research note
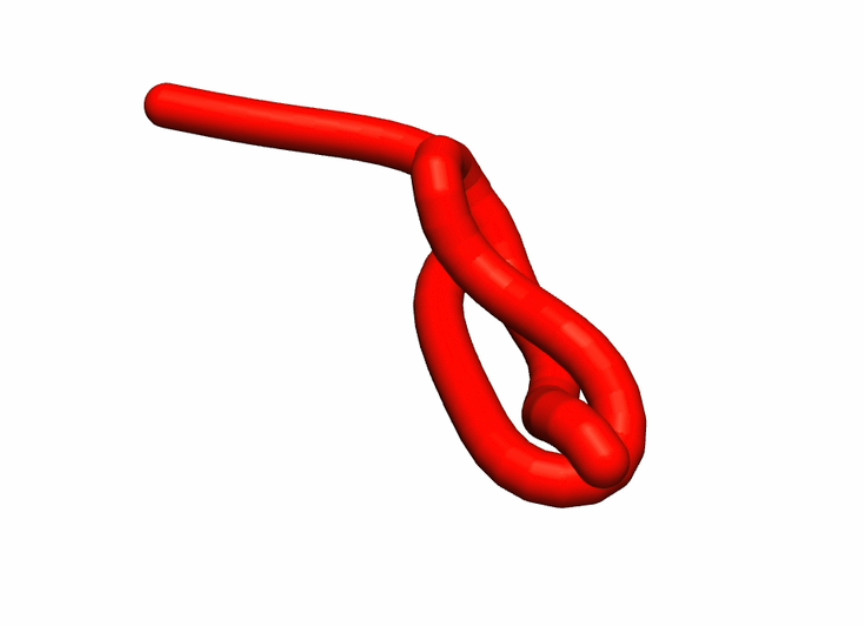
RopeDreamer: A Kinematic Recurrent State Space Model for Dynamics of Flexible Deformable Linear Objects
RopeDreamer tackles long-horizon dynamics prediction for deformable linear objects (DLOs) such as ropes and cables, where standard learned predictors often drift, over-stretch links, or lose track …