research note
Bots Don't Sit Still: A Longitudinal Study of Bot Behaviour Change, Temporal Drift, and Feature-Structure Evolution
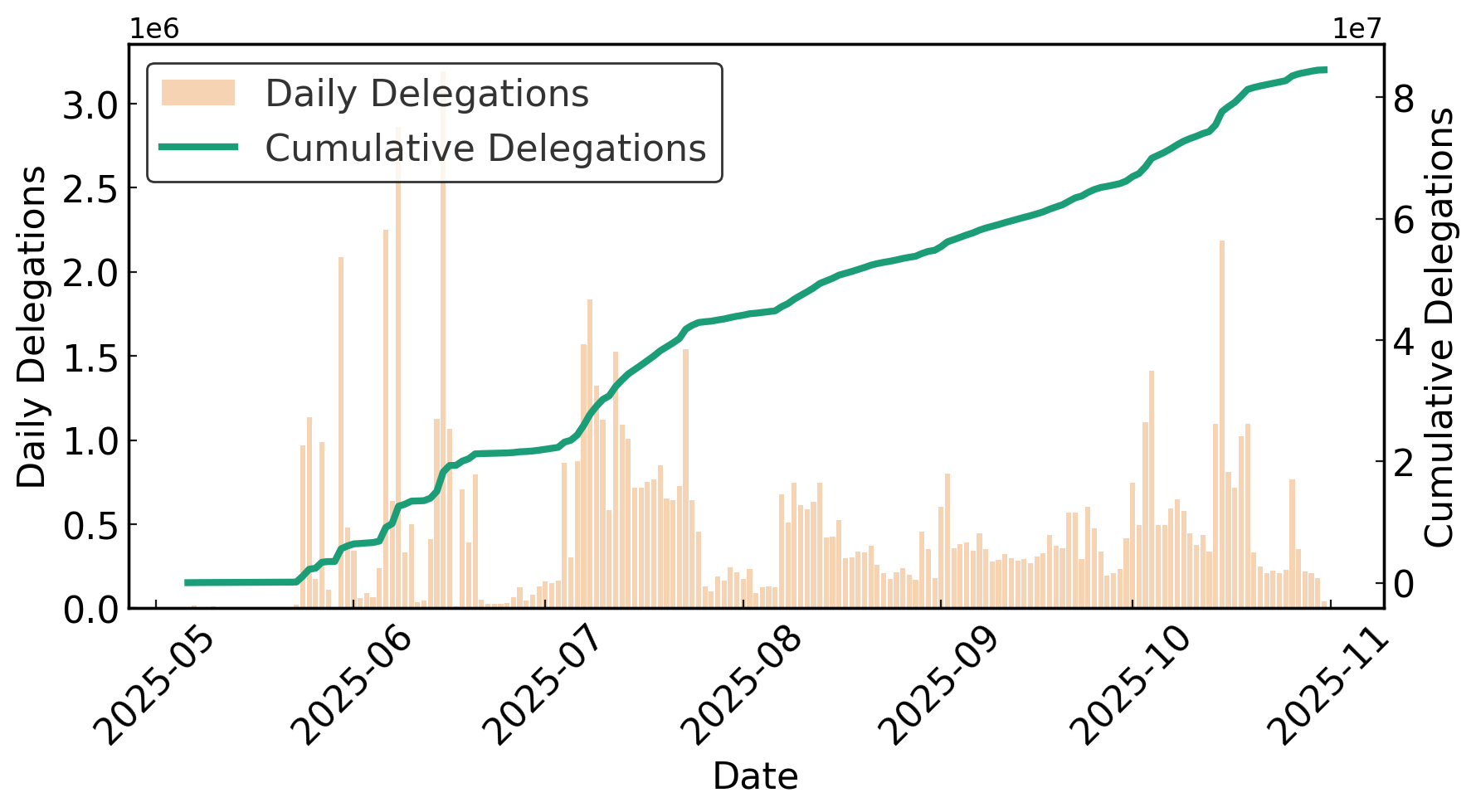
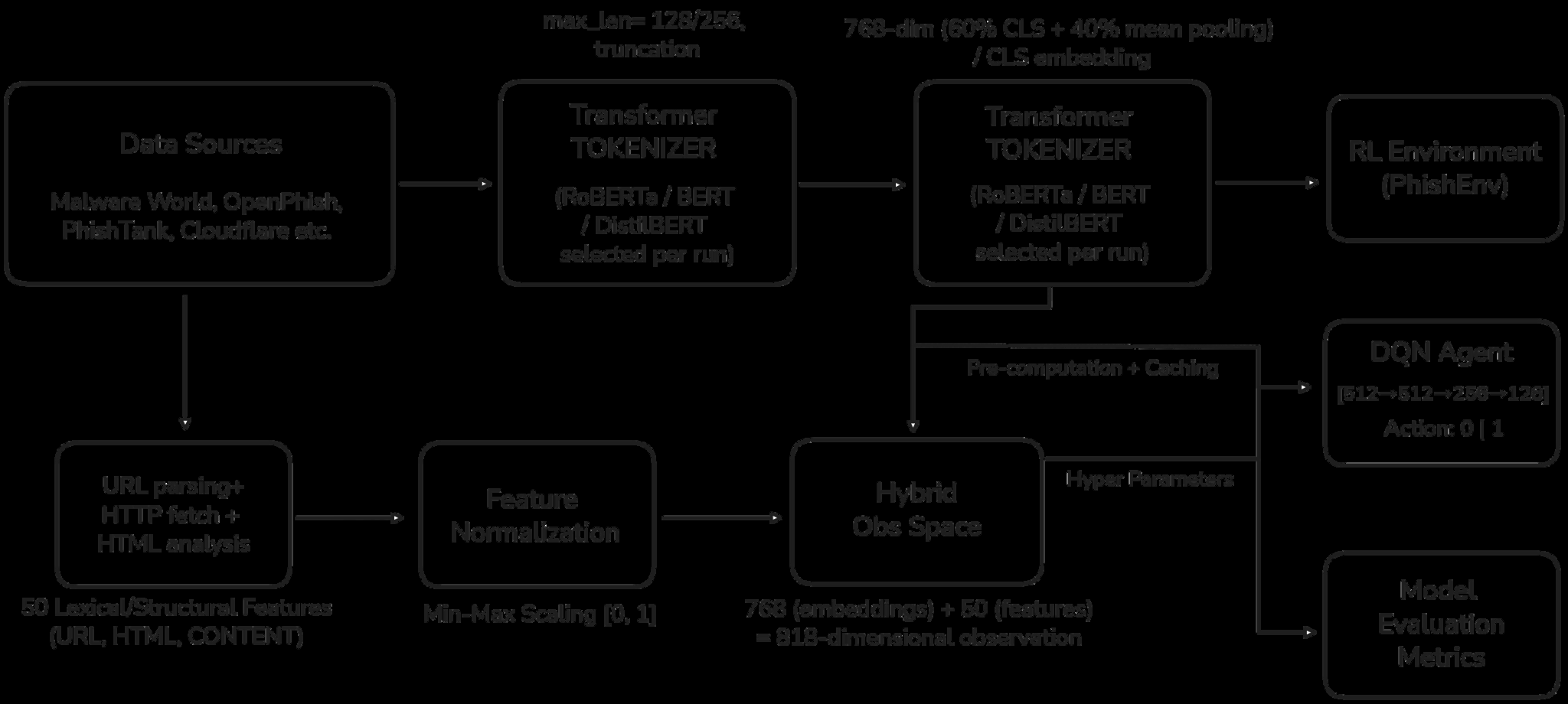
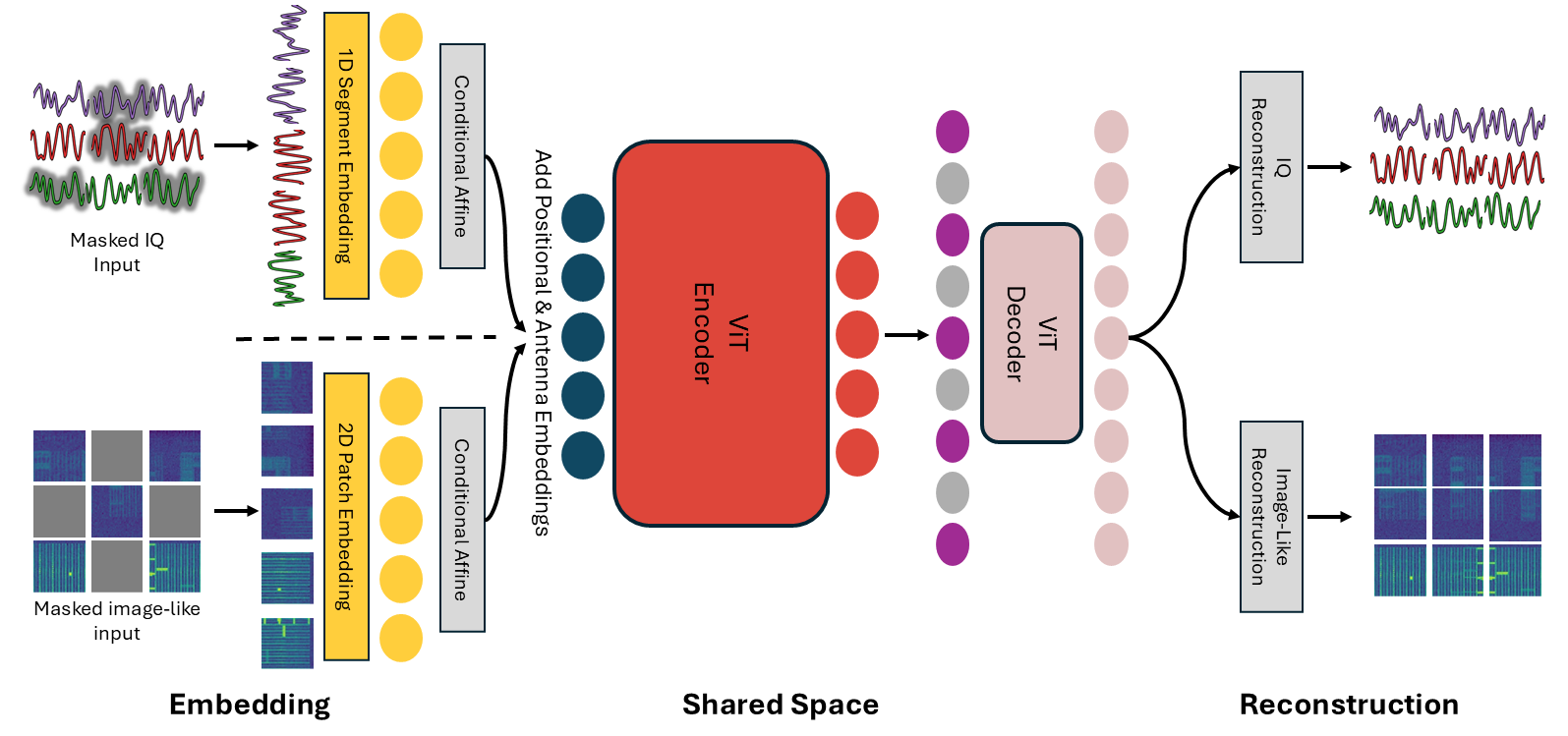
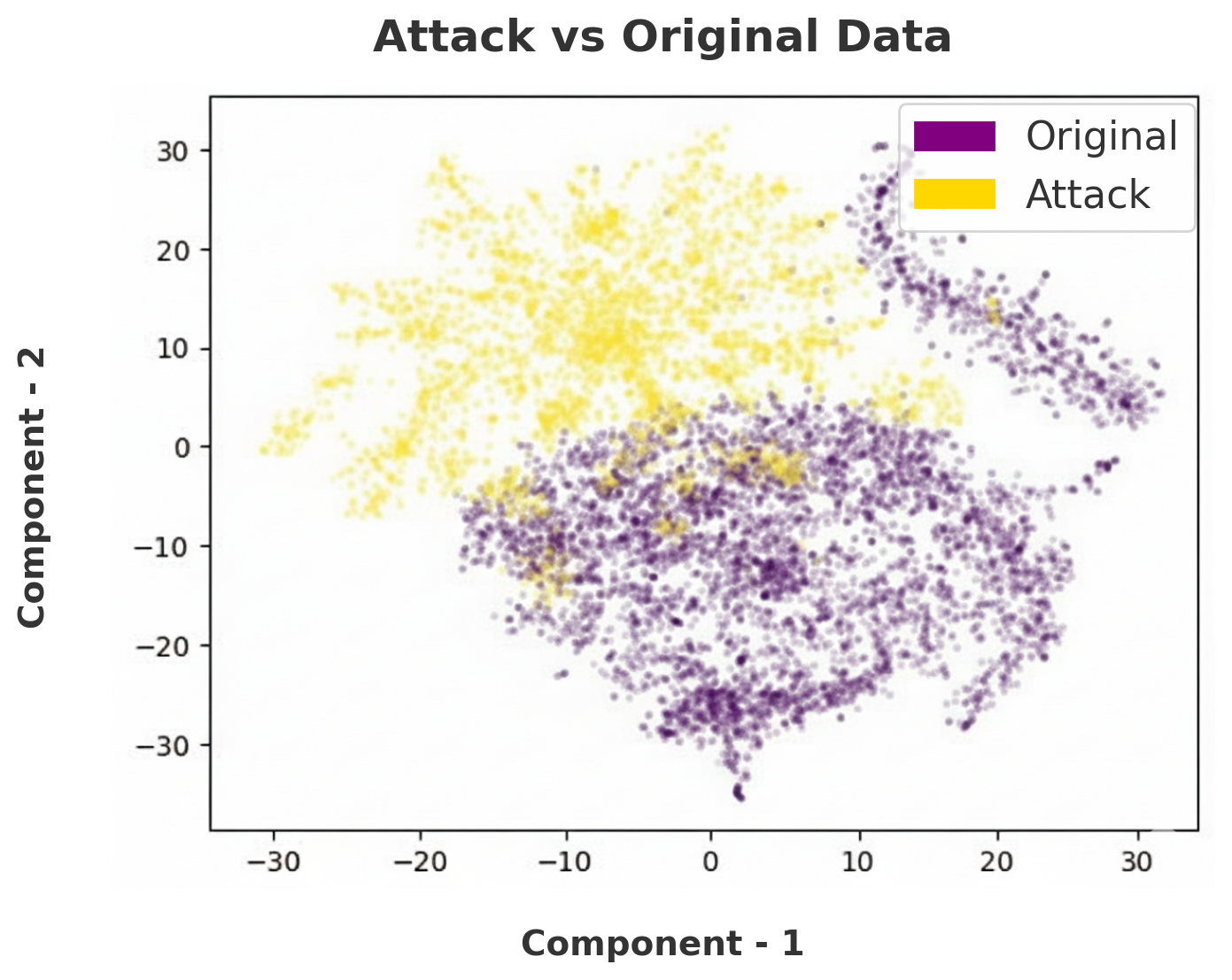
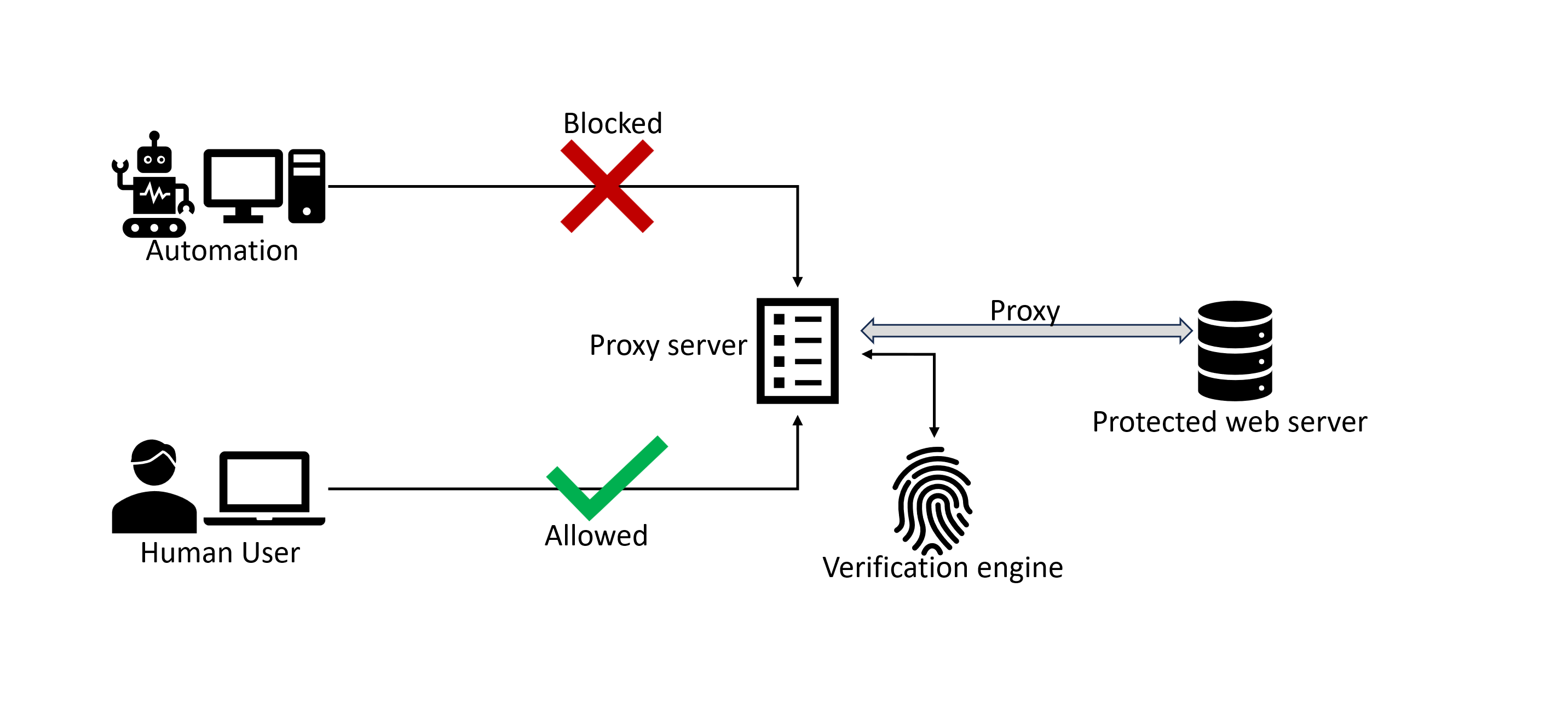
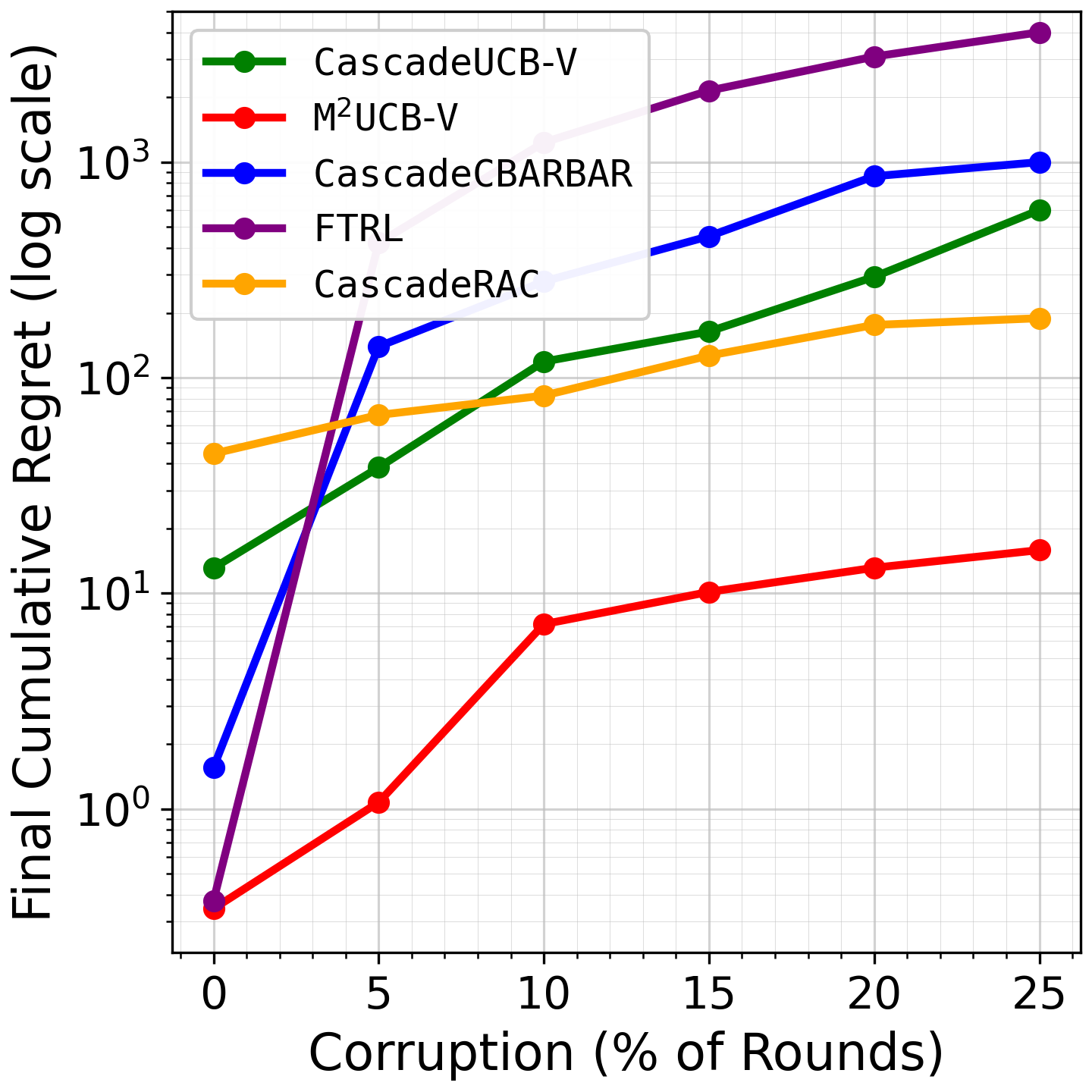
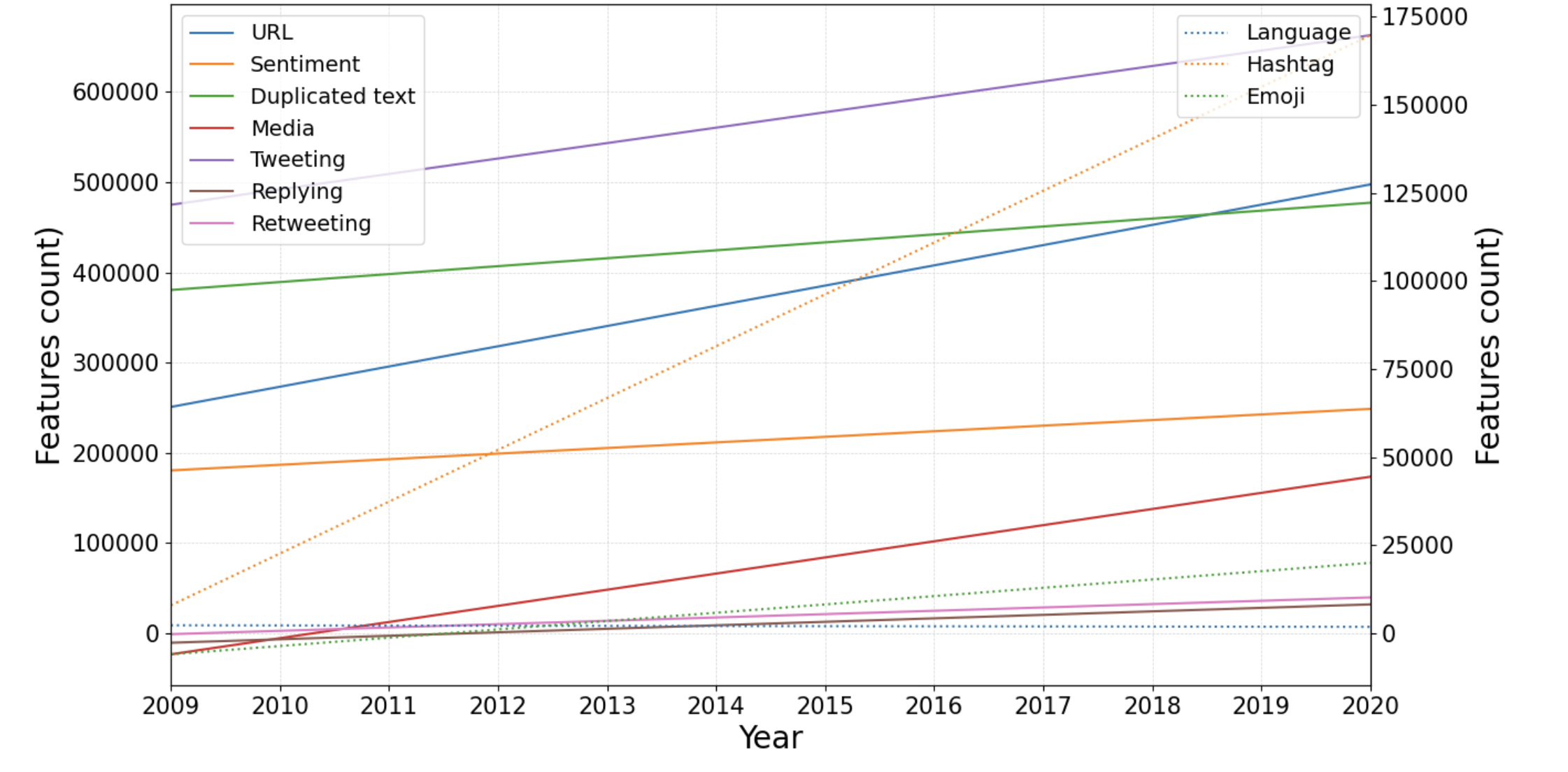
This paper investigates whether promotional social bots on Twitter exhibit systematic behavioural changes over time, challenging the common assumption that bot behaviours and associated features re…