If you need a captcha for Next.js, the cleanest approach is to treat it as a client-side challenge plus a server-side verification step. That gives you a friction point for bots without trusting the browser alone, which is especially important for signup forms, password resets, checkout flows, and any endpoint that can be scripted at scale.
For Next.js specifically, the key decision is not just “which widget do I render?” but “where does validation happen?” A good implementation uses a lightweight loader on the client, sends a pass token back with the form, and verifies that token on your server or route handler before accepting the request. That pattern works whether you use the Pages Router, the App Router, or a separate API backend.

What a captcha for Next.js should actually do
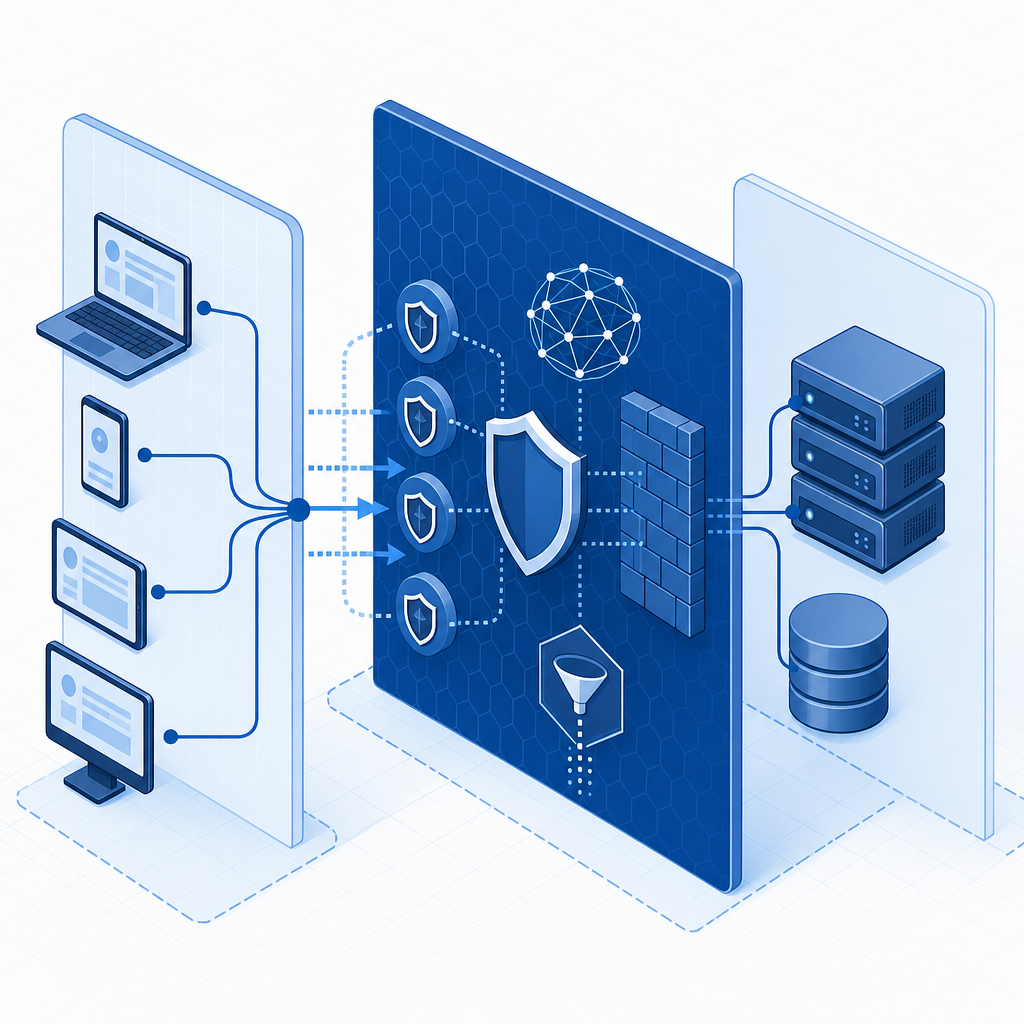
A captcha is not a magic shield. It is one signal in a layered defense strategy. In Next.js, you usually want it to do four things well:
- Reduce automated submissions on high-value routes.
- Avoid adding too much latency to the user experience.
- Work cleanly with React-based forms and server actions.
- Keep verification logic on the server, not in the browser.
That last point matters. If your app only checks a client-side “passed” flag, you have not really verified anything. The browser can be modified, automated, or replayed. Instead, the browser should collect a token after the challenge, then your backend should validate that token with your provider.
A practical implementation pattern looks like this:
- Render the challenge on the client using a loader script.
- Capture the returned pass token.
- Submit the token with the form payload.
- Verify the token server-side with your secret key.
- Accept the action only if validation succeeds.
This model fits Next.js nicely because the framework already encourages a split between client UI and server endpoints. It also makes it easier to reuse the same protection across route handlers, server actions, and traditional API routes.
How to wire it into Next.js
The implementation details depend on your stack, but the structure is consistent. You can mount the widget in a client component, then verify on the server in a route handler or API endpoint.
Here is a minimal flow:
// Client-side form component
'use client';
import { useState } from 'react';
export default function SignupForm() {
const [passToken, setPassToken] = useState('');
async function handleSubmit(e: React.FormEvent<HTMLFormElement>) {
e.preventDefault();
const formData = new FormData(e.currentTarget);
formData.append('pass_token', passToken);
// Send to your Next.js route handler or API route
await fetch('/api/signup', {
method: 'POST',
body: formData,
});
}
return (
<form onSubmit={handleSubmit}>
<input name="email" type="email" required />
<input name="password" type="password" required />
{/* Render your captcha widget here and update passToken on success */}
<button type="submit">Create account</button>
</form>
);
}On the server, validate the token before processing the request. CaptchaLa’s validation endpoint is:
POST https://apiv1.captcha.la/v1/validateThe request body uses pass_token and client_ip, and you send X-App-Key plus X-App-Secret in headers. That keeps the sensitive verification step out of the browser. CaptchaLa also provides a server-token flow for challenge issuance via:
POST https://apiv1.captcha.la/v1/server/challenge/issueIf you prefer a provider-managed loader, the script is:
https://cdn.captcha-cdn.net/captchala-loader.jsFor teams using Next.js App Router, the same pattern works in a route handler. For Pages Router apps, it works in pages/api/*. The important part is that the server, not the client, decides whether the request is trustworthy enough to continue.
Implementation checklist
- Load the captcha widget only on the pages that need it.
- Keep form submission blocked until a pass token is present.
- Forward the user’s IP address when your verification flow requires it.
- Validate tokens inside your route handler or server action.
- Reject replayed, expired, or missing tokens before any business logic runs.
Choosing between reCAPTCHA, hCaptcha, Turnstile, and newer options
There are several reasonable choices for a captcha for Next.js, and the right answer depends on your constraints. reCAPTCHA is familiar and widely documented. hCaptcha is often chosen for its privacy posture and familiar integration pattern. Cloudflare Turnstile is popular for low-friction verification and a simpler end-user experience.
Each can work in Next.js. The differences usually show up in these areas:
| Provider | User friction | Integration style | Server verification | Notes |
|---|---|---|---|---|
| reCAPTCHA | Can vary | Widget or invisible flows | Yes | Common, but often tied to Google ecosystem |
| hCaptcha | Moderate | Widget-based | Yes | Privacy-focused positioning |
| Cloudflare Turnstile | Low | Mostly invisible / lightweight | Yes | Strong fit when minimizing user friction matters |
| CaptchaLa | Flexible | Web SDKs and server validation | Yes | 8 UI languages, native SDKs, and first-party data only |
For a Next.js project, the choice is often less about “which is strongest” and more about operational fit:
- If you want a well-known reference implementation, reCAPTCHA is easy to find examples for.
- If privacy messaging matters, hCaptcha may align better with your product story.
- If you want minimal user friction, Turnstile is attractive.
- If you want a provider built around first-party data only, CaptchaLa is worth evaluating alongside your existing stack.
CaptchaLa supports Web SDKs for JS, Vue, and React, plus native SDKs for iOS, Android, Flutter, and Electron. That matters if your Next.js app is part of a broader product surface and you want a consistent verification model across web and mobile. CaptchaLa also offers server SDKs like captchala-php and captchala-go, which can help if your Next.js frontend talks to another backend service.
If you are comparing vendors, keep your test focused on the actual user journey: time to render, challenge pass rate, token verification complexity, accessibility, and how often legitimate users get blocked.
Practical Next.js deployment tips
A captcha for Next.js works best when it is targeted. You do not need to protect every route. Focus on pages and endpoints with abuse value:
- account creation
- login and password reset
- contact forms
- invite flows
- free trial signup
- checkout or coupon endpoints
- API routes that create expensive resources
That selective approach lowers friction while still reducing bot volume where it matters.
It is also worth thinking about environment-specific behavior:
- Use the challenge only in production and perhaps staging.
- Keep your secret keys in environment variables, never in client bundles.
- Make sure your validation endpoint can read the correct client IP, especially if you are behind a proxy or CDN.
- Log verification failures separately from normal application errors so you can spot abuse patterns.
For teams planning traffic growth, pricing can matter too. CaptchaLa has a free tier for 1,000 monthly requests, Pro tiers in the 50K-200K range, and Business at 1M. If you are prototyping, that can be enough to validate the integration before committing to broader rollout.
Also, do not ignore accessibility and localization. A captcha that frustrates people who use assistive tech or who browse in other languages creates its own conversion problem. Multi-language support helps here; CaptchaLa includes 8 UI languages, which is useful if your Next.js app serves more than one market.
Where this fits in your security stack
Captcha should sit alongside rate limiting, email verification, anomaly detection, and abuse monitoring. If you rely on it alone, you will eventually be disappointed. If you use it as one layer in a broader defense model, it can significantly reduce automated abuse without making your application feel hostile to real users.
That is especially true in Next.js apps, where a single public route can often trigger server-side work, database writes, third-party calls, or account creation. A small verification step up front is much cheaper than cleaning up fake accounts later.
If you want implementation details, the docs cover the validation flow and SDK options, and the pricing page is helpful for estimating volume fit. You can also review CaptchaLa to see whether its web and server support matches your Next.js architecture.
Where to go next: read the docs and choose the integration path that matches your form flow, then estimate traffic against pricing.