Browser Fingerprint Detection and Anti-Tracking
Source: arXiv:2502.14326 · Published 2025-02-20 · By Kaitong Lin, Huazhu Cao, Amin Milani Fard
TL;DR
This paper addresses the significant privacy threat posed by browser fingerprinting, which enables cross-site user tracking and identification beyond traditional cookie-based methods. The authors critically examine existing anti-tracking approaches, demonstrating their limited effectiveness against modern fingerprinting techniques. To fill this gap, they develop a user-friendly Chrome browser extension that detects, customizes, and randomizes browser fingerprints to reduce fingerprint uniqueness and mitigate tracking risks. The extension also monitors and logs fingerprinting activity by websites, enabling users to visualize when and how fingerprint data is accessed.
The main contributions include a rewriting and interception module that forges fingerprint attributes by modifying JavaScript APIs and request headers, a data generation module that injects randomized noise in dynamic fingerprint elements such as Canvas and WebGL, and a monitoring system that logs fingerprint access attempts for user awareness. Performance evaluation on websites of varying complexity shows negligible impact on page load time and memory usage with the extension enabled. Overall, the work demonstrates a practical and extensible client-side defense against digital fingerprint tracking that balances effectiveness with usability for non-expert users.
Key findings
- Chrome extension randomizes static fingerprint attributes (e.g., userAgent, language) from predefined configurations and injects noise into dynamic ones (Canvas, WebGL, AudioContext), effectively forging browser fingerprints.
- API rewriting using JavaScript's Object.defineProperty modifies read-only browser fingerprint properties such as navigator.userAgent to spoof original values.
- The extension logs fingerprint access attempts asynchronously, enabling a dashboard that visualizes fingerprinting activity frequency and sources per-website in an intuitive manner.
- Performance testing on Wikipedia (low), Instagram (medium), and YouTube (high complexity) shows page load latency increases less than 5ms on average (e.g., 33ms to 36ms on Instagram) and no significant impact on memory usage (e.g., Instagram memory usage ~310 MB unchanged).
- Session-specific fingerprint consistency is preserved by storing spoofed values per tab using chrome.storage.session, preventing fingerprint changes mid-session but allowing new randomization between sessions.
- The extension intercepts and modifies request headers related to fingerprinting (User-Agent, Accept-Language, Do Not Track flags) via chrome.declarativeNetRequest.
- Users can customize fingerprints at a granular level (select OS, browser versions, hardware settings) or use one-click randomization, making it accessible to non-technical users.
- Comparison to prior tools shows improved user control, per-tab configuration, integrated monitoring, and broader coverage of fingerprint attributes like WebRTC, Canvas, and Audio fingerprinting.
Threat model
The adversary is a web tracker or malicious website that uses standard browser APIs and HTTP headers to collect detailed fingerprinting attributes to uniquely identify and track users without their consent. This adversary can fully access data exposed by typical browsing environments but cannot execute privileged or native code on the client. The attacker cannot bypass or tamper with the Chrome extension's internal mechanisms or APIs once installed and active.
Methodology — deep read
Threat Model & Assumptions: The adversary is any website or third party that collects browser fingerprint data to uniquely identify or track users across visits and sites. The attacker can access browser APIs and HTTP request headers. The attacker is assumed not to have client-side code execution beyond typical webpage JavaScript.
Data: The system does not train on classical datasets but derives fingerprint attributes from browser APIs such as Navigator, Screen, Canvas, WebGL, AudioContext, and HTTP headers. These attributes are collected live from the user's browser environment.
Architecture/Algorithm: The solution consists of three main components: (a) Rewriting and Interception Module—modifies JavaScript browser API properties (e.g., navigator.userAgent) by redefining getters using Object.defineProperty, and intercepts HTTP request headers (e.g., User-Agent) via Chrome's declarativeNetRequest API to return forged values; (b) Data Generation, Storage and Transfer Module—provides users with configurable spoofed fingerprint attributes or randomization by selecting from predefined values for static data (userAgent, language) and injecting random noise in dynamic rendering identifiers (Canvas, WebGL, Audio), storing these per tab in chrome.storage.session to maintain consistency without cross-session persistence; (c) Monitoring and Logging Module—captures and aggregates fingerprint access attempts by injecting logging calls inside redefined API getters and collecting them asynchronously to avoid blocking page execution, storing logs persistently in chrome.storage.local for analysis.
Training Regime: Not applicable; the solution is heuristic, rewrite- and interception-based, without machine learning training.
Evaluation Protocol: Measured average page load time and memory footprint on three websites (Wikipedia, Instagram, YouTube) over 50 iterations each with the extension enabled or disabled. Performance metrics: page load latency, total JS heap size, overall memory use. Also evaluated coverage of fingerprint attributes modifiable by the extension, and logged website attempts to fingerprint user. Usability demonstrated via extension UI screenshots and feature explanations. No adversarial robustness testing reported.
Reproducibility: Source code is publicly available on GitHub. Data is live browser environment information. Extension integrates with Chrome manifest v3 APIs.
End-to-end example: When a user enables one-click defense, the background script stores randomized fingerprint settings in chrome.storage.session keyed per tab ID. Upon webpage load, the content script injects and rewrites JavaScript fingerprint APIs with forged values selected by the extension, logs any access to these APIs, and modifies request headers to spoof values. Logs are asynchronously written to local storage. The user can later view tracking dashboard charts aggregating fingerprint accesses by domain and attribute.
Technical innovations
- Selective API rewriting of read-only browser fingerprint properties using JavaScript's Object.defineProperty for spoofing fingerprint values dynamically per tab.
- Injection of controlled random noise into dynamic fingerprinting attributes (Canvas, WebGL, Audio fingerprint) preserving visual/audio integrity while breaking fingerprint stability.
- Integrated asynchronous logging of fingerprint access attempts allowing real-time monitoring and user-visible dashboard of fingerprinting activity.
- Hybrid data storage approach using session storage for ephemeral spoofed fingerprint state and local storage for persistent tracking logs, balancing consistency and persistence.
- Comprehensive UI for non-expert users enabling granular customization of spoofed fingerprint attributes or one-click randomized defenses.
Baselines vs proposed
- Page load time on Instagram: without extension = 33 ms vs with extension = 36 ms average over 50 runs.
- Memory usage on Instagram: without extension = 310 MB vs with extension = 310.7 MB average over 10 minutes monitoring.
- Page load time on YouTube: without extension = 37 ms vs with extension = 37.4 ms average over 50 runs.
Figures from the paper
Figures are reproduced from the source paper for academic discussion. Original copyright: the paper authors. See arXiv:2502.14326.
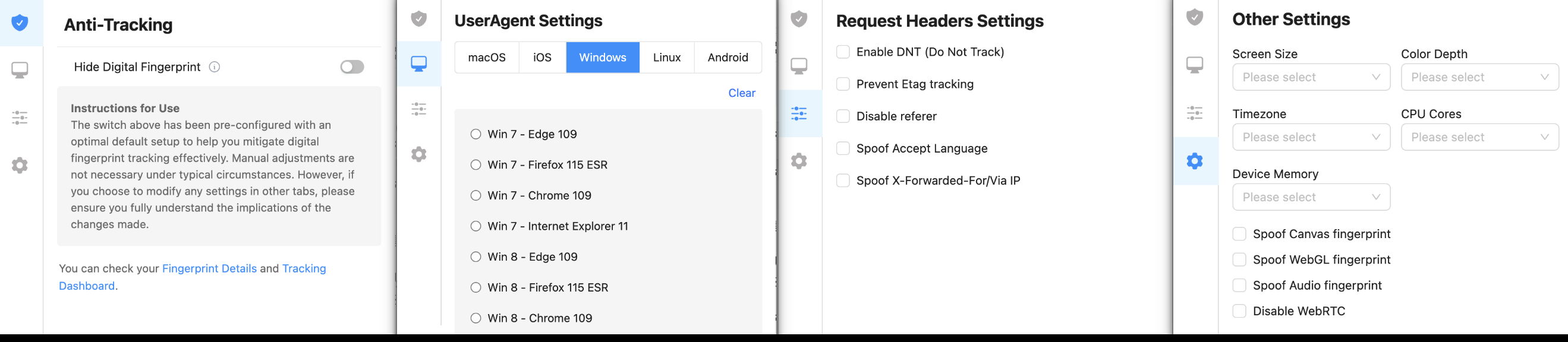
Fig 4: Screenshots of our Chrome extension showing different menu options.
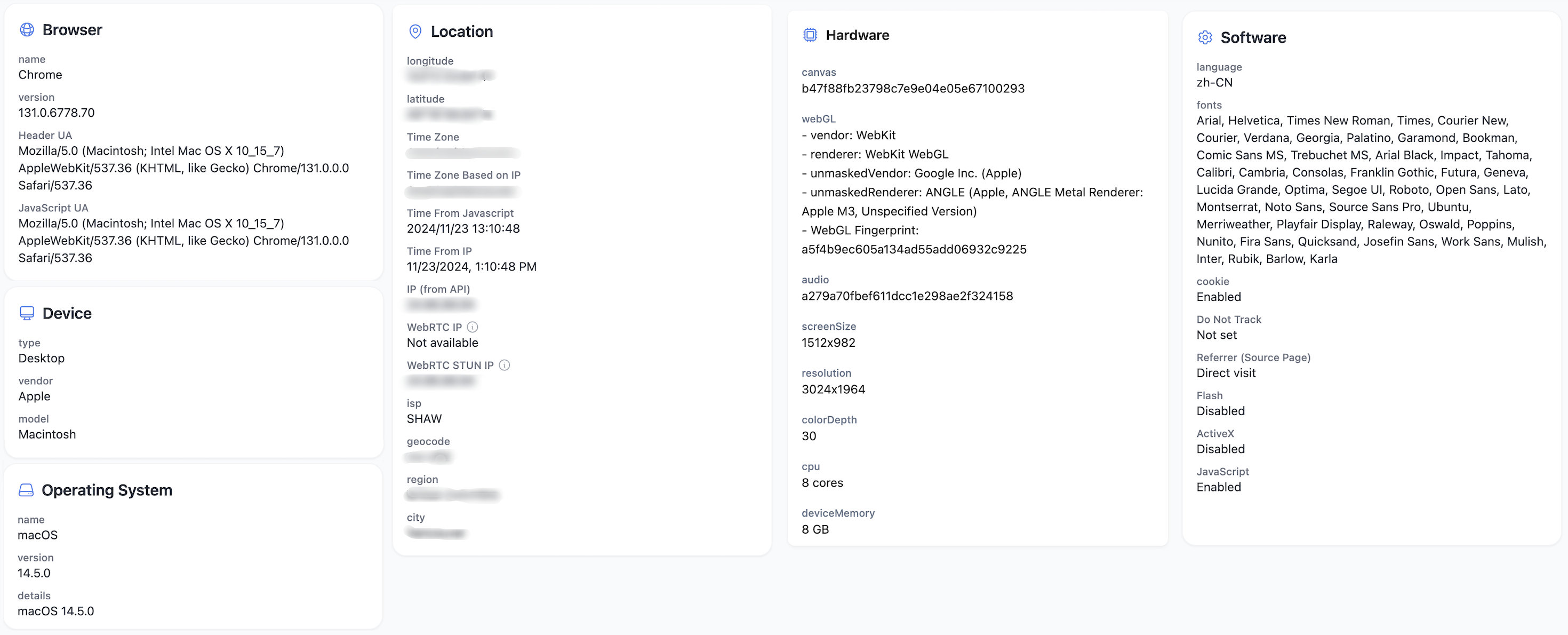
Fig 5: A screenshot of fingerprint information.
Limitations
- No adversarial evaluation against adaptive fingerprinting scripts actively probing and detecting spoofing.
- No quantitative metrics on fingerprint uniqueness reduction or tracking unlinkability provided.
- Performance and effectiveness tested only on a small selection of popular websites, lacking broader internet scale evaluation.
- The extension requires periodic page refresh to reapply API rewriting, as modifications are not persistent across page reloads.
- Limited discussion on potential side effects or website compatibility issues caused by spoofed fingerprint data.
- Reliance on Chrome APIs means limited applicability outside Chromium-based browsers or future API changes.
Open questions / follow-ons
- How effective is randomized fingerprint spoofing against adaptive trackers that apply heuristic anomaly detection or fingerprint stability checks?
- What is the measurable reduction in fingerprint uniqueness and entropy across large-scale web measurements when using this defense?
- Can the approach be extended to support per-site or per-domain fingerprint policies to optimize usability versus protection?
- How resilient is the extension’s logging and monitoring against obfuscated or encrypted fingerprinting scripts loaded by websites?
Why it matters for bot defense
Bot-defense and CAPTCHA practitioners can leverage insights from this work to understand how browser fingerprint spoofing and anti-tracking mechanisms impact the reliability of fingerprint-based bot detection signals. The randomized and configurable spoofing of fingerprint attributes may degrade fingerprint consistency and uniqueness, potentially reducing false positives but also limiting detection confidence. Integrating fingerprint monitoring dashboards similar to the proposed logging module could help researchers identify fingerprints that are actively manipulated or spoofed and adapt their defenses accordingly. However, developers should also consider the limitations of client-side spoofing defenses, particularly against sophisticated attackers who might combine fingerprinting with behavioral signals for more reliable bot detection. Overall, this paper provides a practical reference design for deployable fingerprint obfuscation that CAPTCHA and bot-defense systems must account for in threat modeling and trust scoring.
Cite
@article{arxiv2502_14326,
title={ Browser Fingerprint Detection and Anti-Tracking },
author={ Kaitong Lin and Huazhu Cao and Amin Milani Fard },
journal={arXiv preprint arXiv:2502.14326},
year={ 2025 },
url={https://arxiv.org/abs/2502.14326}
}