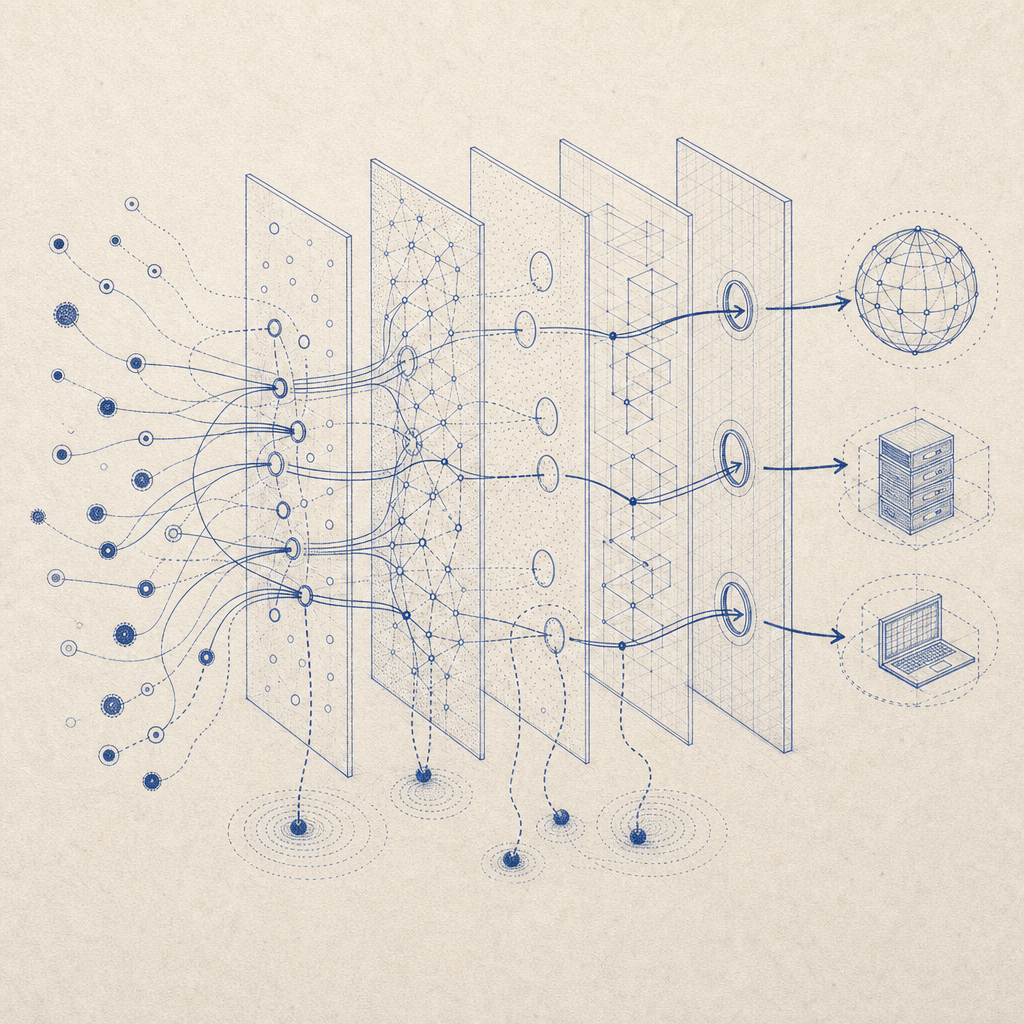
Bot detection using IP information is a fundamental part of distinguishing legitimate human visitors from automated scripts, scraping tools, or malicious bots. By analyzing IP data—such as origin, reputation, frequency, and behavioral patterns—web services can block or challenge suspicious activity before it affects user experience or security. This approach supplements other verification methods and is a critical layer in bot defense.
Understanding how to use IP for bot detection helps businesses reduce fraud, abuse, spam, and account takeovers while maintaining smooth access for real users.
What Does Bot Detection IP Mean?
“Bot detection IP” refers to techniques that leverage IP address data to identify likely bot traffic. Since every device connected to the internet uses an IP address, security systems use this identifier to assess whether activity looks automated or malicious. IP data used for bot detection includes:
- IP reputation scores from threat intelligence databases
- Geographic location and VPN/proxy indicators
- Rate and volume of requests from a single IP
- Patterns of IP address changes or sharing
For example, a flood of requests from a single IP in a short period may indicate a denial-of-service (DoS) or credential stuffing attack. Similarly, known proxy IP ranges pose a higher risk for abusive use.
Key IP-Based Bot Detection Techniques
1. IP Reputation Analysis
Many security tools cross-reference incoming IPs with large databases that catalog IPs' historical behavior—whether they were sources of spam, hacking attempts, or other abuse. Integrating this with real-time checks helps security systems flag suspicious visitors immediately.
2. Rate and Behavioral Tracking by IP
Monitoring the number and frequency of requests per IP can highlight anomalies. Legitimate users rarely exceed certain request thresholds, while bots tend to generate high volumes or very repetitive patterns.
3. Geo-Location and Anomaly Detection
Mapping IPs to their physical or network origin can reveal unusual access patterns, such as logins from unexpected countries far from user time zones. Geo-validation also assists in compliance with regional regulations.
4. Proxy and VPN Detection
Recognizing IP addresses from known proxy services or VPN providers helps limit access to users trying to disguise their origin, a common tactic used by bots and fraudsters.
5. IP Diversity and Fingerprinting
Bots often rotate IPs rapidly across known ranges or data centers. Combining IP checks with browser fingerprinting or Captcha challenges increases detection accuracy.
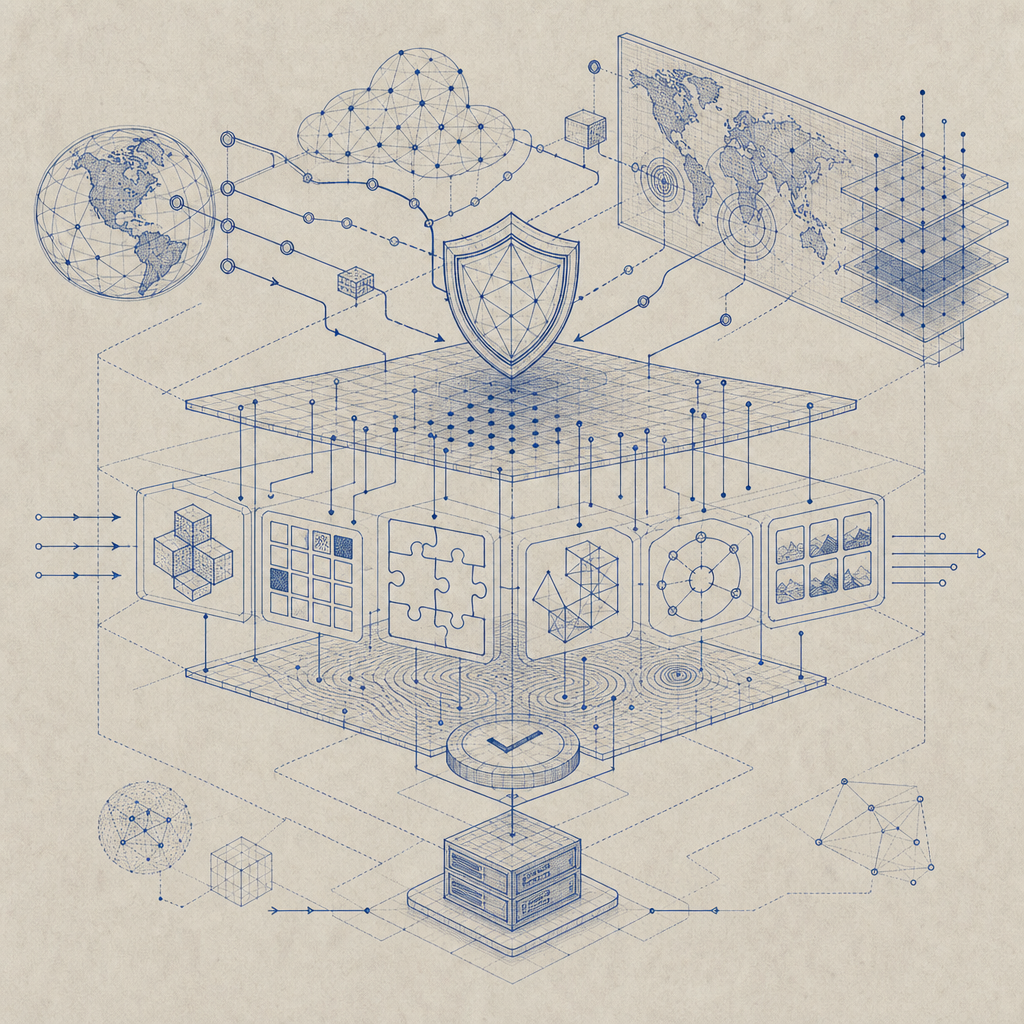
Bot Detection IP in Comparison to Other Bot Defense Methods
While IP analysis is crucial, it’s typically combined with other techniques like CAPTCHA challenges, behavioral biometrics, and JavaScript fingerprinting. Here is how IP-based detection stacks up to popular alternatives:
| Method | Strengths | Limitations | Common Use Cases |
|---|---|---|---|
| IP Reputation | Quick blocking of known bad IP | Limited for new, unknown bots | Spam filtering, early filtering |
| Request Rate Limits | Detects brute force and scrapers | Can block shared IP users | Login and form submissions |
| CAPTCHA Challenges | Differentiates humans vs bots | User friction, accessibility | When suspicious behavior noted |
| Device Fingerprinting | High accuracy, hard to spoof | Privacy concerns, complexity | Fraud prevention, persistent bot detection |
| Behavioral Analysis | Detects subtle bot behavior | Requires more data, latency | Account takeover prevention |
Solutions like CaptchaLa combine IP detection with challenge-based verification to strike a balance between effective bot defense and minimal user friction. Other providers like reCAPTCHA, hCaptcha, and Cloudflare Turnstile similarly integrate IP context as part of broader risk assessments.
Implementing IP-Based Bot Detection with CaptchaLa
For developers, CaptchaLa offers flexible SDKs and APIs to incorporate IP detection alongside CAPTCHAs and other defenses:
- Client SDKs: Native libraries for Web (JS, Vue, React), iOS, Android, Flutter, and Electron enable quick integration capturing the client IP and challenge responses.
- Server Validation: Use the POST endpoint
https://apiv1.captcha.la/v1/validatewith parameters likeclient_ipand the CAPTCHA token to verify requests. - Server-Side Challenge Issuing: Generate server tokens using
https://apiv1.captcha.la/v1/server/challenge/issueto customize security flows. - Language Support: CaptchaLa supports 8 UI languages to globally accommodate diverse user bases seamlessly.
Below is a simplified example of how server-side validation might incorporate IP information:
// Example server-side validation pseudocode (Node.js)
// Validate the CAPTCHA token and client IP with CaptchaLa API
const validateCaptcha = async (token, ip) => {
const response = await fetch("https://apiv1.captcha.la/v1/validate", {
method: "POST",
headers: {
"X-App-Key": "your-app-key",
"X-App-Secret": "your-app-secret",
"Content-Type": "application/json"
},
body: JSON.stringify({
pass_token: token,
client_ip: ip
})
});
const result = await response.json();
return result.success; // true if passed
};Capturing the IP on backend requests and combining it with CaptchaLa’s challenge results provides a robust layer of bot filtering.
Practical Considerations and Limitations
Shared IPs and NAT
Many legitimate users share a public IP (e.g., through corporate NAT or mobile carriers). Overly strict IP rate limiting can inadvertently block real traffic, so it’s important to tune thresholds or combine IP signals with behavioral analysis.
IPv6 and Dynamic IPs
The growth of IPv6 and carriers issuing dynamic IPs complicate reputation scoring, as IP ownership changes frequently. Bot detection systems must account for this fluidity.
Privacy and Compliance
IP data is considered personal information under regulations like GDPR. Ensure IP collection is disclosed in privacy policies, securely handled, and minimized where possible.
Summary
IP-based bot detection is a foundational piece of any bot defense strategy. It offers quick, actionable signals to filter out suspicious traffic by evaluating IP reputation, request patterns, and network characteristics. When integrated with challenge methods such as CAPTCHA, this approach enables web services to protect themselves while preserving user experience. Platforms like CaptchaLa provide ready-to-use tools and APIs that incorporate these IP insights alongside challenges, helping you build layered defenses without complexity.
For a comprehensive overview of integrating IP detection and bot defense strategies, check out the CaptchaLa docs. You can start testing their free tier or explore pricing plans tailored for businesses of all sizes.
Where to go next? Begin by experimenting with IP-inclusive validations and challenge flows to see how they improve your bot detection accuracy and reduce abuse on your site.