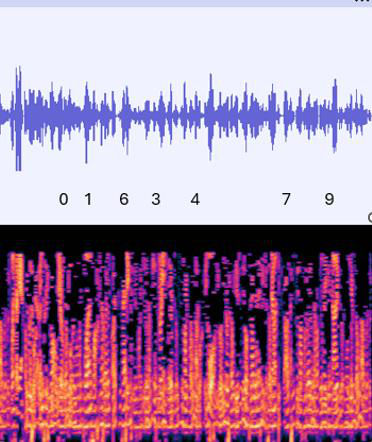
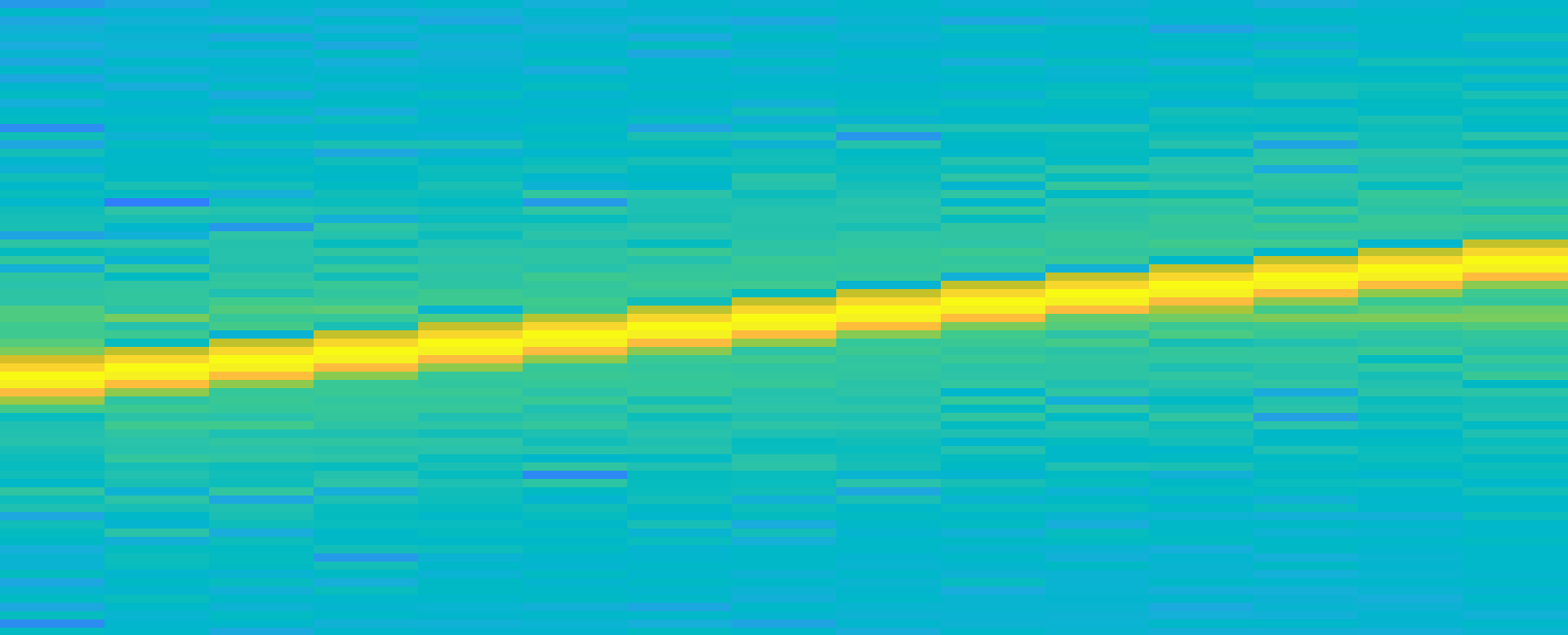
This paper investigates a fundamental and longstanding challenge in AI known as Moravec's paradox, specifically within the domain of auditory perception
research note
This paper investigates a fundamental and longstanding challenge in AI known as Moravec's paradox, specifically within the domain of auditory perception
research note
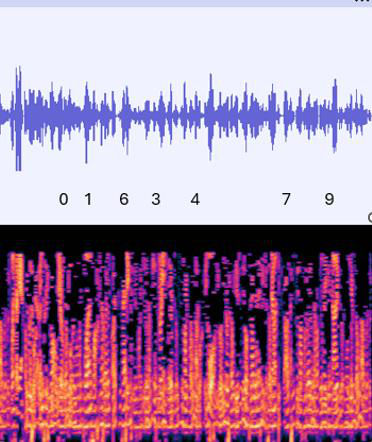
The paper asks whether phishing generation can be pushed beyond static, prompt-based output by treating attack design as an evolutionary process

research note
This paper tackles a practical but underexplored anti-cheating problem: detecting LLM-assisted writing in Korean from typing behavior rather than submitted text

research note
SynPAIN tackles a very specific but important data problem in automated pain assessment: most public facial-pain datasets are small, skew younger, and underrepresent the older adults and demographi…
research note
Vec2Face+ is a synthetic face-dataset generation method aimed at face recognition training, with the central claim that the remaining gap between synthetic and real training data is not just about …
research note
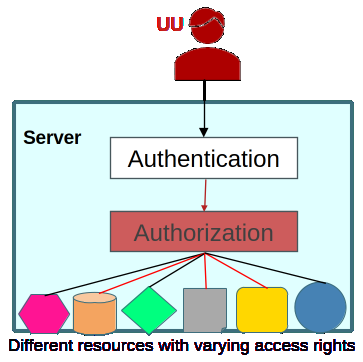
MFAz tackles a gap that standard access control and MFA do not address: once a session is already established, an attacker who steals or reuses the session identifier can often bypass the original …

research note
This paper studies whether the abstract facial-motion streams produced by mixed-reality headsets are privacy-sensitive behavioral biometrics, even when no raw video is exposed
research note
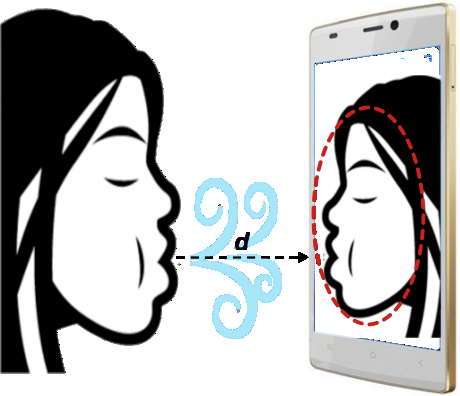
BlowPrint tackles a pretty specific but practical problem in smartphone authentication: can a behavioral signal that is contactless, quick to perform, and hard to spoof be paired with a standard ph…
research note
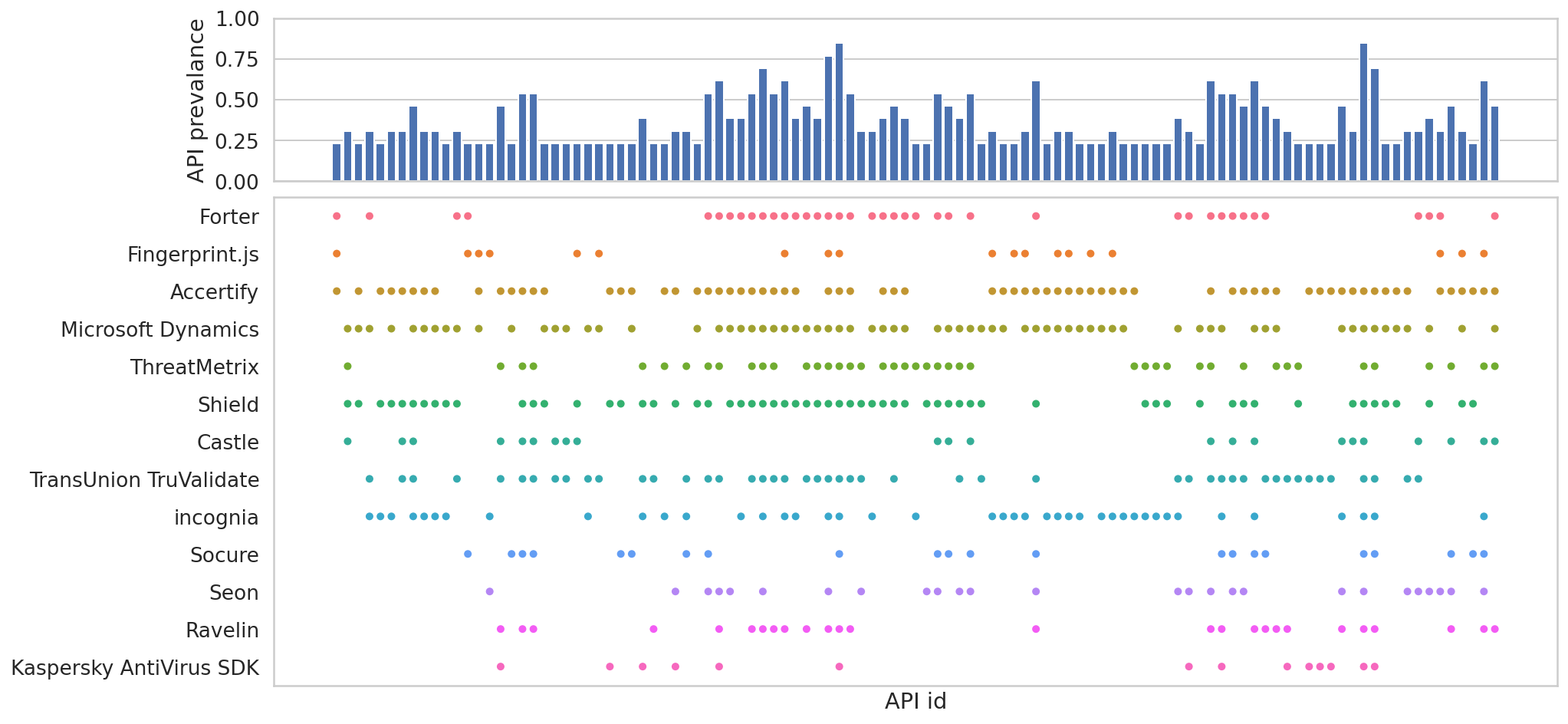
This paper addresses the pervasive practice of device fingerprinting in the mobile app ecosystem, focusing on the role of third-party SDKs embedded in Android apps

research note
SafeTriage tackles a very specific privacy bottleneck in clinical AI: how to share and reuse facial video from suspected stroke patients without exposing identity, while still preserving the subtle…
research note
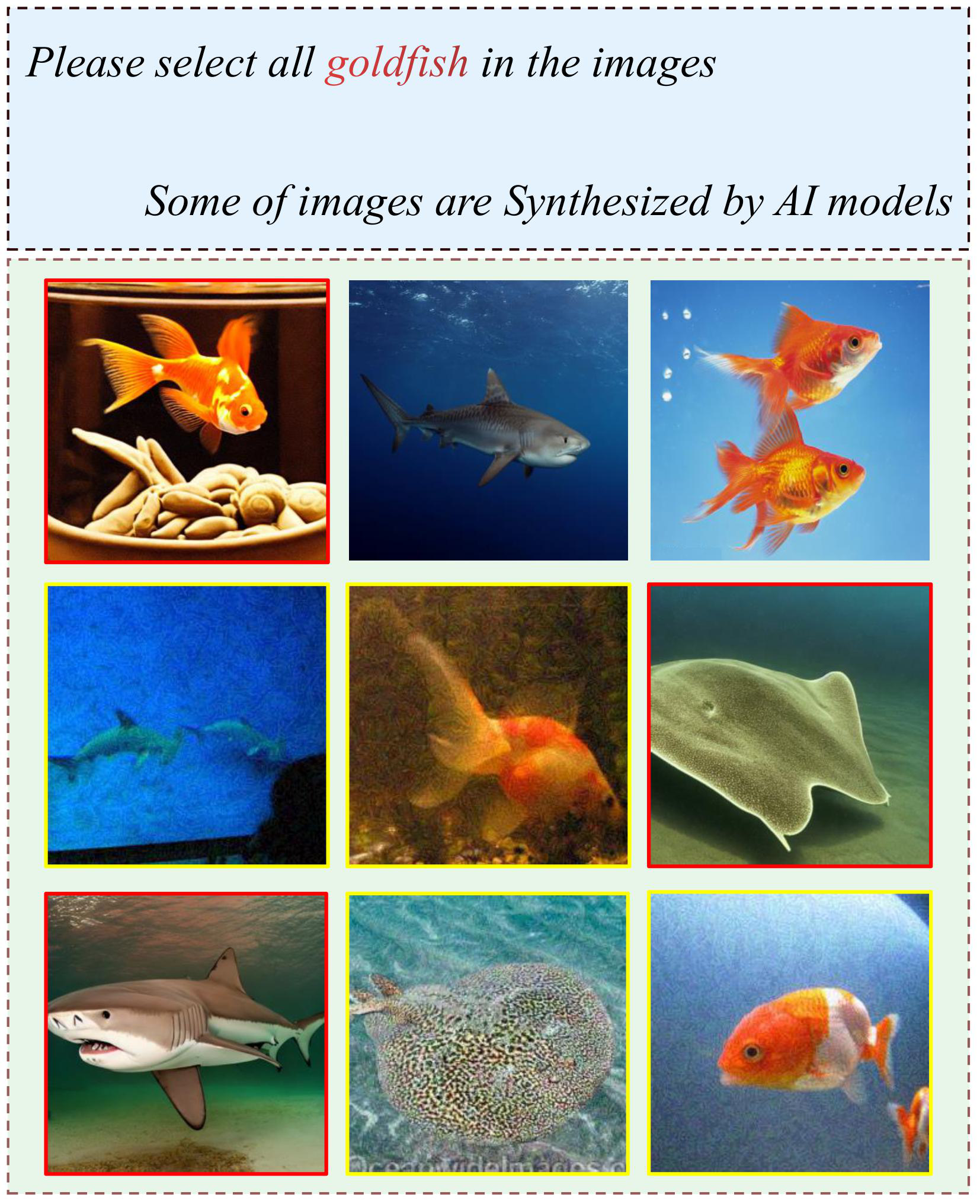
This paper addresses the growing vulnerability of traditional CAPTCHA systems to automated attacks leveraging deep neural networks (DNNs)
research note
This paper addresses the problem of secure device authentication in wireless communications, particularly for resource-constrained Internet of Things (IoT) devices where traditional cryptographic m…