An anti join bot is a security mechanism designed to prevent automated scripts or bots from mass-creating or joining accounts on a platform. These bots can flood websites, forums, or apps with fake users that degrade service quality, skew analytics, or aid fraudulent schemes. Implementing a robust anti join bot strategy ensures only legitimate users successfully complete the join or sign-up process, preserving the integrity and security of your user base.
Understanding Anti Join Bots and Their Impact
Join bots are automated programs specifically crafted to register on sites repeatedly, often exploiting signup forms without user consent or benefit. These bots generate fake accounts at scale, which can be used for spamming, scraping, spreading misinformation, or other malicious activities. Unlike generic bot traffic, join bots target the user acquisition funnel directly.
For community-driven platforms or SaaS products, unchecked join bots may:
- Inflate user counts with fake profiles
- Facilitate fraud by creating disposable accounts
- Consume resources like bandwidth and storage unnecessarily
- Reduce overall engagement and trustworthiness of data
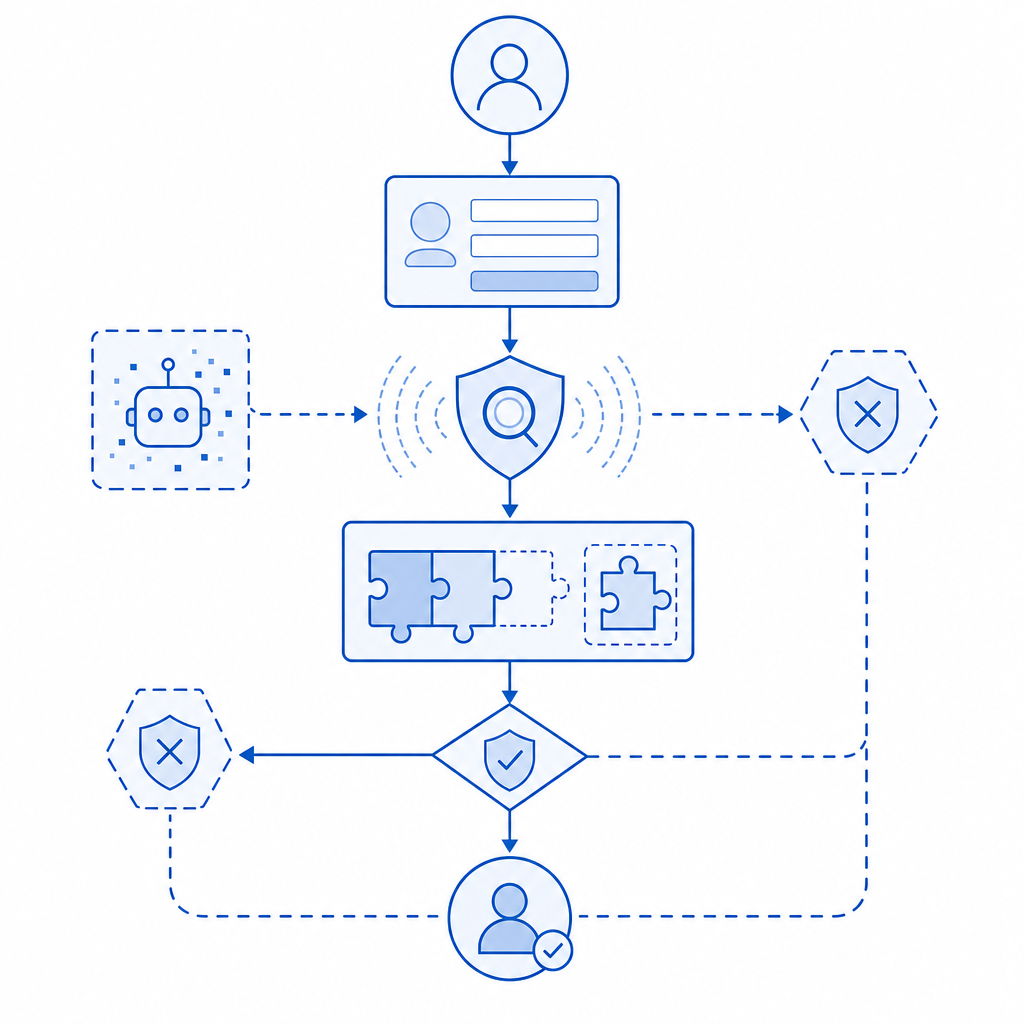
Thus, an anti join bot solution must focus on differentiating human signups from automated ones by analyzing behavioral signals, interaction complexity, and other verification factors.
Key Components of an Effective Anti Join Bot Strategy
Implementing an anti join bot system requires a layered approach, combining multiple technologies and best practices:
1. Challenge-Response Tests (CAPTCHAs)
CAPTCHAs remain a frontline defense. These tests ask users to perform tasks that are easy for humans but challenging for bots, such as identifying images or solving puzzles.
- Modern CAPTCHA providers like CaptchaLa offer adaptive puzzles that adjust difficulty based on suspicion level
- Multiple UI language support and native SDKs (JS, React, iOS, Android, Flutter) improve accessibility and usability for global audiences
- Server-side validations using robust APIs (e.g., POST https://apiv1.captcha.la/v1/validate) confirm token legitimacy
2. Behavioral Analysis
Tracking user interaction patterns—mouse movements, typing speed, or dwell time on fields—helps distinguish bots that often click or type unrealistically fast.
3. Rate Limiting & IP Reputation
Limiting the number of sign-up attempts from a single IP address or subnet reduces bot flood risk. Incorporating IP reputation databases further filters suspicious sources.
4. Email and Phone Verification
Layering email confirmation or SMS OTPs prevents automated bulk account creation without valid contact info.
5. Device Fingerprinting and Session Analysis
Collecting non-invasive device and session metadata can identify patterns of automated traffic over time.
Comparing Popular Anti Join Bot Solutions
Here’s a high-level comparison of some widely-used anti bot tools focusing on join/signup forms:
| Feature | CaptchaLa | reCAPTCHA | hCaptcha | Cloudflare Turnstile |
|---|---|---|---|---|
| CAPTCHA Complexity | Adaptive, multiple UI languages | Image-based puzzles, audio option | Simple/complex, privacy-focused OCR | Invisible challenge, low friction |
| SDK Support | Web (JS, React, Vue), iOS, Android, Flutter, Electron | Web, mobile (Android/iOS) | Web, mobile | Web only |
| Server Validation | API POST with X-App-Key/Secret | API token verification | API token validation | Token-based verification |
| Pricing Model | Free tier (1,000/mo), Pro, Business tiers | Free | Free and paid tiers | Free with paid enterprise options |
| Privacy Focus | First-party data only, GDPR-compliant | Google data sharing concerns | Strong privacy controls | Privacy-friendly, minimal tracking |
Each solution has merits, but selecting the right one depends on your platform’s technical stack, user experience preferences, and security needs.

Implementing Anti Join Bot with CaptchaLa: Technical Overview
For developers looking to add a CAPTCHA layer to their signup forms, CaptchaLa provides flexible tools:
Client Integration
Load the CAPTCHA widget via the CDN script:html<script src="https://cdn.captcha-cdn.net/captchala-loader.js"></script>Render in Your UI
Initialize the challenge via JavaScript SDK or directly in framework components.Server-Side Validation
After the client completes the challenge, send a POST request with thepass_tokenandclient_ipto:bashPOST https://apiv1.captcha.la/v1/validate Headers: { 'X-App-Key': '<your-key>', 'X-App-Secret': '<your-secret>' } Body: { pass_token: '<token>', client_ip: '<ip-address>' }Issue Server Tokens
For advanced integrations using server-issued challenges, call:bashPOST https://apiv1.captcha.la/v1/server/challenge/issueUse Native SDKs
For mobile or desktop apps, libraries likecaptchala-php,captchala-go, or mobile CocoaPods and Maven packages make implementation straightforward.
Practical Tips to Strengthen Anti Join Bot Measures
- Monitor signup activity for unusual spikes or geographic anomalies.
- Combine CAPTCHA with multi-factor verification for high-risk accounts.
- Rotate challenge types randomly to avoid pattern exploitation.
- Employ progressive profiling—ask fewer questions initially, then request more verification for suspicious users.
Conclusion
An anti join bot system is not just about deploying CAPTCHAs. Combining multiple defenses—behavioral analysis, IP control, and verification layers—creates a comprehensive shield to maintain authentic communities and platforms. Solutions like CaptchaLa offer flexible, developer-friendly tools that integrate well with modern stacks and scale as your user base grows.
Where to go next? Explore CaptchaLa pricing to find the tier that fits your needs, or dive into the developer docs for detailed integration guidance. Your users—and your data—will thank you.