If you need a captcha for android app protection, the short answer is: use it at the points where bots can do real damage, and keep the verification flow lightweight enough that legitimate users barely notice. For Android, that usually means account creation, login, password reset, abuse-prone forms, promo claims, and suspicious transaction steps — not every tap in the app.
The goal is not to “block automation forever.” It is to raise the cost of abuse while preserving a smooth path for normal users. On Android, that means choosing a CAPTCHA or bot-defense flow that fits your app architecture, integrates cleanly with your backend, and gives you server-side validation you can trust.

What a captcha for Android app should do
A useful Android CAPTCHA setup has three jobs:
- Detect suspicious interaction before a high-risk action completes.
- Issue a short-lived proof that the client actually passed the challenge.
- Let your server verify that proof against your own policy.
That last part matters most. A challenge solved on-device is not enough by itself; your backend should confirm the pass token before granting access, creating an account, or accepting a sensitive action.
For Android apps specifically, the implementation should also account for:
- Native app flows that may not have a browser page to embed a web widget
- Intermittent connectivity, so the challenge experience should fail gracefully
- Multiple entry points such as login, checkout, referral codes, and signup
- Risk-based triggering, since showing challenges too often hurts conversion
Some teams still think of CAPTCHA as a visual puzzle. In practice, modern bot defense is more about risk signals, client attestation, and server-side validation than asking users to decipher distorted text.
Where to place challenges
A good rule is to challenge only when the action is valuable to an attacker. For example:
- Account creation
- Login after repeated failures
- Password reset
- SMS / email verification requests
- Free-trial activation
- Coupon redemption
- API actions exposed through the mobile app
If you challenge too early, you add friction. If you challenge too late, abuse may already be done.
Choosing an approach: web widget, native SDK, or hybrid
Android teams usually pick one of three patterns.
| Approach | Good for | Tradeoffs |
|---|---|---|
| Web-based challenge in a WebView or browser tab | Simple rollout, existing web backend | More friction, less native feel |
| Native Android SDK | Better app UX, tighter integration | Requires SDK maintenance and release management |
| Hybrid risk-based flow | High-risk actions only, dynamic triggering | More logic in backend and client |
If your app is already using a mobile web experience, a web widget may be enough. If you want a smoother native experience, an SDK is usually a better fit. CaptchaLa offers native SDKs for Android and Flutter, plus web, iOS, and Electron, so teams can keep the same backend verification pattern across platforms. It also supports 8 UI languages, which helps if your app serves multilingual audiences.
For Android builds, the Maven coordinate is:
la.captcha:captchala:1.0.2
That makes it straightforward to wire into a Gradle-based project. If your product also has iOS or cross-platform components, the same service can be consumed with CocoaPods (Captchala 1.0.2) and pub.dev (captchala 1.3.2) for Flutter.
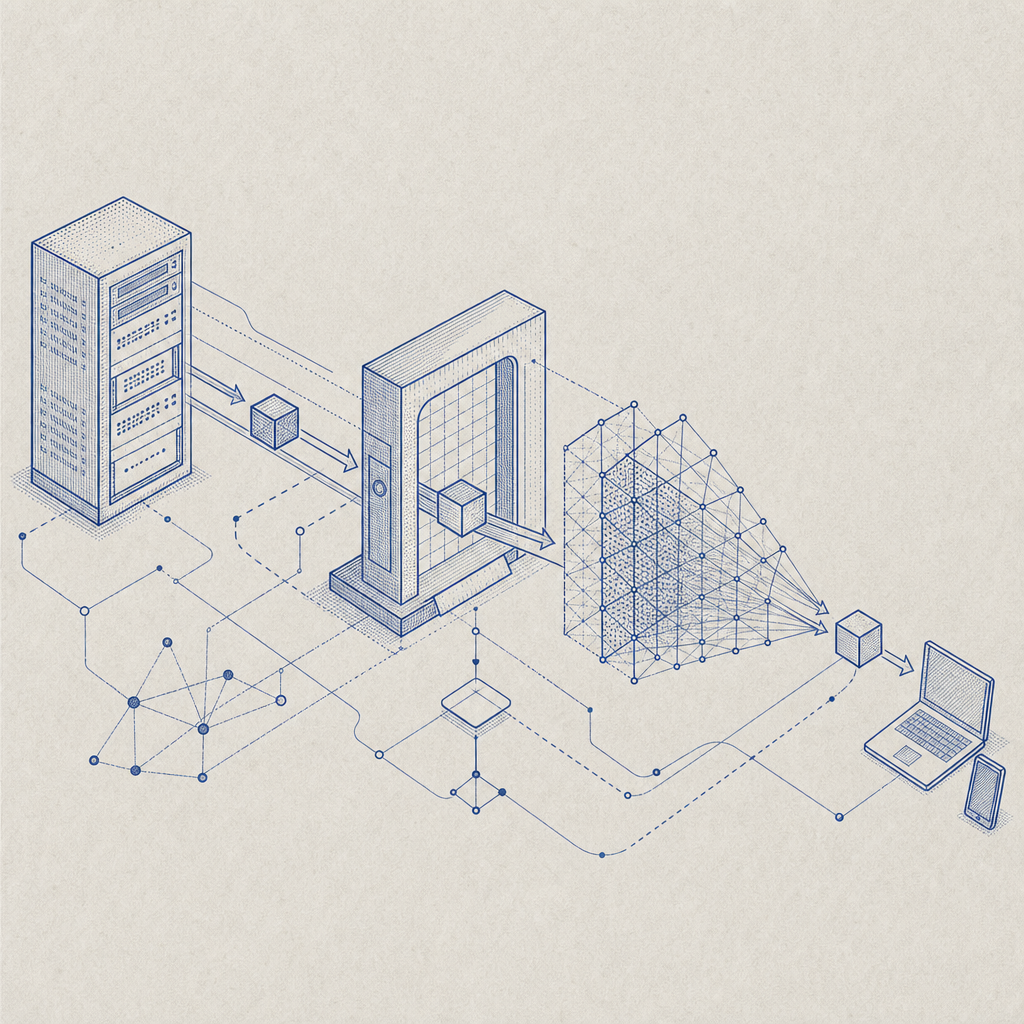
A practical Android verification flow
The safest pattern is: challenge on the client, verify on the server, then allow the action only if verification succeeds.
A typical flow looks like this:
- The app decides a step is high risk.
- The Android client requests or displays a challenge.
- The user completes the challenge.
- The client receives a
pass_token. - The app sends that token to your backend.
- Your backend calls the verification endpoint.
- The backend grants or denies the action.
Here is a simple backend-oriented sequence you can adapt:
Android app -> challenge UI -> pass_token
Android app -> your backend -> validate token
your backend -> allow or deny sensitive actionAnd the validation call itself follows a straightforward model:
POST https://apiv1.captcha.la/v1/validate
Headers:
X-App-Key: your_app_key
X-App-Secret: your_app_secret
Body:
{
"pass_token": "token_from_client",
"client_ip": "203.0.113.42"
}That is the important security boundary: the Android client should not be the final authority. Your server should be.
CaptchaLa also provides a server-token issuance endpoint when your workflow needs an application-generated challenge token:
POST https://apiv1.captcha.la/v1/server/challenge/issue
If you are using a server-side challenge model, keep the logic on the backend and pass only the minimum necessary data to the device. CaptchaLa’s docs are useful here: docs.
Implementation notes for Android teams
A few technical details make the difference between a clean rollout and a flaky one:
- Bind verification to the action you are protecting. A token used for signup should not automatically authorize password reset.
- Use short expiration windows for challenge tokens to reduce replay risk.
- Send the client IP to validation when you have a reliable source for it.
- Fail closed on sensitive actions if verification cannot be completed.
- Log outcomes so you can measure false positives and abuse trends.
If you already have a backend in PHP or Go, CaptchaLa’s server SDKs can simplify integration: captchala-php and captchala-go. If you are running a mixed stack, that can save you from reimplementing the same validation logic in every service.
How it compares with reCAPTCHA, hCaptcha, and Turnstile
Teams often ask whether they should use reCAPTCHA, hCaptcha, Cloudflare Turnstile, or another vendor. The answer depends on your product constraints, privacy posture, and integration style.
A fair high-level comparison:
| Service | Typical strength | Consideration |
|---|---|---|
| reCAPTCHA | Familiar to many teams, widely documented | Can feel more intrusive depending on configuration |
| hCaptcha | Common alternative with similar use cases | UX and tuning may differ by audience |
| Cloudflare Turnstile | Often low-friction, modern bot checks | Best fit when Cloudflare ecosystem already fits your stack |
| CaptchaLa | Mobile-friendly options, native SDKs, first-party data only | Requires your own integration and backend validation |
Two details matter for Android apps in particular:
- Native support: if your app is native Android, an SDK-based flow can be cleaner than forcing a web flow into a mobile screen.
- Data handling: CaptchaLa uses first-party data only, which may simplify privacy review for some teams.
None of these services is universally “better.” The right choice depends on how often you challenge, how much friction you can tolerate, and how much control you want over the verification flow. For pricing and plan sizing, see pricing.
Deployment tips that reduce friction and abuse
If you want the CAPTCHA to help rather than annoy, focus on policy design as much as UI design.
1. Trigger adaptively
Use signals like failed attempts, velocity, device reputation, and unusual navigation patterns to decide when to show a challenge. A blanket “every login gets a CAPTCHA” policy is usually too blunt.
2. Keep the challenge near the risky action
Do not challenge users at app launch unless there is a strong reason. Challenge immediately before the protected action so the user understands why it is there.
3. Measure false positives
Track:
- challenge display rate
- completion rate
- validation failure rate
- drop-off after challenge
- abuse prevented per 1,000 challenges
If legitimate users are failing often, tune thresholds before expanding rollout.
4. Protect the backend endpoint
Your validation endpoint should be treated like any other auth-sensitive route:
- rate limit requests
- store secrets server-side only
- reject malformed tokens
- log suspicious IP patterns
- rotate credentials if exposed
5. Plan for localization
If your app serves multiple regions, ensure the challenge UI and surrounding copy are understandable. CaptchaLa supports 8 UI languages, which can reduce friction for international audiences without requiring separate app builds.
A simple recommendation for Android teams
If your app is new and you want a clean starting point, use a risk-based CAPTCHA only on high-value actions, verify everything on your server, and keep the client integration thin. If you already run a web product alongside Android, reuse the same backend verification model so your policy stays consistent across surfaces.
For many teams, that means a native Android SDK on the client, a validation call on the backend, and careful throttling around signup and login. That is usually enough to stop routine automation without making the app feel gated.
Where to go next: review the integration details in the docs, then check pricing to match your traffic volume and rollout plan.