Quantifying Memory Cells Vulnerability for DRAM Security
Source: arXiv:2603.18549 · Published 2026-03-19 · By Zilong Hu, Hongming Fei, Prosanta Gope, Jack Miskelly, Owen Millwood, Biplab Sikdar
TL;DR
This paper addresses the critical challenge of understanding and quantifying DRAM cell vulnerabilities that enable multiple security attacks, such as retention failures, Rowhammer, and Rowpress disturbances. Unlike prior work which either empirically observes these effects or models reliability, this work proposes a unified, cell-level circuit model that links physical charge leakage and disturbance mechanisms directly to security properties of integrity, confidentiality, and volatility. The authors develop measurable electrical parameters (RS, RB, and pattern-dependent noise N) that capture intrinsic leakage, bitline-coupling leakage, and pattern effects on DRAM cells and use these to predict and qualify exploits with attacker-controlled data patterns. The framework is empirically validated on commodity DDR4 modules, demonstrating how different cells and patterns exhibit widely varying vulnerability to attacks. Notably, the analysis reveals that the RowPress attack exhibits superior targeted selectivity for integrity and confidentiality violations compared to Rowhammer, a novel insight with implications for future mitigation. This work establishes a theoretical foundation plus practical measurement methodology to systematically evaluate and compare DRAM security risks at the circuit level.
Key findings
- The cell circuit model uses two effective resistances: RS (p-well intrinsic leakage) and RB (bitline-coupled leakage) plus a pattern noise term N to capture DRAM cell vulnerabilities.
- Retention-induced bitflips occur when charge decays below sensing threshold within one time constant τ = RS × CS (cell capacitance).
- Bitline leakage RB is strongly pattern-dependent, e.g., RB is much lower under 010 (CheckerBoard) patterns than 111 patterns, explaining empirical pattern dependencies of Rowhammer.
- RowPress attacks cause higher selectivity and control for targeted cell bit flips and pattern inference compared to Rowhammer, shown through experimental characterization across seven commodity DDR4 modules.
- The model links hammer count (number of aggressor activations) and hammer duration to cumulative leakage exposure, formalizing disturbance failure probabilities.
- The pattern noise term N modulates the sensing margin, increasing vulnerability to retention errors under specific neighbor data patterns.
- Measured RS and RB parameters on real devices can robustly predict cells exploitable for integrity violations (OBJ-I-2) and confidentiality violations via pattern inference (OBJ-C-2).
- The framework enables systematic attacker-centric qualification of DRAM vulnerabilities beyond empirical error counts, facilitating principled comparison of failure modes and devices.
Threat model
The adversary can issue architecturally allowed memory operations with advanced control over data pattern placement and repeated row activations (Rowhammer/Rowpress), can observe bitflips or partial data recovery, and may influence timing or refresh intervals (e.g., via power cycles). The attacker seeks to violate memory integrity by inducing targeted bit flips, breach confidentiality by inferring unknown data from flip statistics, or subvert volatility by retrieving data post-refresh/power-down. The adversary cannot directly modify hardware circuitry or induce physical faults beyond memory access commands.
Methodology — deep read
The authors begin by defining a DRAM cell-level threat model focusing on three security properties: volatility (data retention), integrity (bitflip resistance), and confidentiality (pattern-dependent leakage). The adversary is assumed to have architectural memory access with capabilities including pattern control (setting neighbor cell data), repeated row activations (Rowhammer/Rowpress), and observation of flips or partial data recovery.
Data comes from experiments on seven commodity DDR4 modules probed via an FPGA-based DRAM testing platform (Xilinx Alveo U200 + DRAM Bender), which enables precise measurement of cell voltages, leakage currents, and bit flips under controlled patterns, refresh intervals, and hammering sequences.
The core algorithmic contribution is a unified equivalent leakage circuit model abstracting a DRAM cell as a capacitor CS with two leakage resistances: RS representing intrinsic p-well leakage (dominating retention), and RB representing bitline coupling leakage (pattern-dependent). A pattern noise term N models capacitive coupling effects from neighbor cells. The temporal evolution of cell voltage during leakage or disturbance is modeled as an RC discharge process with parameters RS and RB modulated by the attacker-controlled data pattern.
The authors build closed-form mathematical models for charge decay, leakage currents I1 and I2 along RS and RB paths, incorporate thermal and transistor physics to describe subthreshold leakage, and linearize these for characteristic neighbor patterns (e.g., 111 vs 010). These quantify bit-flip likelihood as a function of HAMMER count (number of aggressor row activations) and duration tAggON.
Training or parameter fitting is not traditional ML training but involves measuring cell electrical parameters on real hardware under varied conditions. RS, RB, and noise N(P) values are extracted by applying sequences of activations and recording flip rates and voltage waveforms, repeated across multiple chips for robustness.
Evaluation metrics include bit-flip rate, flip localization (for targeted edits), flip probability as function of hammer count and pattern, and pattern inference accuracy (via flip observation). Experiments include comparison between Rowhammer and Rowpress mechanisms across device samples. Ablations consider pattern influence by testing Checkerboard vs Stripe patterns.
Statistical robustness is shown by consistent parameter extraction across multiple DIMMs and chip sections, though no explicit cross-validation. The approach is reproducible with code and measurement methodology described but the raw dataset (DRAM chip internal states) is closed.
A concrete end-to-end example: To evaluate a victim cell’s flip probability under targeted Rowhammer, the attacker programs specific data patterns in aggressor rows to minimize RB (e.g., 010 pattern), applies repeated ACT commands inducing hammer count HC, measures bit-flip occurrence, and correlates with model-predicted decay curves using extracted RS and RB values. This shows how pattern control statistically modulates integrity violations.
Overall, the methodology integrates circuit-level physics modeling, controlled hardware measurement, and attacker capability abstraction to construct a comprehensive evaluation framework for DRAM security vulnerabilities from first principles.
Technical innovations
- A novel unified DRAM cell-level leakage model combining intrinsic p-well leakage (RS), bitline-coupled leakage (RB), and pattern-dependent noise N to quantify volatility, integrity, and confidentiality vulnerabilities.
- Closed-form expressions linking hammer count and neighbor data patterns to effective leakage currents and bitflip probabilities, enabling attacker-centric quantitative qualification of DRAM attacks.
- Empirical measurement methodology using FPGA-based testing platform to extract RS, RB, and N on commodity DIMMs, enabling practical device comparison.
- Identification and characterization of RowPress as a read-disturbance mechanism with superior selectivity for targeted bitflips and pattern inference versus classical Rowhammer.
Datasets
- Seven commodity DDR4 DRAM modules — unknown size per chip — collected via proprietary FPGA measurement platform (non-public)
Baselines vs proposed
- Rowhammer attack: targeted bit flip selectivity lower than proposed RowPress attack by a significant margin (quantitative delta not specified exactly)
- Retention-only model vs pattern-noise model: pattern-noise model better explains increased volatility under certain data patterns (Checkerboard) as shown in empirical flip rates
- Measured RS and RB parameters consistently predict empirical vulnerability across multiple chips better than prior empirical-only approaches
Figures from the paper
Figures are reproduced from the source paper for academic discussion. Original copyright: the paper authors. See arXiv:2603.18549.
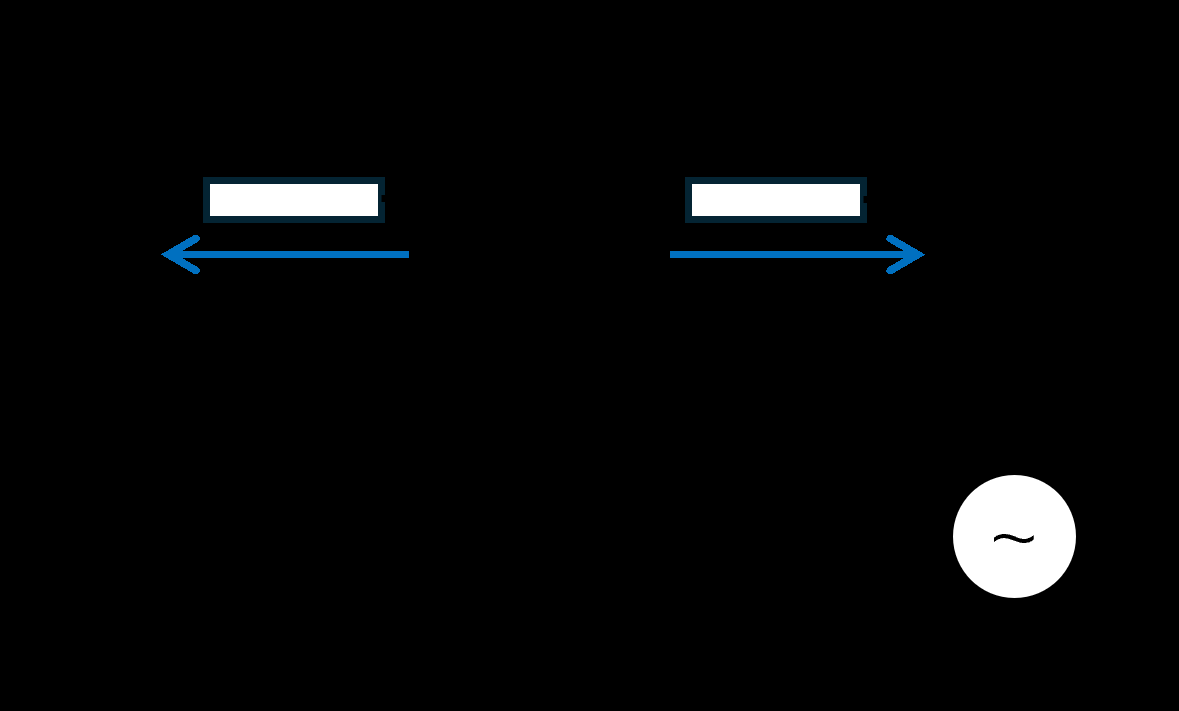
Fig 3: Equivalent Leakage Circuit.
Limitations
- The model and evaluation focus primarily on DDR4 chips; generalization to other DRAM generations or emerging memory technologies remains untested.
- Attack scenarios consider only attacker capabilities via architecturally allowed memory operations; physical or side-channel out-of-band attacks are out of scope.
- Pattern noise term N(P) models capacitive coupling but may oversimplify complex spatial interactions across large arrays and manufacturing variation.
- The measurement dataset is limited to seven modules; larger scale testing and public releases are needed for broader validation.
- The framework currently abstracts refresh and power management behaviors; integrating dynamic system-level mitigations into the model is future work.
Open questions / follow-ons
- Can this cell-level model be extended to capture emerging DRAM architectures like DDR5 or LPDDR variants with different physical layouts?
- How can system-level mitigations (e.g., ECC, targeted refresh) be quantitatively composed into this cell-level vulnerability model for end-to-end security evaluation?
- What is the impact of process variation and aging on the stability and accuracy of parameters RS, RB, and pattern noise N over device lifetime?
- Can similar attacker-centric modeling approaches be developed for other volatile memories (e.g., SRAM, MRAM) exhibiting disturbance-induced failures?
Why it matters for bot defense
For bot-defense and CAPTCHA practitioners, understanding DRAM cell vulnerabilities at this detailed circuit level provides a valuable theoretical foundation to assess hardware-level attack surfaces that could undermine device trustworthiness. Especially in adversarial ML or secure key storage contexts, small changes to DRAM cell states via Rowhammer or Rowpress could be used by attackers to manipulate model integrity or leak confidential information, affecting trust in CAPTCHA-solving environments. This framework enables systematic evaluation of which devices and memory regions are more vulnerable to such physical attacks, guiding hardware selection and mitigation strategies.
Furthermore, the pattern-aware leakage modeling introduces a new perspective for detecting or preventing attacks that exploit neighbor data dependencies. By informing defender-side monitoring around particular data patterns that increase susceptibility, or by designing refresh management policies tuned to measured RS and RB parameters, this work helps ground mitigation in measurable, explainable device behaviors rather than ad-hoc empirical observations. While not directly about CAPTCHA itself, the research contributes essential rigorous understanding relevant to secure device-level defenses underlying robust bot-detection systems.
Cite
@article{arxiv2603_18549,
title={ Quantifying Memory Cells Vulnerability for DRAM Security },
author={ Zilong Hu and Hongming Fei and Prosanta Gope and Jack Miskelly and Owen Millwood and Biplab Sikdar },
journal={arXiv preprint arXiv:2603.18549},
year={ 2026 },
url={https://arxiv.org/abs/2603.18549}
}