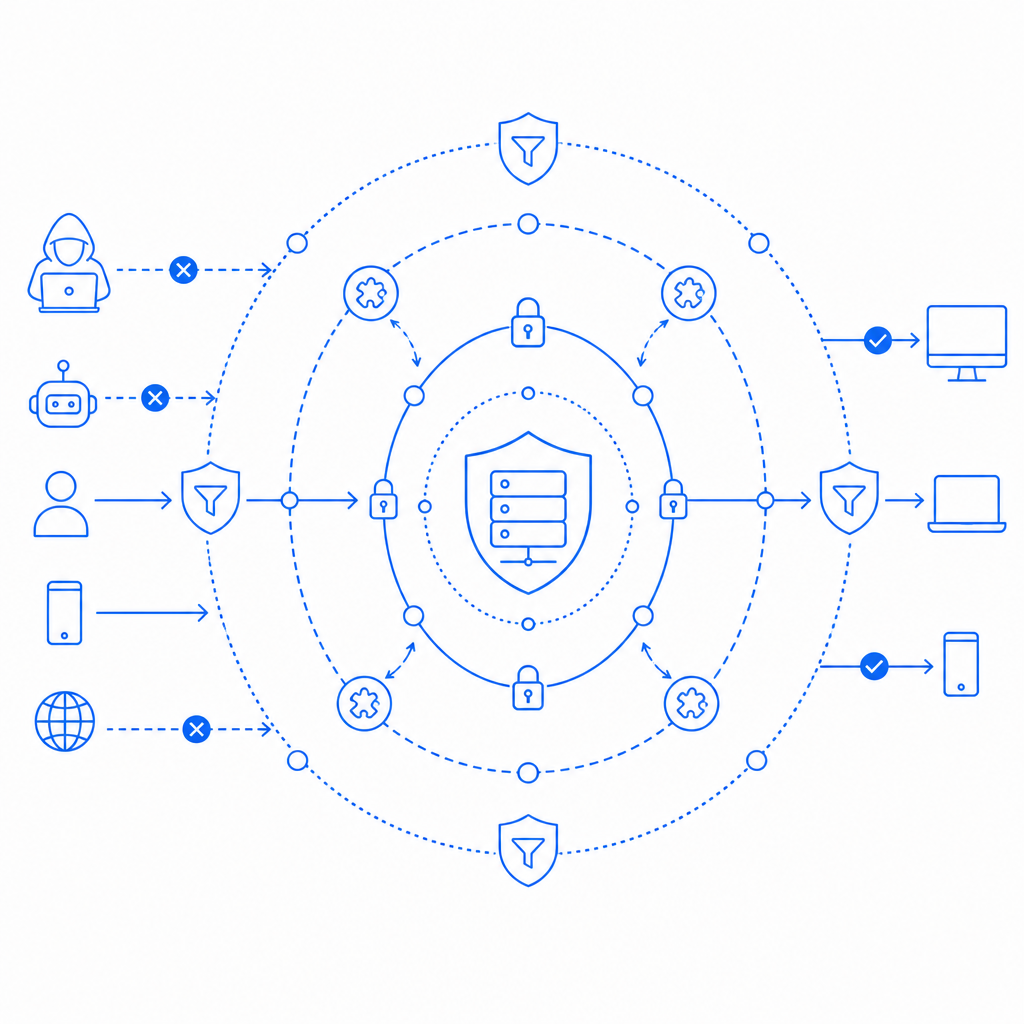
Bot detection evasion is the practice by which automated tools or malicious actors avoid triggering the security systems designed to identify and block bots. As automated attacks grow more sophisticated, traditional bot detection methods alone are no longer sufficient. Understanding common evasion techniques and effective defenses is crucial for maintaining the integrity of your website or application.
While no defense is foolproof, layering multiple techniques and leveraging adaptive challenges helps to raise the bar for attackers. Services like CaptchaLa offer customizable bot defense solutions that integrate with your infrastructure to stay up to date with evasion trends. This post outlines the main evasion strategies used by attackers and how defenders can respond.
Common Techniques of Bot Detection Evasion
Understanding the approaches attackers use to bypass bot detection systems helps defenders identify gaps in their security and adopt more resilient measures.
1. User-Agent and IP Address Spoofing
Bots often masquerade as real browsers by faking User-Agent strings or switching between IP addresses to blend in with legitimate traffic. Rotating proxy networks and VPNs allow bots to avoid detection by IP rate limiting or geofencing.
2. Browser Automation Frameworks
Headless browsers driven by tools like Puppeteer or Selenium are common in automated attacks. However, many detection solutions can recognize artifacts left behind by these frameworks, prompting attackers to employ evasions such as:
- Modifying the browser environment to mimic real users
- Randomizing navigation timings and mouse movements
- Injecting fake browser fingerprint data
3. JavaScript and Cookie Handling
Some bots disable or bypass JavaScript execution to avoid client-side detection scripts. Others carefully execute scripts but avoid accepting cookies, session tokens, or tracking pixels, hindering traditional stateful protection mechanisms.
4. Machine Learning and Human-in-the-Loop
Advanced attackers incorporate machine learning models to adapt behavior and evade heuristics dynamically. Others outsource CAPTCHA solving and interaction challenges to human workers, enabling them to overcome typical bot-blocking measures.
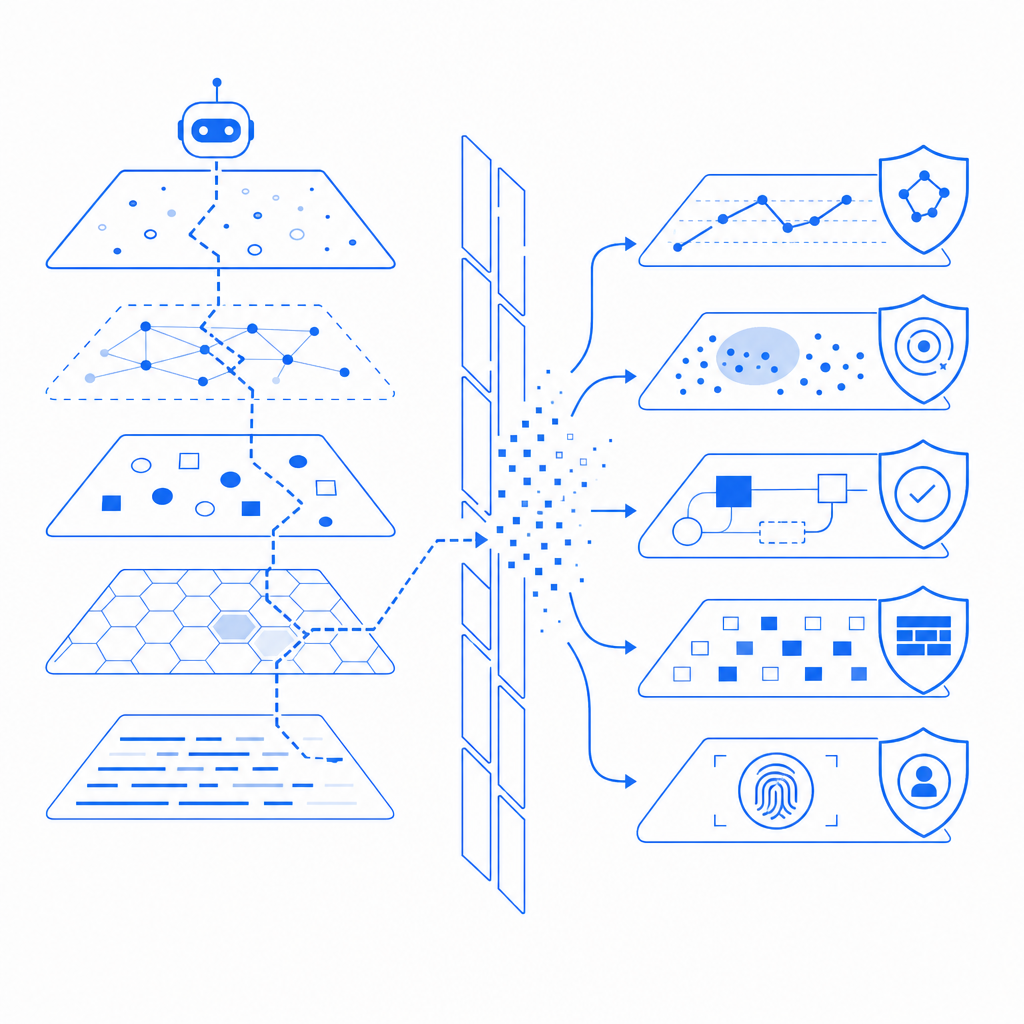
Effective Defenses Against Bot Detection Evasion
Combating evasive bots requires a multi-layered, adaptive approach that combines client-side and server-side verification with continuous behavioral analysis.
Multi-Factor Verification Combining Behavior and Challenges
Rather than relying only on static indicators, modern bot defense tools analyze:
- Mouse movement patterns
- Keystroke dynamics
- Browser fingerprinting signals (fonts, WebGL data, hardware concurrency)
- Rate and sequence of navigation actions
When suspicious behavior is detected, adaptive challenges such as CAPTCHAs or interactive puzzles can be introduced. This mixed approach complicates automation and human outsourcing.
Server-Side Token Validation and Analytics
Offloading critical validation to the backend reduces exposure to tampering. For example, CaptchaLa validates tokens via a secure POST request to their endpoint with pass_token and client_ip parameters. This server-token model helps ensure challenges were genuinely solved by human users or trusted clients.
Leveraging Native SDKs and Multi-Platform Coverage
Bot detection evasion isn't confined to browsers. Apps and desktop clients also face automated attack risks. Utilizing SDKs available for Web (JS, Vue, React), iOS, Android, Flutter, and Electron — as provided by CaptchaLa — enhances protection uniformly across platforms.
Regularly Updating Bot Detection Models
Attackers evolve constantly. Solutions that offer:
- Continuous threat intelligence updates
- Adjustable sensitivity settings
- Support for first-party data integration
tend to maintain efficacy longer. This differentiates providers from competitors like reCAPTCHA, hCaptcha, or Cloudflare Turnstile, who offer varied approaches but similar challenges in adapting fast enough.
| Feature | CaptchaLa | reCAPTCHA | hCaptcha | Cloudflare Turnstile |
|---|---|---|---|---|
| Multi-language UI | 8 languages | 40+ languages | 30+ languages | Limited languages |
| Native SDKs | Web, iOS, Android, Flutter | Web, Android, iOS | Web, Android, iOS | Web |
| Server-side validation | Yes, token + IP | Yes | Yes | Yes |
| Free tier requests/month | 1000 | High | High | High |
| Adaptive Challenge Support | Yes | Yes | Yes | Limited |
| First-party data reliance | Yes | No | No | No |
Technical Best Practices to Harden Bot Detection
Enforce HTTPS and Secure Headers: Bots scanning for vulnerabilities often ignore TLS and headers such as Content-Security-Policy or X-Frame-Options, which can help filter basic unwanted traffic.
Implement Rate Limiting with IP Reputation Checks: Limit request rates by IP and monitor for known proxy or VPN services, reducing the surface for evasion by IP rotation.
Integrate Multi-Source Fingerprinting: Combine canvas fingerprinting, WebGL, fonts enumeration, and audio context analysis into a single fingerprint score, reviewed server-side.
Deploy Adaptive Challenge Triggers: Rather than showing a CAPTCHA on every access, use behavioral scoring scripts client-side to trigger challenges only when suspicious.
Continuously Monitor Logs for Anomalies: Analyze request patterns, headers, and timings for new evasion techniques and tweak detection rules accordingly.
Why CaptchaLa Supports Defenders Against Bot Evasion
As attackers grow more resourceful, token-based and behavior-driven bot defenses become essential. CaptchaLa offers:
- Straightforward server SDKs (PHP, Go) and client loaders to simplify integration
- Flexible adaptive challenge mechanisms tailored to your traffic
- Transparent pricing tiers from free use (1000 challenges/month) to one million requests for businesses
- Documentation for developers in eight UI languages, helping international projects implement robust defenses
Its server-token validation ensures that even sophisticated evasion methods must overcome a trusted, backend-enforced hurdle to succeed.
Bot detection evasion remains a persistent challenge that requires continual attention and proactive defense strategies. Combining client behavior analysis, server-side verification, and adaptive challenges builds resilience toward the bot threat landscape’s ongoing transformation.
To explore how you can improve your defenses with token validation and SDK integration, consider reviewing CaptchaLa’s documentation and checking out their pricing plans. Staying ahead of evasion means adopting tools that evolve alongside attackers — and maintaining a layered, adaptive approach across your entire digital footprint.