A good captcha laravel package should make bot defense easy to add, straightforward to validate on the server, and light enough that real users barely notice it. For most Laravel apps, the key question is not “do I need a CAPTCHA?” but “which integration fits my stack, traffic, and user experience best?”
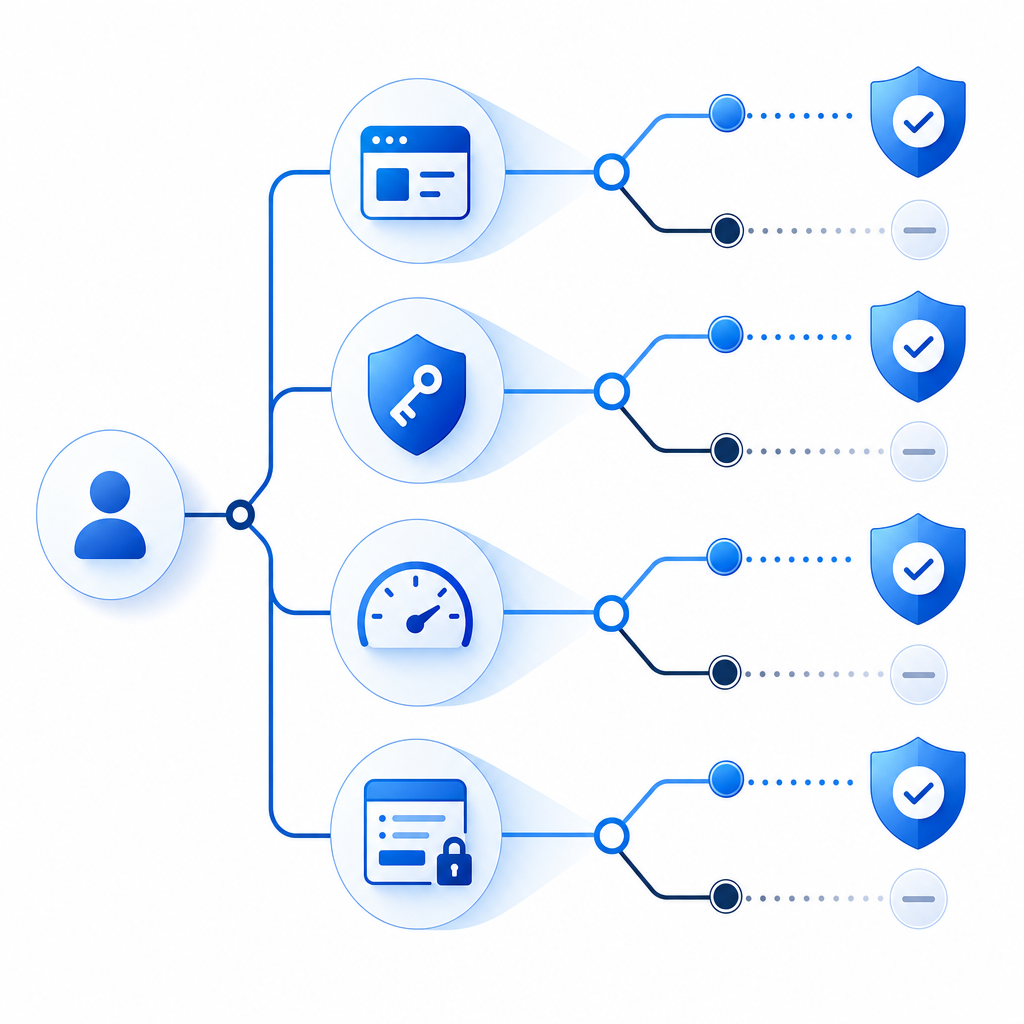
Laravel teams usually want three things from a CAPTCHA layer: simple frontend setup, reliable backend verification, and enough flexibility to support forms, login flows, registration, password reset, and API-backed actions. That means the package should fit cleanly into your existing controllers, middleware, and validation rules without forcing a large rewrite.
The practical choice often comes down to whether you want a generic widget or a full bot-defense workflow. A package can help with display and client-side token handling, but the real protection comes from validating tokens server-side and pairing CAPTCHA with rate limits, CSRF protection, and input validation.

What a Laravel CAPTCHA package should actually do
A lot of teams search for a captcha laravel package when they really need a complete verification flow. In Laravel, that means the package should support both the browser side and the application side.
At a minimum, look for these capabilities:
Simple frontend injection
- A script loader or component you can place in Blade templates
- A predictable way to render the challenge or widget
- Support for modern frontend stacks if you use them alongside Blade
Server-side verification
- A POST endpoint or SDK method to validate the pass token
- A way to send the client IP along with the token
- Secret management through environment variables, not hardcoded config
Framework-friendly integration
- Validation rules or reusable middleware
- Clean error handling for failed challenges
- Low friction in forms and auth controllers
Operational controls
- Clear documentation
- Support for multiple UI languages if your audience is international
- Pricing that matches your traffic patterns
For reference, CaptchaLa supports 8 UI languages and provides native SDKs for Web (JS/Vue/React), iOS, Android, Flutter, and Electron. That matters if your Laravel app is only one piece of a larger product stack, such as a mobile app with a shared login flow.
Comparing common options for Laravel
Not every CAPTCHA option has the same tradeoffs. Some teams prefer reCAPTCHA because they already know it. Others use hCaptcha for privacy or policy reasons. Cloudflare Turnstile is attractive if you want a low-friction challenge experience. The question is how each option fits your Laravel codebase and operational requirements.
| Option | Strengths | Tradeoffs | Laravel fit |
|---|---|---|---|
| reCAPTCHA | Very familiar, widely documented | Can feel heavier in UX; Google dependency | Easy to find examples, but implementation often needs careful tuning |
| hCaptcha | Common alternative, familiar widget model | Can still add friction depending on challenge behavior | Similar pattern to reCAPTCHA for forms and auth pages |
| Cloudflare Turnstile | Low-friction user experience | Best aligned if you already use Cloudflare’s ecosystem | Good for lightweight form protection |
| CaptchaLa | Web and native SDK support, 8 UI languages, first-party data only | You still need to wire server validation like any serious CAPTCHA | Good fit when you want a straightforward verification flow and room to scale |
The important point is that no CAPTCHA product replaces application logic. Laravel still needs rate limiting, account lockout rules, email verification, and input sanitation. CAPTCHA should be one layer in a defense stack, not the whole wall.
If you want to compare pricing and traffic bands early, it helps to map your expected monthly volume. CaptchaLa’s free tier covers 1,000 validations per month, with Pro sized for 50K–200K and Business for 1M. That makes it easier to estimate what you’ll need before wiring everything into production. See the current pricing page for details.
A practical Laravel integration pattern
A clean Laravel setup usually follows the same shape whether you use Blade or a frontend framework.
1) Render the loader in your layout
For a browser-side challenge, include the loader script in your base layout:
<script src="https://cdn.captcha-cdn.net/captchala-loader.js"></script>Then render the widget or challenge element where your form needs it. Keep this close to the form submission path so users understand why the challenge appears.
2) Capture the pass token
When the challenge succeeds, the browser receives a pass token. Your form should submit that token alongside the rest of the payload, usually in a hidden input. Treat it as a short-lived verification artifact, not as a session token.
3) Validate on the server
On the Laravel side, verify the token before you complete the sensitive action. A server request to CaptchaLa’s validation endpoint looks like this conceptually:
<?php
// Validate the captcha token before processing the form.
$payload = [
'pass_token' => $request->input('pass_token'),
'client_ip' => $request->ip(),
];
$response = Http::withHeaders([
'X-App-Key' => config('services.captchala.key'),
'X-App-Secret' => config('services.captchala.secret'),
])->post('https://apiv1.captcha.la/v1/validate', $payload);
// Check whether the token is accepted before continuing.
if (! $response->successful() || ! $response->json('valid')) {
return back()->withErrors([
'captcha' => 'Verification failed. Please try again.',
]);
}That pattern keeps the trust decision on the server, where it belongs. If you are generating challenges server-side, CaptchaLa also provides a server-token issuance endpoint: POST https://apiv1.captcha.la/v1/server/challenge/issue. That can be useful when you want tighter control over challenge creation in protected flows.
4) Add it where abuse hurts most
You do not need CAPTCHA on every endpoint. Start where automated abuse costs you time or money:
- account registration
- login after repeated failures
- password reset requests
- contact forms and lead forms
- comment submission
- promo code or coupon redemption
- checkout steps that are frequently attacked
A good heuristic is to protect the endpoints that are publicly reachable, cheap to automate, and expensive to review manually.
Defensive details that make the difference
A captcha laravel package is only as good as the way you use it. The details below matter more than the widget style.
Use token validation together with rate limits
Laravel’s rate limiter should work alongside CAPTCHA. If a bot is hammering your login form, rate limits reduce request volume while CAPTCHA raises the cost of each attempt. Together, they give you a better signal than either one alone.
Keep secrets out of the browser
Only public loader assets belong client-side. API keys and secrets should stay in .env and be read by Laravel config. If your frontend and backend are separated, make sure the token validation happens only through your application server.
Respect user experience
CAPTCHA should protect the flow, not destroy it. If a verification fails, return a clear error and allow retry without clearing the entire form. For multilingual products, 8 UI languages can significantly reduce friction for non-English users.
Choose based on traffic shape, not just brand recognition
A smaller app with occasional form abuse may not need the same setup as a marketplace or SaaS with login storms and signup attacks. If your traffic is modest, a free tier can be enough to begin testing. If you’re scaling toward six or seven figures of monthly validations, pricing should be part of architecture planning, not an afterthought.
When CaptchaLa fits particularly well
CaptchaLa tends to make sense when you want a CAPTCHA layer that works across web and native surfaces without fragmenting your tooling. If your Laravel backend serves a web app plus mobile clients, it helps to have one verification model that maps cleanly to Web, iOS, Android, Flutter, and Electron.
It also helps that the product is designed around first-party data only, which can matter for teams with tighter privacy and data-governance requirements. For implementation guidance, the docs are the right starting point before you wire anything into production.
Final recommendation
If you are choosing a captcha laravel package, favor the one that fits your server-side workflow first and your frontend second. The most reliable setup is the one where Laravel validates every sensitive action, failure states are clear, and the CAPTCHA layer complements rate limiting rather than replacing it.
Where to go next: review the docs for implementation steps, then check pricing to match your expected validation volume.