Building an effective bot detection system design means creating a solution that accurately identifies malicious automation while minimizing friction for genuine users. At its core, a bot detection system must balance accuracy, speed, scalability, and privacy. Getting this design right requires combining multiple layers of analysis, from user behavior to risk scoring, and often integrating CAPTCHA challenges strategically.
Core Principles of Bot Detection System Design
A robust bot detection system is not a single component but a blend of techniques working together to detect automated activities with high precision. The main goals are:
- Accurate bot/human differentiation: Avoid false positives that annoy real users, and catch bots before they exploit your system.
- Real-time processing: Identification must happen quickly enough to allow or block access without noticeable delays.
- Adaptability: Bots evolve constantly, so the system must adjust to new attack tactics.
- Privacy compliance: Especially in regions with strict data laws, user privacy must be respected.
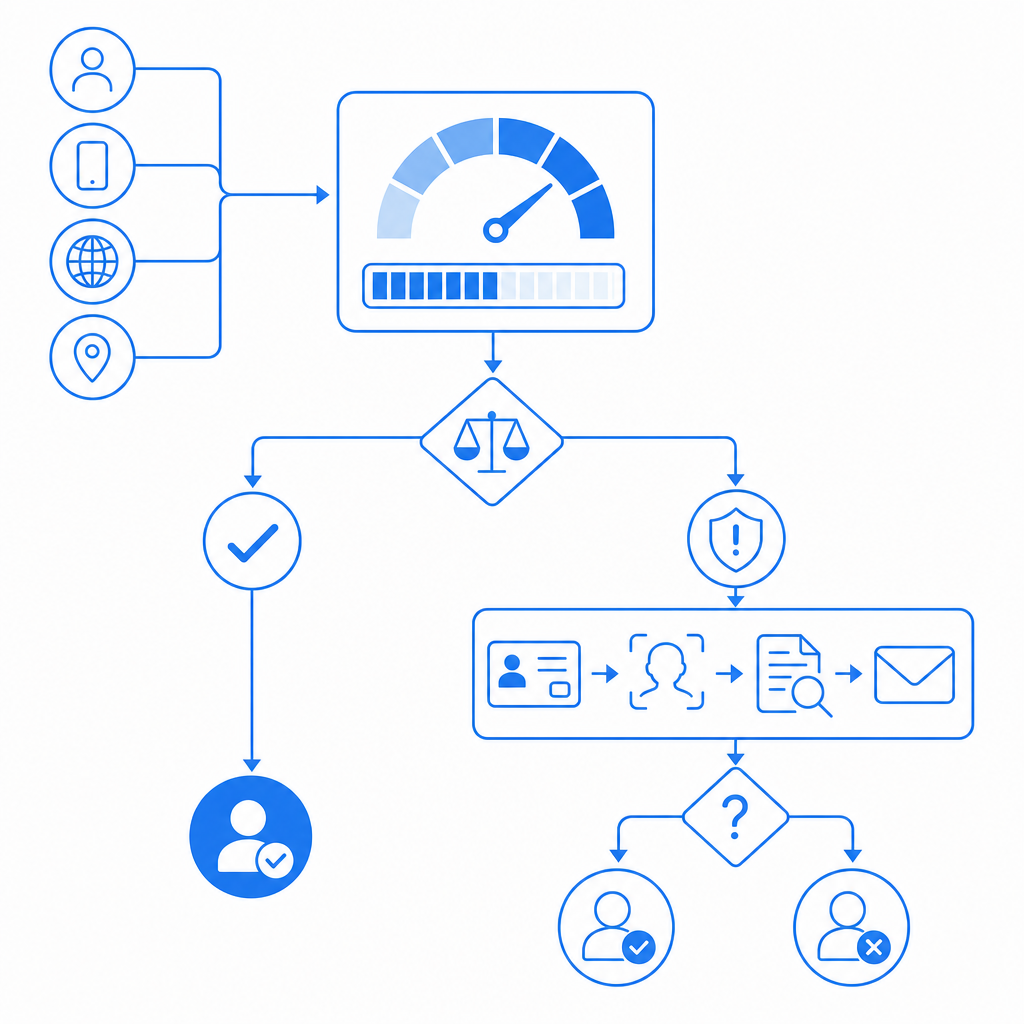
The foundation of bot detection design often involves risk scoring based on signals like device fingerprinting, behavioral profiling, IP reputation, and challenge-response tests such as CAPTCHAs. Each signal alone may be ambiguous, but combined analysis provides stronger confidence in identifying bots.
Key Components to Include in Your Design
1. Data Collection and Signal Aggregation
Effective bot detection begins by collecting as many relevant signals as possible during user interaction. Typical signals include:
- Browser and device fingerprinting: Capturing browser type, OS, installed fonts, screen resolution, and other subtle details that bots may not perfectly emulate.
- Behavioral indicators: Mouse movements, typing patterns, scrolling, click timing, and interaction velocity can reveal automated behavior.
- Network metadata: IP address, geolocation, proxy or VPN usage, request headers, and TLS fingerprinting assist in reputation assessment.
- Historical context: Prior interactions from the same user or IP help track suspicious patterns.
These signals are continuously fed into a scoring engine for risk assessment.
2. Risk Scoring and Decision Logic
A bot detection system design includes a scoring mechanism that assigns a risk score based on aggregated data. The score determines the appropriate response, such as:
| Risk Score Range | Action |
|---|---|
| Low (0-30%) | Allow without challenge |
| Medium (31-70%) | Present friction (e.g., CAPTCHA challenge) |
| High (71-100%) | Block or require strict verification |
Machine learning models are often employed here to weigh different signals and identify subtle bot behaviors while minimizing false positives.
3. Challenge Mechanisms (CAPTCHA Integration)
In scenarios with elevated risk, presenting challenges to distinguish humans from bots is critical. CAPTCHAs remain a common and effective tool when used judiciously — for instance, only triggering after suspicious behavior rather than on every visit.
CaptchaLa offers integrations that fit naturally into risk-based bot detection systems. Its native SDKs for web (JS/Vue/React), mobile (iOS/Android), and cross-platform frameworks like Flutter and Electron enable flexible implementation across environments. You can validate user responses server-side securely via API calls.
4. Continuous Learning and Adaptation
Attackers evolve, so your system should incorporate feedback loops with labeled data to retrain models and update heuristics. Periodic updates improve detection accuracy over time. Monitoring metrics such as false positive rates, challenge completion rates, and conversion impact guides tuning.
Comparing Popular Bot Detection Approaches
Here’s a concise comparison of some well-known solutions frequently considered when designing bot detection:
| Feature | CaptchaLa | reCAPTCHA (Google) | hCaptcha | Cloudflare Turnstile |
|---|---|---|---|---|
| Open SDKs | Web, iOS, Android, Flutter, Electron | Web, Android, iOS SDKs | Web-centric, some mobile support | Web-focused, no official mobile SDKs |
| Privacy | First-party data only | Uses Google infrastructure | Privacy-focused, more user data control | Privacy by design, minimal data |
| Pricing | Free tier (1000/mo) + tiers up to 1M | Free, usage-based (Google limits) | Usage-based, offers payouts | Free with Cloudflare services |
| Challenge Types | Visual, interactive | Mostly image-based challenges | Image tasks, interactive challenges | Invisible by default, fallback CAPTCHA |
| Server-side Verification | Yes, REST API | Yes, REST API | Yes, REST API | Yes, integrated into Cloudflare stack |
Each has trade-offs. For example, Cloudflare Turnstile focuses on invisible verification to reduce user friction but requires Cloudflare services. reCAPTCHA is well-established but has raised privacy questions. CaptchaLa emphasizes easy integration across platforms with a strong privacy stance via first-party data usage.

Best Practices for Implementing Your Bot Detection System
To help guide your design process, consider these technical specifics:
- Start with signal diversity: The broader the types of signals collected, the more accurate your risk scoring can be. Combine behavioral, device, and network data.
- Use risk scoring thresholds: Define clear cutoffs to trigger escalating challenges instead of blanket enforcement.
- Leverage asynchronous validation: Where possible, validate tokens server-side to minimize user impact and secure APIs.
- Integrate adaptive challenges: Implement CAPTCHAs that adjust difficulty or frequency according to user risk score.
- Employ rate limiting and anomaly detection: Combine bot detection with traffic patterns for layered defense.
- Ensure SDK support for multiple platforms: CaptchaLa’s SDKs in JavaScript, iOS, Android, Flutter, and Electron ease deployment across diverse environments.
- Monitor and iterate: Use analytics to track false positives, user abandonment, and passes. Continuously update models based on fresh attack data.
Sample Server-side Validation Call (Pseudo-code)
# Call CaptchaLa API to validate user response token
import requests
API_URL = "https://apiv1.captcha.la/v1/validate"
APP_KEY = "your-app-key"
APP_SECRET = "your-app-secret"
def validate_captcha(pass_token, client_ip):
headers = {
"X-App-Key": APP_KEY,
"X-App-Secret": APP_SECRET,
"Content-Type": "application/json"
}
payload = {"pass_token": pass_token, "client_ip": client_ip}
response = requests.post(API_URL, json=payload, headers=headers)
result = response.json()
# result['success'] is True if validation passed
return result.get("success", False)This approach centralizes validation, allowing your backend to decide whether to grant access based on the CAPTCHA verification.
Conclusion
Designing an effective bot detection system demands thoughtful layering of signals, risk-based decision-making, and smart challenge integration. Balancing security and user convenience means applying CAPTCHA judiciously rather than relying on it alone. Solutions like CaptchaLa provide the flexibility, multi-platform SDKs, and privacy-conscious design needed to build a tailored bot defense system.
For those looking to dive deeper, our docs cover implementation details and advanced features. When ready, check out CaptchaLa pricing for options suitable from small projects up to enterprise-scale deployments.
The key is continuous adaptation: measure performance, tune your risk scoring, and stay ahead of evolving automated threats with a layered defensive architecture.