CSI-RFF: Leveraging Micro-Signals on CSI for RF Fingerprinting of Commodity WiFi
Source: arXiv:2602.22738 · Published 2026-02-26 · By Ruiqi Kong, He Chen
TL;DR
This paper addresses the challenge of authenticating commodity WiFi devices using physical-layer fingerprints extracted from Channel State Information (CSI). Unlike prior RF fingerprinting approaches that require expensive measurement equipment capturing raw physical-layer signals, CSI is readily available on commodity off-the-shelf (COTS) WiFi devices and thus offers a practical fingerprinting avenue. The novel insight is the identification of subtle micro-signals, termed micro-CSI, embedded within the CSI that arise primarily from hardware imperfections in the WiFi radio-frequency (RF) circuitry. These micro-CSI distortions are device-specific and remain stable over long periods, making them suitable for fingerprinting.
The authors develop a signal space-based method to disentangle these micro-CSI fingerprints from the confounding wireless channel distortions, focusing on strong line-of-sight (LoS) scenarios. Extensive real-world experiments across 15 WiFi 4/5/6 devices over a 14-month period demonstrate that micro-CSI fingerprints are unique, time-invariant, and robust even in mobile conditions. The CSI-RFF framework achieves an average attack detection rate close to 99% with zero false alarms using only 20 CSI measurements per fingerprint. A practical case study on mobile robot access control confirms the method’s feasibility and effectiveness in operational scenarios.
Key findings
- Micro-CSI originates from RF circuitry imperfections rather than noise, channel multipath, or CSI tool artifacts (Fig 1c).
- Micro-CSI can be reliably extracted by averaging groups of CSI measurements and applying signal space separation under strong LoS.
- CSI-RFF achieves ~99% average attack detection rate (ADR) and 0% false alarm rate (FAR) in both static and mobile conditions using 20 CSI samples.
- Micro-CSI fingerprints show stability and time-invariance over 14 months of data collection.
- CSI-based fingerprints require 100x fewer CSI measurements than prior CSI+network-layer approaches while improving FAR from 4.3% to 0%.
- Single-antenna transmitter and SIMO receiver setups stabilize and isolate micro-CSI fingerprints effectively.
- Receiver chains produce negligible micro-CSI differences within the same device, enabling multiple CSI links to improve noise suppression.
- Robotic use case with 15 NICs validates practical authenticity verification in real indoor LoS environments.
Threat model
The adversary attempts to gain unauthorized network access by impersonating legitimate WiFi NICs. They may inject forged packets or spoof device MAC addresses but cannot perfectly replicate or emulate the unique micro-CSI caused by hardware imperfections of the target devices. The adversary is assumed unable to physically clone or precisely mimic the intrinsic RF distortions embedded within CSI. The authentication system assumes strong line-of-sight and stable channel conditions to enable fingerprint separation. High-power jamming, advanced hardware trojans, or channel manipulation attacks are out of scope.
Methodology — deep read
The authors target open-set authentication of COTS WiFi devices by extracting device-specific micro-signals (micro-CSI) embedded in CSI amplitude and phase curves.
Threat Model & Assumptions: The adversary is an attacker attempting unauthorized network access spoofing legitimate WiFi NICs. The attacker cannot perfectly replicate device-specific hardware imperfections that cause micro-CSI fingerprints. The work assumes strong line-of-sight (LoS) wireless channels to enable disentangling channel and hardware distortions, representing static or controlled indoor environments.
Data Collection: Data is collected from 15 WiFi NICs spanning WiFi 4, 5, and 6 standards, from multiple vendors (e.g., Espressif, Atheros, Intel, Realtek). Measurements include static and mobile robot scenarios in indoor LoS settings. CSI is collected using software-defined radio (SDR) hardware with customized tools to capture CSI from ACK packets, which have fixed single-antenna transmitter chains even in MIMO NICs. Over 14 months, multiple groups of CSI measurements are recorded (e.g., groups of 20, 50, or 100 consecutive CSI samples) to average out noise and channel fluctuations.
Architecture / Algorithm:
- The key innovation lies in modeling the CSI measurement as a convolution of the channel impulse response and a hardware distortion term (micro-CSI) in time/frequency domains.
- Under strong LoS, the channel impulse response is sparse with limited taps, allowing least squares projection to isolate the channel component from the frequency domain CSI.
- The residual component after dividing out the channel estimate corresponds to micro-CSI, a device-specific distortion vector.
- To suppress noise and outliers, micro-CSI is extracted by averaging multiple CSI samples and applying normalization techniques.
Training Regime: The authors do not train a deep model but rather use statistical anomaly detection algorithms (e.g., K-Nearest Neighbors) on constructed micro-CSI fingerprints. Multiple sets of CSI samples per device are used to construct fingerprints and train the anomaly detectors.
Evaluation Protocol:
- Metrics include attack detection rate (ADR) and false alarm rate (FAR).
- Tested under static and mobile conditions.
- Compared alternative anomaly detection algorithms and distance metrics.
- Ablations include varying the number of CSI samples (Ncsi) used to form fingerprints and tuning the number of channel taps Np in LS estimation.
- Cross-validation is performed on multiple days with realistic environmental variations.
- Reproducibility:
- Code and the dataset are publicly available at https://github.com/Oriseven/CSI-RFF.
- The CSI extraction method depends on commodity WiFi devices and open-source CSI tools.
- Some CSI collection relies on SDR platforms for ACK packet CSI, which may require specific hardware.
Overall, an example end-to-end example is:
- Capture a group of 20 CSI measurements on a single-antenna transmitter (ACK packets from a known WiFi NIC) received on a multi-antenna SDR receiver.
- Apply LS projection on CSI vector to estimate and remove channel component assuming strong LoS and limited taps.
- Divide original CSI by channel estimate to get micro-CSI vector.
- Aggregate and normalize micro-CSI vectors over the group to form a stable fingerprint.
- Use KNN anomaly detector trained on known devices’ fingerprints to authenticate devices and detect attacks.
- Evaluate performance via ADR/FAR in static and mobile scenarios.
This pipeline leverages domain knowledge of OFDM channel sparsity and hardware RF distortions, combined with careful averaging and anomaly detection to yield robust device authentication.
Technical innovations
- Identification and characterization of micro-CSI, subtle hardware-induced micro-signals embedded in CSI curves of WiFi NICs, as a novel RF fingerprint source.
- Development of a signal space-based least squares extraction method under strong LoS assumptions to separate micro-CSI distortions from confounding wireless channel effects.
- Demonstration that micro-CSI fingerprints remain stable and time-invariant over 14 months and across mobility, outperforming existing CSI-based RF fingerprinting methods in accuracy and robustness.
- Application of commodity WiFi CSI from ACK packets with single-antenna transmitter chains and multi-antenna receivers to enable practical, low-cost fingerprint extraction on COTS devices.
Datasets
- CSI dataset of 15 WiFi NICs (WiFi 4/5/6) — size: 14 months of CSI measurements under static and mobile conditions — collected by authors using SDR and commodity devices — publicly available at https://github.com/Oriseven/CSI-RFF
Baselines vs proposed
- Carrier frequency offset (CFO)-based fingerprint [33]: ADR = 97.24%, FAR = 1.47% vs CSI-RFF: ADR ≈ 99%, FAR = 0%
- Nonlinear phase error-based fingerprint [20]: Up to 97% classification accuracy with same-room training vs CSI-RFF: 99% ADR with cross-day and mobility robustness
- Power amplifier-induced fingerprint combined with network-layer features [36]: ADR = 96.55%, FAR = 4.31% vs CSI-RFF: ADR ≈ 99%, FAR = 0% using 100x fewer CSI measurements
Figures from the paper
Figures are reproduced from the source paper for academic discussion. Original copyright: the paper authors. See arXiv:2602.22738.
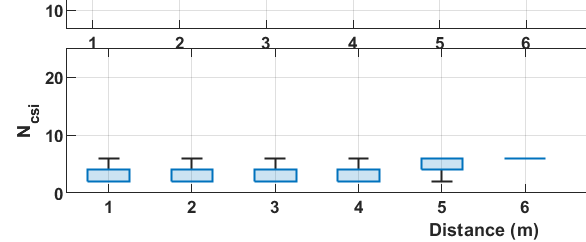
Fig 6: Invariance of the fingerprints with respect to time, where Ncsi = 50, Nrx = 1.
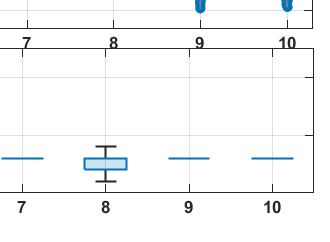
Fig 7: Influence of noise on the needed number of CSI measurements Ncsi,
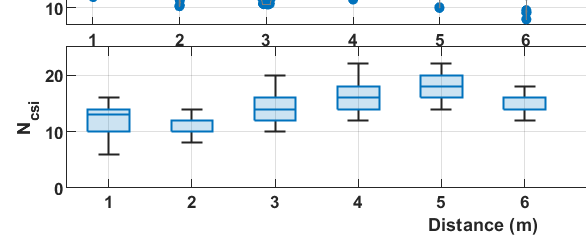
Fig 8: Mobility influence on fingerprints, where Ncsi = 100, Nrx = 1.
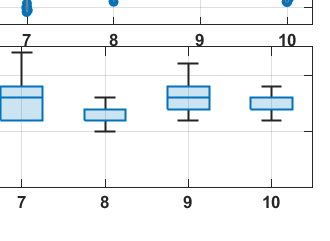
Fig 5: Uniqueness of amplitude of fingerprints of 8 NICs of various brands, where Ncsi = 20, Nrx = 4.
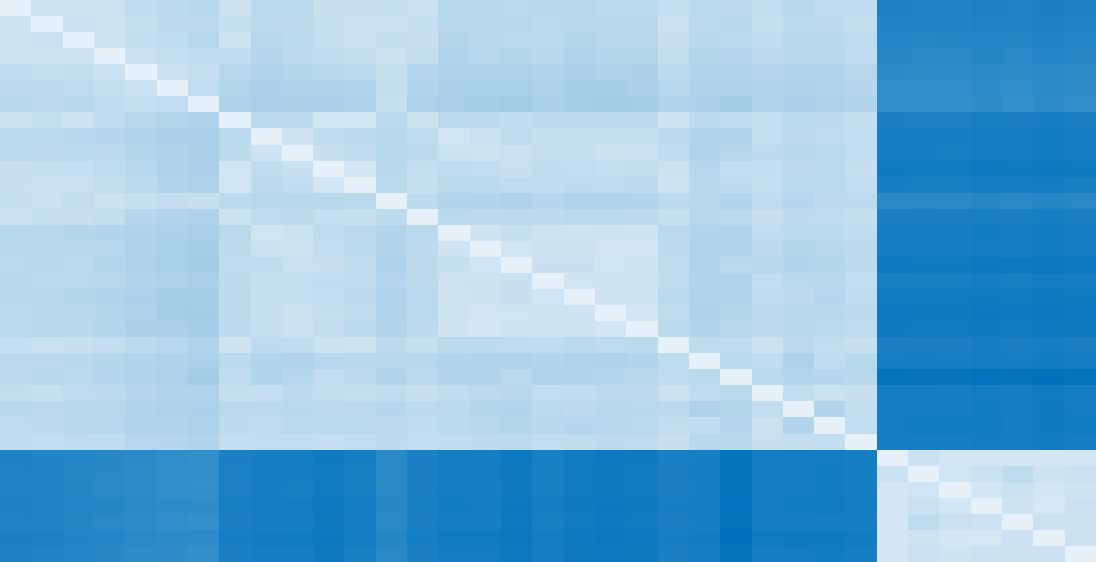
Fig 9: Robot authentication for area access control.
Fig 10: Experiment setup in room B.
Fig 11: Impacts of anomaly detection algorithms, when FAR ≤1% and
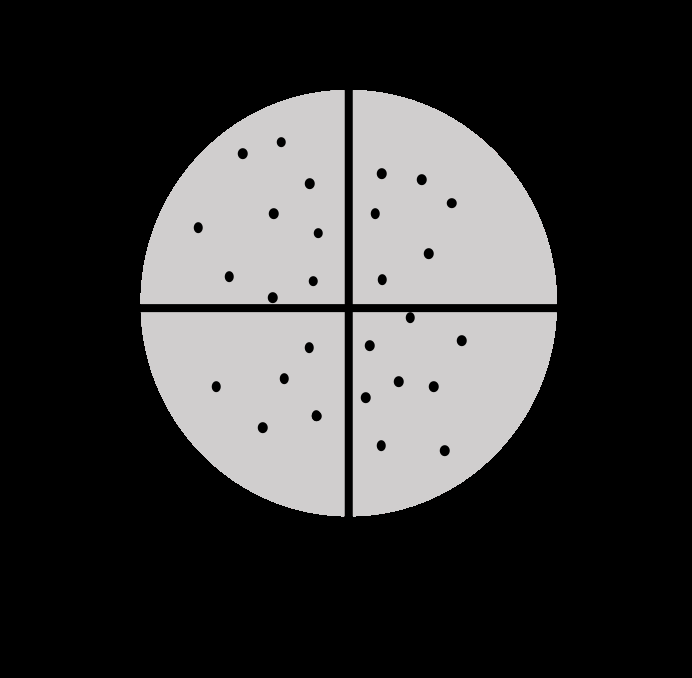
Fig 12: Impacts of distance metrics, when FAR ≤1% and Ncsi =
Limitations
- Method relies on strong line-of-sight (LoS) scenarios; performance in severe multipath or non-LoS not fully characterized.
- CSI extraction and micro-CSI separation assume sparsity and stability of channel impulse response; may degrade in highly dynamic or noisy environments.
- Limited testing on larger-scale device populations beyond 15 NICs; scalability to hundreds or thousands of devices unverified.
- Attack model assumes adversary cannot replicate hardware imperfections; sophisticated attackers with hardware cloning not evaluated.
- Extraction currently depends on access to ACK packet CSI requiring SDR or specialized CSI tools; may limit deployment on some platforms.
- Impact of environmental changes (temperature, interference) on fingerprint stability is not exhaustively examined.
Open questions / follow-ons
- How resilient is CSI-RFF fingerprint extraction in non-line-of-sight or rich multipath indoor/outdoor environments?
- Can micro-CSI extraction be adapted to dynamic channels or fast mobility scenarios beyond the tested indoor robots?
- What strategies can be developed to detect or mitigate adversaries attempting micro-CSI cloning or hardware-based spoofing attacks?
- How does environmental variability such as temperature shifts or interference affect fingerprint stability and authentication error rates over longer periods?
Why it matters for bot defense
From a bot-defense and CAPTCHA perspective, CSI-RFF offers a promising physical-layer fingerprinting approach to authenticate WiFi or IoT devices based on intrinsic RF hardware imperfections accessible via commodity network interfaces. This method complements cryptographic authentication by providing a tamper-resistant second factor that is extremely difficult to spoof remotely. For CAPTCHA or bot defense practitioners, deploying this could enhance system trust in legitimate user devices, especially in IoT settings where device identity is critical.
However, the current reliance on line-of-sight conditions and specialized CSI collection tools means immediate applicability might be limited in highly dynamic or outdoor networks. The approach could inspire new device fingerprinting techniques that leverage channel-independent micro-signals for stronger authentication. It also suggests incorporating physical-layer observations into multi-factor defenses against device impersonation and rogue access, which is relevant for mitigating automated or scripted network attacks. Overall, CSI-RFF expands the toolbox for low-level, hardware-rooted bot and device authentication in wireless contexts.
Cite
@article{arxiv2602_22738,
title={ CSI-RFF: Leveraging Micro-Signals on CSI for RF Fingerprinting of Commodity WiFi },
author={ Ruiqi Kong and He Chen },
journal={arXiv preprint arXiv:2602.22738},
year={ 2026 },
url={https://arxiv.org/abs/2602.22738}
}