If you want to avoid captcha python friction for legitimate users, the answer is not to “defeat” CAPTCHA systems — it is to reduce false positives, validate sessions cleanly, and design your Python-backed flows so real traffic looks trustworthy. That means using stable headers, consistent session handling, rate limits that match your app’s behavior, and a challenge flow that only triggers when risk is actually elevated.
For defenders, “avoid captcha” usually means “avoid making good users prove themselves unnecessarily.” Python applications often run into trouble because background jobs, API clients, or automation-heavy flows can look suspicious if they reuse tokens incorrectly, burst traffic too quickly, or send incomplete metadata. The fix is architectural, not evasive.
Why Python apps trigger extra challenges
Python itself is not the problem. The problem is the pattern of requests around it. A script, cron job, or automation harness can accidentally resemble bot traffic when it behaves like a bot without enough context.
Common causes include:
Bursting too quickly
- Multiple requests in the same second from the same IP or account
- Retry loops that amplify traffic after a timeout
- Parallel workers all hitting the same endpoint
Missing or inconsistent client context
- No stable session cookie
- Rotating IPs from proxies or serverless egress
- User-agent strings that do not match the actual client
Weak challenge integration
- Tokens validated too late
- Reused tokens
- No server-side verification
- Validation that ignores
client_ipentirely
Behavior that looks automated
- Form submits immediately after page load
- Login attempts with no navigation path
- API calls that skip the normal UI lifecycle
The practical goal is to make your Python service predictable to your own bot-defense layer. When the app can explain itself — through token validation, stable sessions, and sensible throttling — legitimate users hit fewer challenges.
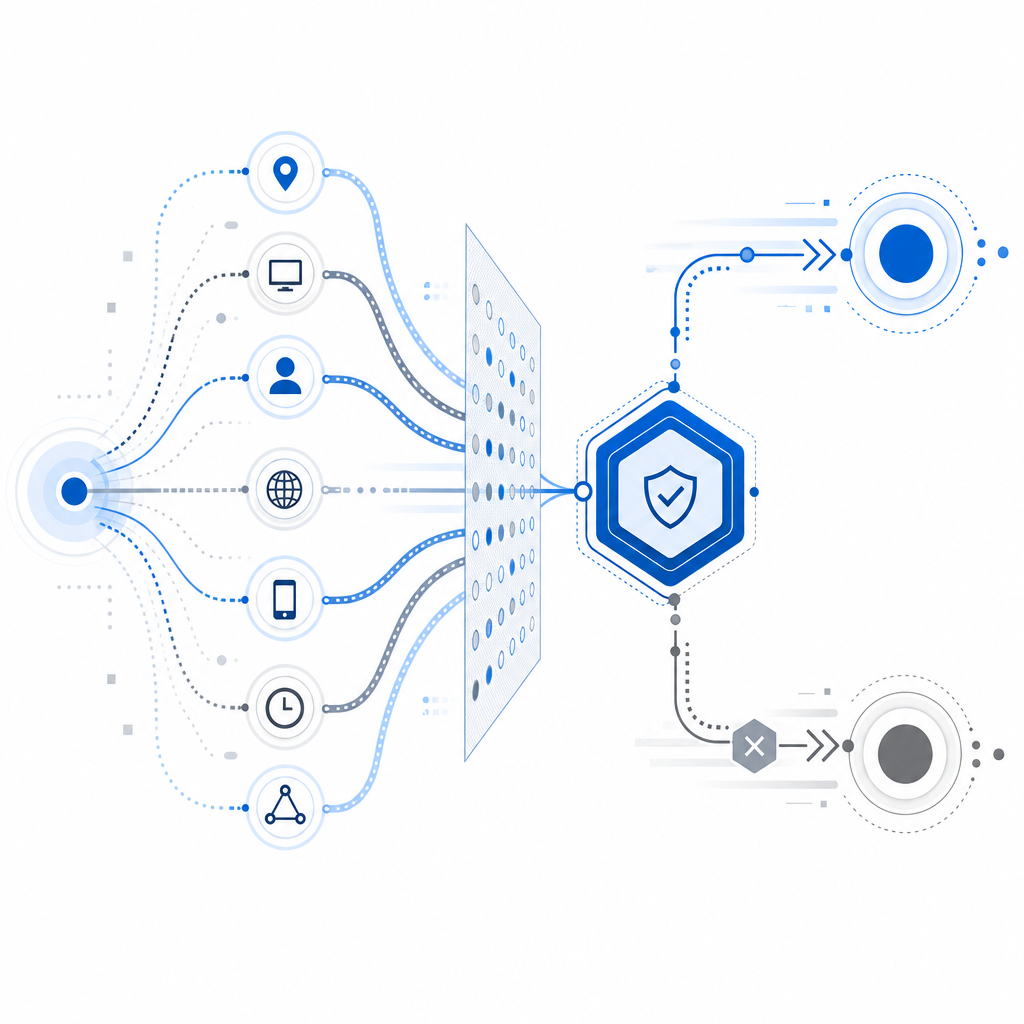
Build a challenge flow that favors real users
A good CAPTCHA flow should be invisible most of the time and strict only when needed. For Python-backed apps, that means splitting the experience into two parts: client-side challenge issuance and server-side validation.
1. Issue a challenge only when risk rises
Do not challenge every request. Trigger the challenge based on signals like:
- repeated failures
- high request velocity
- suspicious account creation patterns
- mismatched geo/session data
- unusual payload structure
CaptchaLa supports a server-token flow via POST https://apiv1.captcha.la/v1/server/challenge/issue, which is useful when your backend decides a user needs an extra verification step.
2. Validate every token server-side
Client-side checks alone are not enough. Validate the result on your backend with:
POST https://apiv1.captcha.la/v1/validate- body:
{pass_token, client_ip} - headers:
X-App-KeyandX-App-Secret
That matters because the backend is where you can tie the token to the actual request, session, and IP context. If you skip this, you make it easier for stale or replayed tokens to slip through.
3. Keep the validation window short
Tokens should be treated as one-time, short-lived artifacts. A secure flow usually:
- presents a challenge
- receives a pass token
- validates immediately on the server
- marks the token as consumed
- proceeds only if validation succeeds
This is especially important in Python APIs where retries are common. If your client retries a completed request, you do not want it to re-submit the same token as if it were fresh.
Example: Python-side validation pattern
import requests
def validate_captcha(pass_token, client_ip, app_key, app_secret):
url = "https://apiv1.captcha.la/v1/validate"
headers = {
"X-App-Key": app_key,
"X-App-Secret": app_secret,
"Content-Type": "application/json",
}
payload = {
"pass_token": pass_token,
"client_ip": client_ip,
}
# Send the validation request immediately after the user completes the challenge
response = requests.post(url, json=payload, headers=headers, timeout=5)
response.raise_for_status()
return response.json()This is not about bypassing anything. It is about making sure the challenge result is trustworthy before your app continues.
Reduce false positives without weakening defense
If your goal is to avoid captcha python interruptions for legitimate traffic, tune the rest of your stack so the CAPTCHA is not carrying all the burden.
Use layered controls
A CAPTCHA is one signal, not the whole defense. Combine it with:
- rate limiting by IP, account, and route
- device/session continuity
- behavioral thresholds for login, signup, and password reset
- request normalization so your backend can compare like with like
- bot reputation checks where appropriate
This layered approach reduces the chance that a single noisy signal trips a challenge.
Preserve first-party context
CaptchaLa is built around first-party data only, which is helpful when you want verification that aligns with your own application context rather than relying on broad third-party profiling. That can make your challenge decisions easier to justify and easier to tune.
Be careful with retries
Python services often use retries for resilience, but retries can create accidental abuse patterns. To avoid self-inflicted CAPTCHA friction:
- cap retries per request
- add exponential backoff
- distinguish network failures from logical failures
- avoid replaying a pass token after a failed downstream step
- log validation outcomes with request IDs
That last point is especially useful when debugging “why did this user get challenged?” If you can trace token issuance, validation, and action completion together, you can usually find the real cause quickly.
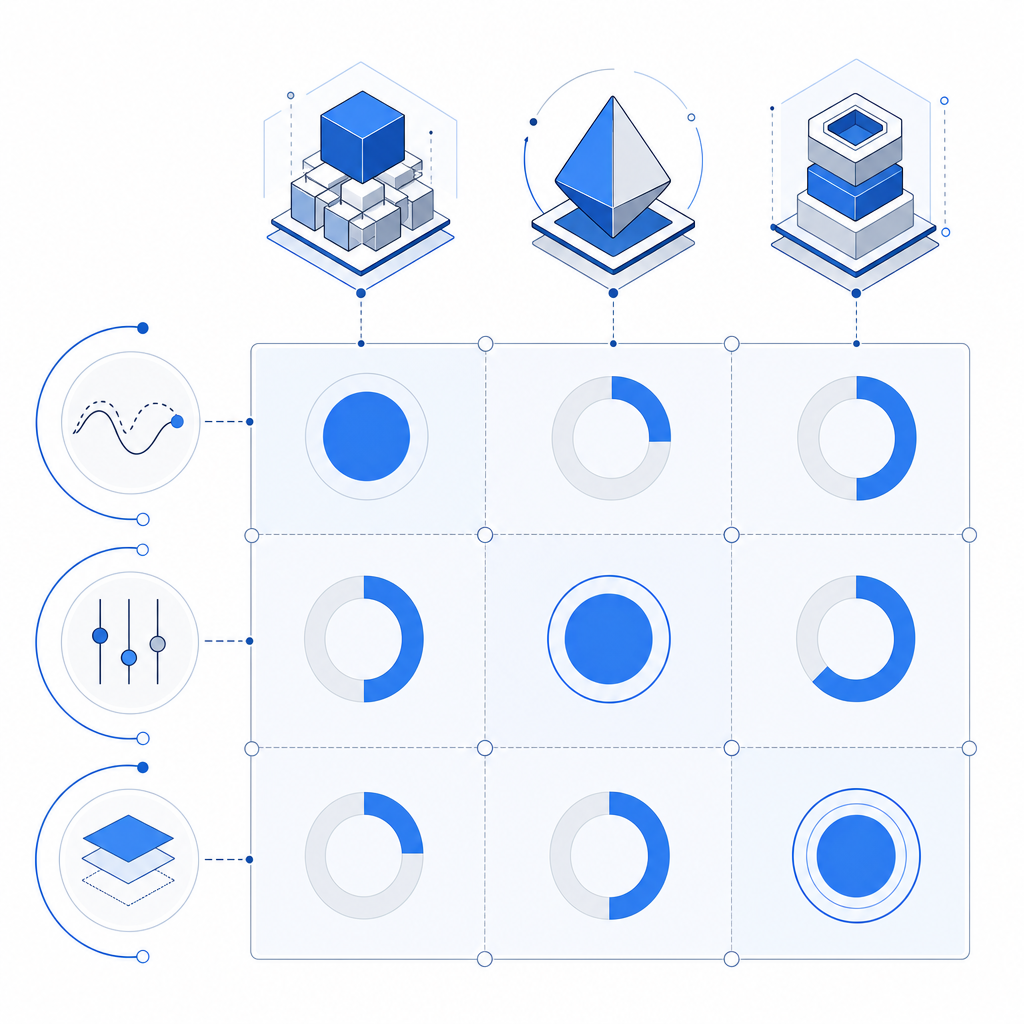
Compare common CAPTCHA options for Python stacks
Different CAPTCHA providers have different trade-offs. The right choice depends on how much control you want over the flow, your Python integration style, and whether you need mobile or desktop support.
| Option | Strengths | Considerations |
|---|---|---|
| reCAPTCHA | Widely recognized, lots of integrations | Can be opaque to tune; some teams want more control over data flow |
| hCaptcha | Flexible challenge options, common alternative | Still requires careful validation and UX tuning |
| Cloudflare Turnstile | Low-friction user experience in many cases | Best fit depends on your edge and app architecture |
| CaptchaLa | Native SDKs for Web, iOS, Android, Flutter, Electron; server SDKs for PHP/Go; 8 UI languages | You still need proper server-side validation and sensible risk rules |
For Python teams, the most important question is not which brand is “stronger.” It is whether the CAPTCHA fits your session model, your risk rules, and your backend verification path.
CaptchaLa also provides native SDKs for Web (JS/Vue/React), iOS, Android, Flutter, and Electron, which matters if your Python service is only one part of a broader product. If your frontend, mobile app, and backend all share the same verification model, you spend less time reconciling edge cases.
A practical checklist for Python teams
If you are trying to keep CAPTCHA friction low while staying secure, start here:
Validate server-side every time
- Use
X-App-KeyandX-App-Secret - Include
pass_tokenandclient_ip - Reject missing or stale tokens
- Use
Challenge selectively
- Only trigger after risk signals accumulate
- Avoid challenging healthy, repeated sessions
- Separate signup, login, and password reset thresholds
Make sessions stable
- Preserve cookies across page transitions
- Keep IP and device signals consistent when possible
- Avoid unnecessary redirects that reset context
Throttle automation-heavy paths
- Add per-account and per-IP limits
- Use backoff for retries
- Watch for concurrency spikes in worker pools
Instrument the flow
- Log challenge issuance
- Log validation responses
- Track challenge completion rates by route
Test with real traffic patterns
- Mobile on flaky networks
- Corporate NAT environments
- Browser privacy features
- High-latency connections
If you want a working implementation reference, the docs are the best place to start. For packaging and rollout planning, the pricing page can help you map usage to the right tier, whether you are on Free, Pro, or Business.
What “avoid” should mean in practice
When developers search for how to avoid captcha python issues, they usually want fewer interruptions, not weaker security. That is the right instinct. The safest way to reduce CAPTCHA prompts is to make your app’s legitimate traffic easy to recognize and your verification path easy to trust.
A well-designed flow should feel almost boring: issue a challenge when needed, validate it immediately, move on. If your Python backend is doing that consistently, your users will see fewer interruptions, and your security team will have cleaner signals to work with.
Where to go next: review the docs for integration details or see pricing to match a deployment tier to your traffic volume.