An API gateway captcha is a challenge step you place at the edge of an API request flow to separate legitimate human-driven traffic from automated abuse before it reaches sensitive services. In practice, that means the gateway can request or validate a pass token, then allow, rate-limit, or block the request based on risk and business rules.
The important part is placement: a captcha at the gateway is usually most useful for endpoints where automation hurts you most — account creation, login, password reset, trial signup, coupon abuse, or high-value form submission. Put it too early and you add friction everywhere; put it too late and your origin systems still absorb the cost of bot traffic.
What an API gateway captcha actually does
An API gateway sits between clients and your upstream services, so it is a natural enforcement point for bot checks. Instead of every service implementing its own challenge logic, the gateway can centralize the decision: is this request from a real client with a valid pass token, or should it be challenged, throttled, or denied?
This is especially useful when your APIs are exposed through one front door but fan out into multiple services. A gateway captcha can protect the whole cluster from:
- credential stuffing against authentication endpoints
- fake account creation and trial abuse
- automated scraping of protected endpoints
- repeated high-cost submissions
- disposable traffic that inflates infrastructure spend
The main design choice is not “captcha or no captcha,” but “where in the flow does verification happen?” Some teams validate at the gateway and forward a clean signal downstream. Others use the gateway to issue or enforce a server token, then verify on the application server only for routes that truly need it.
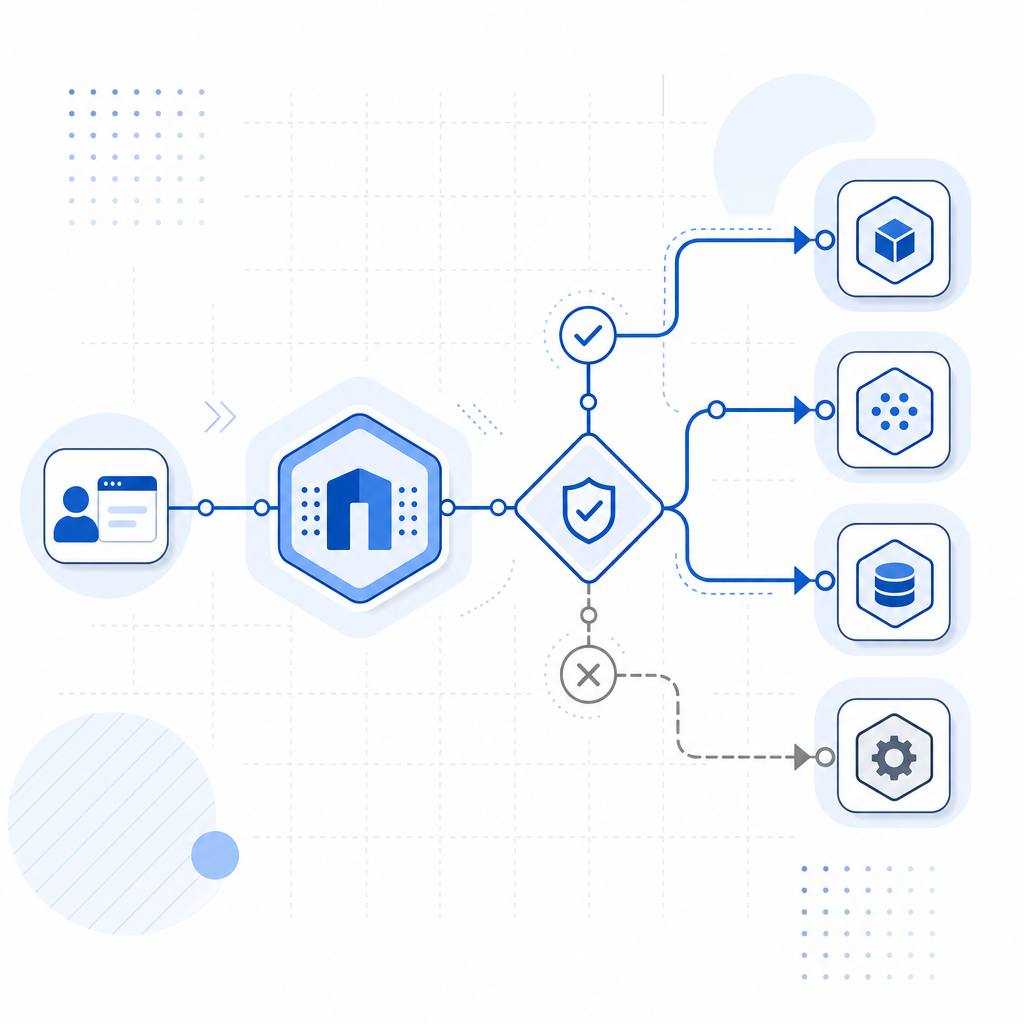
A good mental model is this:
- Client loads a challenge widget or embedded loader.
- Client completes the challenge and receives a pass token.
- The gateway or upstream server validates that token.
- The request is allowed, challenged again, rate-limited, or rejected.
If you use CaptchaLa, the validation step can happen with a simple server-side call to POST https://apiv1.captcha.la/v1/validate, sending {pass_token, client_ip} with X-App-Key and X-App-Secret. That keeps the trust decision on the server side, which is where it belongs.
Where it fits in a modern gateway architecture
The ideal location for an API gateway captcha depends on your traffic patterns and your tolerance for friction. A gateway is great when you want one policy layer for many endpoints, but not every route should behave the same way.
Common placement options
| Placement | What it protects | Pros | Tradeoffs |
|---|---|---|---|
| Before auth | Login, signup, reset flows | Blocks automation early | Can frustrate users if overused |
| After auth, before sensitive action | Profile changes, checkout, transfers | Lower friction for known users | More complexity in policy routing |
| On risk triggers | Unusual velocity, geo mismatch, repeated failures | Adaptive and targeted | Requires event signals and scoring |
| At edge only | Public forms and anonymous APIs | Centralized enforcement | Limited awareness of application context |
A gateway-based approach works well when you already have routing logic for paths, methods, headers, or identities. For example, you might challenge anonymous POST /signup requests, but skip internal service-to-service calls that use mutual trust and machine credentials.
When a gateway captcha is a good fit
- You have multiple apps behind one gateway.
- You want one validation policy instead of duplicating code in every service.
- You need to reduce load before requests hit origin.
- You want to combine captcha with IP reputation, rate limiting, and route-level rules.
- You operate in several locales and need a challenge experience that supports your audience; CaptchaLa supports 8 UI languages, which helps when a single gateway policy serves diverse traffic.
A gateway captcha is less useful when the decision must depend on rich business context that only the application knows. In those cases, validate the token at the app layer after the gateway has already done coarse filtering.
How to implement the validation flow safely
The key is to treat the captcha token as a short-lived signal, not as identity. It tells you that a client completed a challenge; it does not replace authentication, authorization, or abuse monitoring.
A typical safe implementation looks like this:
# English comments only
Client -> Gateway -> Challenge UI -> pass_token
Gateway or app server -> validate pass_token with captcha provider
If valid -> forward request to upstream service
If invalid -> return 403 or trigger step-up challengeFor CaptchaLa, the server-side options are straightforward. Your backend can validate with the /v1/validate endpoint using X-App-Key and X-App-Secret, and certain flows can issue a server token with POST https://apiv1.captcha.la/v1/server/challenge/issue. That gives you a clean pattern for step-up verification on routes that need stronger assurance.
A few implementation details matter a lot:
Bind validation to the client IP when appropriate.
Sendingclient_iphelps reduce token reuse across locations.Keep secrets out of the browser.
X-App-Secretshould stay server-side; the client should only see what it needs to render the challenge.Validate close to the decision point.
If the gateway is making the allow/deny decision, verify there. If the app needs the context, re-check at the app.Log the result, not the token.
Store outcome, route, timestamp, and a request identifier. Avoid writing sensitive token material into logs.Layer captcha with rate limits and reputation signals.
Captcha is strongest as one control in a broader bot-defense stack, not the only control.
If you are building from scratch, the docs are the best place to see how the loader, validation API, and SDKs fit together. CaptchaLa also offers native SDKs for Web, iOS, Android, Flutter, and Electron, plus server SDKs for PHP and Go, which can simplify mixed gateway-and-app deployments.
Comparing captcha options for gateway use
Different providers fit different constraints, and the right choice often depends on how much control you want over the validation path.
- reCAPTCHA is widely recognized and easy to encounter in existing stacks, especially for web forms.
- hCaptcha is often chosen when teams want a similar challenge model with different operational tradeoffs.
- Cloudflare Turnstile is popular for lower-friction challenge experiences at the edge.
Those are all valid tools, but the gateway question is less about branding and more about how the control integrates with your architecture. Ask:
- Can I validate server-side with the exact route context I need?
- Can I keep secrets and trust decisions on the backend?
- Can I support the platforms I ship on, including mobile and desktop?
- Can I combine captcha with my existing gateway policies?
If the answer is yes, the captcha becomes part of your routing logic rather than a separate island. That matters when your public surface includes both browser traffic and native apps. For teams that need one provider across web and native clients, CaptchaLa’s SDK coverage and first-party data model are designed around that kind of deployment, and the pricing page makes the free, Pro, and Business tiers easy to compare if you are estimating traffic volume.

Practical rules for deciding what to protect
Not every endpoint deserves a captcha. Over-challenging users can hurt conversion and create support load, so it helps to define a policy up front.
Protect these first
- public signup and login routes
- password reset and recovery
- trial creation and promo-code submission
- comment, review, and message posting
- expensive or irreversible transactions
- high-velocity API endpoints with anonymous access
Usually skip these
- internal service-to-service calls
- health checks
- background jobs
- admin-only endpoints behind stronger auth
- low-risk read-only endpoints with good rate limiting
A useful rule is to challenge when automation creates asymmetric cost: the bot can send 10,000 requests cheaply, but each request forces you to spend compute, storage, or support time. That is where an api gateway captcha earns its place.
If you are unsure where to start, begin with one route and one metric: failed abuse attempts before and after enforcement. Measure whether challenge completion is acceptable, whether false positives spike, and whether origin load drops. Then expand cautiously.
Closing the loop without overcomplicating the stack
A gateway captcha works best when it is just one decision in a larger request policy. Let the gateway handle coarse filtering, let the app enforce route-specific logic, and keep the validation path simple and server-side. That combination gives you protection without turning every request into a puzzle.
If you want to see the wiring in more detail, start with the docs and then compare traffic tiers on pricing. Where to go next: review your highest-risk routes, map where validation should live, and decide whether the gateway or application should own the final allow/deny decision.