If your bluesky captcha not working, the issue is usually one of three things: the challenge never renders, the token never validates, or the browser/app is blocking the scripts, cookies, or network calls the CAPTCHA needs. Start by checking the front end load path, then verify your server-side validation flow, and finally confirm that the challenge provider isn’t being blocked by extensions, CSP, or a proxy.
Most “captcha not working” reports are not actually CAPTCHA failures; they’re integration mismatches. That means the quickest fix is often to inspect the challenge script, confirm the response token is being sent to the backend, and make sure your validation request is using the right endpoint and credentials. If you’re defending a Bluesky-related signup, posting, or auth flow, that layered check matters more than any single widget setting.

What “not working” usually means
When someone says the Bluesky CAPTCHA is broken, they usually mean one of these:
- The widget never appears.
- The challenge appears, but submission fails.
- Validation succeeds in one browser but not another.
- Mobile app or in-app webview integration fails.
- The challenge is visible, but bots still get through.
That distinction matters because each symptom points to a different layer. A missing widget suggests a script, CSP, or DNS/CDN problem. A failing submission usually means the pass token isn’t reaching your backend or the validation request is malformed. If bots are getting through, the issue may be rate limiting, token reuse, or a weak server-side decision path.
A practical debugging sequence looks like this:
- Open the page in a clean browser profile.
- Disable privacy extensions temporarily.
- Check the browser console for script or CSP errors.
- Verify the challenge script loads from
https://cdn.captcha-cdn.net/captchala-loader.js. - Confirm the client receives a pass token after completion.
- Send that token to your server and validate it with the proper API credentials.
- Log both success and failure reasons on the backend.
If you’re using a vendor-agnostic setup, the same structure applies whether you’re comparing reCAPTCHA, hCaptcha, or Cloudflare Turnstile. The main difference is the exact token format and validation endpoint.
Client-side checks: browser, app, and script delivery
If the captcha widget is absent or spins forever, check the delivery path first. Many failures come from the client never completing the load.
Common client-side causes
- Ad blockers or privacy tools blocking CAPTCHA assets
- CSP rules that do not allow the script/CDN
- Mixed-content issues on HTTPS pages
- A stale cached script version
- Webviews that don’t support third-party cookies or modern JS as expected
- Race conditions in SPA frameworks where the widget mounts before the DOM is ready
For CaptchaLa, the client loader is served from https://cdn.captcha-cdn.net/captchala-loader.js. If you use a framework like React, Vue, Electron, or Flutter web, confirm the loader is mounted only once and not reinitialized on every route change. The platform also supports native SDKs for Web, iOS, Android, Flutter, and Electron, which helps reduce the “works in browser, breaks in app shell” class of problems.
A quick client checklist:
- Inspect network tab for a 200 on the loader file
- Verify no CSP violation in console
- Confirm the challenge iframe/script is not hidden by CSS
- Make sure cookie/storage permissions are enabled where needed
- Test without VPN, corporate proxy, or tracker-blocking extensions
If your audience uses multiple UI languages, make sure you’re not confusing localization with rendering failures. CaptchaLa supports 8 UI languages, so a non-English UI should still render cleanly if the integration is correct.
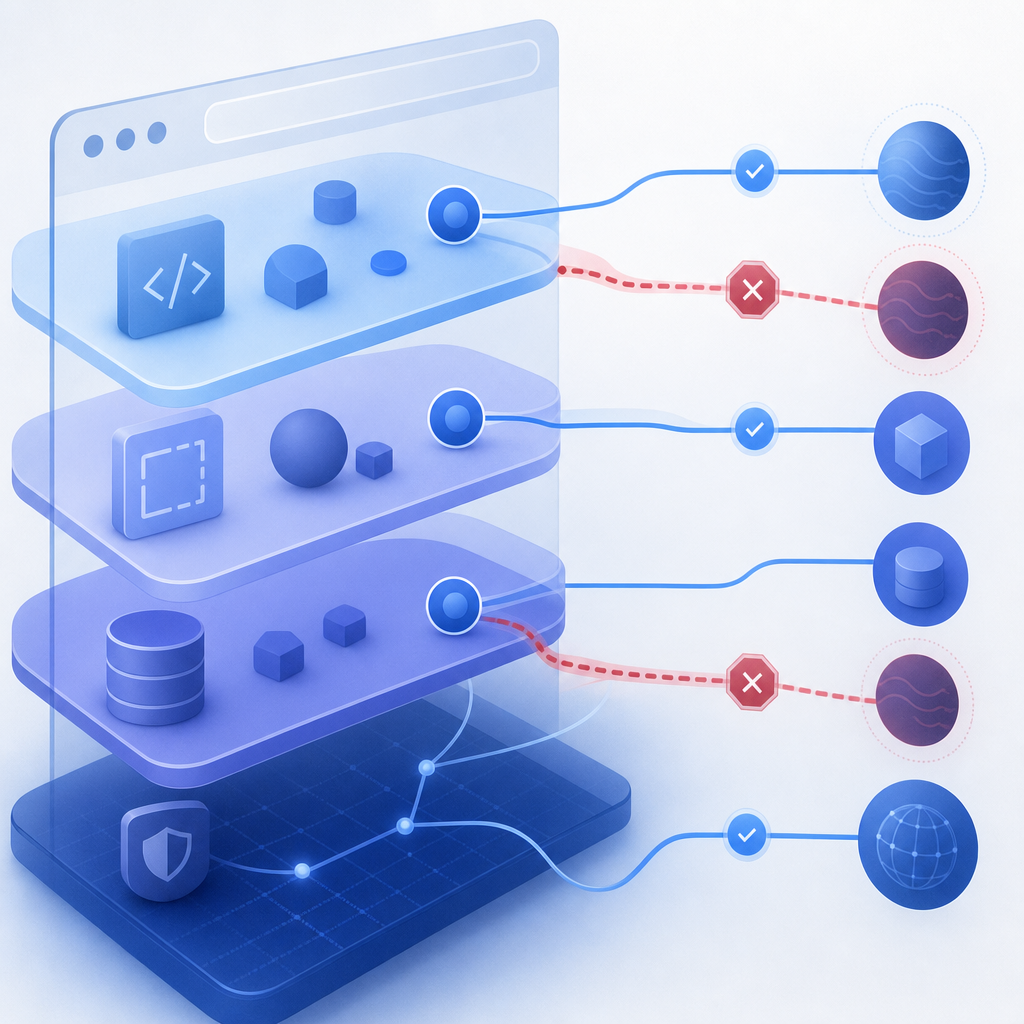
Server-side validation: where many integrations break
A CAPTCHA is only as reliable as the backend check. If the front end collects a pass token but the server never validates it correctly, you’ll see confusing “captcha not working” behavior even though the challenge itself looked fine.
The typical flow is:
- User completes the challenge in the client.
- The client receives a
pass_token. - The client sends
pass_tokenandclient_ipto your server. - Your server validates the token with the CAPTCHA provider.
- Your app allows or denies the action based on the result.
For CaptchaLa, validation is performed via:
POST https://apiv1.captcha.la/v1/validatewith a body like:
{
"pass_token": "token_from_client",
"client_ip": "203.0.113.10"
}and authentication headers:
X-App-KeyX-App-Secret
If your app uses a challenge issuance step, the server-token endpoint is:
POST https://apiv1.captcha.la/v1/server/challenge/issueThat separation is important. The client should not be trusted to self-approve. Validation must happen server-side, and your application should only continue when the provider confirms the token is valid and fresh.
A minimal validation pattern
// English comments only
async function verifyCaptcha(passToken, clientIp) {
const res = await fetch("https://apiv1.captcha.la/v1/validate", {
method: "POST",
headers: {
"Content-Type": "application/json",
"X-App-Key": process.env.CAPTCHALA_APP_KEY,
"X-App-Secret": process.env.CAPTCHALA_APP_SECRET
},
body: JSON.stringify({
pass_token: passToken,
client_ip: clientIp
})
});
const data = await res.json();
// Treat non-OK or invalid responses as deny
return res.ok && data?.valid === true;
}Server-side failure modes to inspect
- Wrong
X-App-KeyorX-App-Secret - Using the token after it expires
- Reusing a pass token more than once
- Sending the wrong client IP format
- Allowing the request even when validation fails
- Not handling upstream timeouts gracefully
If you’re comparing providers, the backend principle is the same across reCAPTCHA, hCaptcha, and Turnstile: the front end gathers proof, but your server decides whether the proof is acceptable. CaptchaLa’s docs cover the request flow and integration points, and the pricing page can help if you’re sizing traffic for a migration or rollout.
Defender-focused fixes for Bluesky-style abuse
Bluesky-like social flows tend to attract automated signups, spam replies, and token replay attempts. If your CAPTCHA “isn’t working,” you may actually be seeing abuse that bypasses weak control points around the CAPTCHA rather than the CAPTCHA itself.
The defender’s goal is not just to show a challenge. It is to make the entire action path trustworthy.
Strengthen the decision chain
Use multiple signals instead of relying on a single pass/fail checkbox:
- Validate the CAPTCHA token server-side.
- Compare
client_ipagainst request metadata and abuse history. - Rate-limit account creation, login, or posting attempts.
- Reject replayed or expired tokens.
- Log suspicious patterns by ASN, region, or user agent cluster.
- Add step-up friction only when risk rises.
That approach is especially useful for apps with bursty public signups or invitation flows. If a CAPTCHA passes but the request pattern still looks automated, you can slow the actor down without breaking legitimate users.
Compare common options objectively
| Provider | Strengths | Tradeoffs |
|---|---|---|
| reCAPTCHA | Familiar to many teams, broad ecosystem support | Can feel heavier in some UX flows |
| hCaptcha | Good fit for bot mitigation with flexible challenges | May require tuning for user experience |
| Cloudflare Turnstile | Lightweight integration in many cases | Best when your stack already fits Cloudflare’s model |
| CaptchaLa | SDKs for web, mobile, Flutter, Electron; first-party data only | Best evaluated by your own traffic patterns and compliance needs |
If you want a smoother implementation path, CaptchaLa’s SDK coverage can reduce glue code across web and app surfaces. But whichever provider you use, the same rule holds: the CAPTCHA is one checkpoint, not the whole defense.
When to escalate the issue
Escalate beyond “basic troubleshooting” if any of these happen:
- The widget loads but validation fails on every device
- The failure rate spikes only behind a proxy or VPN
- Tokens validate in staging but not production
- A mobile or Electron build behaves differently from the browser
- The challenge passes, yet abuse still gets through at scale
At that point, collect logs from the client, your app server, and the CAPTCHA provider response. You want timestamps, request IDs if available, token age, client IP, and the exact validation response. If your implementation spans web and native clients, confirm each SDK version is aligned: Web JS/Vue/React, iOS, Android, Flutter, and Electron can all behave slightly differently when mounted or networked incorrectly.
For new deployments, the free tier can be enough to prove the flow with 1,000 monthly validations. Larger rollouts often move into Pro for 50K-200K or Business for 1M, depending on traffic and risk posture.
Where to go next: if you’re tightening up a Bluesky-style signup or posting flow, review the implementation details in the docs and check the plan fit on pricing.