A captcha logo is usually a visual shorthand for trust, verification, and bot protection. In practice, it tells users, “this step is part of an anti-abuse system,” while helping teams make the challenge feel recognizable rather than suspicious.
That small mark can do a lot of work. It can set expectations before a challenge loads, reassure users that a form is protected, and reduce confusion when people hit a verification step. But the logo also needs to be used carefully: if it looks too dominant, too opaque, or too disconnected from the surrounding UI, it can raise more doubts than it resolves.

What the captcha logo communicates
The best captcha logo does not try to entertain people or sell the brand. Its job is to communicate function fast.
At a glance, it should answer three questions:
- Is this a verification step?
- Is this expected?
- Is this safe to continue?
Those answers matter because CAPTCHA is one of the few interface elements that can interrupt a user’s task on purpose. A clear logo can soften that interruption by making the step feel intentional rather than broken. That is true whether you are using a classic checkbox flow, an invisible risk check, or a challenge issued only when behavior looks abnormal.
For product teams, the logo also becomes part of the credibility layer. Users often judge the protection by what they can see, not by the security model behind it. A concise logo and label can help avoid the “is this a phishing page?” moment that sometimes appears when a form suddenly asks for extra verification.
Logo as a trust signal, not decoration
A captcha logo works best when it behaves like a system cue:
- It is visible near the challenge or protected action.
- It is small enough not to compete with the primary CTA.
- It uses consistent naming and iconography across pages.
- It matches the tone of the site, whether formal, friendly, or technical.
If you use CaptchaLa, the interface can be localized across 8 UI languages, which matters because visual trust signals are read differently across markets. The same logo treatment that feels straightforward in one locale can feel too aggressive or too vague in another.
Design choices that affect conversion
A captcha logo is not just branding; it is part of form conversion. The wrong placement or style can make a simple verification step feel like friction, while the right one can keep the flow calm and understandable.
Here are the main variables to think about.
Placement
Place the logo where it explains the verification step, not where it competes with the primary action. Common good spots include:
- above or beside the challenge container
- near the submit button, if the verification happens after submission
- in a small footer line inside the widget
Avoid placing it far from the control it explains. If users have to hunt for context, the logo loses its job.
Visual weight
The logo should be noticeable but not loud. Large badges can make a page look cluttered; tiny, low-contrast marks can look accidental. A good rule is that the logo should support the challenge, not become the challenge.
Brand relationship
Some teams want the captcha logo to blend seamlessly into the page. Others want it to stand out as an external trust mark. Either can work, but be deliberate:
- Blend in if the CAPTCHA is part of a smooth, embedded form experience.
- Stand out if you want the verification boundary to be obvious.
Language and copy
A logo alone is rarely enough. Pair it with short, concrete copy such as “Protected by bot detection” or “Verification required to continue.” Keep the wording plain and avoid anything that sounds scary, legalistic, or overly technical.
Comparing captcha providers through the UI lens
Different providers present their trust signals differently, even when the backend goal is the same. If you are choosing a provider or auditing a redesign, it helps to compare them from the user-interface side, not just the security side.
| Provider | Typical UI style | Brand visibility | Integration feel | Notes |
|---|---|---|---|---|
| reCAPTCHA | Familiar, often recognizable badge or challenge | High | Well known, sometimes visually prominent | Commonly associated with Google infrastructure |
| hCaptcha | Challenge-oriented, explicit verification cues | Medium to high | Clear separation between app and verification | Often used where visible proof of verification is preferred |
| Cloudflare Turnstile | Minimal, often low-friction and lightweight | Low to medium | Designed to feel unobtrusive | Useful when teams want less visual interruption |
| CaptchaLa | Flexible, localized UI with server-side validation options | Adjustable | Can be embedded in a product’s own visual language | Supports native SDKs and server SDKs for practical integration |
This is not about declaring one approach superior. It is about matching the UI to the risk model and the user journey.
For example, a signup flow for a consumer app may benefit from a very light visual treatment. A ticketing platform or rate-limited API portal may want a more explicit verification boundary. The more sensitive the action, the more important it is that the captcha logo clearly indicates what is happening and why.
Technical details that support the logo experience
The logo may be the visible part, but the backend determines whether the experience feels solid or flaky. If verification is slow or unreliable, even a well-designed logo cannot save the interaction.
A few implementation details matter:
- Load the client script early enough that the challenge does not appear late.
- Keep the validation path predictable.
- Tie the UI state to the token lifecycle.
- Use server-side checks before granting access to protected actions.
- Make error states specific so users know whether to retry or refresh.
With CaptchaLa, the loader is available at:
<script src="https://cdn.captcha-cdn.net/captchala-loader.js"></script>Validation is done server-side with a POST request to:
POST https://apiv1.captcha.la/v1/validateThe request body includes:
{
"pass_token": "your-token",
"client_ip": "203.0.113.42"
}And it uses X-App-Key plus X-App-Secret headers. That matters because a logo can promise trust, but validation is what actually enforces it.
If your product uses challenge issuance instead of a fully passive check, you can also create a server token with:
POST https://apiv1.captcha.la/v1/server/challenge/issueThat pattern is especially useful when the UI needs to reflect state changes cleanly: challenge issued, challenge shown, token passed, request validated.
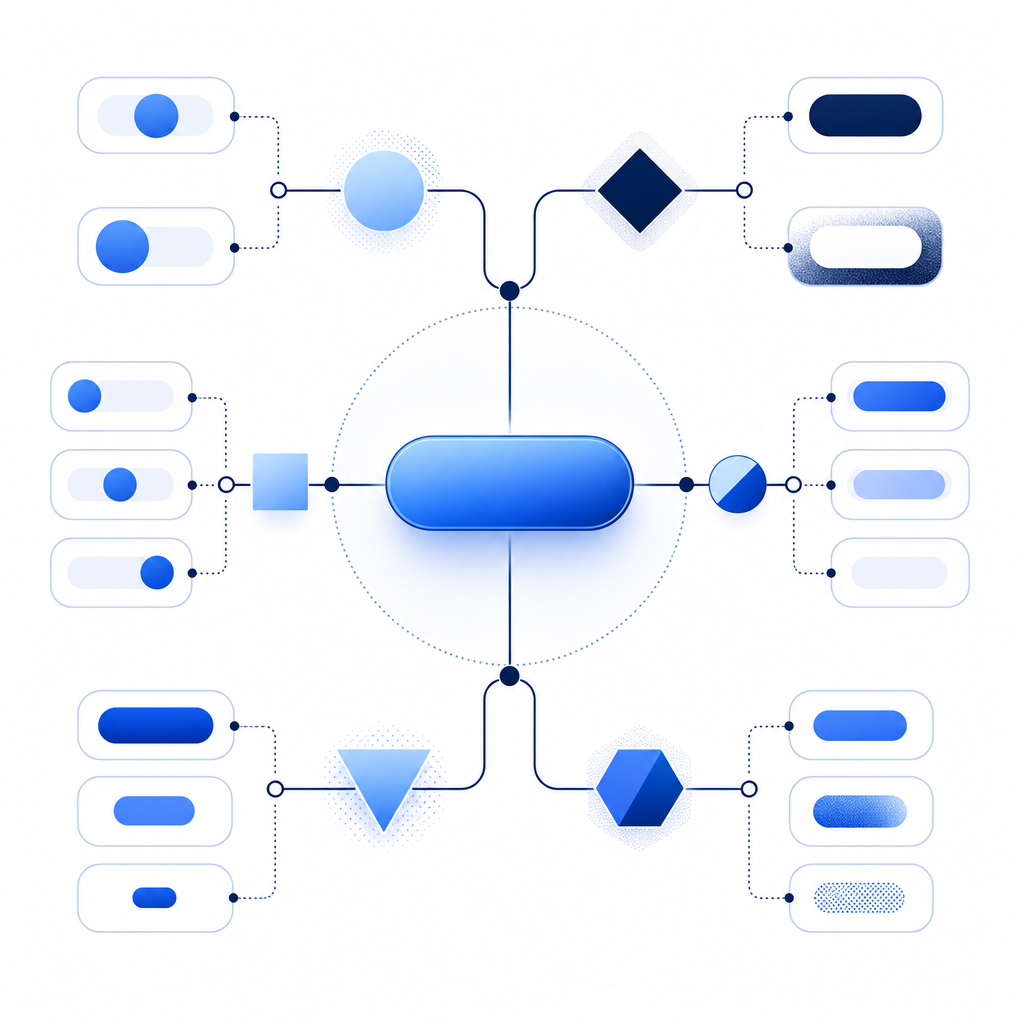
A simple integration flow
1. User opens protected form
2. Loader initializes captcha UI
3. Logo and label explain verification
4. User completes challenge
5. Client sends pass_token to server
6. Server validates token before proceedingThat sequence sounds simple, but it is what keeps the visual trust signal honest. The logo says “verification is happening”; the server says “verification actually happened.”
When to keep the logo subtle
Not every page needs the same level of visual emphasis. A subtle captcha logo is often the right choice when:
- the protected action is routine, such as login or newsletter signup
- the user is already context-aware
- the page has limited space
- you want the verification to feel embedded in the workflow
A more explicit logo can help when:
- the action is high risk, such as account recovery or payment changes
- users may not expect additional verification
- you need to reduce support tickets about “why am I seeing this?”
The key is consistency. If the logo appears sometimes and disappears other times without explanation, users may think the system is unstable. Clear rules are better than clever UI tricks.
For teams shipping across platforms, this consistency is easier when the same product logic spans web, mobile, and desktop. CaptchaLa’s native SDKs for Web, iOS, Android, Flutter, and Electron make that easier to standardize without reinventing the presentation layer on every platform. Server SDKs like captchala-php and captchala-go help keep the validation path aligned with the same trust message.
Final thought
A captcha logo is small, but it is never meaningless. It can calm users, frame a security step, and make bot defense feel like part of the product instead of an interruption pasted on top of it. The goal is not to maximize logo visibility; it is to make the verification boundary understandable, predictable, and easy to trust.
Where to go next: if you are planning a new verification flow or refining an existing one, review the implementation details in the docs or compare tiers on the pricing page.