The best captcha typing website is the one that balances three things well: it stops automated abuse, stays usable for real people, and fits cleanly into your stack without adding maintenance pain. If you’re evaluating options for a site, app, or internal workflow, the right choice is usually not “the hardest puzzle,” but the most reliable verification flow for your risk level.
That means looking beyond the visual challenge itself. You’ll want to compare token validation, SDK coverage, server-side checks, localization, and how each platform handles privacy and scaling. For many teams, that shortlist ends up including reCAPTCHA, hCaptcha, Cloudflare Turnstile, and newer platforms like CaptchaLa when they need a simpler integration path or more control over first-party data.
What “best” really means for a captcha typing website
A “captcha typing website” can mean two different things. For defenders, it’s a site that uses typing or challenge-based verification to separate humans from bots. For researchers or QA teams, it may mean a demo environment where CAPTCHA behavior is tested. Either way, the best choice is less about flashy puzzles and more about operational fit.
Here are the criteria that usually matter most:
Verification quality
The system should meaningfully raise the cost of automated abuse. That means good challenge design, anti-replay protection, and server-side validation that cannot be faked by client-only checks.User experience
A CAPTCHA that blocks legitimate users too often creates abandonment. Good products reduce friction with accessible design, fast loading, and sensible fallback behavior.Integration effort
If it takes a week to wire up a challenge and another week to get validation correct, adoption slows. Look for clear SDKs, straightforward endpoints, and documentation that maps to your language stack.Privacy and data handling
Some teams prefer first-party data handling and minimal sharing. That can be a deciding factor, especially in regulated environments.Operational visibility
You want to know when challenge volume spikes, which routes are under attack, and whether verification failures are due to bots or integration bugs.
A platform can be excellent at one of these and mediocre at the rest. The “best” one is the one that matches your threat model and your product constraints.
Comparing common CAPTCHA and bot-defense options
When people search for the best captcha typing website, they often really want the best CAPTCHA platform for their use case. Here’s a practical comparison of the most common choices.
| Platform | Strong points | Tradeoffs | Best fit |
|---|---|---|---|
| reCAPTCHA | Widely recognized, mature ecosystem | Can feel opaque; UX and privacy concerns vary by implementation | Teams that want familiarity and broad adoption |
| hCaptcha | Strong bot-detection focus; flexible deployment | Can still add friction depending on challenge type | Sites prioritizing abuse prevention |
| Cloudflare Turnstile | Low-friction experience; easy for some Cloudflare users | Best if you already use Cloudflare’s edge stack | Teams already invested in Cloudflare |
| CaptchaLa | First-party data only, broad SDK coverage, server validation endpoints | Smaller ecosystem than legacy incumbents | Teams wanting tighter control and simpler integration |
The comparison is not about declaring a universal winner. For example, if you already run a lot of traffic through Cloudflare, Turnstile may be the lowest-effort option. If your security team wants explicit control over challenge issuance and validation, a more self-contained flow can be easier to reason about. CaptchaLa is built around that style of implementation, with UI coverage in 8 languages and native SDKs for Web, iOS, Android, Flutter, and Electron.
A good way to think about it: the best CAPTCHA is the one your product team can maintain confidently under load, and your security team can audit without surprises.
What to check before you choose a platform
If you’re comparing candidates, focus on the details that affect both security and day-two operations.
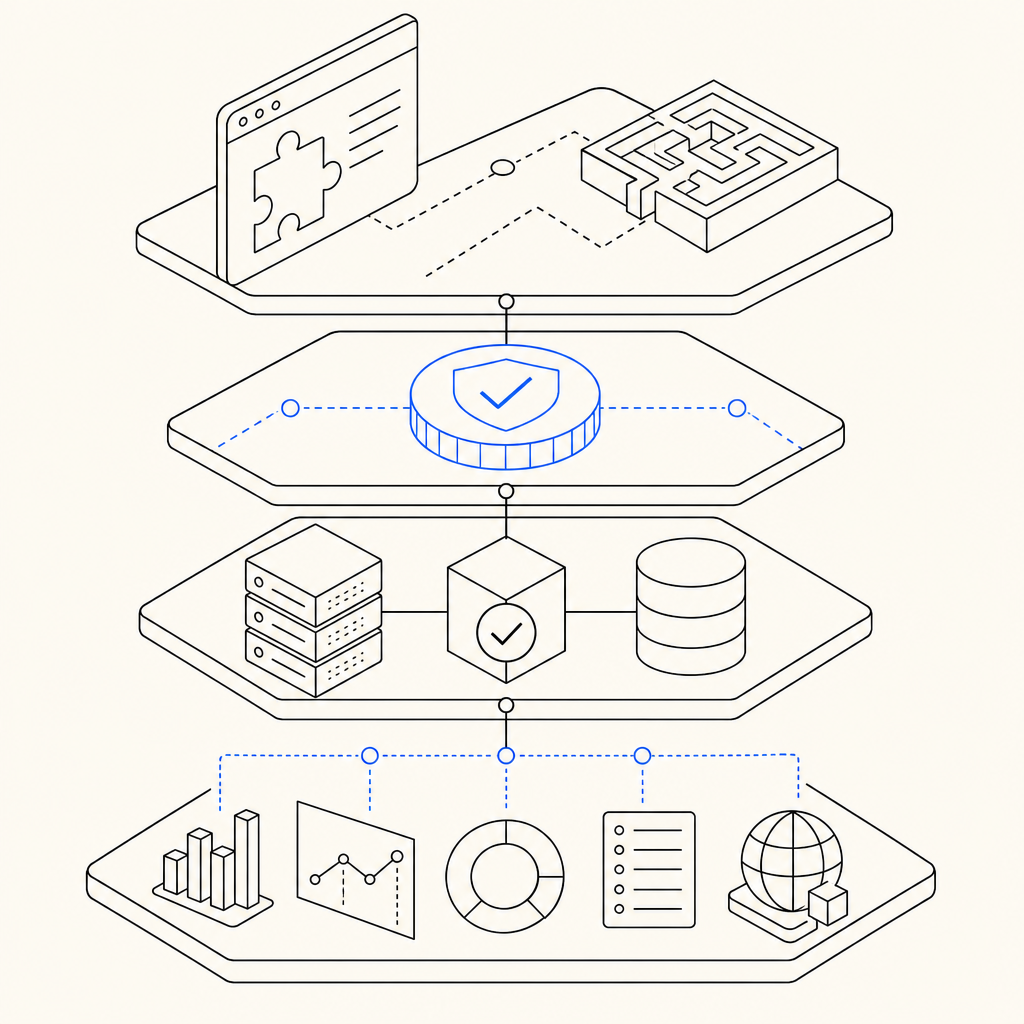
1) Client and SDK coverage
If your product spans web and mobile, SDK breadth matters. Captcha support is often easy on one surface and awkward on another. Look for:
- Web support that works with your frontend framework
- Native SDKs for iOS and Android
- Flutter and Electron support if you ship cross-platform apps
- Language coverage for your backend stack
CaptchaLa, for example, provides SDKs for Web (JS/Vue/React), iOS, Android, Flutter, and Electron, plus server SDKs for captchala-php and captchala-go. That makes it easier to keep challenge behavior consistent across client types.
2) Validation model
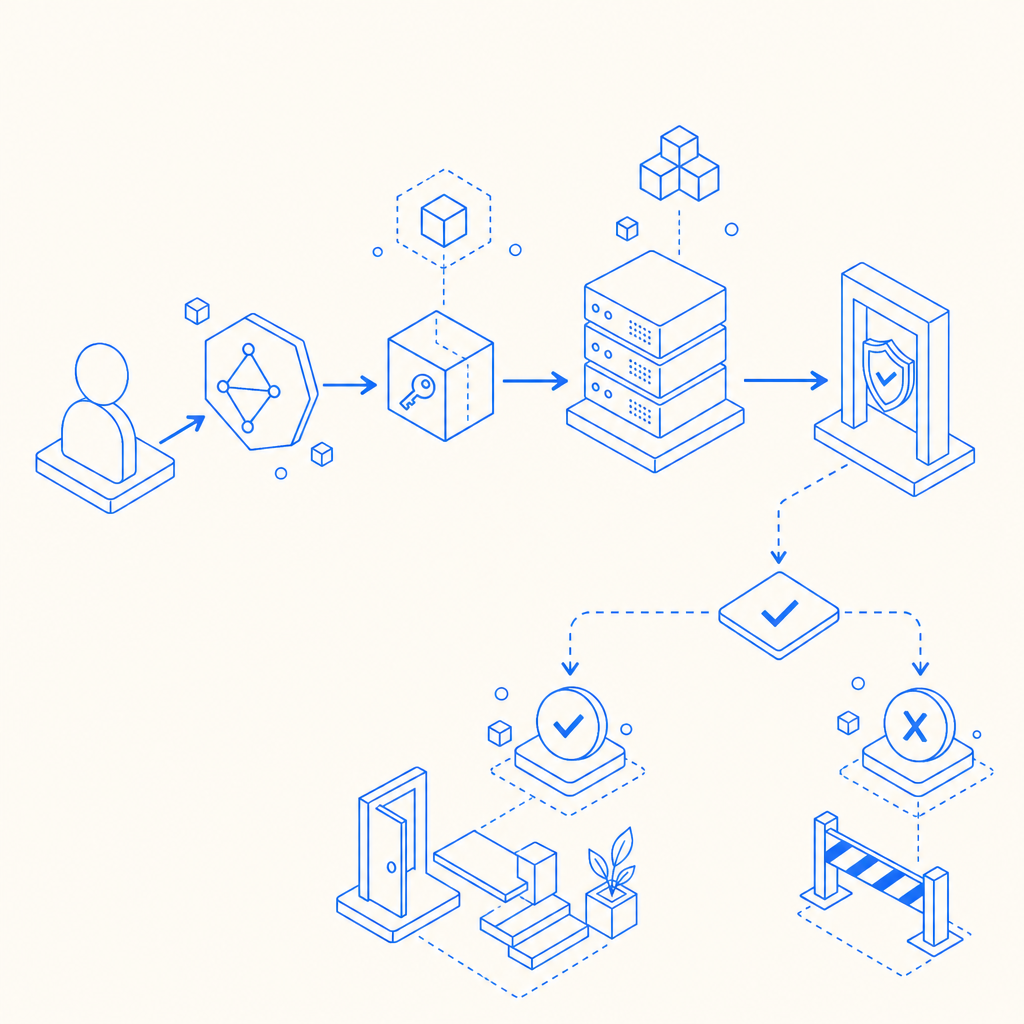
Client-side challenge rendering is only half the story. The important part is server validation. A robust flow should include token issuance, token submission, and a backend check that decides whether the request is allowed.
A typical implementation pattern looks like this:
// Send the challenge result to your backend
// Then validate it server-side before allowing the request
const payload = {
pass_token: token,
client_ip: userIp
};
// Backend should POST to the validation endpoint
// and enforce the result before proceedingFor CaptchaLa, validation is performed with POST https://apiv1.captcha.la/v1/validate using pass_token and client_ip, along with X-App-Key and X-App-Secret. Server-token issuance is handled through POST https://apiv1.captcha.la/v1/server/challenge/issue. That separation is useful because it keeps challenge logic and trust decisions on the server, where they belong.
3) Localization and accessibility
If your product serves global audiences, language support is not cosmetic. A CAPTCHA prompt that is unclear in a user’s language can become a silent conversion killer. Eight UI languages is a meaningful baseline, especially when paired with accessible UI behavior and predictable challenge patterns.
4) Pricing and scaling
The right platform should fit your traffic curve. A site with 30,000 monthly challenges has different needs from one with a million. Public pricing tiers help reduce surprises, especially when you’re budgeting security infrastructure alongside application growth.
CaptchaLa’s current tiers are designed around volume bands: Free at 1,000 per month, Pro at 50K–200K, and Business at 1M. If you want to compare cost against expected challenge volume, the pricing page is the fastest place to start.
5) Data handling
For teams with privacy requirements, “first-party data only” is more than a slogan. It can simplify legal review and reduce concerns about unnecessary data sharing. When evaluating any CAPTCHA platform, ask where challenge data goes, how long it is retained, and what gets sent off-domain.
A practical recommendation by use case
If your goal is simply to stop obvious bot abuse on a small site, a lightweight, low-friction tool may be enough. If you operate account creation, checkout, scraping-sensitive APIs, or ticketing flows, you’ll want more explicit controls and better server-side enforcement.
A simple decision path:
- Low traffic, low risk: choose the tool with the easiest setup and acceptable UX.
- Moderate abuse risk: prioritize token validation, analytics, and framework support.
- High abuse risk: require server-issued tokens, backend verification, and clear operational controls.
- Multi-platform product: pick a provider with consistent SDKs across web and mobile.
- Privacy-sensitive org: review data handling carefully and favor first-party-only designs.
If you’re building or replacing a CAPTCHA layer now, the best approach is usually to pilot one option on a single high-value flow, measure completion rate and abuse reduction, then expand only after validation is stable.
Where to go next: if you want implementation details, start with the docs. If you want to compare plans for your traffic volume, check the pricing page.