Can Cross-Layer Design Bridge Security and Efficiency? A Robust Authentication Framework for Healthcare Information Exchange Systems
Source: arXiv:2604.26339 · Published 2026-04-29 · By Khalid M. Ezzat, Muhammad El-Saba, Mahmoud A. Shawky
TL;DR
This paper tackles a practical tension in healthcare information exchange (HIE): strong device authentication is usually expensive, but lightweight schemes are often too weak for hostile hospital networks. The authors propose a cross-layer design that combines conventional PKI/ECC bootstrapping with physical-layer fingerprints extracted from OFDM traffic. The idea is to pay the cryptographic cost once during enrollment/handshake, then use PHY features like carrier frequency offset (CFO) and quadrature skewness for fast re-authentication in the steady state.
What is new here is not a new cipher or a new deep model, but a layered protocol architecture: a centralized authority (CA) registers devices and regional authorities (RCA), extracts CFO traces during enrollment, and provisions certificates and pseudo-identities; then the RCA runs an offline ML phase on those PHY features and an online identification phase on later traffic. The paper reports a formal BAN-logic proof and claims resistance to impersonation, MitM, replay, and Sybil attacks, while reducing computational and communication overhead versus conventional per-message cryptographic authentication. The experimental section is only partially visible in the supplied text, so the exact numerical accuracy/latency results are not recoverable from the excerpt.
Key findings
- Initial device registration uses ECC on the 160-bit secp160k1 curve, which the authors explicitly state is used for 80-bit security.
- The scheme extracts CFO samples during enrollment and stores them as a per-device feature list (listDi); these are later reused for ML training at the RCA.
- Re-authentication is moved off the cryptographic critical path: later health-related messages are checked using CFO plus quadrature-skew features from OFDM symbols rather than validating a fresh digital signature every time.
- The RCA trains its ML model in an offline mode using 80% of the collected device-feature dataset, with the remaining 20% used for testing (as stated in Section IV-B and IV-C).
- The protocol refreshes pseudo-identities every session interval Δt, with the new PID encrypted under the RCA–device shared key, to preserve unlinkability.
- The paper’s security argument is formalized with BAN logic and claims successful derivation of mutual-key and message-origin beliefs for the initial handshake and re-authentication messages.
- A figure caption indicates a 'confusion matrix of nearest neighbor algorithm for 20 devices scenario,' implying a 20-device identification experiment, but the supplied excerpt does not expose the actual accuracy values.
Threat model
The adversary is an external or adjacent network attacker in an HIE/IoMT setting who can eavesdrop, replay, forge identities, attempt MitM, modify traffic, and instantiate multiple bogus identities (Sybil). The protocol assumes the attacker cannot break ECC/Diffie-Hellman, cannot forge CA signatures, cannot compromise the CA/RCA trust roots or tamper-proof device storage, and cannot consistently mimic the targeted device’s PHY-layer fingerprint once the RCA’s classifier is trained. It also assumes timestamps and periodic pseudo-identity refresh are available and trustworthy for freshness and unlinkability checks.
Methodology — deep read
The threat model is a hospital/HIE environment with wireless OFDM communication between devices Di and an RCA, all under a CA that initializes public parameters and certifies principals. The adversary model in the text is the standard network attacker: it can eavesdrop, replay, impersonate devices, attempt MitM, modify messages, and launch Sybil-style identity forgeries. The authors assume the CA is trusted for key certification, the RCA and devices possess tamper-proof devices (TPDs), timestamps are available for freshness checks, and each device can participate in an initial PKI-based handshake before PHY-layer re-authentication begins. What the adversary cannot do, according to the protocol assumptions, is break ECC/Diffie-Hellman, forge CA signatures, or reliably spoof the PHY fingerprints once the ML classifier is trained.
Data provenance is mostly protocol-generated rather than a public benchmark. During registration, each device Di sends its public key and original identity in M1; the CA observes the transmission over M OFDM symbols and runs the van-de-Beek CFO estimator to collect l CFO estimates, which are stored in listDi. The CA then creates a digital certificate CertDi and stores ⟨listDi, OIDDi, CertDi⟩ in its records and preloads ⟨PPs, CertDi⟩ into the device TPD. For the RCA side, the CA preloads ⟨PPs, listDi, CertRCA⟩ into the RCA TPD, and the RCA later uses listDi to train its ML model. The excerpt says the RCA uses 80% of the overall dataset for training and 20% for testing, but it does not specify the total sample count, number of packets per device, train/test stratification, or whether the split is per-device, per-session, or per-frame. Likewise, the paper mentions a 20-device nearest-neighbor confusion matrix figure, but the exact dataset size and label construction are not visible in the provided text.
Architecturally, the protocol has three phases. First, initialization: the CA picks secp160k1 domain parameters, chooses SKCA, computes PKCA, and defines symmetric encryption/decryption primitives EncSK and DecSK; PPs = {a, b, p, q, g, PKCA, EncSK, DecSK}. Second, registration and initial handshaking: the device chooses SKDi, computes PKDi, and transmits M1 = ⟨PKDi, OIDDi, T1⟩. The CA extracts CFO features from M1, creates CertDi = ⟨PKDi, TR, σCA⟩ where σCA = SignSKCA(PKDi ∥ TR), and loads those values into the TPD. The RCA similarly registers with the CA, gets CertRCA, and periodically broadcasts M2 = ⟨CertRCA, T1, σRCA⟩. The device verifies CertRCA, freshness of T1, and σRCA, then derives a Diffie-Hellman shared key SKRCA-Di = SKDi · PKRCA, encrypts a pseudo-identity as CIDT2_Di = EncSKRCA-Di(PIDT2_Di), and returns M3 = ⟨CertDi, T2, CIDT2_Di, σDi⟩. The RCA verifies the device certificate and signature, derives the same shared key, decrypts the pseudo-identity, and stores ⟨CertDi, PIDT2_Di, SKRCA-Di⟩ in listComm. Third, re-authentication: for each health-related message m, the device sends M4 = ⟨m, PIDT2_Di⟩, and the RCA extracts CFO and quadrature-skew features from the incoming OFDM symbols, then classifies the sender using the trained ML model. Every session interval Δt, the device also sends an updated pseudo-identity M5 = ⟨m, PIDT2_Di, CIDT3_Di⟩ where CIDT3_Di = EncSKRCA-Di(PIDT3_Di), and the RCA decrypts and updates its device list. One concrete end-to-end example is the re-authentication path: an OFDM health message arrives, the RCA computes the CFO estimate with the van-de-Beek autocorrelation formula and the quadrature skew angle from I/Q samples, feeds those features into the offline-trained classifier, and if the predicted identity matches the stored device profile, the message is accepted without a fresh ECC signature check.
The algorithmic novelty is therefore a cross-layer fusion rather than a new classifier family. CFO is estimated using the van-de-Beek method over the cyclic prefix, with the normalized offset converted to Hz; quadrature skewness is computed from I/Q sample correlations; those two features are treated as device fingerprints. The paper does not describe the exact ML architecture in the visible excerpt beyond calling it a 'lightweight neural network' in related-work positioning and showing a nearest-neighbor confusion matrix figure caption, so the source is ambiguous about whether the final classifier is k-NN, SVM, or a neural net in the reported experiment. Training details such as optimizer, learning rate, epochs, batch size, random seed, or hardware are not present in the provided text. Evaluation appears to focus on (i) BAN-logic formal verification of authentication goals, (ii) a PHY-layer identification experiment, and (iii) computational/communication overhead comparisons, but the excerpt does not expose the numerical results, the exact baselines, or any statistical significance tests. Reproducibility is limited by the fact that only protocol details and one parameter table are visible here; there is no code link, no frozen model release, and no public dataset specified in the excerpt.
Technical innovations
- Combines PKI/ECC bootstrapping with PHY-layer device fingerprints so that expensive cryptographic verification is used for enrollment, not for every message.
- Uses CFO and quadrature skewness extracted from OFDM symbols as per-device authentication features, rather than relying only on channel-state information or RF fingerprints.
- Adds encrypted pseudo-identity rotation every session interval Δt to reduce linkability between successive transmissions.
- Formally models the handshake and re-authentication logic in BAN logic to argue mutual authentication and freshness properties.
Datasets
- Protocol-generated OFDM feature traces — not specified — collected during device registration and later re-authentication; no public source named in the excerpt
Baselines vs proposed
- []
Figures from the paper
Figures are reproduced from the source paper for academic discussion. Original copyright: the paper authors. See arXiv:2604.26339.
Fig 1: System modeling.

Fig 2 (page 2).

Fig 3 (page 2).

Fig 4 (page 2).

Fig 5 (page 2).
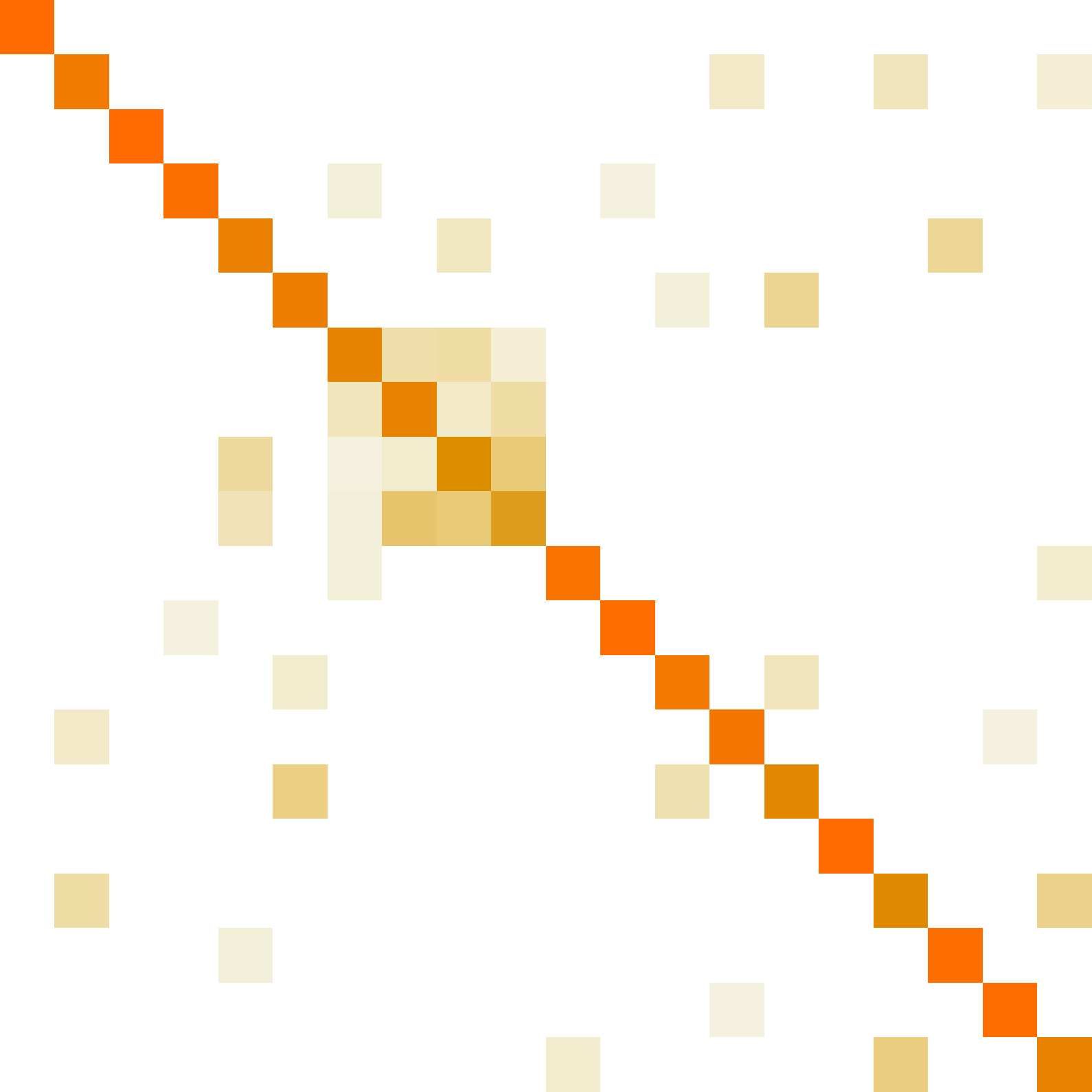
Fig 6: Confusion matrix of nearest neighbor algorithm for 20 devices scenario
Limitations
- The excerpt does not provide the actual dataset size, number of devices, or the exact train/test split beyond an 80/20 division.
- The classifier architecture, hyperparameters, training epochs, and hardware used for ML training/evaluation are not specified in the visible text.
- The security argument relies heavily on BAN logic, which proves beliefs under protocol assumptions but does not substitute for a computational adversary proof or real-world attack emulation.
- No distribution-shift evaluation is shown for changing channels, mobility, device aging, or RF front-end drift, all of which can alter CFO/skew fingerprints.
- The provided text does not expose concrete accuracy/latency/overhead numbers, so the claimed efficiency and robustness cannot be independently judged from the excerpt.
- The system assumes trusted CA/RCA infrastructure and tamper-proof devices, which may be strong assumptions in real hospital deployments.
Open questions / follow-ons
- How stable are CFO and quadrature-skew fingerprints across temperature changes, mobility, antenna replacements, and long-term hardware aging in a hospital setting?
- What happens under deliberate PHY mimicry, adversarial over-the-air perturbation, or replay using recorded OFDM bursts from a legitimate device?
- How much accuracy is lost when moving from a controlled single-RCA environment to multiple wards, more devices, and heterogeneous radios?
- Can the protocol be hardened with a computational security proof or a red-team evaluation beyond BAN-logic reasoning?
Why it matters for bot defense
For bot-defense engineers, the main lesson is that identity assurance can be layered: a strong cryptographic bootstrap can be paired with a cheap behavioral or physical signal for continuous verification. The analogous move in CAPTCHA/bot systems is to avoid forcing a heavyweight challenge on every interaction; instead, use a higher-cost enrollment step and then maintain confidence with low-latency, session-level signals that are hard to fake at scale. The caution is the same as with browser fingerprinting or behavioral biometrics: if the signal is too stable, you get tracking risk; if it is too volatile, false rejects rise. This paper’s pseudo-identity rotation is a useful design pattern for reducing linkability, but the unseen failure modes are exactly the ones bot-defense teams care about: drift, spoofability, and the gap between formal protocol arguments and messy deployment conditions.
Cite
@article{arxiv2604_26339,
title={ Can Cross-Layer Design Bridge Security and Efficiency? A Robust Authentication Framework for Healthcare Information Exchange Systems },
author={ Khalid M. Ezzat and Muhammad El-Saba and Mahmoud A. Shawky },
journal={arXiv preprint arXiv:2604.26339},
year={ 2026 },
url={https://arxiv.org/abs/2604.26339}
}