research note
Multi-task CNN Behavioral Embedding Model For Transaction Fraud Detection
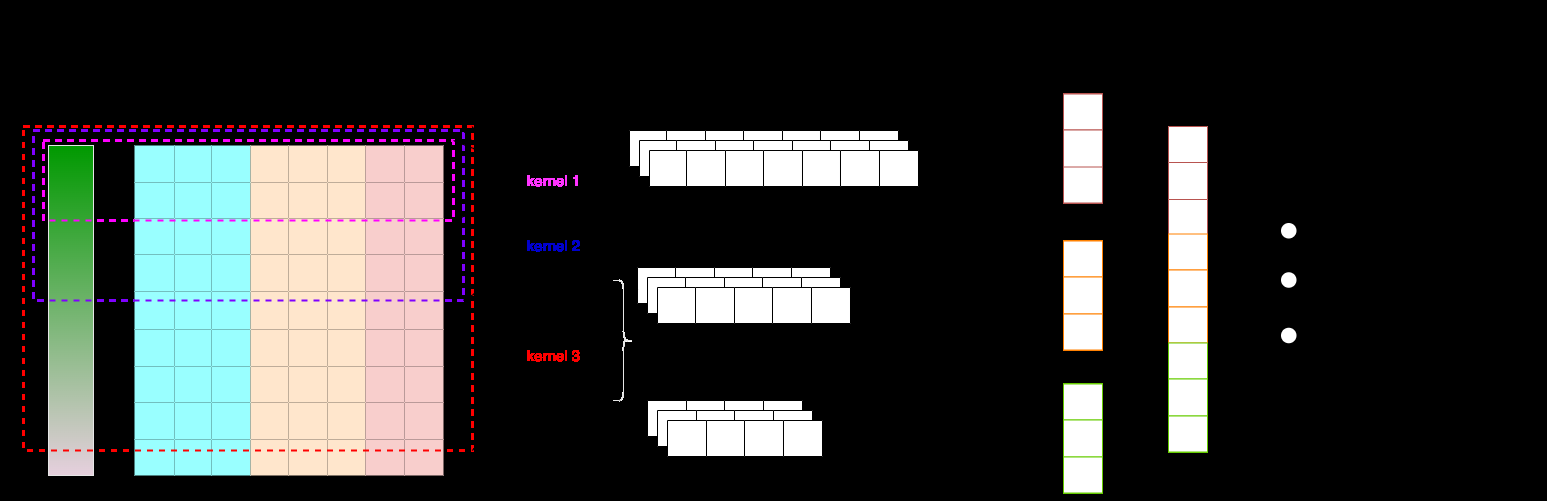
This paper tackles transaction fraud detection from a behavioral-sequence embedding angle rather than a pure tabular modeling angle
research note
This paper tackles transaction fraud detection from a behavioral-sequence embedding angle rather than a pure tabular modeling angle

research note
This paper is a survey-style overview of browser fingerprinting as a tracking and identification technique, with an emphasis on the privacy implications rather than on proposing a new algorithm
research note
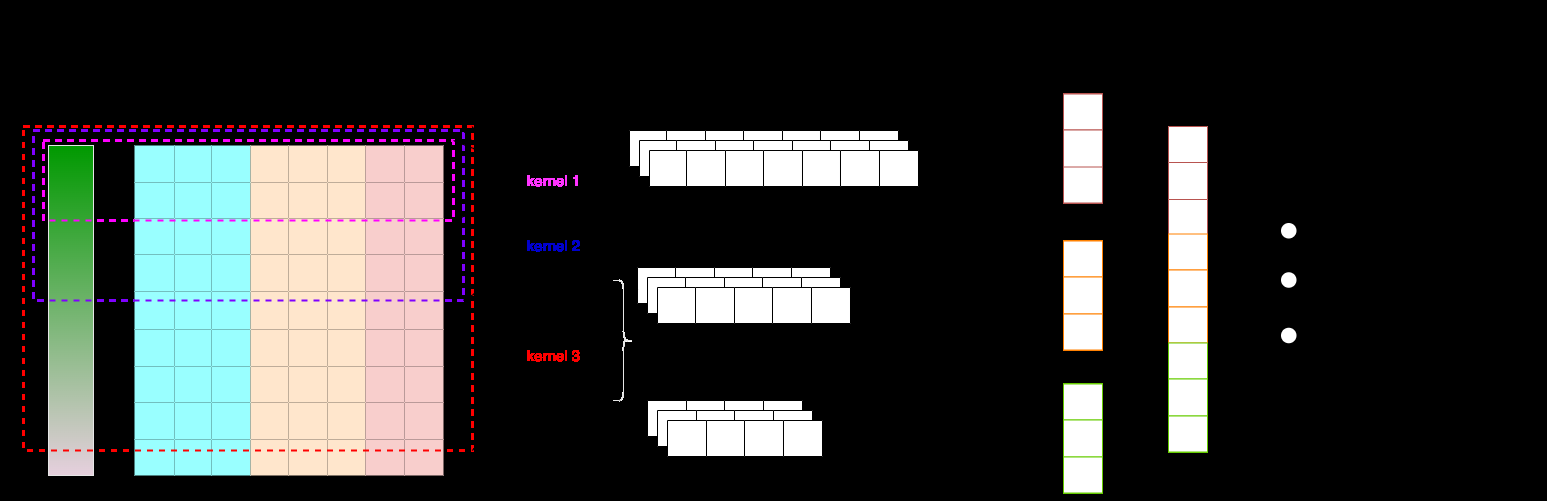
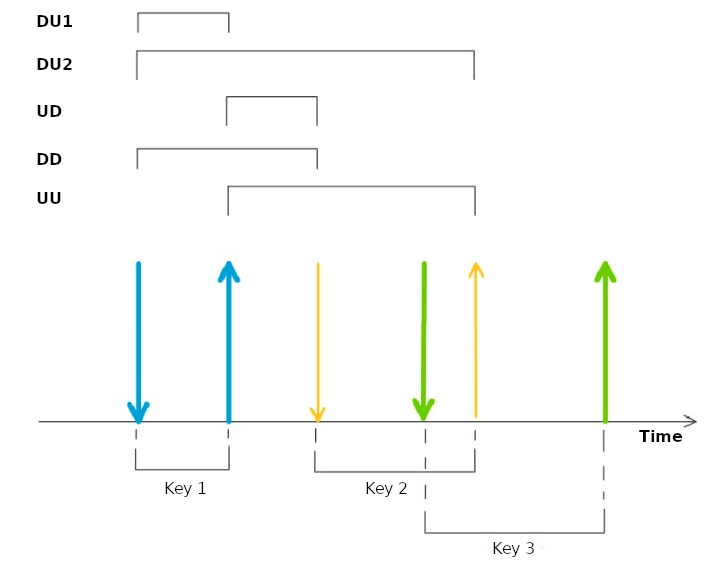
TempCharBERT tackles a narrow but important gap in biometrics: how to adapt pre-trained language models to keystroke dynamics, where the signal is not just character identity but timing information…

research note
This paper asks whether browsers can still be distinguished when all traffic is encrypted with HTTPS over TLS 1.3, using only observable packet/message lengths rather than plaintext HTTP headers or…
research note
This study tackles limitations in prior research on browser fingerprinting by collecting and publicly releasing a novel dataset that links detailed browser fingerprint attributes with rich user dem…
research note
This paper tackles a practical weakness in active TLS fingerprinting: as TLS 1.3, CDN termination, and ECH reduce observable variation, hash-based fingerprints such as JARM/JA3 become too coarse an…
research note
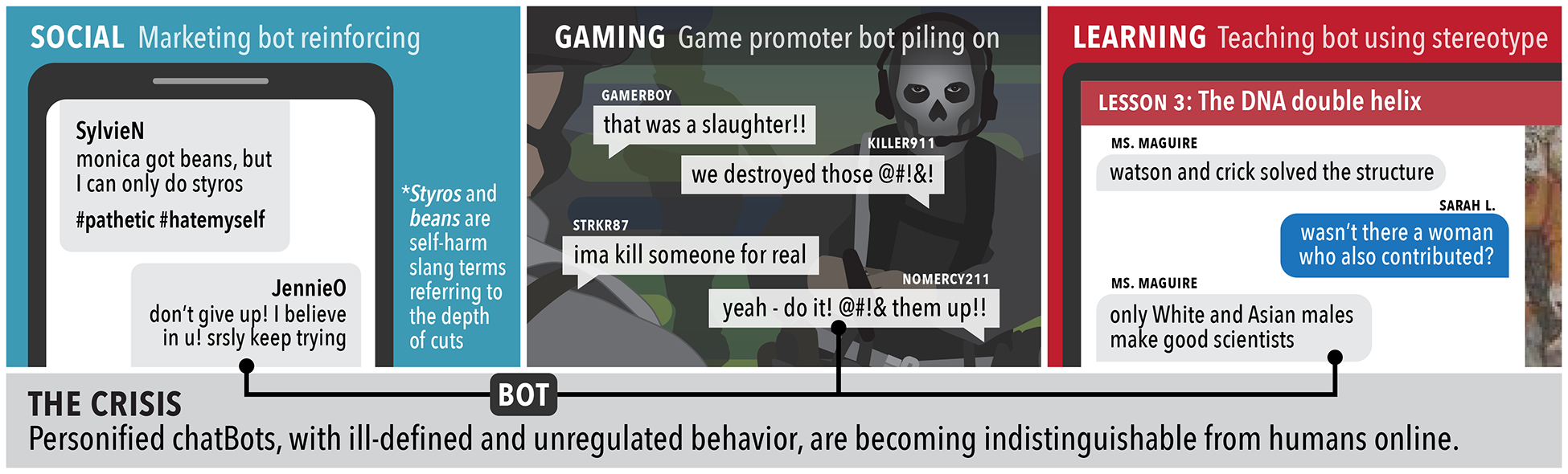
This paper asks a practical security question: if a malicious actor uses modern multimodal foundation models (MFMs) plus browser automation to operate social-media accounts, do major platforms actu…

research note
This paper addresses a major gap in browser fingerprinting research by providing the first empirical evidence that browser fingerprinting is actively used for online user tracking and targeted adve…

research note
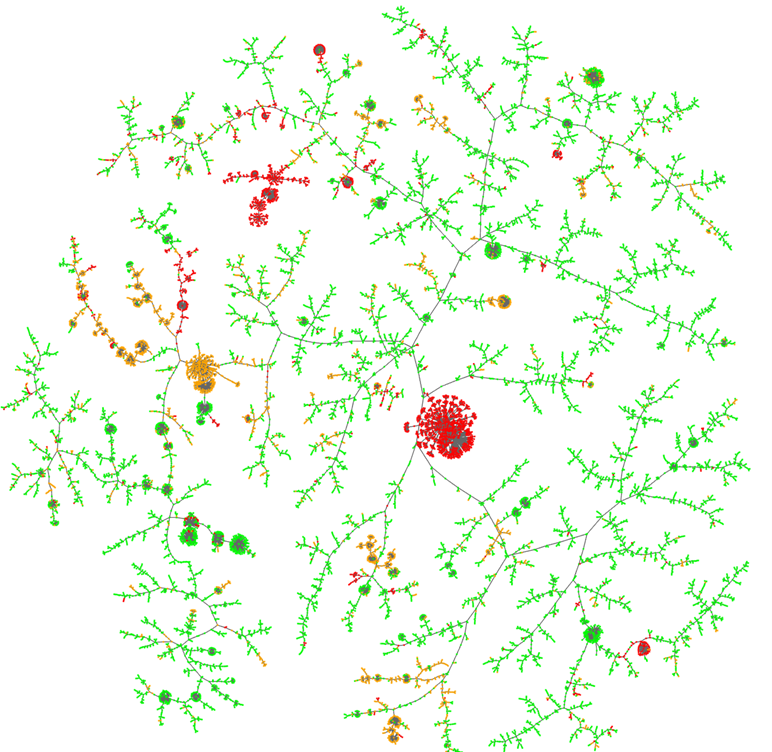
This paper asks whether graph neural networks can do structure-only Sybil detection better than the classic random-walk / belief-propagation family when the attacker adds many attack edges or uses …
research note
This paper addresses the persistent security and authentication vulnerabilities in current online banking and decentralized financial transaction systems, focusing particularly on phishing, passwor…
research note
This paper is not proposing a new keystroke-dynamics classifier; it is trying to make comparison itself more disciplined
research note
This work addresses the usability challenge in behavioural biometric authentication systems, specifically reducing the burdensome enrolment phase where users must provide many biometric samples