Captcha integration in Angular is straightforward when you separate three concerns: load the widget only when needed, bind it to an Angular component cleanly, and verify the result on your server. That structure keeps your UI responsive and your validation trustworthy, whether you use CaptchaLa, reCAPTCHA, hCaptcha, or Cloudflare Turnstile.
Angular is a good fit for this kind of integration because it already encourages component-based boundaries. You can wrap the captcha in a reusable component, keep the token in form state, and send that token to your backend alongside whatever action you are protecting. The important part is not the widget itself; it is the flow around it.

What a solid Angular captcha flow looks like
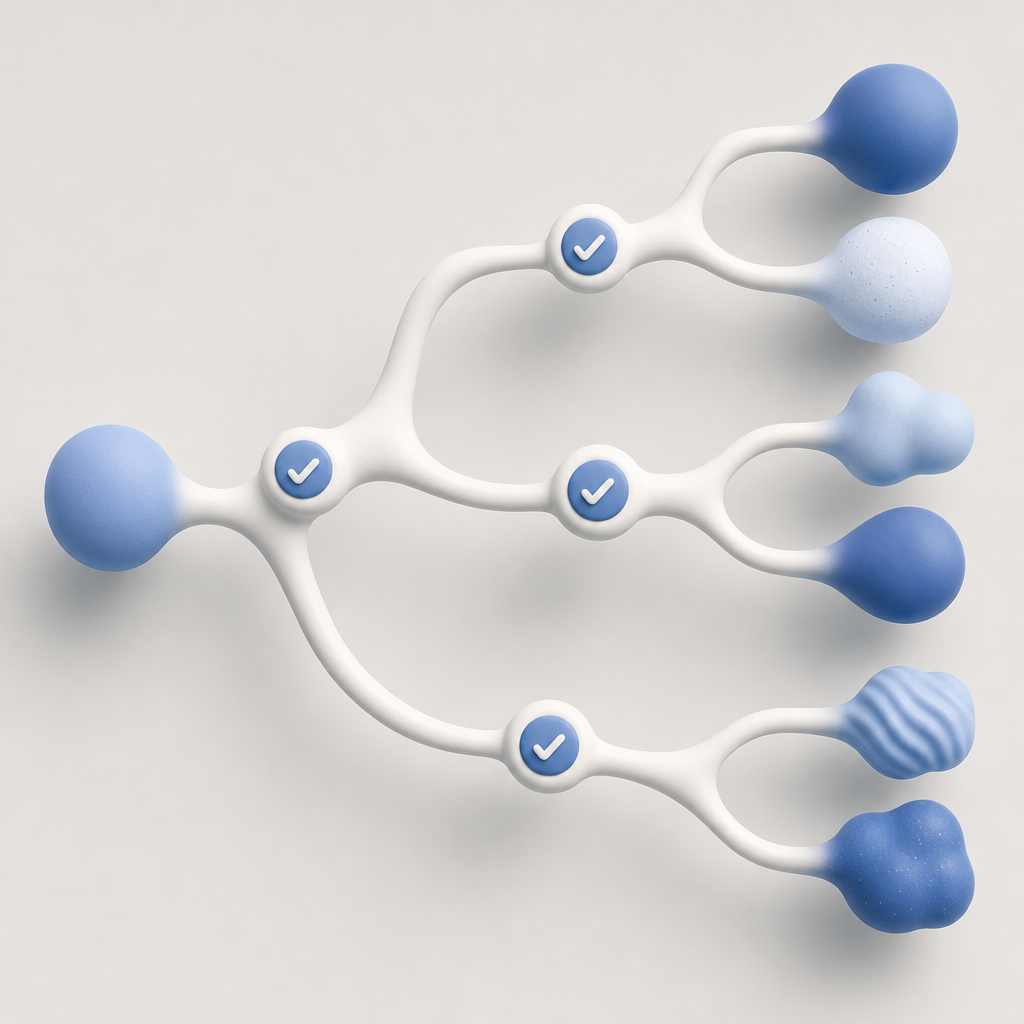
A reliable captcha flow in Angular should do three things:
- Load the challenge lazily so it does not slow every page.
- Capture a short-lived pass token after the user completes the challenge.
- Validate that token on your server before accepting the action.
That third step matters most. A client-side “success” state is not enough by itself, because the browser is the untrusted environment. With CaptchaLa, for example, the server-side validation endpoint is POST https://apiv1.captcha.la/v1/validate, and the request body includes pass_token and client_ip, authenticated with X-App-Key and X-App-Secret. That separation keeps your Angular app simple while your backend makes the trust decision.
Here is the mental model:
- Angular handles rendering and state.
- The captcha provider issues a token.
- Your backend verifies the token before login, signup, checkout, or form submission continues.
If you are comparing providers, the same pattern applies to reCAPTCHA, hCaptcha, and Cloudflare Turnstile. The differences are mostly in widget style, language support, and API shape, not in the basic architecture.
Implementing captcha integration in Angular
A clean Angular implementation usually starts with a dedicated component. The component loads the provider script, renders the challenge, and emits a token to the parent form.
For CaptchaLa, the loader script is:
<script src="https://cdn.captcha-cdn.net/captchala-loader.js"></script>From there, you can wrap the widget in a component and keep your form logic separate. Below is a simple pattern that works well with reactive forms.
import { Component, ElementRef, EventEmitter, Output, ViewChild, AfterViewInit } from '@angular/core';
declare global {
interface Window {
Captchala?: {
render: (container: HTMLElement, options: {
siteKey: string;
onSuccess: (passToken: string) => void;
onError?: () => void;
}) => void;
};
}
}
@Component({
selector: 'app-captcha',
template: `<div #captchaHost></div>`
})
export class CaptchaComponent implements AfterViewInit {
@ViewChild('captchaHost', { static: true }) captchaHost!: ElementRef<HTMLDivElement>;
@Output() verified = new EventEmitter<string>();
ngAfterViewInit(): void {
const widget = window.Captchala;
if (!widget) {
throw new Error('Captcha loader is not available');
}
widget.render(this.captchaHost.nativeElement, {
siteKey: 'your-site-key',
onSuccess: (passToken: string) => {
// Emit token to parent form
this.verified.emit(passToken);
},
onError: () => {
// Handle widget error state
console.warn('Captcha challenge failed');
}
});
}
}Then your form can store the token and submit both the form data and token to your API. A common mistake is to submit the form as soon as the widget returns a token. That is fine only if your backend validates immediately and rejects expired or reused tokens. Otherwise, you are trusting a value that should be treated as temporary evidence, not proof.
Practical integration tips
- Load the loader script once, ideally at the app shell or a guarded route.
- Avoid rendering the widget until the user reaches a sensitive action.
- Reset the challenge after any failed submit.
- Keep the token in memory, not local storage.
- Validate on the server for every protected transaction, not just on first login.
Server-side validation and security boundaries
The backend is where captcha becomes meaningful. Angular can make the user experience smooth, but only your server can decide whether the request is legitimate.
A typical validation request sends the token and client IP to the provider’s validation endpoint. With CaptchaLa, that request looks like this conceptually:
POST https://apiv1.captcha.la/v1/validate- body:
{ pass_token, client_ip } - headers:
X-App-KeyandX-App-Secret
That design is intentionally simple, which makes it easy to integrate with Node, PHP, Go, or any framework behind Angular. If your backend is already using docs for request details, keep the validation step in the same code path as authentication, registration, password reset, or payment initiation.
A good server-side policy usually includes:
- Reject missing tokens immediately.
- Validate the token before any side effects.
- Tie the token to the intended action, if your provider supports action labels or context.
- Check IP and expiry rules where applicable.
- Log failures for abuse analysis, but do not store sensitive user data unnecessarily.
For some deployments, a separate server-to-server challenge flow is also useful. CaptchaLa exposes a server token issuance endpoint at POST https://apiv1.captcha.la/v1/server/challenge/issue, which is helpful when you need backend-driven challenge orchestration instead of purely browser-driven rendering.
Minimal backend example
// English comments only
import fetch from 'node-fetch';
async function validateCaptcha(passToken, clientIp) {
const response = await fetch('https://apiv1.captcha.la/v1/validate', {
method: 'POST',
headers: {
'Content-Type': 'application/json',
'X-App-Key': process.env.CAPTCHALA_APP_KEY,
'X-App-Secret': process.env.CAPTCHALA_APP_SECRET
},
body: JSON.stringify({
pass_token: passToken,
client_ip: clientIp
})
});
if (!response.ok) {
return false;
}
const result = await response.json();
return result?.success === true;
}If you are evaluating providers from a compliance or architecture standpoint, CaptchaLa’s first-party data approach is worth noting. That means you keep the signal collection and validation focus narrow, which can simplify internal reviews and data governance.
Choosing a provider and planning the UX
Angular teams usually compare providers on four practical points: rendering flexibility, localization, validation workflow, and pricing. CaptchaLa supports 8 UI languages and offers native SDKs for Web, iOS, Android, Flutter, and Electron, which can matter if your Angular app is part of a larger product stack.
Here is a quick comparison view:
| Provider | Strengths | Typical considerations |
|---|---|---|
| reCAPTCHA | Very familiar, broad adoption | Can feel heavier depending on version and integration style |
| hCaptcha | Good privacy positioning, flexible deployment | Some teams need more custom styling work |
| Cloudflare Turnstile | Friction-light user experience | Best fit if you already use Cloudflare-oriented tooling |
| CaptchaLa | Simple validation flow, multi-platform SDK coverage | Newer brand, so teams may evaluate docs and fit carefully |
For Angular specifically, the best choice is usually the one that fits your form flow without creating extra friction. If you need a product-wide bot-defense layer across web and mobile, a provider with consistent SDKs can reduce integration overhead. If your use case is limited to a single login form, the smallest possible implementation often wins.
It is also worth aligning captcha placement with the user journey:
- Use it on signup, password reset, email change, contact forms, and checkout.
- Avoid forcing it on every page view unless you have a strong abuse signal.
- Keep copy around the challenge clear, especially for accessibility.
- Preserve keyboard navigation and visible focus states in your Angular template.
If you are still deciding on package tiers, pricing is a useful place to compare usage levels. CaptchaLa’s published tiers include a free tier at 1000 monthly requests, Pro at 50K to 200K, and Business at 1M, which maps well to small apps, growing SaaS products, and higher-volume platforms.
A few Angular-specific implementation details that save time
Angular can make captcha integration cleaner if you lean into its strengths:
- Use a dedicated service to load the script once and share its readiness state.
- Store the token in a form control so validation errors can be surfaced consistently.
- Trigger captcha refresh on submit failures or expired sessions.
- If you use route guards for sensitive areas, prefetch the loader only after the guard passes.
- Keep provider-specific code isolated so you can swap services later without rewriting every form.
If your application has international users, language support matters more than teams expect. Captcha interfaces are part of the trust moment, and a familiar UI language lowers abandonment. CaptchaLa’s 8 UI languages can help there, but the same general rule applies across providers: match the widget language to the user’s locale when possible.
For hybrid stacks, remember that Angular may be just one client in a larger system. If your backend also serves iOS, Android, Flutter, or Electron clients, it can be useful to standardize the verification logic across all surfaces instead of building a separate trust model for each one.
Where to go next
If you are implementing captcha integration in Angular now, start with the smallest protected form, wire the token through your backend, and verify the full request path end to end. Then expand the pattern to other sensitive actions. The docs cover the API details, and CaptchaLa can help if you want a single flow across web and mobile.