If you're searching for an "anti fingerprint browser reddit," you're likely seeking insights on browsers or tools discussed on Reddit that minimize browser fingerprinting to enhance privacy. Simply put, an anti-fingerprint browser is designed to prevent websites and trackers from uniquely identifying and profiling users based on device and browser attributes—something highly debated and dissected on Reddit’s privacy and security communities.
This post explores what makes a browser anti-fingerprinting, common Reddit perspectives, and the role of bot-defense services like CaptchaLa when countering fingerprint-based attacks, all with a focus on technical specifics and practical context.
What Is Browser Fingerprinting and Why Does It Matter?
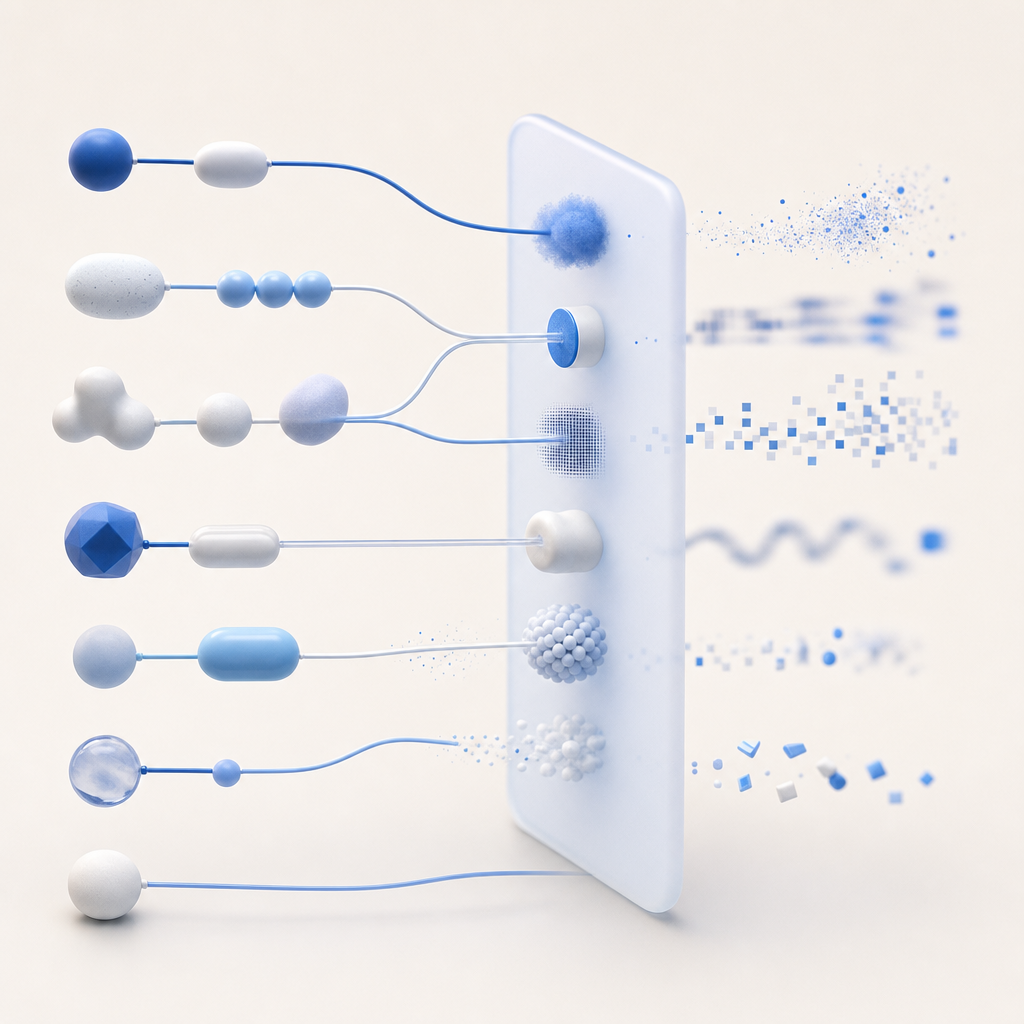
Browser fingerprinting is a technique used to collect an array of data points from your device/browser—like screen resolution, installed fonts, canvas rendering, user agent, and more—to create a nearly unique profile. Unlike cookies, fingerprints are harder to block or erase and are extensively discussed on Reddit threads concerned with online tracking and anonymity.
Common Fingerprinting Factors:
- User agent strings
- HTTP headers
- Canvas and WebGL rendering
- AudioContext data
- Fonts and plugins installed
- Timezone and language settings
On Reddit, users often debate whether certain browsers effectively reduce fingerprint uniqueness to defeat tracker profiles. Popular conversations revolve around browsers like Tor Browser, Brave, Firefox (with anti-fingerprinting patches), and tools like the Privacy Badger extension.
Reddit’s Take on Anti Fingerprint Browsers
What Browsers and Tools are Most Recommended?
On subreddits like r/privacy and r/privacytoolsio, several browsers are commonly recommended for anti-fingerprinting capabilities:
| Browser | Anti-Fingerprinting Approach | User Experience Notes |
|---|---|---|
| Tor Browser | Uniform fingerprint & network obfuscation | Slower speeds due to onion routing, strong privacy |
| Brave | Fingerprinting resistance via Chrome hardening | Fast browsing, integrates privacy-first features |
| Firefox + Mods | Built-in resist fingerprinting mode + addon support | Customizable, requires tweaking |
| Ungoogled Chromium | Stripped down Chromium with privacy tweaks | Familiar UI, less tracking |
These browsers often come with trade-offs such as speed, compatibility, or configurability that Reddit users discuss at length. For example, Tor creates a nearly uniform fingerprint by design, but Redditors note the performance impact. Others highlight Brave’s balance of usability and privacy, especially after its introduction of anti-fingerprinting flags.
Challenges Highlighted in Reddit Discussions
- Websites breaking functionality due to fingerprint blocking
- Difficulty sustaining anonymity without hampering user experience
- Fingerprinting morphing to use richer system calls and behavior analysis
- Complicated setups requiring browser mods and multiple extensions
How Bot-Defense Services Like CaptchaLa Address Fingerprint-Based Attacks
Bot-defense platforms such as CaptchaLa recognize that fingerprinting isn’t just a privacy issue but a key technique bot operators use to impersonate legitimate users or evade detection. Detecting suspicious or non-human browser characteristics is part of strengthening defenses.
CaptchaLa Features Relevant to Anti-Fingerprinting Defense
- Multi-language UI and native SDKs for JavaScript (React, Vue), iOS, Android, Flutter, Electron — allowing flexible client integration that can detect anomalies
- Server and client-side verification helping correlate suspicious token usage with fingerprint signals
- Use of first-party data rather than relying on third-party cookies or fingerprint databases — reducing privacy concerns but maintaining defense strength
Comparison With Other Bot-Defense Products
| Feature | CaptchaLa | reCAPTCHA | hCaptcha | Cloudflare Turnstile |
|---|---|---|---|---|
| Open SDKs (Mobile + Web) | Yes | Limited (mainly Web) | Yes | Limited |
| Support for Fingerprinting | Indirect via integrated risk scoring | Basic fingerprinting | More advanced fingerprinting | Minimal |
| Privacy Focus | First-party data based, 8 UI languages | Google tracking concerns | Privacy minded, GDPR compliant | Privacy-oriented |
| Pricing | Free tier + scalable paid plans | Free (with Google ecosystem) | Free with paid enterprise | Free for many customers |
While reCAPTCHA and hCaptcha integrate fingerprint signals, CaptchaLa emphasizes a balance between user privacy and robust bot detection through straightforward SDKs and first-party data usage.
Technical Insights: Implementing Anti-Fingerprint Features in Browsers
Here’s a simplified example illustrating how browsers or extensions might spoof or obfuscate fingerprint data to reduce uniqueness:
// Example: Overriding the canvas fingerprint method to obfuscate rendering
HTMLCanvasElement.prototype.toDataURL = (function(origFunc) {
return function() {
const ctx = this.getContext('2d');
ctx.fillStyle = 'red'; // Slight alteration to fingerprint canvas
ctx.fillRect(0, 0, 1, 1);
return origFunc.apply(this, arguments);
};
})(HTMLCanvasElement.prototype.toDataURL);Key technical strategies include:
- Standardization of reported values (e.g., user agent spoofing)
- Noise injection in canvas, audio, and timing measurements
- Blocking access to certain API features or zeroing out signals
- Randomizing attributes between sessions to prevent tracking
Even with these methods, Reddit conversations often stress the ongoing cat-and-mouse game between trackers and anti-fingerprinting efforts.

Final Thoughts: Where Anti Fingerprint Browsers and Bot Defense Intersect
Reddit’s discussions reveal there’s no perfect solution for eliminating browser fingerprints, but a combination of tools and approaches helps mitigate tracking and improve privacy. For websites and services worried about bot traffic leveraging client-side fingerprint signals, integrating bot-defense from providers like CaptchaLa complements browser-side anti-fingerprinting by validating user authenticity server-side.
Captchas solved with fingerprint data contribute to stronger bot detection with less frustrating user friction. For developers interested in exploring integration, CaptchaLa’s docs and pricing pages provide clear pathways to trial and scale.
If you’re curious about how browser privacy tools and bot defense mesh to protect online experiences, diving into Reddit’s rich discussions on anti fingerprint browser and experimenting with solutions like CaptchaLa will offer valuable insights.
To explore how CaptchaLa can add advanced bot protection while respecting user privacy, check our comprehensive documentation or view detailed pricing plans. Stay one step ahead in defending your web applications from bot attacks that leverage fingerprinting vulnerabilities.