Secure Authentication in Wireless IoT: Hamming Code Assisted SRAM PUF as Device Fingerprint
Source: arXiv:2604.15810 · Published 2026-04-17 · By Florian Lehn, Pascal Ahr, Hans D. Schotten
TL;DR
This paper addresses the challenge of reliable and resource-efficient device authentication in constrained Industrial Internet of Things (IIoT) scenarios using SRAM Physically Unclonable Functions (PUFs). While SRAM PUFs provide unique hardware fingerprints derived from intrinsic manufacturing variations, their responses suffer from inherent noisiness causing bit errors that threaten usability and security. To address this, the authors propose a combined approach using simple Hamming code (HC) error correction (EC) and Temporal Majority Voting (TMV) to stabilize PUF responses, enabling a threshold-based authentication scheme. They implement and evaluate this on ESP32-S3 microcontrollers, demonstrating the ability to keep post-authentication bit error rate (BER) below 1% with a calibrated acceptance threshold. Moreover, they thoroughly analyze the design trade-offs between reliability, computational overhead, memory/storage requirements, and security.
Key findings
- Post-authentication BER can be reliably capped below 1% using a combination of Hamming code EC and Temporal Majority Voting (TMV).
- Increasing either TMV count or HC redundancy reduces BER with diminishing returns, especially beyond about 5 votes for TMV.
- SECDED codes reduce syndrome aliasing miscorrections compared to SEC-only codes, narrowing BER variance by suppressing triple-bit flip miscorrections.
- Smaller HC blocks (e.g. H(7,4)) achieve lower BER but incur higher helper data overhead: e.g., 1536 parity bits added for 256-byte responses, vs 640 bits for H(21,16).
- TMV via repeated boot cycles dominates computational overhead versus HC EC computation, with execution time growing linearly in TMV count N (e.g., up to hundreds of milliseconds with 20 votes).
- Authentication acceptance threshold calibration leveraging an analytical impostor model establishes a security margin (SMec) that quantifies the safe operating window balancing False Acceptance Rate (FAR) and False Rejection Rate (FRR).
- Scaling the PUF response length n from 64 to 2048 bits improves the security margin SMec by approximately 28%, a larger effect than varying TMV count or HC redundancy.
- A design budget approach is proposed that actively trades off reliability (BER), computational overhead, and memory to meet strict FAR/FRR constraints for resource-constrained IIoT.
Threat model
Adversaries are remote attackers attempting to impersonate legitimate devices by forging or predicting PUF responses and possibly accessing public helper data. They cannot physically clone the device or perfectly model the PUF due to inherent manufacturing variations and noise. Side-channel or invasive attacks are outside the scope. Security assumes helper data leakage does not enable effective response prediction beyond modeled assumptions.
Methodology — deep read
The authors consider a threat model where adversaries attempt impersonation but cannot perfectly replicate or predict the SRAM PUF response, relying on helper data security assumptions. The primary challenge is the inherent unreliability (bit flips) in SRAM startup patterns due to environmental and hardware noise.
The experimental data comprises SRAM startup values captured on six ESP32-S3 MCUs running FreeRTOS in a controlled climate chamber (21°C, 50% humidity). Each device's SRAM PUF response is 2048 bits long. For smaller effective PUF sizes, the baseline 2048-bit response is partitioned into equal blocks to gain more samples. Enrollment and authentication each have 45 measurements per device, with aggregated results pooled for analysis.
The core authentication scheme combines TMV and HC error correction. TMV obtains N independent SRAM reads, each separated by deep sleep power cycling of SRAM to mitigate correlated noise, accumulating bitwise tallies stored in RTC memory and thresholded at the halfway point (N/2) to finalize stable bits. HC error correction is applied on the fly during authentication using stored parity helper data saved in non-volatile storage (NVS). Multiple HC variants are tested, including Single Error Correction (SEC) and Single Error Correction Double Error Detection (SECDED) codes with various block sizes (e.g., H(7,4), H(21,16)).
The enrollment phase consists of capturing N SRAM PUF readings to generate a stable enrolled response R, encoding R with HC to generate parity bits as helper data stored in flash. Authentication repeats the N SRAM reads to generate r', reconstructs codewords with stored parity, and applies syndrome-based HC decoding to recover R'. The bit error rate (BER) between R and R' measures accuracy.
Training per se is not applicable; rather, the design space is explored empirically by varying N, HC code parameters, and PUF response length. Execution time measurements approximate computational overhead.
Evaluation metrics include BER after error correction, uniformity (bit bias) of responses, False Acceptance Rate (FAR) modeled analytically via Binomial distributions assuming bit independence and uniform probability p=0.5 for impostors, and False Rejection Rate (FRR) from empirical genuine authentication attempts. The authentication threshold τBER discriminates acceptance/rejection. Analytical and empirical curves characterize the trade-off between FAR and FRR to define a security margin SMec = τmax - τmin, quantifying the feasible acceptance threshold range.
The authors provide detailed time breakdowns separating SRAM reads, TMV voting, HC computation, and NVS helper data access. They instrument the ESP32 environment to enable repeatable SRAM PUF reading by pinning PUF memory to a noinit section and zeroing SRAM prior to deep sleep cycles.
No code release is mentioned. The dataset is private, derived from the six ESP32 entities in-house. The analytical FAR impostor model provides reproducibility for security margin analysis. The work carefully aligns the practical constraints of the IIoT environment—low power, limited memory, constrained MCU—with the implementation complexity and reliability requirements.
A concrete example flow: Enrollment captures SRAM PUF startup response 20 times, tallies bit values temporally to choose stable bits, computes parity for H(7,4) HC codes over 2048-bit response, storing 768 parity bits in NVS. Authentication repeats 20 reads generating noisy r' responses, reconstructs codewords by combining r' with stored parity to correct single errors, computes BER with respect to R, and compares against τBER=3% acceptance threshold for deciding authentication success.
Overall, the methodology rigorously quantifies trade-offs inherent to practical SRAM PUF authentication on resource-limited wireless IoT devices with carefully instrumented hardware experiments supported by analytical impostor modeling.
Technical innovations
- Integration of Hamming code (HC) error correction with Temporal Majority Voting (TMV) for resource-efficient SRAM PUF response stabilization tailored to constrained IIoT devices.
- Quantitative introduction of a security margin (SMec) metric that captures the operating window bounded by FAR and FRR constraints, reframing threshold calibration as a design budget for resource optimization.
- Empirical comparative assessment of multiple HC variants (SEC and SECDED) with detailed trade-off analysis between error correction capabilities, helper data storage overhead, and computational cost on real MCU hardware.
- Implementation of TMV via power-cycled deep sleep to achieve independent SRAM PUF samples, alongside practical memory management for stable and repeatable PUF extraction within MCU startup sequences.
Datasets
- SRAM PUF startup responses from 6 ESP32-S3 devices — 2048 bits per response — proprietary in-house dataset collected under controlled conditions (21°C, 50% RH).
Baselines vs proposed
- No ECC: post-correction BER median above 5% at low TMV vs H(7,4) HC reduces BER to below 1% at N=20 TMV votes.
- H(7,4) SECDED: execution time overhead approx 1-2 ms without TMV, TMV increases execution time linearly reaching several hundred ms at N=20.
- H(22,16) SECDED code rate ~81% helper data overhead lower than smaller block HCs but yields higher residual BER (~2-3% vs. <1% for H(7,4)).
- Increasing TMV N from 1 to 20 reduces median BER approximately 60-80% for all HC variants, with diminishing returns beyond N=5.
- FAR modeled analytically for impostor follows binomial distribution offering extreme separation from genuine FRR when n=2048; FAR ≤ 10⁻⁹ at τmax=43.4%, FRR ≤1% at τmin=0.6%-2.3% depending on HC variant.
- Scaling PUF size from 64 to 2048 bits improves security margin SMec by ~28%, outweighing gains from increasing TMV votes or HC redundancy.
Figures from the paper
Figures are reproduced from the source paper for academic discussion. Original copyright: the paper authors. See arXiv:2604.15810.
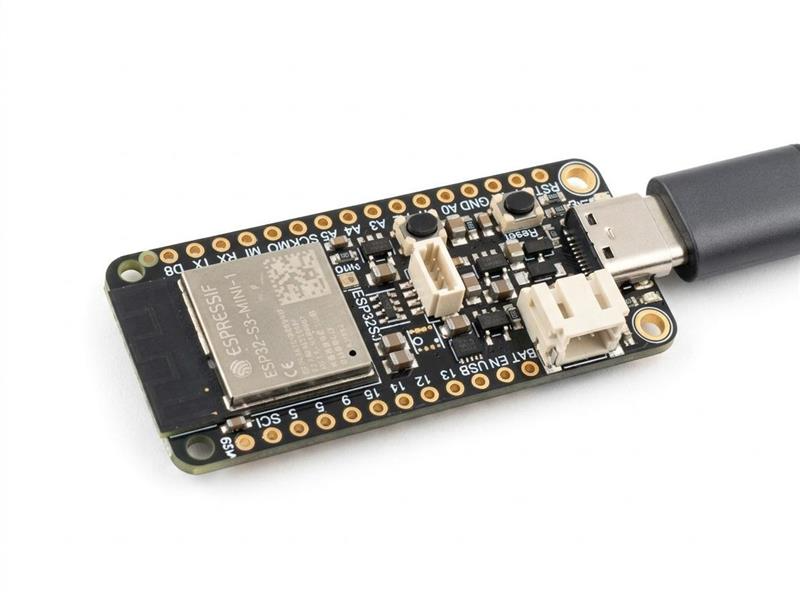
Fig 1: Sequence diagram of the PUF-based authentication

Fig 2: Experimental setup for measurements within a CTS
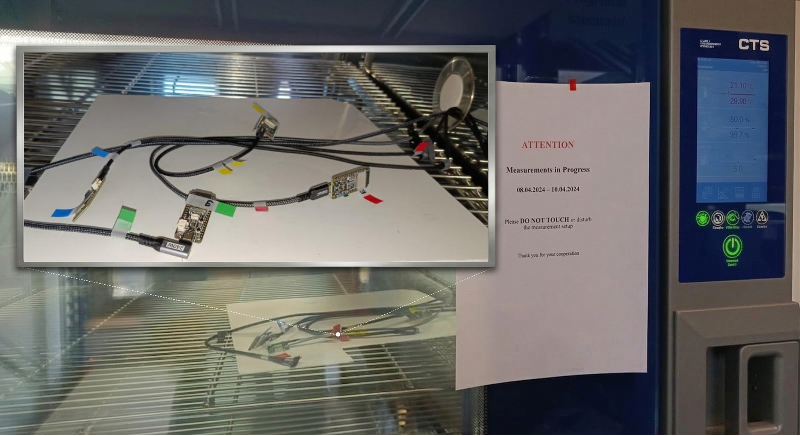
Fig 3: Uniformity distributions per measured ECC scheme
Limitations
- Empirical False Acceptance Rate (FAR) evaluation is not performed; relies on idealized analytical impostor model assuming perfect bit independence and uniformity.
- Dataset limited to six ESP32-S3 microcontrollers; results may not generalize across wide chip populations or different SRAM architectures.
- Environmental influence tests limited to stable controlled temperature/humidity; no evaluation under diverse or extreme operating conditions.
- Energy consumption is approximated by execution time without direct power measurements; actual battery life impact remains unquantified.
- Helper data leakage and security vulnerabilities from parity storage are acknowledged but not mitigated or experimentally evaluated here.
- No explicit adversarial robustness tests against modeling attacks or physical tampering on the PUF.
Open questions / follow-ons
- How does environmental variation (temperature, voltage) affect the scheme’s reliability and security margin in real deployment?
- What are practical countermeasures to protect helper data leakage and resist machine learning modeling attacks?
- Can more advanced error correcting codes or alternative PUF stabilization approaches realize better trade-offs within the IIoT resource constraints?
- How does the authentication performance and security scale when tested on a larger, more diverse chip population?
Why it matters for bot defense
This work provides important insights for bot-defense engineers designing hardware-rooted authentication solutions on resource-constrained IoT devices incorporating PUFs. The combined TMV and lightweight HC approach offers a pragmatic path to mitigating PUF noise while balancing latency, computational load, memory overhead, and security guarantees. The concept of framing threshold calibration as a resource budgeted design problem could be adapted to tune challenge-response verification thresholds in CAPTCHA or bot-detection systems to optimize false positive/negative trade-offs under usage constraints. However, the reliance on strong assumptions for false acceptance modeling highlights the need for empirical adversarial evaluations before deployment in adversarial bot-defense contexts. Overall, the study advances understanding of how to operationalize noisy hardware fingerprints reliably in constrained wireless environments, a growing concern in securing Internet-of-Things endpoints from spoofing or automation attacks.
Cite
@article{arxiv2604_15810,
title={ Secure Authentication in Wireless IoT: Hamming Code Assisted SRAM PUF as Device Fingerprint },
author={ Florian Lehn and Pascal Ahr and Hans D. Schotten },
journal={arXiv preprint arXiv:2604.15810},
year={ 2026 },
url={https://arxiv.org/abs/2604.15810}
}