research note
FATe of Bots: Ethical Considerations of Social Bot Detection
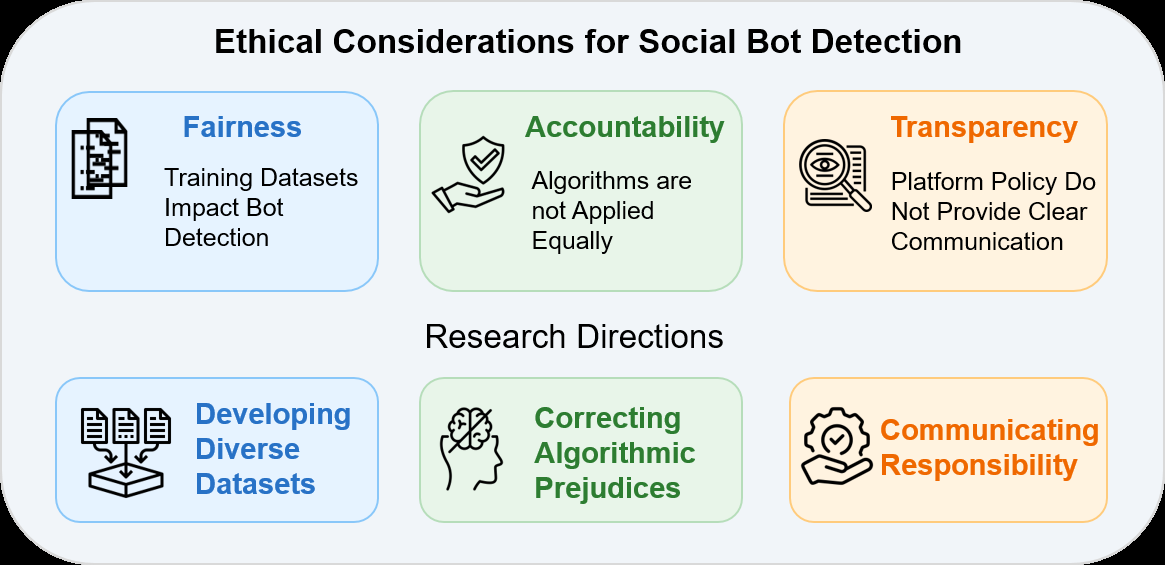
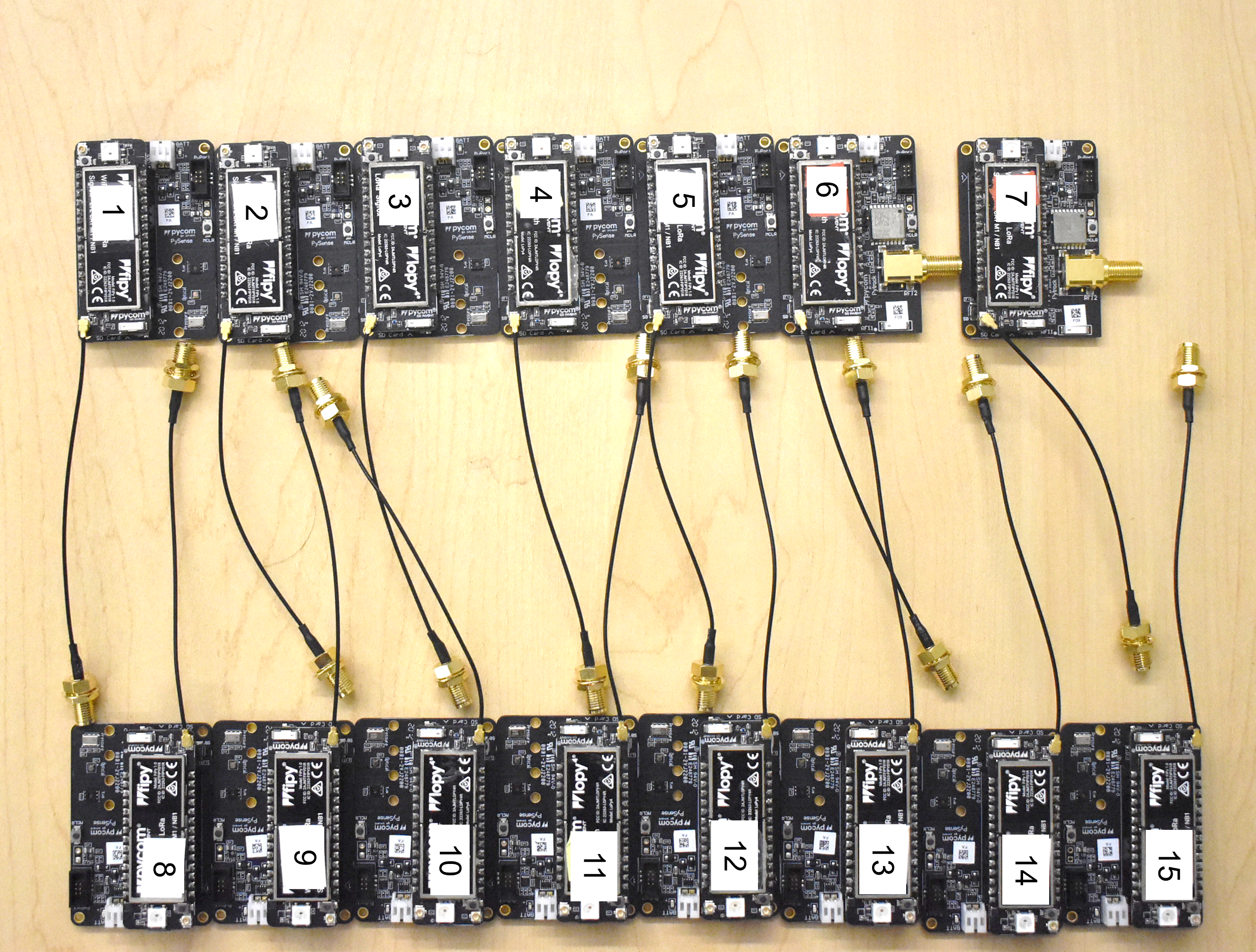
This paper addresses the important and understudied topic of the ethical considerations in social media bot detection
research note
This paper addresses the important and understudied topic of the ethical considerations in social media bot detection
research note
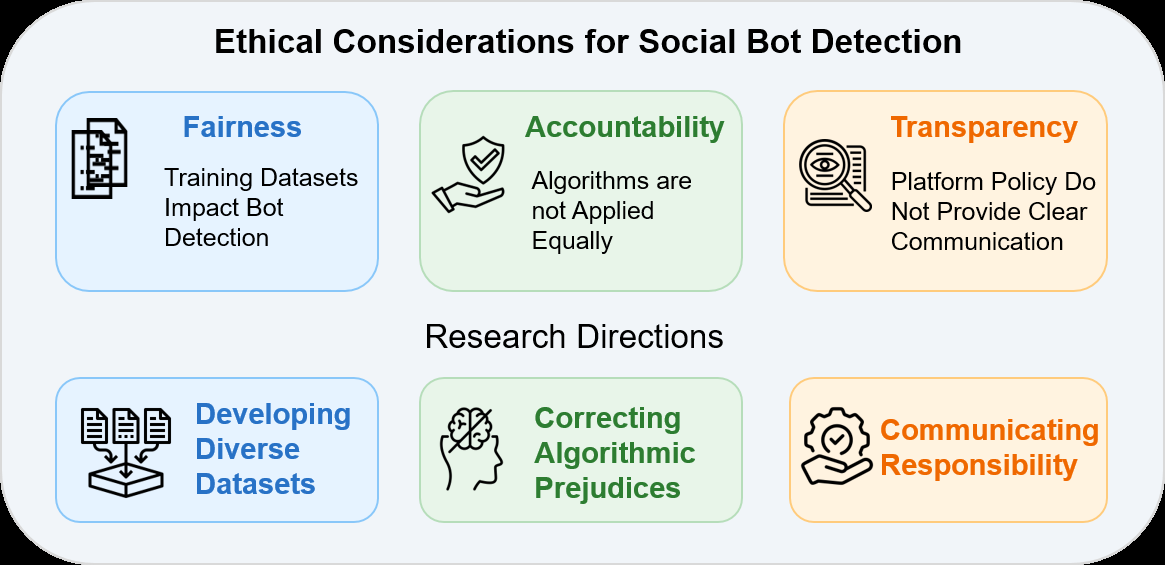
TaSA tackles a very specific but important failure mode in tactile manipulation: when a dexterous hand has to tell the difference between its own fingers/palm touching each other and the object act…
research note
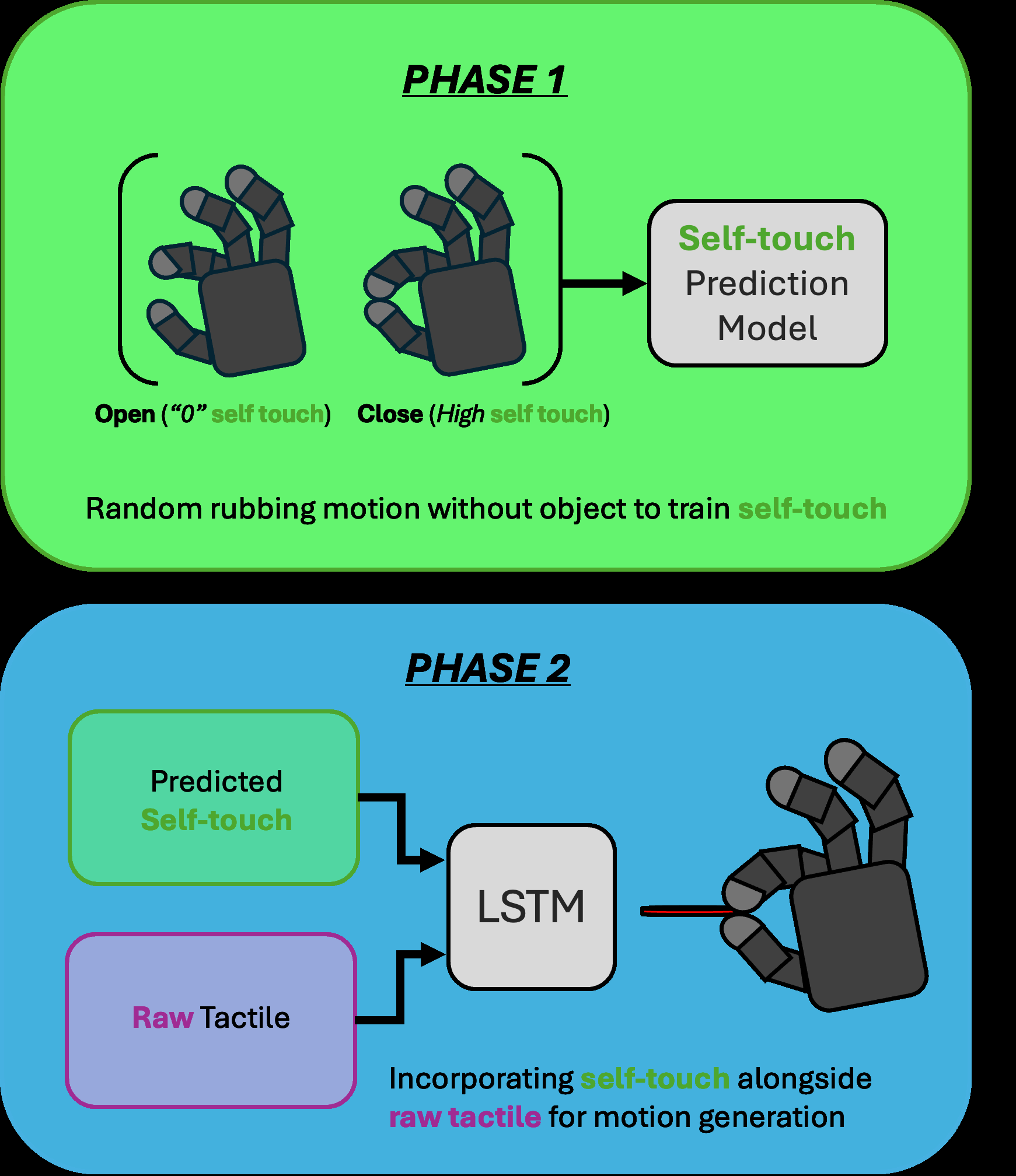
HEEDFUL tackles a practical failure mode in deep-learning RF fingerprinting — models trained on one capture regime often collapse when the device is still warming up

research note
This paper addresses the challenge of detecting sophisticated malicious bots on e-commerce platforms, which evade traditional defenses like IP blacklists and CAPTCHAs by using proxies, botnets, or …
research note
BOCLOAK is a constraint-aware adversarial attack framework for graph neural network (GNN) bot detectors on social networks
research note
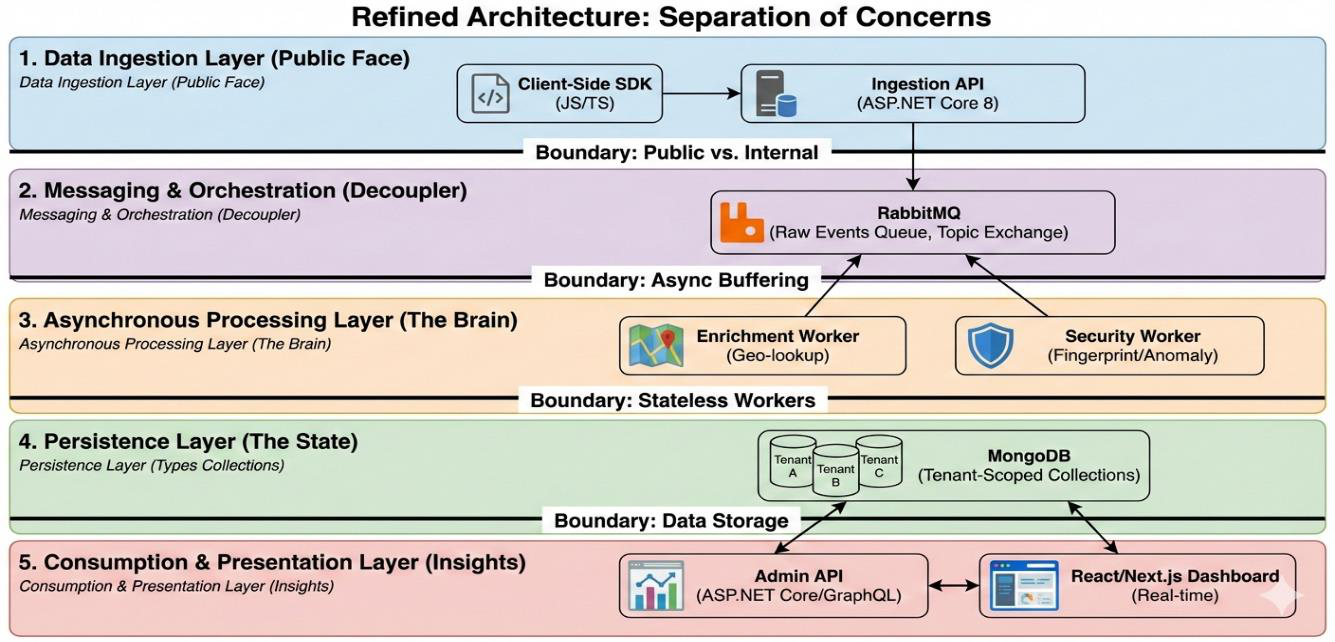
This paper presents Trackly, a unified SaaS platform designed to integrate comprehensive user behavior analytics with real-time rule-based anomaly detection
research note
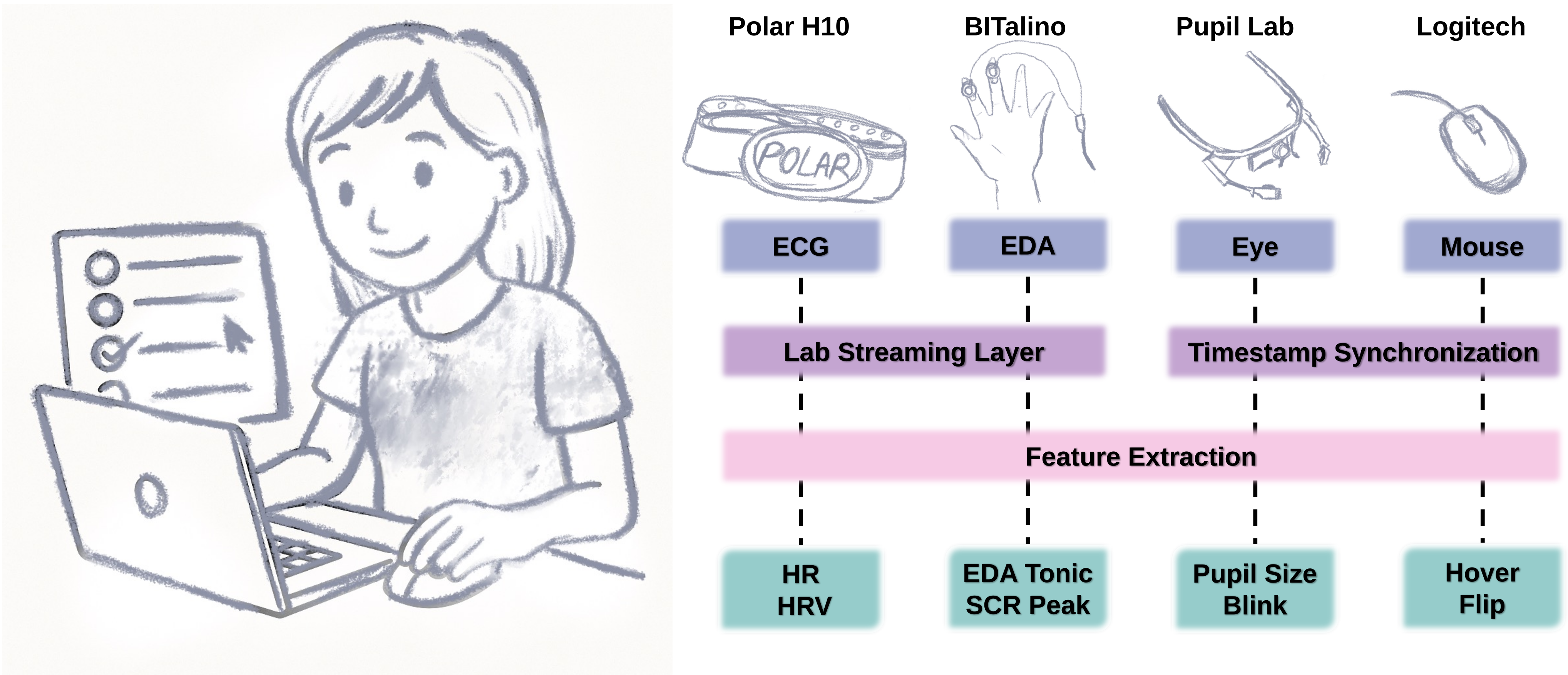
This paper studies whether very short web survey interactions can reveal stress and cognitive load from multimodal signals, and whether those signals align better with experimentally manipulated ta…
research note
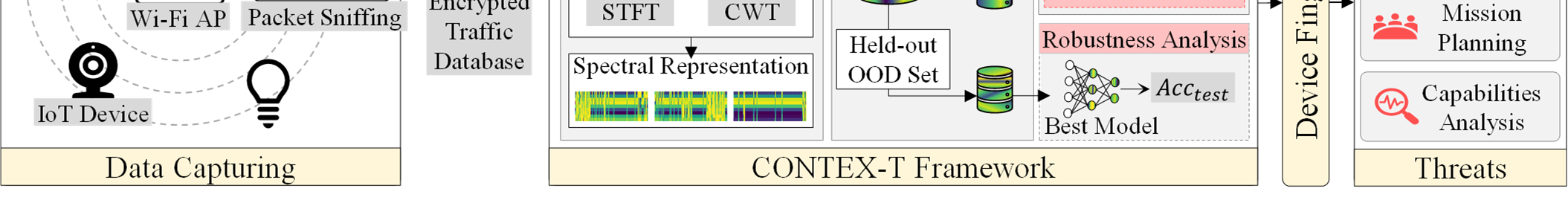
CONTEX-T studies a passive device-fingerprinting attack on encrypted IoT traffic, but instead of working directly in the packet-sequence or grayscale-image domain, it transforms packet-length windo…
research note
This paper studies whether large language models can generate proof-faithful explanations over OWL ontologies, not just answer entailment queries
research note
This paper asks a security-oriented question: can we reliably distinguish genuine online handwriting from synthetic handwriting generated by modern models and classical motion synthesis? The author…

research note
This paper addresses the strategic click-fraud vulnerability often attributed to the pro-rata revenue sharing rule on music streaming platforms, which allocates artists’ royalties proportional to t…
research note
This paper argues that audio CAPTCHAs have quietly become brittle in the face of modern speech and audio foundation models