The best open source captcha depends on what you need to protect: a simple form, a login flow, or a high-risk signup pipeline. If you want maximum control and self-hosting flexibility, open source CAPTCHA projects can be a strong fit. If you want less maintenance and more coverage against modern automation, you may want to compare them with managed alternatives like CaptchaLa and cloud services such as reCAPTCHA, hCaptcha, or Cloudflare Turnstile.
That said, “best” is rarely about the logo on the package. It usually comes down to verification strength, accessibility, integration effort, and how much operational work your team is willing to own. The right choice for a small community site is often very different from the right choice for an API-heavy SaaS.
What “best open source captcha” really means
Open source CAPTCHA tools usually appeal to teams that want transparency, self-hosting, or the ability to inspect and modify challenge logic. Those are real advantages, but they come with tradeoffs: you own updates, fraud tuning, uptime, and the burden of keeping the challenge fresh against automation.
For defenders, the key questions are practical:
- How hard is it to integrate into your stack?
- Does it work for users on mobile and assistive tech?
- Can it stop scripted abuse without creating too many false positives?
- Will it age well as bot tooling changes?
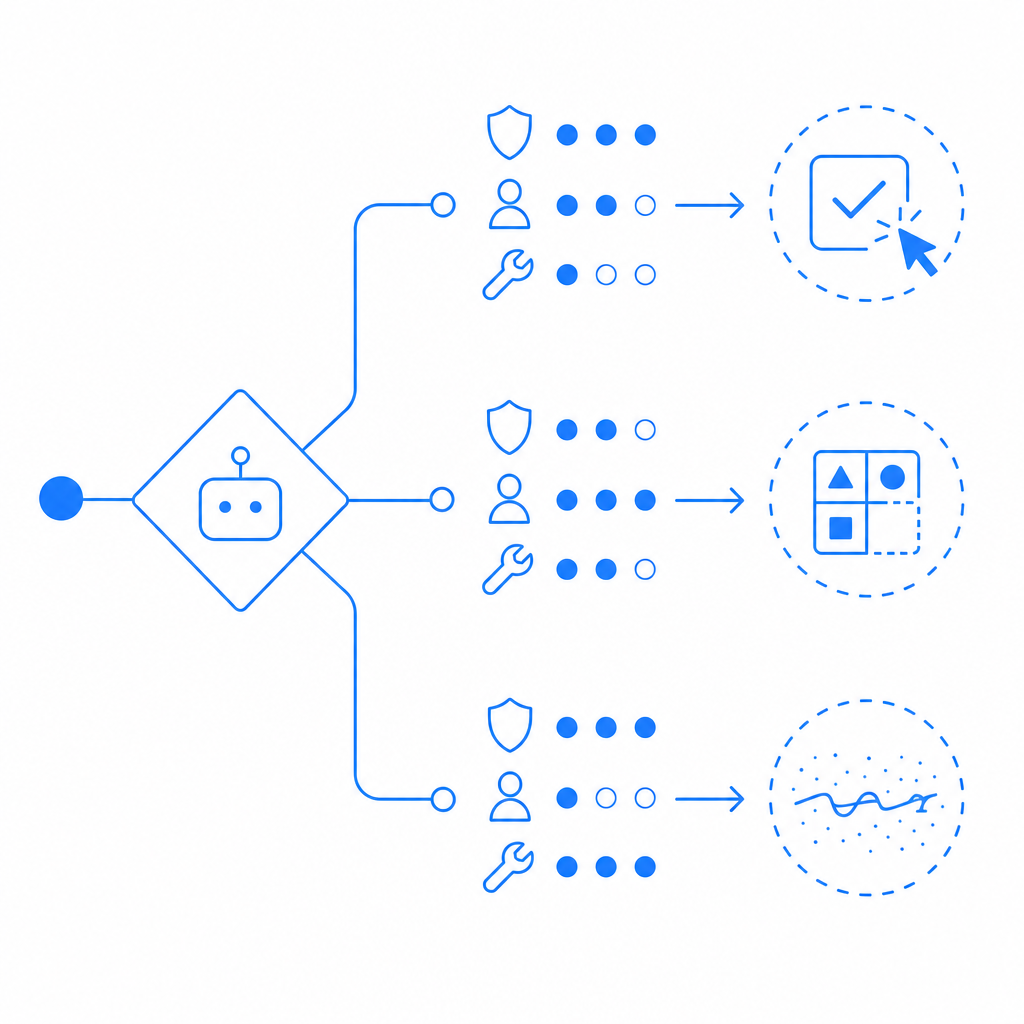
Open source CAPTCHA solutions often do well on control and privacy. They are less consistent on long-term maintenance because the “captcha problem” is not static. Attackers adapt quickly, and static puzzles tend to become training data for automation. If your threat model includes account creation abuse, credential stuffing, or ticket scalping, you need more than a visual challenge.
A defender-friendly way to think about this is: use CAPTCHA as one signal, not the whole decision. Rate limits, device and session signals, IP reputation, and anomaly detection matter too. That is true whether you self-host or use a managed service.
Popular options and how they differ
There isn’t one universally accepted “best open source captcha,” but there are a few common styles of solutions you’ll see in the wild:
| Option type | Typical strengths | Typical drawbacks | Best fit |
|---|---|---|---|
| Image/puzzle CAPTCHA | Familiar to users, simple concept | Can be harder for accessibility, may age poorly | Basic form protection |
| Question-answer CAPTCHA | Easy to build, lightweight | Often weak against automation | Low-risk or internal tools |
| Math/text challenge | Very simple integration | Predictable and easy to script around | Low-abuse apps only |
| Self-hosted challenge framework | Full control, data ownership | More ops work, more tuning required | Teams with security engineering capacity |
| Managed CAPTCHA / bot defense | Ongoing updates, less maintenance | Less control than self-hosting | SaaS, signup, login, and abuse prevention |
Open source projects can be perfectly reasonable if your traffic patterns are modest and your team wants full control. But if you’re defending a public-facing app with meaningful abuse risk, the biggest question is not “Can it present a challenge?” It’s “Can it keep adapting?”
That’s where managed systems often become attractive. For example, CaptchaLa is built around first-party data and supports multiple client SDKs, so teams can integrate bot defense without maintaining challenge logic themselves. It also offers 8 UI languages, which matters if your user base is international.
Some teams compare open source CAPTCHA projects against reCAPTCHA, hCaptcha, and Cloudflare Turnstile. Objectively, those services differ in privacy posture, user friction, and ecosystem fit:
- reCAPTCHA is familiar and widely supported, but it can introduce more friction depending on risk signals.
- hCaptcha is often chosen as an alternative with a different privacy and commercial model.
- Cloudflare Turnstile aims for low-friction verification and may fit sites already using Cloudflare infrastructure.
Each of those can be a valid choice. The right answer depends on your stack, risk tolerance, and whether you want to manage the verification layer yourself.
Technical factors that matter more than branding
If you are evaluating the best open source captcha for defender use, focus on implementation details instead of hype. A few technical factors usually decide whether the project is sustainable.
1) Validation model
Look at how the server verifies the result. A robust design should separate the client challenge from server-side validation and make replay difficult. If your architecture is too simple, attackers will eventually map it.
With managed systems, you typically validate a pass token server-to-server. CaptchaLa’s validation flow is straightforward: your backend sends a POST request to https://apiv1.captcha.la/v1/validate with pass_token and client_ip, authenticated using X-App-Key and X-App-Secret. That kind of pattern is useful because it keeps the trust decision on the server.
2) SDK coverage
The more platforms you support, the fewer custom forks you maintain. If your product spans web and native apps, look for native SDKs rather than trying to shoehorn a web-only widget everywhere.
CaptchaLa supports Web SDKs for JS, Vue, and React, plus iOS, Android, Flutter, and Electron. It also has server SDKs for captchala-php and captchala-go. For teams shipping across channels, that can reduce integration drift.
3) Load and challenge delivery
Challenge delivery should be lightweight and cache-friendly. For browser clients, the loader is served from https://cdn.captcha-cdn.net/captchala-loader.js. If you self-host an open source CAPTCHA, you’ll want to think about asset serving, cache headers, and regional latency yourself.
4) Challenge lifecycle
A useful defense does not rely on one static puzzle. It should support challenge issuance, token validation, and policy changes without forcing a frontend rewrite.
CaptchaLa also provides a server-token issue endpoint at POST https://apiv1.captcha.la/v1/server/challenge/issue, which is helpful when you need to initiate a challenge from backend logic instead of only from the browser.
Here is a simple example of the validation flow from a defender’s point of view:
// Client completes challenge
// Client sends pass_token to your backend
// Backend verifies with CAPTCHA provider
// If valid, allow sensitive action
// If invalid, block or step up authThat looks basic, but the important part is that the trust decision stays server-side. Whether you use open source or managed tooling, avoid making the browser the source of truth.

When open source is the right call
Open source CAPTCHA can be the right answer when one or more of these are true:
- You must self-host for compliance, internal policy, or data-residency reasons.
- Your app has low to moderate abuse risk and you want a simple, inspectable layer.
- You have engineering capacity to maintain and update the challenge experience.
- You need full customization of visuals, text, or localization.
- You want to experiment with nonstandard challenge logic in a controlled environment.
But there are cases where open source becomes more expensive than it looks. If the challenge is easily learned, if accessibility becomes a recurring issue, or if you spend too much time tuning for false positives, the “free” option can cost more in engineering hours than a managed service.
CaptchaLa’s plans illustrate the kind of scaling teams often need to think about. There is a free tier at 1000 monthly uses, Pro at 50K–200K, and Business at 1M. That kind of tiering can be a useful benchmark when you are comparing self-hosting costs against a hosted bot-defense layer.
Practical recommendation
If you want the short version: the best open source captcha is the one you can keep secure, accessible, and maintained over time. For many teams, that means choosing a project that is easy to self-host and easy to replace later if abuse patterns change.
If your traffic is small and your threat model is modest, open source may be enough. If you are protecting signups, logins, contact forms, or checkout flows at scale, a managed system can reduce maintenance while giving you stronger operational controls. That is why many teams evaluate open source CAPTCHA alongside tools like reCAPTCHA, hCaptcha, Cloudflare Turnstile, and CaptchaLa.
For implementation details, see the docs. If you are comparing usage tiers or planning rollout volume, the pricing page is a good place to start.