CAHICHA: Computer Automated Hardware Interaction test to tell Computer and Humans Apart
Source: arXiv:2511.07841 · Published 2025-11-11 · By Aditya Mitra, Sibi Chakkaravarthy Sethuraman, Devi Priya V S
TL;DR
This paper addresses the increasing ineffectiveness of conventional human verification methods such as CAPTCHAs against advanced AI bots capable of solving visual puzzles, emulating typing behavior, and bypassing security checks. The authors propose CAHICHA, a novel human verification approach leveraging direct hardware interactions combined with cryptographically attested User Presence (UP) and User Verification (UV) flags provided by trusted hardware authenticators compliant with FIDO2/WebAuthn standards. This enables reliable distinction between real human users physically interacting with their devices and automated bots or scripts that cannot emulate such hardware-rooted presence.
The CAHICHA system is deployable as a proxy server that intercepts user requests, challenges browser authenticators to cryptographically prove user presence via physical actions like PIN entry, fingerprint scan, or touch sensor activation on hardware security modules or TPMs. Verification relies on attestation from legitimate hardware devices validated via FIDO Metadata Service. Extensive performance and usability evaluations demonstrate CAHICHA's ability to sustain high request volumes with zero failures, fast challenge completion (~12ms), strong resilience to volumetric bot attacks, and favorable user experience (majority rating 4 or 5) compared to traditional CAPTCHAs. By moving verification to hardware-mediated physical interaction, CAHICHA raises the complexity and cost for attackers relying on purely software bots to bypass security checks, providing a promising direction for bot defense in the era of AI-driven automated threats.
Key findings
- CAHICHA challenges complete in approximately 12 milliseconds, significantly faster than reCAPTCHA v3 (4–10 seconds) and hCaptcha (~19 seconds).
- Load testing under concurrent users (up to 6 simulated) showed zero request failures and stable throughput around 4 requests per second with median response times stabilizing around 200–300 ms after initial warm-up.
- Under volumetric HTTP flood simulation (using HOIC tool), CAHICHA blocked all automated attack traffic at proxy layer, allowing zero bot requests through to backend server.
- User accessibility testing with 64 participants showed over 59% rated web experience as 5/5 and 61% rated mobile experience as 5/5; 64% highly recommended CAHICHA over existing CAPTCHA systems.
- CAHICHA in strict mode validates hardware via FIDO Metadata Service, ensuring only certified authenticators are accepted, increasing security assurances against fake devices.
- In general mode, CAHICHA still requires physical user interaction (User Presence flag) but accepts any authenticator, trading off some security for broader compatibility.
- Feature comparison table shows CAHICHA has zero false positives vs high false positive rates on behavioral CAPTCHAs and AI spoofing vulnerabilities on reCAPTCHA and hCaptcha.
- CAHICHA’s encryption and token issuance use AES-CBC with Fernet format and HttpOnly, Secure cookies for secure session validation.
Threat model
The adversary is an automated bot or AI-powered script capable of mimicking human browser interactions, solving visual CAPTCHA challenges, and scripting behavioral patterns. The adversary lacks the ability to perform trusted hardware-mediated physical interactions required by FIDO2/WebAuthn authenticators (such as PIN entry, biometric scan, or touch sensor activation) and cannot forge or bypass cryptographically attested User Presence flags. The attacker also cannot easily deploy large-scale robotic setups that physically manipulate users' devices at scale, making automated large-volume attacks costly and complex.
Methodology — deep read
Threat Model & Assumptions: The adversary is an automated bot or AI-powered script capable of mimicking human browsing, mouse movement, typing, cookie management, and solving traditional CAPTCHAs. They do not have access to interact physically with hardware-level authenticators or spoof the cryptographically protected User Presence (UP) and User Verification (UV) flags generated by hardware security modules or TPMs. Attackers cannot easily simulate physical PIN input, biometric scans, or touch sensor activation tied to trusted hardware.
Data: The system operates on live web user interactions; no public dataset was used. User actions such as touches, PIN entries, or biometric scans are processed by client authenticators (hardware security keys or platform TPMs) and cryptographically attested to the server. Usability data from a 64-participant User Accessibility Test was collected to evaluate the human experience.
Architecture/Algorithm: CAHICHA deploys as a reverse proxy server that intercepts client requests to a web app. Upon initial visit, it issues a WebAuthn credential creation challenge with UP and UV flags set to 'required'. The client browser invokes Navigator.credentials.create(), triggering the authenticator device to require a physical user action (e.g., biometric scan, PIN entry, touch) to generate attested credential data containing RP ID hash, flags including User Presence bit, counters, and attestation certificates. This challenge-response uses public-key signatures and FIDO metadata to verify authenticator legitimacy (in strict mode). The proxy validates the response (signature, challenge binding, attestation chain), and on success issues a cryptographically encrypted session token (Fernet style AES-CBC) in an HttpOnly, Secure cookie.
Training Regime: Not applicable—system is protocol and hardware-based rather than machine learning.
Evaluation Protocol: The authors conducted load testing using Locust to simulate concurrent users and measure request failures, throughput, and response time distributions over 10-minute periods. Stress testing used HOIC to emulate volumetric HTTP floods, monitoring for request failures or server degradation. Usability evaluation surveyed 64 participants on both web and mobile platforms regarding speed, ease of use, and recommendation likelihood. A detailed feature comparison with traditional CAPTCHA systems was also performed. The system was tested in two deployment modes: strict and general, with differing levels of attestation validation.
Reproducibility: No public code or dataset release is mentioned. The method relies on standards-compliant hardware authenticators and FIDO alliance services. Deployment as a proxy simplifies integration without changes to existing website code.
Example workflow: When a new client request arrives, the proxy checks for a verification cookie; if absent, it sends a WebAuthn credential creation request requiring user presence and verification flags. The browser prompts the user to physically interact with their authenticator (touch button, fingerprint scan, PIN input). The authenticator signs a challenge including embedded RP ID and user presence flags. The proxy verifies the signature and attestation against trusted metadata, issues a time-limited encrypted session cookie, and allows client requests to pass. Bots unable to complete physical hardware interactions cannot produce valid attestation responses and are blocked at the proxy.
Overall, the methodology innovatively applies existing FIDO2/WebAuthn standards beyond authentication into bot detection by leveraging hardware-rooted cryptographic attestations of genuine human physical interaction.
Technical innovations
- Leveraging cryptographically attested User Presence (UP) flags from hardware authenticators as a deterministic bot detection signal.
- Deploying a proxy-based WebAuthn challenge system requiring physical hardware interaction (PIN, biometrics, touch) without website code modification.
- Utilizing strict attestation verification with FIDO Metadata Service (MDS v3) to vet authenticators and prevent fake or software-based devices.
- Issuing short-lived cryptographically encrypted session tokens as HttpOnly cookies to maintain stateful verification across requests.
- Introducing dual deployment modes (strict and general) balancing security rigor and compatibility.
Datasets
- User Accessibility Test (UAT) — 64 participants — internal experimental data
Baselines vs proposed
- reCAPTCHA v3: Average time 4–10 seconds vs CAHICHA: ~12 milliseconds challenge time
- hCaptcha: Average completion ~19 seconds vs CAHICHA: ~12 milliseconds
- ReCAPTCHA and hCaptcha: High false positive rates with sophisticated AI bots vs CAHICHA: Zero false positives in strict mode
- Behavioral CAPTCHAs: Spoofable by advanced AI vs CAHICHA: Deterministic hardware interaction verification
Figures from the paper
Figures are reproduced from the source paper for academic discussion. Original copyright: the paper authors. See arXiv:2511.07841.
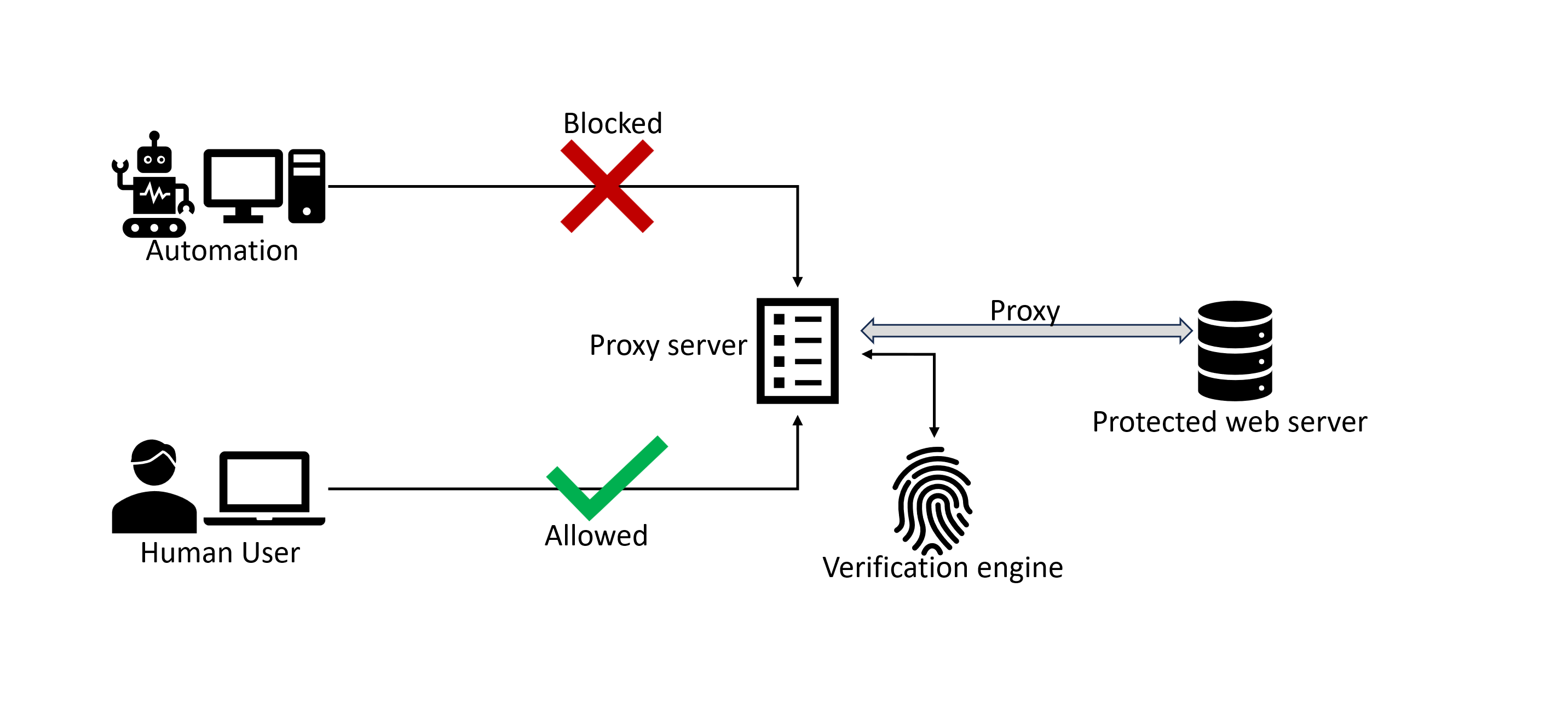
Fig 1: Workflow of CAHICHA
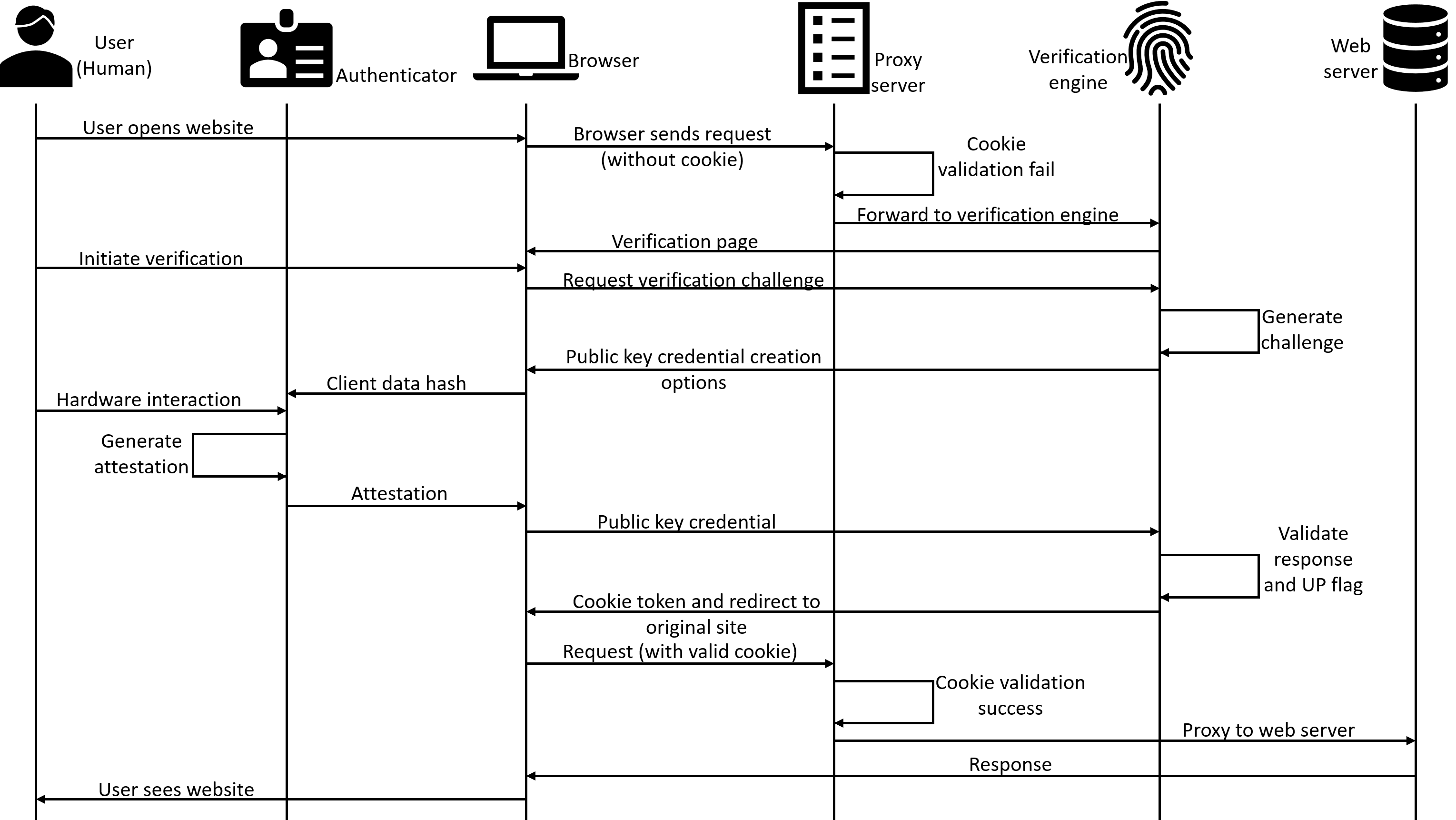
Fig 2: Sequential Diagram of CAHICHA
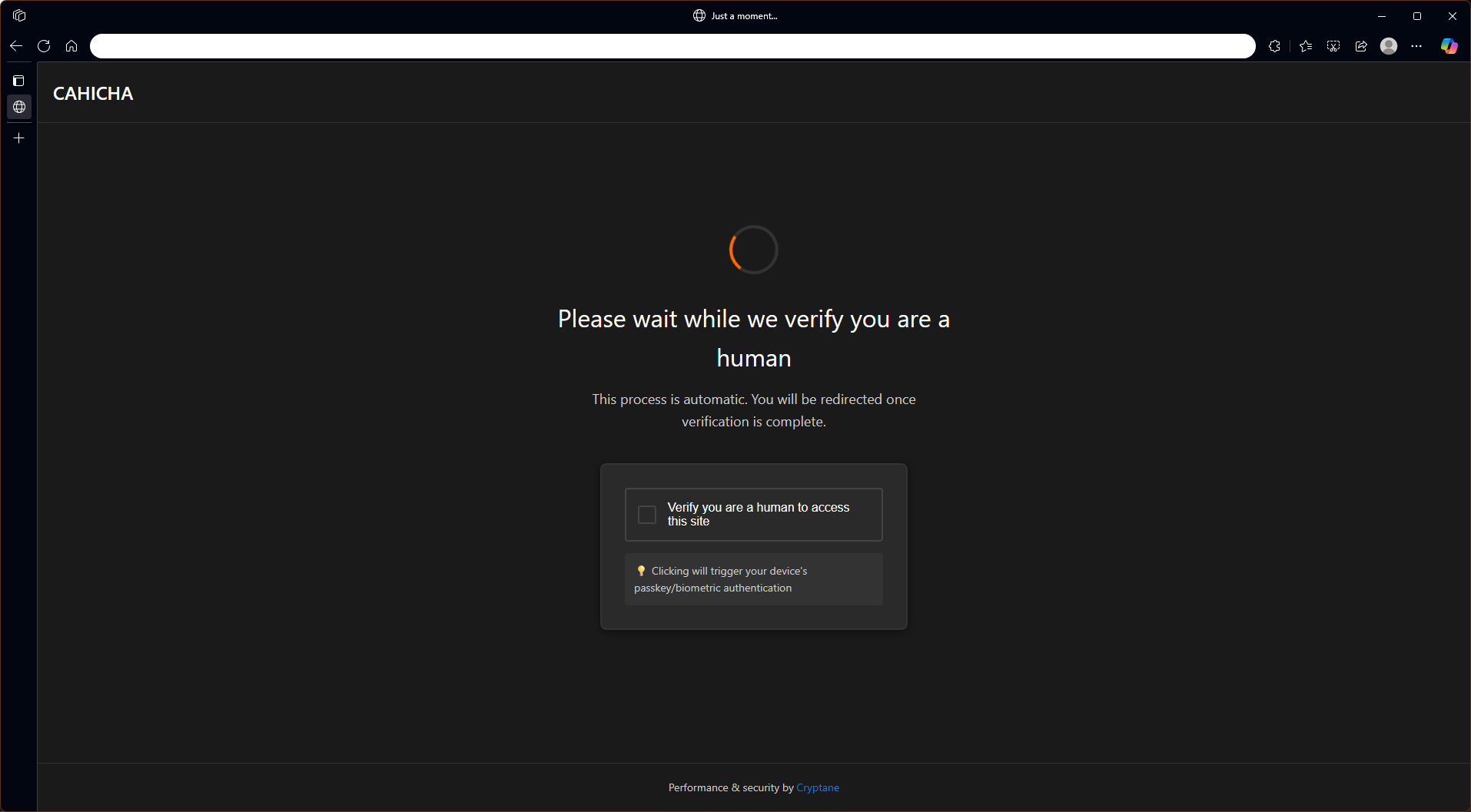
Fig 3: CAHICHA Login Verification Interface
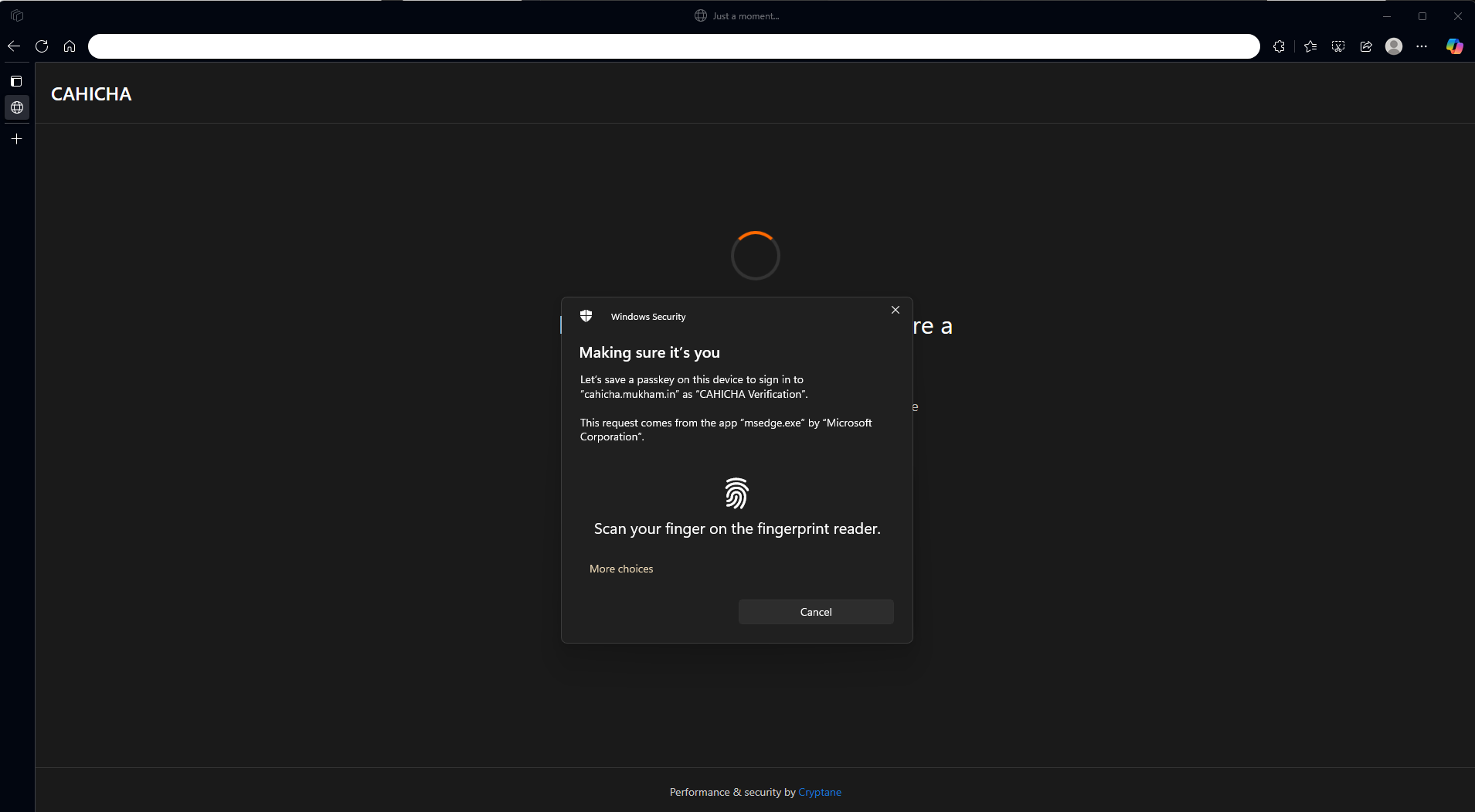
Fig 4: Biometric Verification for Human Authentication
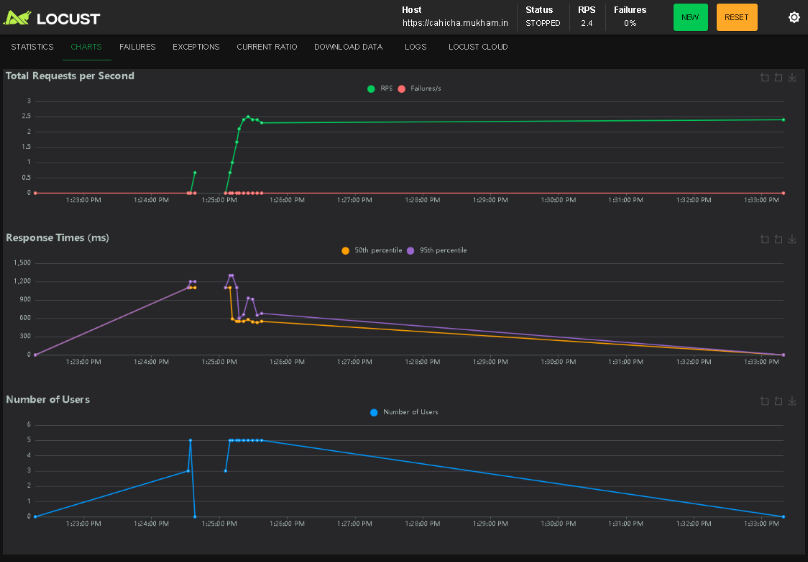
Fig 5: Load Test Result using Locust
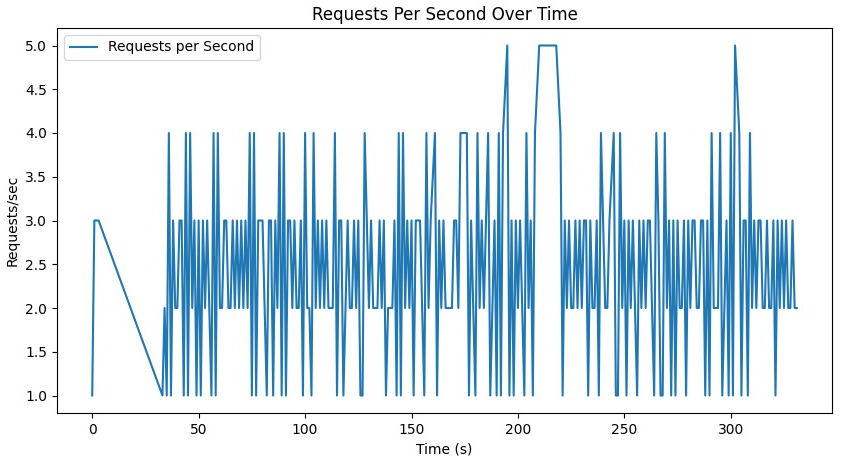
Fig 6: System Performance Metrics Over Time
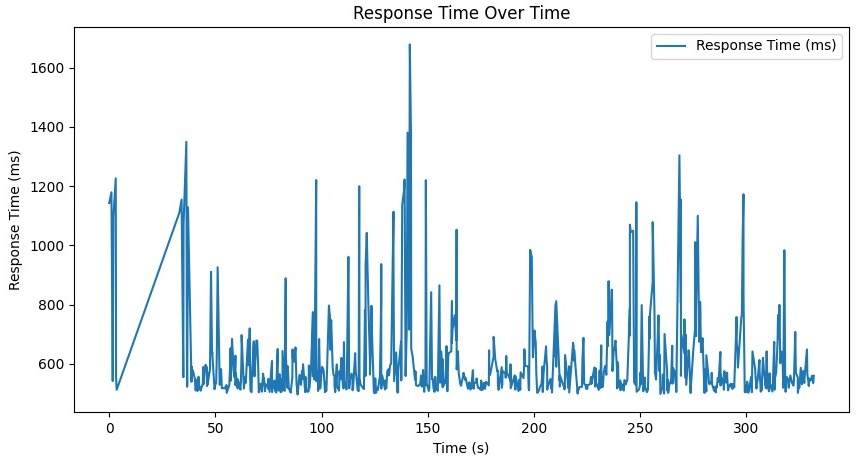
Fig 7: System Performance Metrics Over Time
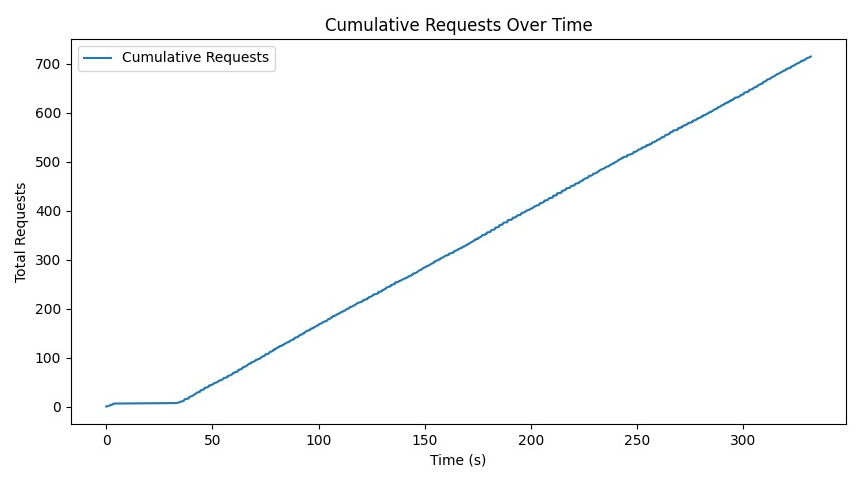
Fig 8: System Performance Metrics Over Time
Limitations
- The system depends on user devices having compatible hardware authenticators (security keys or TPMs), which may limit broader adoption, especially on older or low-end devices.
- In general mode, allowing non-certified authenticators may open avenues for hardware-level attacks or fake authenticators to bypass verification.
- No adversarial machine learning or dedicated bot attack modeling was reported beyond volumetric HTTP flood stress testing.
- The experimental deployment was limited to a single VPC instance and simulated user counts; large-scale, real-world internet deployment impacts remain to be studied.
- Accessibility improvements are needed for users with disabilities who might have difficulty completing certain hardware interactions like biometric scans.
- No detailed analysis of latency impact or additional user friction in diverse network conditions beyond controlled testing was provided.
Open questions / follow-ons
- How effective is CAHICHA against semi-automated attacks that combine remote scripting with occasional human interaction (e.g., click farms or human solvers)?
- What is the impact on adoption and usability among users without hardware authenticators or on platforms not supporting WebAuthn hardware security keys robustly?
- How resilient is CAHICHA to emerging hardware-level attacks or cloning of FIDO authenticators, including attempts to bypass attestation mechanisms?
- Can this hardware interaction verification approach be extended and adapted to mobile, IoT, or edge scenarios with constrained hardware?
Why it matters for bot defense
CAHICHA offers a compelling alternative to purely software or behavioral CAPTCHA challenges by requiring cryptographically attested physical user interactions tied to hardware authenticators (e.g., TPMs or security keys). This elevates defense capabilities beyond visual or behavioral heuristics that AI-driven bots can imitate or solve. Bot-defense engineers can leverage CAHICHA as a proxied verification layer to harden critical endpoints against automated abuse without significantly impacting legitimate user experience due to its fast challenge completion times (~12 ms).
However, the approach is not a universal drop-in replacement; it requires infrastructure to support WebAuthn and client devices with compatible hardware. It also necessitates consideration around accessibility and fallback modes for users lacking hardware authenticators. Skilled attackers with access to specialized hardware or human-in-the-loop setups may still pose risks, but CAHICHA raises the cost and complexity of automation significantly. In bot defense strategies, integrating hardware-attested presence verification complements existing CAPTCHA systems by providing a deterministic, cryptographically verifiable signal of genuine human interaction that is currently difficult to emulate at scale.
Cite
@article{arxiv2511_07841,
title={ CAHICHA: Computer Automated Hardware Interaction test to tell Computer and Humans Apart },
author={ Aditya Mitra and Sibi Chakkaravarthy Sethuraman and Devi Priya V S },
journal={arXiv preprint arXiv:2511.07841},
year={ 2025 },
url={https://arxiv.org/abs/2511.07841}
}