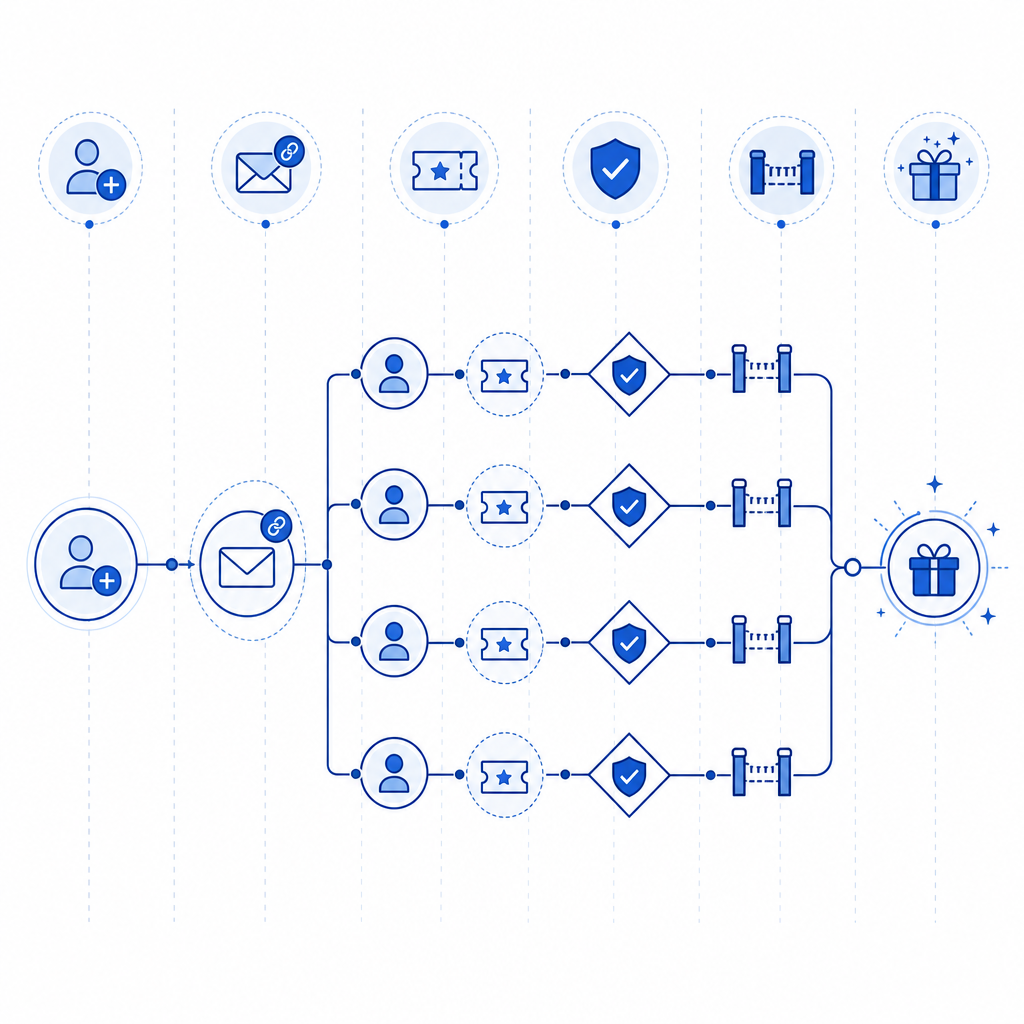
An anti invite bot flow is a set of checks that blocks automated invite abuse before it can drain referral credits, spam onboarding, or inflate signups with fake accounts. The practical goal is simple: verify that invite requests, invite acceptance, and downstream signup events are tied to a real user journey, not a script.
The mistake most teams make is treating invites like a single endpoint problem. They protect the “send invite” button and ignore everything around it: repeated email patterns, bursty traffic, token reuse, disposable domains, and oddly synchronized completion times. A stronger approach combines client-side friction, server-side validation, and rate controls so the system can distinguish normal sharing from automated abuse.

What an anti invite bot system needs to stop
Invite abuse usually shows up in one of a few ways:
- Mass invite creation from one account or IP range.
- Fake recipient signups using disposable or harvested email addresses.
- Credential or account farming where bots create accounts just to generate invite rewards.
- Replay attacks where the same invite token is submitted multiple times.
- Low-and-slow automation that tries to look human by spacing requests out.
The important part is that these are not all the same problem. A rate limit helps with burst traffic, but it does little against a distributed botnet. A CAPTCHA challenge can slow automated submissions, but by itself it does not prove whether an invite was later redeemed legitimately. That is why anti invite bot protection works best as a workflow, not a single widget.
A good defender’s question is: “What proof do I need at each step?”
- At invite creation: is this action coming from a normal browser/app session?
- At invite acceptance: is the recipient interaction fresh and expected?
- At signup completion: does the session, token, and IP context line up?
- After activation: should this invite be trusted enough to trigger rewards?
That framing makes it easier to build controls that are strict where abuse is common and lighter where real users need speed.
The detection layers that matter most
A durable anti invite bot stack usually combines four layers.
1) Client-side challenge at risky moments
Use a challenge when the user attempts something high-value, such as generating a batch of invites, redeeming a referral, or completing a signup that originated from an invite link. The challenge should be attached to the specific action, not the whole app session.
CaptchaLa supports native SDKs for Web (JS, Vue, React), iOS, Android, Flutter, and Electron, plus 8 UI languages. That matters because invite funnels often span multiple surfaces: a web marketing page, a mobile app, and a desktop client.
2) Server-side token validation
Never trust the client alone. Validate the pass token on your server before you issue invite credits or mark an invite as consumed. CaptchaLa’s validation flow is straightforward:
POST https://apiv1.captcha.la/v1/validate- body:
{pass_token, client_ip} - headers:
X-App-KeyandX-App-Secret
That separation keeps your secret off the client and lets your backend make the final decision.
3) Invite-specific rate and replay controls
The best anti invite bot setups add simple rules around the challenge:
- one invite batch per account per time window
- one redemption per invite token
- one reward payout after a confirmed downstream event
- extra friction when IP, device, and email domain signals look suspicious
You do not need to overcomplicate this. Many abuse patterns collapse under a few predictable constraints.
4) Risk-based escalation instead of blanket blocking
Not every suspicious action deserves a hard fail. Sometimes you want to:
- require a stronger challenge,
- delay reward issuance,
- queue the action for review,
- or temporarily cap invite volume.
That keeps legitimate growth from stalling while still making automation expensive.
A practical implementation pattern
Here is a simple server-side pattern for invite redemption or invite-triggered reward logic:
// English comments only
async function confirmInviteAction({ passToken, clientIp, inviteToken, userId }) {
// 1) Validate the captcha token with your backend secret
const validation = await fetch("https://apiv1.captcha.la/v1/validate", {
method: "POST",
headers: {
"Content-Type": "application/json",
"X-App-Key": process.env.CAPTCHALA_APP_KEY,
"X-App-Secret": process.env.CAPTCHALA_APP_SECRET,
},
body: JSON.stringify({ pass_token: passToken, client_ip: clientIp }),
});
const result = await validation.json();
// 2) Stop immediately if the token is invalid or expired
if (!result || result.success !== true) {
throw new Error("Invite action blocked");
}
// 3) Enforce one-time invite token use
const invite = await db.invites.findUnique({ where: { token: inviteToken } });
if (!invite || invite.redeemedAt) {
throw new Error("Invite token invalid");
}
// 4) Check the account that is receiving the invite
if (invite.redeemedByUserId && invite.redeemedByUserId !== userId) {
throw new Error("Invite already claimed");
}
// 5) Mark the invite as redeemed only after all checks pass
await db.invites.update({
where: { token: inviteToken },
data: { redeemedAt: new Date(), redeemedByUserId: userId },
});
return { ok: true };
}If your architecture issues a server token before a challenge, CaptchaLa also supports a server-token flow via POST https://apiv1.captcha.la/v1/server/challenge/issue. That can be useful when you want the backend to initiate a challenge as part of an elevated-risk decision.
The key lesson here is that the bot check is only one part of the state machine. The database rules are what stop replay and reward fraud.
Comparing common bot-defense options
Different tools solve different slices of the problem. Here is a neutral comparison for invite flows:
| Tool | Strengths | Tradeoffs | Good fit for invite abuse? |
|---|---|---|---|
| reCAPTCHA | Familiar, widely used, strong ecosystem | Can feel heavy in some flows; tuning varies by product | Yes, especially for generic abuse prevention |
| hCaptcha | Flexible challenge styles, commonly used for bot defense | User experience depends on configuration | Yes, especially where challenge-based friction is acceptable |
| Cloudflare Turnstile | Low-friction experience, easy to deploy on Cloudflare-adjacent stacks | Best when your stack already aligns with Cloudflare tooling | Yes, especially for lightweight verification |
| CaptchaLa | SDK coverage across web/mobile/desktop, validation API, first-party data only | Requires integrating your backend logic correctly | Yes, especially when invites span multiple platforms |
The right choice depends on your product shape. If your invite flow is web-only, a simpler integration may be enough. If you have web plus mobile plus desktop, consistency matters more, and SDK coverage becomes a real advantage. CaptchaLa’s docs at docs are helpful when you need to wire the same protection into multiple clients without inventing separate logic for each one.
Signals that improve decision quality
A few low-noise signals can make anti invite bot logic much stronger:
- Email domain quality: disposable or newly registered domains often correlate with abuse.
- IP clustering: many signups from the same subnet, ASN, or proxy pool can be suspicious.
- Timing patterns: ultra-fast completion after invite receipt can be normal, but repeated perfect timing is not.
- Token reuse: any repeated submission of the same invite token should be treated as fraud.
- Account age: brand-new accounts that generate many invites deserve additional scrutiny.
- Device continuity: if the invite is created on one device and redeemed on a totally different risk profile, consider escalation.
Do not make the mistake of using any single signal as a verdict. These are inputs for a policy, not a magic detector. Good anti invite bot systems score context across several signals and then choose the least disruptive response that still protects the business.
Deployment notes that save pain later
A few implementation details are easy to miss:
- Keep secrets only on the server.
- Validate challenge tokens as close to the protected action as possible.
- Log validation outcomes with a request ID for later review.
- Make invite tokens one-time use.
- Separate “invite sent” from “invite rewarded” so fraud cannot immediately cash out.
- Set thresholds carefully, then tighten them after you observe real traffic.
If you are rolling this out from scratch, start with one high-risk action, such as referral redemption, and measure false positives before expanding to the rest of the funnel. That approach keeps UX damage low and gives you cleaner data.
For teams wanting a straightforward integration path, CaptchaLa offers a free tier up to 1,000 validations per month, with Pro plans covering 50K-200K and Business at 1M. That makes it easy to pilot protection on a single invite flow before expanding. You can also review pricing when you are estimating volume, and use docs for the SDK and API details.
Where to go next: if you are ready to tighten your invite funnel, start with the docs and map the challenge to your highest-risk action, then check pricing for the tier that fits your traffic.