An anti nuke bot is a defense system that detects and stops destructive automation before it can mass-delete data, kick users, spam actions, or otherwise “nuke” a community, workspace, or app. In practice, it combines rate limits, anomaly detection, permission checks, and step-up verification so suspicious actions are slowed, challenged, or blocked while legitimate users keep moving.
The term usually shows up in community moderation, Discord-style server defense, admin tooling, and SaaS abuse prevention. But the underlying problem is broader: any product that lets a single actor trigger high-impact actions needs a way to separate normal use from coordinated or scripted abuse. That’s where an anti nuke bot becomes less of a “bot” and more of a policy engine.
What an anti nuke bot actually does
At a high level, an anti nuke bot watches for destructive patterns and intervenes before damage spreads. The “nuke” part is shorthand for a burst of high-impact operations, such as:
- Bulk deletes or bulk role removals
- Rapid permission changes
- Invite/link spam or mass account creation
- Repeated admin-only requests from a suspicious session
- Sudden API spikes from one IP, device, or token family
The core logic is simple: monitor action velocity, context, and privilege. A single delete is not evidence of abuse. Fifty deletes in two seconds from a freshly created account with no historical trust is a different story.
A practical anti nuke bot usually makes one of four decisions:
- Allow the action
- Allow but log and lower trust
- Challenge with verification
- Block and alert moderators or security systems
That last step matters. If you only “detect” destructive automation without creating a response path, you’ve built a dashboard, not a defense.
How to design the detection logic
A good anti nuke bot is less about one magic signal and more about combining weak signals into a strong decision. The trick is to keep false positives low, because admin users and power users often do legitimate things quickly.
Signals worth tracking
You can build a useful policy using signals like these:
- Request rate per user, device, session, and IP
- Action type sensitivity
- Time since account creation
- Changes in geo, ASN, or device fingerprint
- Prior trust level and historical behavior
- Correlation across multiple accounts or tokens
- Failure patterns, such as repeated retries or malformed requests
A simple decision flow
if action is low-risk:
allow
elif trust score is high and rate is normal:
allow and log
elif action burst is suspicious:
challenge the session
elif destructive intent is confirmed:
block the request
notify moderators
preserve audit trailThat flow looks basic, but it works because it respects context. A moderation bot that blindly blocks all rapid actions will frustrate legitimate admins. A system that ignores velocity will eventually get nuked.
One useful technique is step-up verification. Instead of blocking immediately, ask for proof of human interaction or a verified session when the risk rises. This is especially helpful for “first contact” abuse, where the attacker is still probing your defenses.
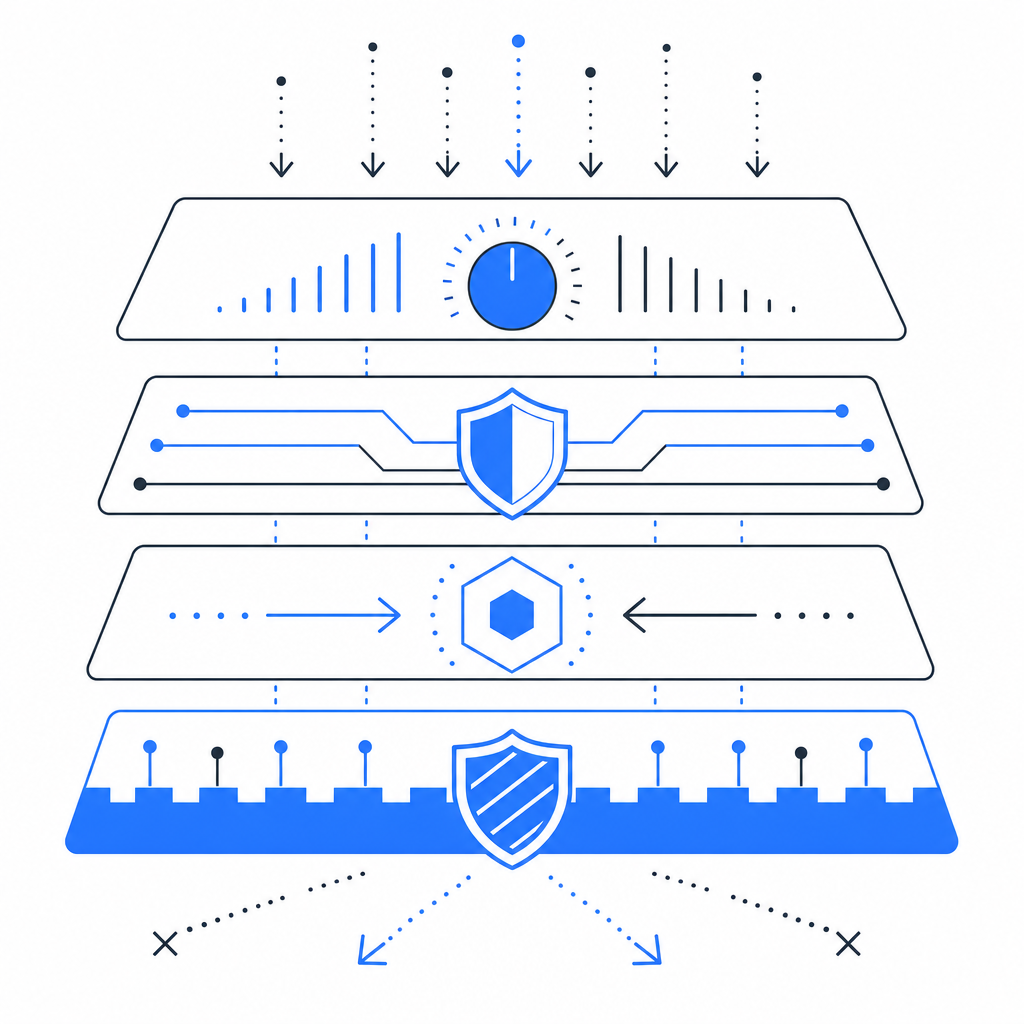
Where CAPTCHA fits in an anti nuke strategy
CAPTCHA is not the entire answer, but it is a strong checkpoint when destructive automation is trying to cross a sensitive boundary. Think of it as one layer in a broader anti nuke bot design.
Use CAPTCHA when:
- A user is about to perform a high-impact action
- You see unusual velocity from a trusted account
- A session suddenly behaves like scripted automation
- You need to verify intent before allowing irreversible operations
That last point is important. CAPTCHA should protect the moment of risk, not just the login form. If an account can log in normally and then mass-delete content without any additional friction, you’ve left the door open.
CaptchaLa supports that model with native SDKs for Web, iOS, Android, Flutter, and Electron, plus 8 UI languages for user-facing flows. For server-side enforcement, you can validate pass tokens with POST https://apiv1.captcha.la/v1/validate using {pass_token, client_ip} and your X-App-Key plus X-App-Secret. If you need a challenge issuance flow, there is also POST https://apiv1.captcha.la/v1/server/challenge/issue. The loader is served from https://cdn.captcha-cdn.net/captchala-loader.js.
If you are comparing vendors, the main tradeoff is usually integration style and how much control you want over the challenge flow. reCAPTCHA, hCaptcha, and Cloudflare Turnstile are all familiar options, and each can fit into an anti abuse stack. The right choice depends on UX, privacy posture, and how tightly you want to couple verification with your own server logic. CaptchaLa is worth looking at when you want first-party data only and a clear validation API, especially for product teams that need a straightforward abuse checkpoint rather than a sprawling security platform.
Example: protect a destructive endpoint
Here is a pattern you can adapt for any high-risk action:
// English comments only
async function performDestructiveAction(req, res) {
const { pass_token } = req.body;
const client_ip = req.ip;
// Validate the challenge before allowing the action
const result = await validateCaptcha({
pass_token,
client_ip
});
if (!result.ok) {
// Stop suspicious automation early
return res.status(403).json({ error: "verification required" });
}
// Continue with the high-impact operation
await deleteSensitiveResource(req.user.id);
return res.json({ success: true });
}That pattern is simple, but the placement matters. Put the check immediately before the destructive action, not only at login.
Comparing common anti-abuse controls
An anti nuke bot works best when paired with other controls. Here is a practical comparison:
| Control | What it catches well | Main limitation | Best use |
|---|---|---|---|
| Rate limiting | Bursty abuse from one source | Can be bypassed by distributed attacks | First-line throttle |
| Permission checks | Unauthorized actions | Doesn’t stop compromised admins | Access control |
| Anomaly detection | Unusual patterns | Needs tuning and data | Risk scoring |
| CAPTCHA / challenge | Human-vs-automation tests | Adds friction | Step-up verification |
| Audit logs | Post-incident analysis | Not preventive alone | Forensics and alerts |
The strongest systems use several layers together. A rate limit slows the blast radius. A permission check blocks privilege abuse. A CAPTCHA challenge verifies intent. Logs and alerts help you see the pattern before it spreads.
For implementation details, the docs are useful if you want to wire verification into a custom flow, and pricing shows how the free and paid tiers line up with different traffic levels. CaptchaLa’s tiers are straightforward: Free covers 1,000 monthly validations, Pro spans 50K–200K, and Business is designed for 1M-scale usage.
Operational tips for real-world deployments
An anti nuke bot should be tuned like a safety system, not a blunt hammer. A few practical habits go a long way:
- Protect the irreversible actions first. Deleting resources, removing members, changing billing, and rotating secrets should have the strictest checks.
- Use trust decay carefully. New accounts should be scrutinized more heavily, but long-term users should not become permanently exempt.
- Log the reason for each decision. When a challenge or block happens, record the signal mix that triggered it.
- Make moderation escalation visible. If an admin is challenged, support staff should know why.
- Review false positives weekly. If legitimate workflows keep getting caught, your policy is too aggressive.
- Keep the response proportional. Sometimes a challenge is enough; sometimes you need a temporary freeze or manual review.
A useful mental model is “friction by risk.” Low-risk users should barely notice the system. High-risk actions should trigger increasing resistance.
Building for abuse without punishing everyone
The best anti nuke bot designs assume abuse will happen, but they also assume most users are honest. That balance is what keeps your product usable. If you make every action feel like a security exam, users will resent the defense. If you make everything seamless, attackers will eventually find the weakest path and automate through it.
That is why modern abuse prevention tends to separate identity, behavior, and action risk. Identity tells you who the actor claims to be. Behavior tells you whether the session looks normal. Action risk tells you how much damage the next click could cause. When those three layers disagree, that is your cue to step in.
If you are starting from scratch, focus on the highest-value actions and add verification only where the blast radius justifies it. A small amount of well-placed friction is usually better than a heavy-handed wall around the entire app.
Where to go next: if you want to add step-up verification to risky flows, start with the docs or review pricing for the plan that matches your traffic.