research note
Pain in 3D: Generating Controllable Synthetic Faces for Automated Pain Assessment
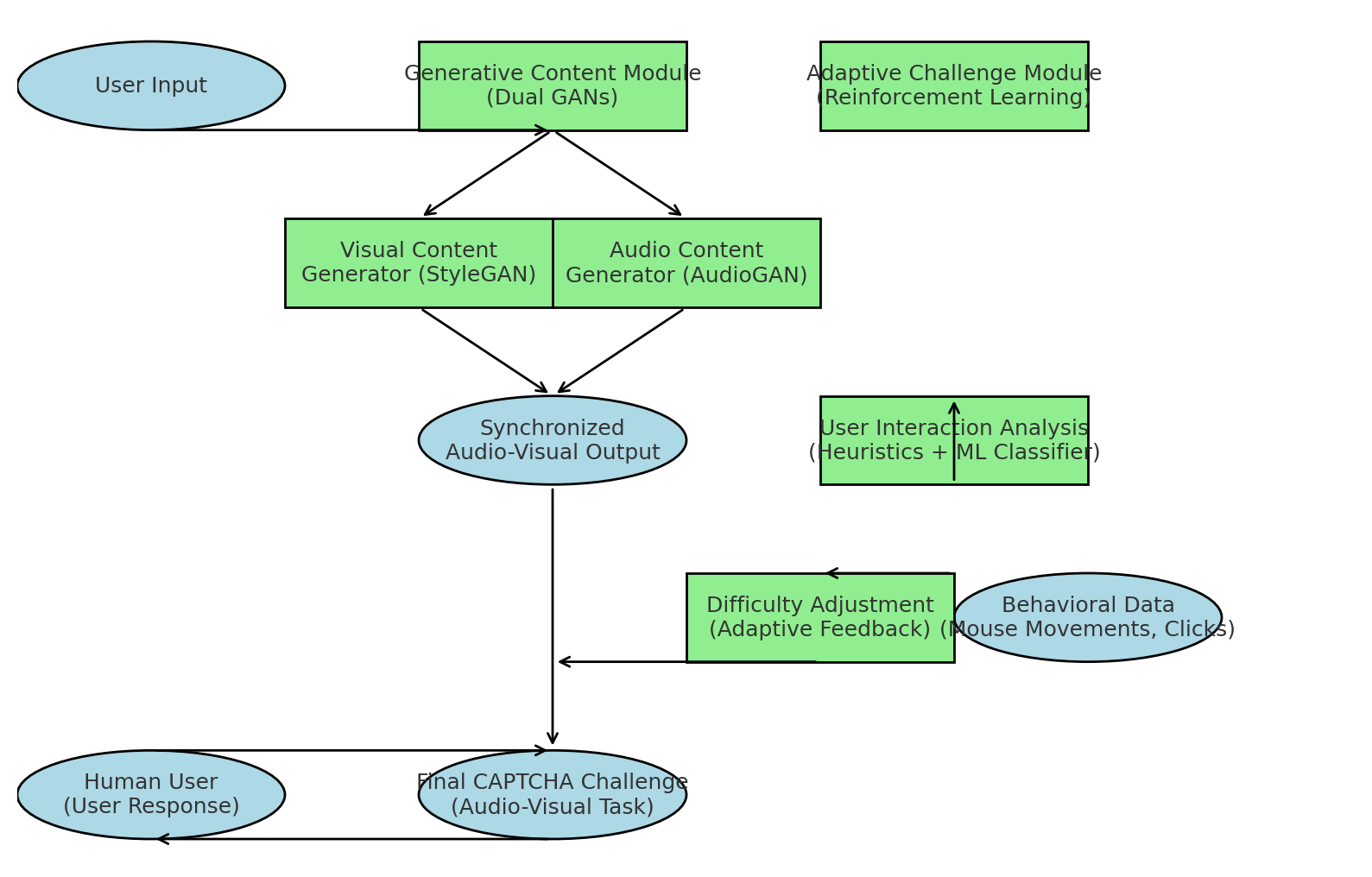
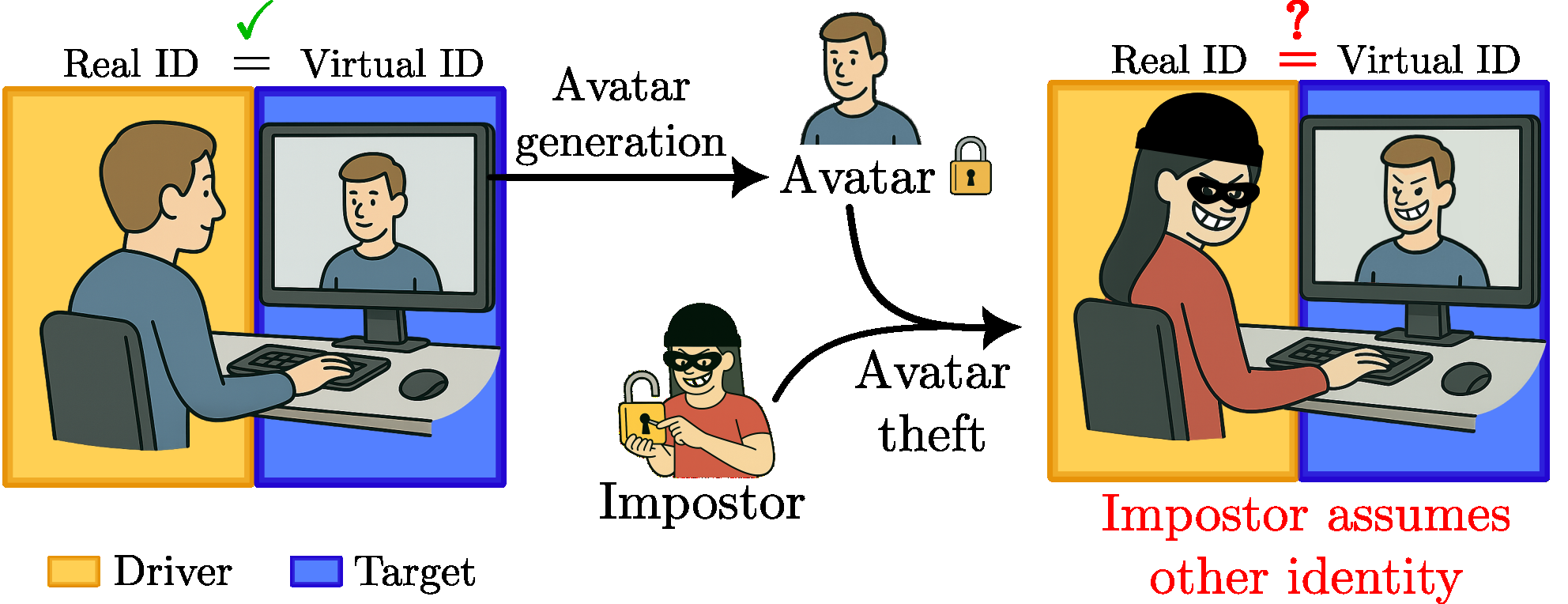
This paper tackles a very practical bottleneck in automated pain assessment: there are too few diverse, high-pain facial examples to train models that generalize beyond a small set of subjects and …