Bot detection in Python can be implemented using various techniques that identify and block automated malicious traffic before it affects your application. By analyzing behavioral patterns, request headers, and integrating CAPTCHA challenges, developers can reliably distinguish between real users and bots. This article explains how to perform bot detection using Python, compares popular solutions, and highlights how you can combine custom logic with services like CaptchaLa for robust bot defense.
Core Concepts of Bot Detection in Python
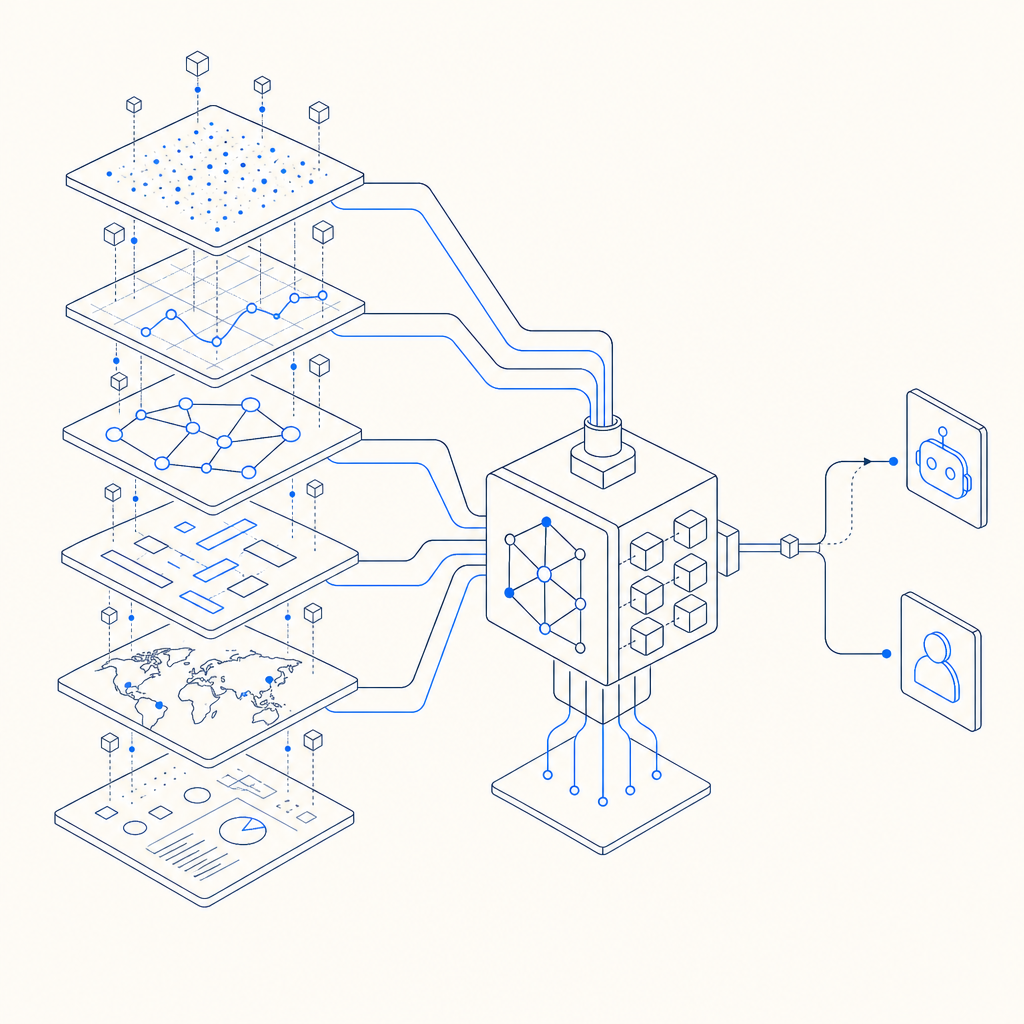
At its heart, bot detection involves collecting data points such as IP reputation, request headers, mouse movements, and timing patterns, then using heuristics or machine learning to classify traffic. Python excels in data processing and integration with web frameworks, making it a natural choice for adding bot detection layers.
Common approaches to detect bots programmatically include:
- Monitoring User-Agent strings and HTTP headers for suspicious or missing values
- Rate limiting requests per IP or session to identify automation bursts
- Analyzing request frequency and interaction timing patterns
- Utilizing third-party APIs to score IPs and user behavior
- Incorporating CAPTCHA challenges conditionally based on risk score
Python’s rich ecosystem offers libraries like requests, Flask or Django middleware, and machine learning frameworks to help implement custom detection logic. Yet, integrating specialized bot defense services provides a valuable addition to DIY methods.
Implementing Basic Bot Detection in Python
Here’s a simple Python example demonstrating how to gather request information and flag suspicious traffic patterns:
from flask import Flask, request, abort
import time
app = Flask(__name__)
# Dictionary to track request timestamps per IP
ip_request_log = {}
@app.before_request
def detect_bot():
ip = request.remote_addr
now = time.time()
user_agent = request.headers.get('User-Agent', '')
# Basic check: flag empty or common bot UA strings
if not user_agent or 'bot' in user_agent.lower():
abort(403, description="Bot detected: User-Agent suspicious")
# Rate limiting: allow max 10 requests per IP per minute
window = 60
max_requests = 10
timestamps = ip_request_log.get(ip, [])
timestamps = [t for t in timestamps if now - t < window]
if len(timestamps) >= max_requests:
abort(429, description="Too many requests - potential bot")
timestamps.append(now)
ip_request_log[ip] = timestamps
@app.route("/")
def home():
return "Hello human!"
if __name__ == "__main__":
app.run()This snippet implements elementary checks: User-Agent inspection and rate limiting. While useful, these should not be the sole defense—bots can spoof headers and mimic human request rates.
Augmenting Python Detection with Risk-Based Services
To enhance bot detection beyond heuristics, Python backends can call third-party APIs that analyze traffic in real time and issue challenges.
For instance, integrating CaptchaLa can add adaptive CAPTCHA challenges when suspicious activity occurs. Below is a conceptual example of making a server-side verification request to CaptchaLa’s API after a CAPTCHA is solved client-side:
import requests
CAPTCHA_API_URL = "https://apiv1.captcha.la/v1/validate"
APP_KEY = "your_app_key"
APP_SECRET = "your_app_secret"
def verify_captcha(pass_token, client_ip):
headers = {
"X-App-Key": APP_KEY,
"X-App-Secret": APP_SECRET
}
payload = {"pass_token": pass_token, "client_ip": client_ip}
response = requests.post(CAPTCHA_API_URL, json=payload, headers=headers)
return response.json().get("success", False)By requiring users to complete such challenges during suspicious activity—identified via your Python backend metrics—you improve detection accuracy while maintaining user experience.
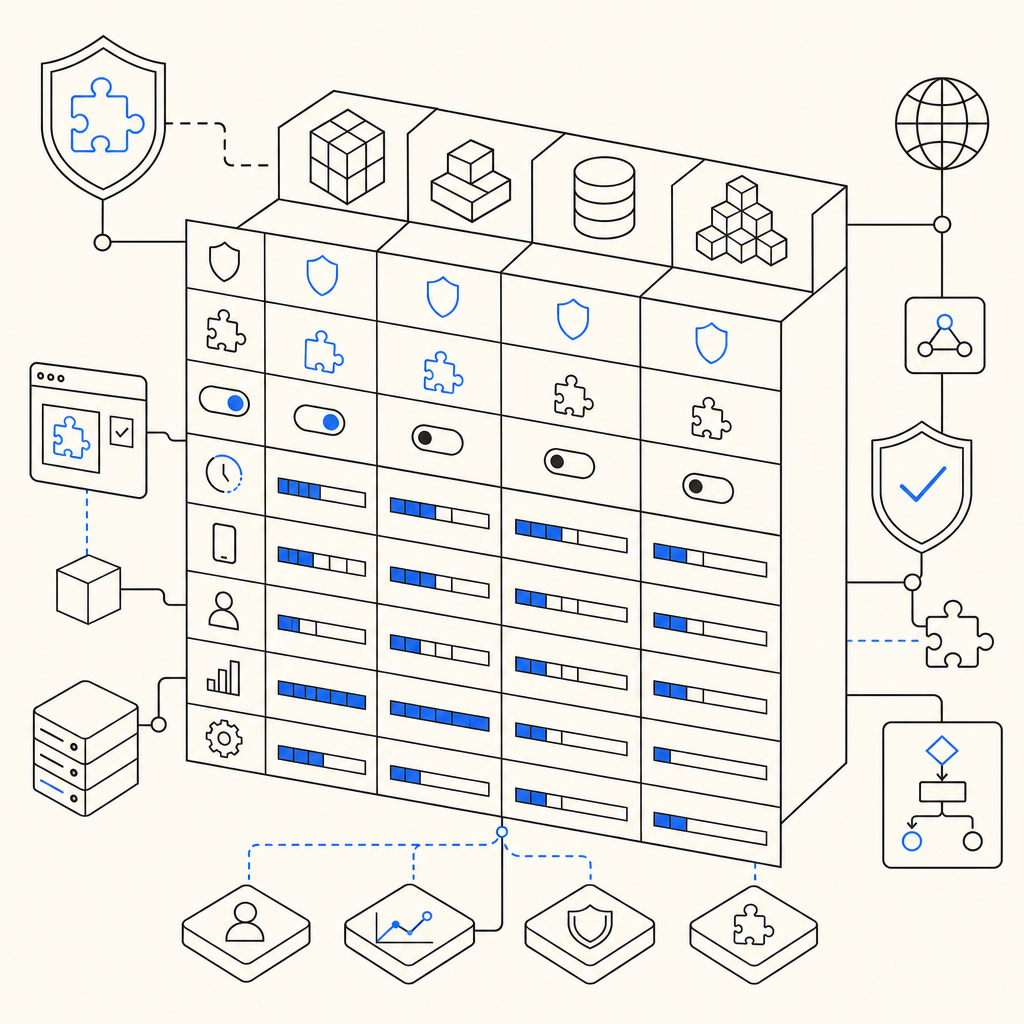
Comparing Popular Bot Defense Solutions
Here is a brief comparison of some widely used bot detection and CAPTCHA providers:
| Feature | CaptchaLa | Google reCAPTCHA | hCaptcha | Cloudflare Turnstile |
|---|---|---|---|---|
| SDK Support | Web, iOS, Android, Flutter | Web, mobile SDKs | Web, mobile SDKs | Web only |
| Pricing | Free tier + scalable plans | Free | Free with paid options | Free with Cloudflare CDN |
| Privacy | First-party data, no tracking | Google data collection | Privacy-focused options | Integrated with Cloudflare |
| Challenge Types | Image, puzzle CAPTCHAs | Checkbox, invisible CAPTCHA | Similar puzzles | Invisible CAPTCHA |
| Customization | High (open APIs and SDKs) | Moderate | Moderate | Low |
Captchala’s multi-language SDK support and transparent pricing make it an attractive choice for developers wanting lightweight but flexible bot defense in Python applications.
Best Practices for Python Bot Detection
When implementing bot detection in Python, consider the following approaches:
- Multi-layered defense: Combine client-side CAPTCHA challenges with backend behavior analysis.
- Use native SDKs: CaptchaLa offers SDKs for various platforms including web JS frameworks, iOS, Android, Flutter, and Electron, simplifying integration.
- Leverage server-side validation: Always validate CAPTCHA tokens and risk signals server-side to avoid bypass.
- Monitor and tune thresholds: Analyze logs to adjust rate limits and heuristics for false positive reduction.
- Respect privacy and transparency: Use providers that prioritize user data privacy, especially relevant for GDPR compliance.
By layering techniques, your Python services can ward off scraping, spam, and credential stuffing attacks with minimal user friction.
Integrating CaptchaLa in Your Python App
CaptchaLa provides straightforward server SDKs (captchala-php, captchala-go) and native clients for mobile platforms, making it well suited for Python backend integration as well.
For example, after sending a CAPTCHA challenge to the client (using the loader from https://cdn.captcha-cdn.net/captchala-loader.js), you validate the user response as shown above. This allows your Python API to programmatically grant or deny access based on real-time bot risk assessment.
Explore the CaptchaLa docs to get started with SDKs, API calls, language support, and client integration samples that complement your bot detection scripts.
Conclusion: Building Efficient Bot Detection with Python
Bot detection using Python combines request analysis, heuristics, and external risk scoring. While basic techniques like checking headers and rate limiting help catch simple bots, integrating services such as CaptchaLa provides adaptive and multilingual bot challenges that raise the bar. Supported by native SDKs and transparent APIs, these solutions bring reliable protection without degrading user experience.
Where to go next? Check out CaptchaLa pricing for plan options suitable for small projects or enterprise deployments, and dive into the docs for detailed integration guides tailored for Python developers. Implementing bot detection is an ongoing process, but a thoughtful combination of Python code and specialized services will keep your app secure against evolving bots.