Trackly: A Unified SaaS Platform for User Behavior Analytics and Real Time Rule Based Anomaly Detection
Source: arXiv:2601.22800 · Published 2026-01-30 · By Md Zahurul Haque, Md. Hafizur Rahman, Yeahyea Sarker
TL;DR
This paper presents Trackly, a unified SaaS platform designed to integrate comprehensive user behavior analytics with real-time rule-based anomaly detection. The motivation stems from existing fragmentation between product analytics (focused on business metrics) and security monitoring systems, which leads to delayed threat detection, limited visibility, and operational complexity—especially for SMEs. Trackly addresses this by continuously monitoring sessions, device/browser fingerprints, geo-location, and fine-grained events like add-to-cart and checkout in a scalable multi-tenant architecture. Suspicious activities such as impossible travel, new devices or IP locations, VPN usage, and rapid bot-like actions are detected with a configurable rule set combined with weighted risk scoring to provide explainable, transparent alerts.
The platform includes a real-time administrative dashboard featuring global session maps and behavioral statistics (DAU, bounce rates, session times). Built with a modern microservices stack and flexible MongoDB schema, Trackly achieved 98.1% accuracy, 97.7% precision, and a low 2.25% false positive rate on synthetic datasets simulating typical web behaviors and attacks. These results show that a carefully tuned rule-based approach combined with session and geo-analytics provides an efficient, practical solution without the complexity or opacity of ML-driven UEBA, suitable for SMEs and ecommerce with API and lightweight SDK integrations.
Key findings
- Trackly achieved 98.1% accuracy, 97.7% precision, and 2.25% false positive rate on a 2000-sample synthetic dataset simulating anomalous user behaviors.
- Impossible travel detection using the Haversine formula identified 298 out of 300 injected anomalies with only 2 false positives, demonstrating high effectiveness.
- VPN/proxy detection generated the most false positives (18 in 350 test cases), mostly due to legitimate VPN usage; mitigated by whitelist exclusions in production.
- Rapid bot-like actions (>50 actions in <60 seconds) were detected with 188/200 true positives and 12 false positives.
- Mixed high-risk anomaly scenarios combining multiple flags achieved 248/250 true positives and 2 false positives.
- Configurable weighted risk scoring rules flagged suspicious sessions with thresholds: low (<0.3), medium (0.3–0.5), and high risk (≥0.5).
- The system processed approximately 4,826 simulated sessions over 7 days with POI filtering and real-time dashboard updates at 10-second intervals.
- Integration setup via JavaScript SDK took under 10 minutes in informal peer testing; the dashboard was responsive and intuitive.
Threat model
The adversary attempts to compromise user accounts or conduct fraud via credential stuffing, session hijacking, bot-like rapid actions, or location spoofing. They can access different IP addresses, devices, and use VPNs/proxies but cannot fully obfuscate fingerprinting or produce realistic travel trajectories. The system assumes attackers do not have unrestricted capability to evade all rule-based detection mechanisms simultaneously.
Methodology — deep read
The threat model assumes an adversary aiming to compromise user accounts or perform automated fraud/bot attacks via unauthorized access, credential stuffing, or rapid/bot-like interactions. The attacker capabilities include controlling multiple IPs or devices but do not extend to evading all fingerprinting or geo-location checks.
The platform ingests synthetic datasets simulating 2,000 user sessions with labeled anomalies across categories: new device logins, new country access, impossible travel, VPN/proxy usage, rapid bot actions, and multiple accounts from the same IP. These synthetic data allow controlled injections of attack scenarios with ground truth labels for normal vs suspicious sessions.
Trackly's architecture is a multi-tenant microservices stack built on ASP.NET Core, with event ingestion via a lightweight JavaScript SDK and REST APIs. MongoDB stores session metadata and event logs in tenant-isolated collections, indexed for efficient querying. RabbitMQ mediates asynchronous processing tasks like geo-ip lookups, fingerprint comparisons, and risk scoring. The frontend React/Next.js dashboard consumes APIs for real-time session maps and behavioral metrics.
Anomaly detection uses a purely rule-based engine combining discrete checks (e.g., new device/browser fingerprint, new country location, impossible travel using the Haversine formula, VPN/proxy flags, rapid action bursts, multiple accounts per IP) with assigned risk points for each anomaly type (e.g., new device = +0.3, impossible travel = +0.4). The weighted sum yields a risk score, which determines alert levels.
The impossible travel detection uses the Haversine formula between consecutive login geo-coordinates, dividing distance by elapsed time to compute travel velocity. Speeds above 1000 km/h trigger flags. This threshold balances between blocking unrealistically fast travel and avoiding false positives from legitimate VPNs or minor geolocation errors.
Evaluation computed standard binary classification metrics (accuracy, precision, recall, F1, false positive rate) on synthetic labeled sessions. Multiple anomaly types and combined scenarios were tested for detection and false alarm rates. The dashboard's usability was informally validated on session volumes averaging 689 DAUs over a simulated week.
While code or dataset release is not mentioned explicitly, the methodology is reproducible given the detailed rule definitions, data schema descriptions, and anomaly injection procedures. Exact hyperparameter tuning and seed strategies are not discussed due to the rule-based nature rather than ML training.
Technical innovations
- Integration of comprehensive user behavior analytics and real-time rule-based anomaly detection within a single multi-tenant SaaS platform with unified visibility.
- Use of weighted risk scoring combining multiple heuristic rules (device fingerprint, geo-location, impossible travel, VPN/proxy detection, action rate) to generate explainable anomaly flags.
- Application of the Haversine formula for impossible travel detection with a tunable 1000 km/h threshold to balance sensitivity and false positives.
- Development of a lightweight JavaScript SDK and secure REST APIs enabling quick integration and real-time behavioral monitoring coupled with a responsive dashboard.
- Microservices architecture with MongoDB tenant-scoped data isolation and RabbitMQ-driven asynchronous event processing to support scalability and operational efficiency.
Datasets
- Synthetic User Behavior Dataset — 2,000 labeled sessions — generated by authors simulating normal and anomalous events
Baselines vs proposed
- No machine learning baselines reported; evaluation focused on rule-based detection with overall Accuracy = 98.1%, Precision = 97.7%, False Positive Rate = 2.25% on synthetic data.
Figures from the paper
Figures are reproduced from the source paper for academic discussion. Original copyright: the paper authors. See arXiv:2601.22800.
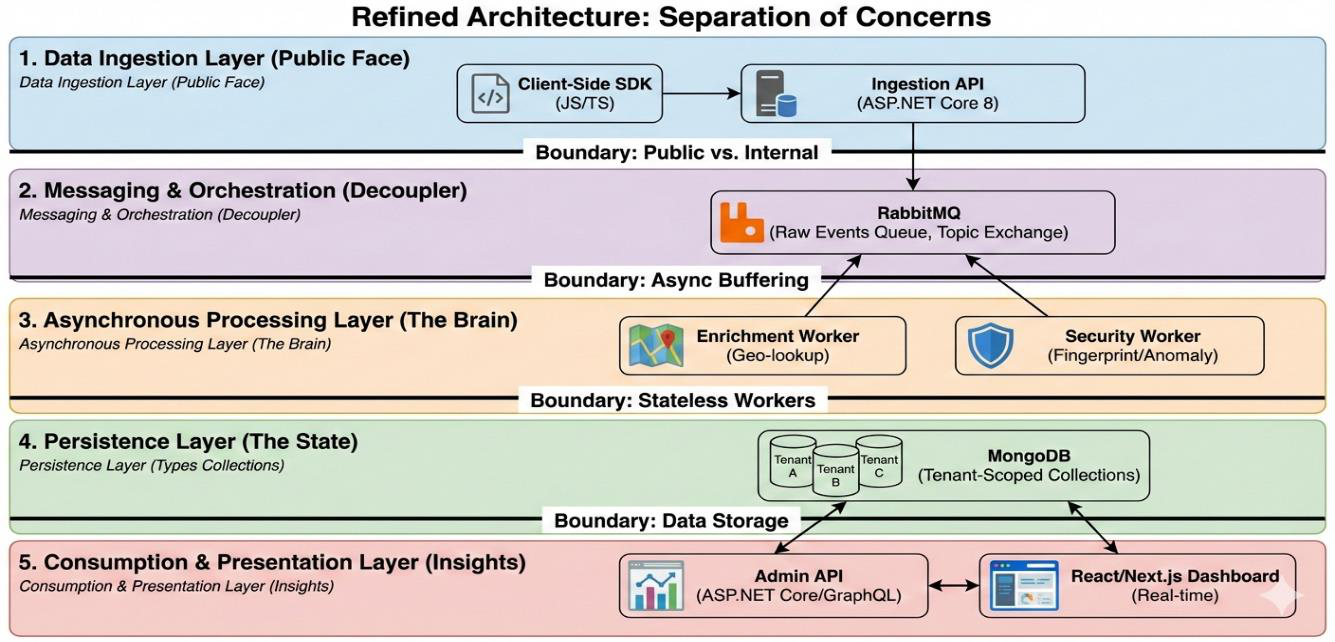
Fig 1: High-Level System Architecture
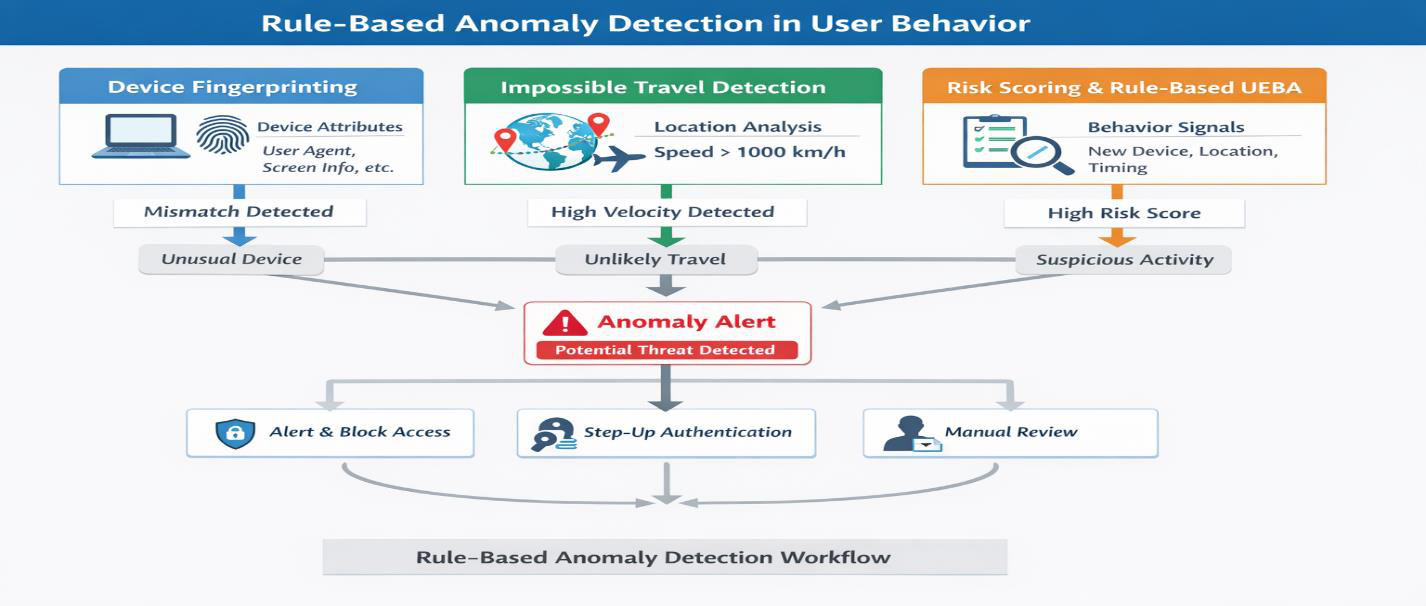
Fig 2: Rule-Based Anomaly Detection in User Behavior
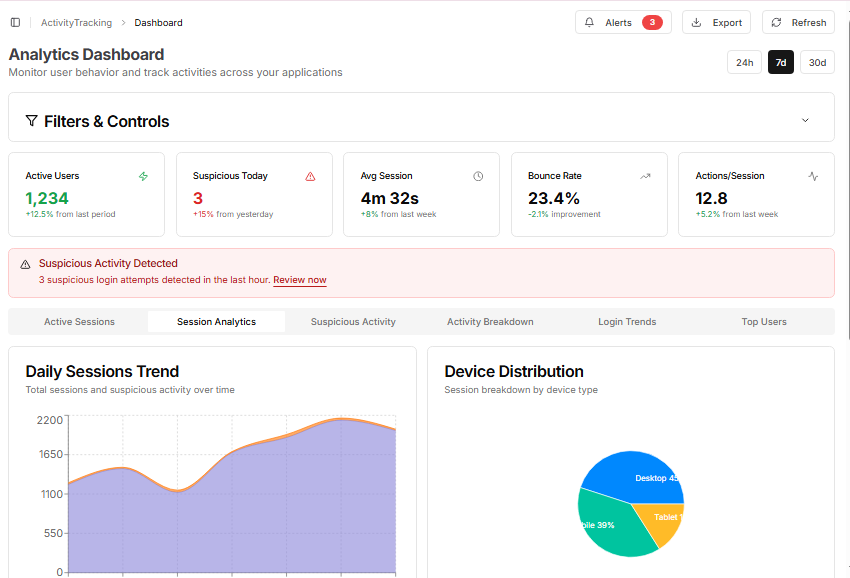
Fig 3: Daily Sessions analysis Dashboard

Fig 4: Geographical Distribution of Sessions
Limitations
- Reliance on static, manually configured rules limits adaptability to novel or evolving attack patterns not captured by the heuristics.
- Evaluation restricted to synthetic datasets; no real-world deployment data or adversarial validation reported.
- VPN/proxy detection generated relatively higher false positives due to legitimate usage, requiring manual whitelist tuning.
- Risk scoring thresholds were per-MVP fixed with no per-tenant dynamic customization in the current implementation.
- Mobile platform support and advanced UX analytics like session replay or heatmaps remain future work.
- No machine learning or unsupervised anomaly detection currently integrated, which could enhance detection coverage.
Open questions / follow-ons
- How would Trackly's rule-based detection perform against adaptive adversaries who mimic normal behavioral profiles or gradually evolve attack patterns?
- What gains and trade-offs arise from integrating machine learning-based unsupervised anomaly detection alongside the current rules to detect subtle or unknown threat types?
- How effective is Trackly when deployed in real-world heterogeneous environments with noisy and incomplete behavioral telemetry, especially across diverse global user bases?
- Can risk scoring thresholds be automatically personalized per tenant or dynamically adapted based on ongoing feedback to reduce false positives without losing security coverage?
Why it matters for bot defense
Bot-defense practitioners can draw key insights from Trackly's effective use of explainable, rule-based anomaly detection combined with user behavior analytics to identify automated or malicious activities in real time. The use of weighted risk scores over heuristics such as device fingerprint mismatches, impossible travel via geo-location, and rapid interaction bursts parallels many common bot indicators. This system avoids the complexity and opacity of ML models, achieving high precision and low false positives—critical in CAPTCHA and bot mitigation to minimize user friction.
Moreover, the unified platform design demonstrates the value of consolidating security and product analytics for holistic detection visibility, relevant for CAPTCHA operators seeking to correlate suspicious behavior signals across sessions or accounts. The detailed Haversine-based impossible travel detection offers a practical technique to identify session hijacking or credential stuffing, a threat often coupled with bot attacks. However, the reliance on static rules underscores the ongoing challenge of adapting to evolving bot tactics, suggesting that CAPTCHA implementations should consider mixed approaches integrating behavior rules with ML to improve robustness and reduce false positives in production deployments.
Cite
@article{arxiv2601_22800,
title={ Trackly: A Unified SaaS Platform for User Behavior Analytics and Real Time Rule Based Anomaly Detection },
author={ Md Zahurul Haque and Md. Hafizur Rahman and Yeahyea Sarker },
journal={arXiv preprint arXiv:2601.22800},
year={ 2026 },
url={https://arxiv.org/abs/2601.22800}
}