A captcha extension adds an extra verification step to a website or app so you can tell legitimate users from automated traffic before spam, abuse, or credential attacks reach your backend. In practice, it’s a client-side component plus a server-side validation flow, and the best implementations try to keep the friction low for real users while still making automation expensive and unreliable.
That sounds simple, but the details matter. A good captcha extension is not just “a box users click.” It may run as a script, native SDK, or embedded widget, collect a limited set of signals, issue a short-lived pass token, and require your server to verify that token before allowing sensitive actions like signups, logins, coupon redemption, or form submission.
What a captcha extension actually does
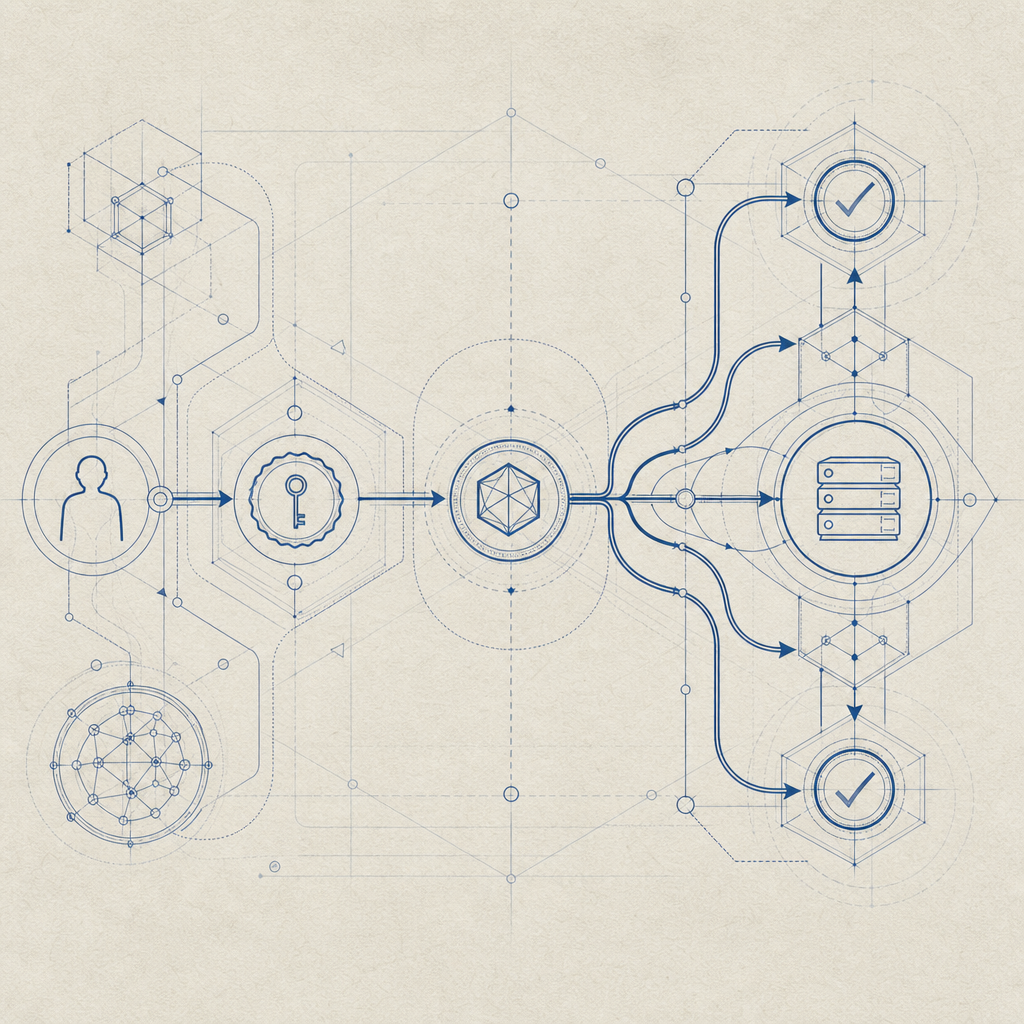
At a technical level, a captcha extension sits between the user action and your protected endpoint. The goal is to prove that the request came from a real interaction path, not a script blasting your form endpoint directly.
A typical flow looks like this:
- The page loads a client component or extension script.
- The user completes a challenge or risk check.
- The client receives a pass token.
- Your backend validates that token with the CAPTCHA provider.
- Only then do you accept the protected request.
The important part is that the client token is not the final source of truth. Your server should always validate it. For CaptchaLa, that validation happens via POST https://apiv1.captcha.la/v1/validate with a body containing pass_token and client_ip, authenticated using X-App-Key and X-App-Secret.
A minimal server-side example might look like this:
// Validate the token on your backend before allowing the action
async function verifyCaptcha(passToken, clientIp) {
const res = await fetch("https://apiv1.captcha.la/v1/validate", {
method: "POST",
headers: {
"Content-Type": "application/json",
"X-App-Key": process.env.CAPTCHALA_APP_KEY,
"X-App-Secret": process.env.CAPTCHALA_APP_SECRET,
},
body: JSON.stringify({
pass_token: passToken,
client_ip: clientIp,
}),
});
if (!res.ok) return false;
const data = await res.json();
return data?.success === true;
}When a captcha extension makes sense
Not every endpoint needs a challenge. If you place one everywhere, you usually create more frustration than security. A better approach is to protect the interactions that bots value most.
Common places to use a captcha extension include:
- account signup and email verification
- login attempts after repeated failures
- password reset forms
- contact forms and lead-gen forms
- checkout abuse prevention
- coupon, referral, and promo workflows
- public APIs that still accept browser-originated requests
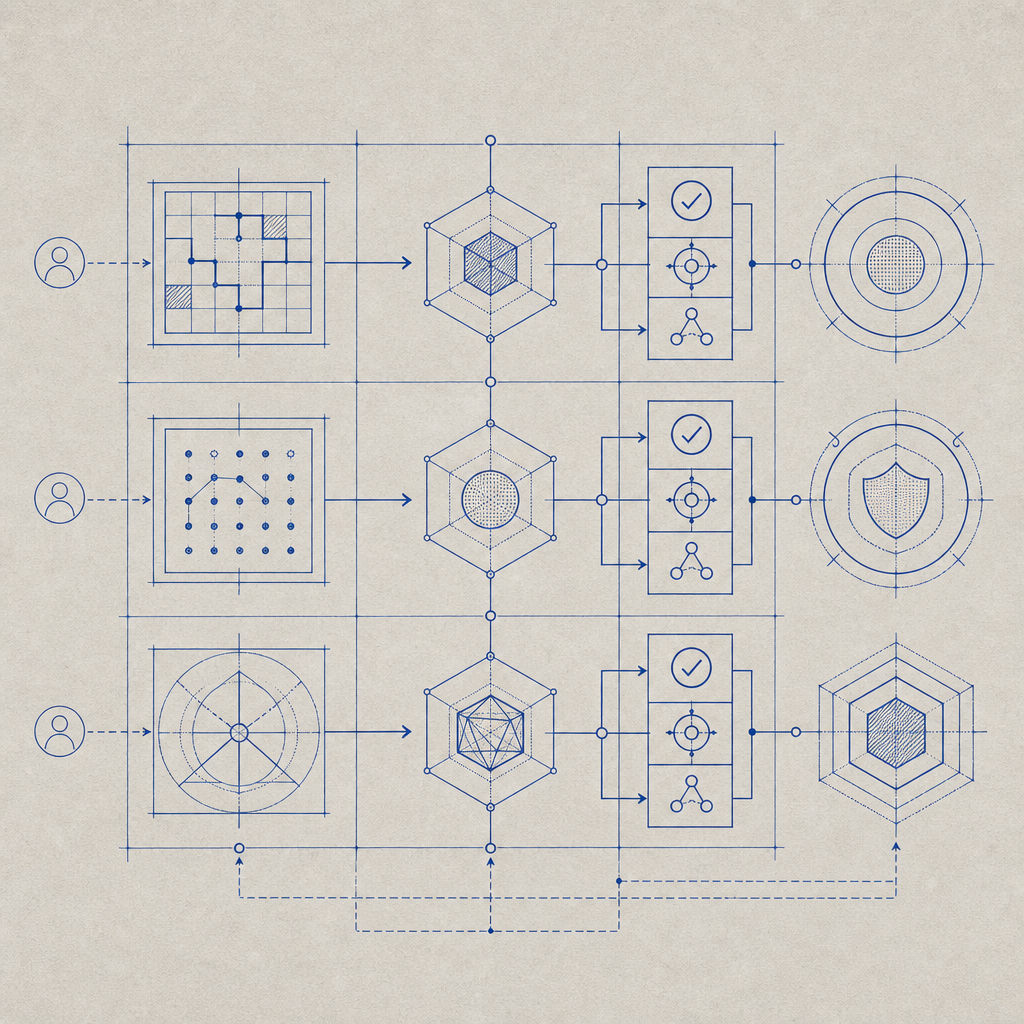
Use risk, not habit
The strongest pattern is to trigger the captcha extension when risk increases, not on every page load. For example:
- first attempt: allow silently
- repeated failures: add challenge
- suspicious IP or automation signature: require verification
- high-value action: always verify
This approach is especially useful if you run a consumer app where friction can hurt conversion. A lightweight challenge at the right moment beats a heavy challenge everywhere.
CaptchaLa supports this kind of deployment across web and app surfaces, with native SDKs for Web (JS, Vue, React), iOS, Android, Flutter, and Electron, plus 8 UI languages for global audiences. If you need server-side integrations, the available SDKs include captchala-php and captchala-go, which makes it easier to keep the client and backend in sync.
Choosing between reCAPTCHA, hCaptcha, Turnstile, and others
People often use “captcha extension” as a general term, but the implementation choices are not identical. The major options each lean differently on friction, privacy posture, and integration style.
| Provider | Typical strength | Tradeoff to consider | Good fit for |
|---|---|---|---|
| reCAPTCHA | widely recognized | can feel more intrusive in some flows | broad compatibility and familiar UX |
| hCaptcha | flexible challenge options | may require more tuning for UX | publishers and sites wanting an alternative model |
| Cloudflare Turnstile | low-friction verification | works best in certain Cloudflare-adjacent setups | teams prioritizing minimal user friction |
| CaptchaLa | token-based validation with SDK coverage | you still need server validation and sane risk rules | teams wanting first-party data control and app coverage |
A few practical takeaways:
- If your site needs the lowest possible visible friction, evaluate Turnstile-style flows carefully.
- If you need broad web and mobile SDK coverage, make sure the provider has native support across your stack.
- If you care about keeping the verification process tied to your own application data, choose a design that emphasizes first-party data only.
That last point matters more than many teams expect. A captcha extension should help you defend forms and login flows without creating data sprawl. CaptchaLa’s model is built around first-party data only, which is useful when your security team wants tighter control over what leaves the app boundary.
How to integrate a captcha extension cleanly
The biggest implementation mistake is treating the captcha extension as a frontend widget problem. It’s a full request-validation pattern. If the backend doesn’t enforce the check, the defense is mostly cosmetic.
A practical integration checklist
- Load the client script or SDK from the provider’s CDN or package manager.
- Render the challenge only when needed, not automatically everywhere.
- Capture the resulting pass token on the client.
- Send the token with the protected form or API request.
- Validate the token on the server before any state change.
- Log failures separately from business logic so you can tune thresholds.
- Expire or rotate challenge sessions according to the provider’s guidance.
For CaptchaLa web integrations, the loader is available at https://cdn.captcha-cdn.net/captchala-loader.js. Mobile and app teams can use the native packages instead of trying to force a browser-style flow into a native shell.
If you want to confirm the implementation details, the docs are the right place to check SDK setup, request formats, and language-specific examples. That is especially helpful when you’re wiring validation into a backend that already has rate limiting, device checks, or authentication rules.
Server-token and validation patterns
Some applications need a server-generated challenge flow rather than a purely client-first approach. CaptchaLa also exposes a server-token endpoint at POST https://apiv1.captcha.la/v1/server/challenge/issue, which can be useful when you want the backend to participate more directly in the challenge lifecycle.
That said, the principle stays the same: never trust the browser alone. A pass token is a proof artifact, not an authorization decision.
A clean mental model is:
- client proves interaction
- provider issues pass token
- server validates pass token
- application grants access
Operational details teams usually overlook
A captcha extension is easiest to maintain when you design for the day after launch, not just the first integration.
A few details worth planning for:
- Localization: if you have global traffic, language coverage affects completion rates.
- SDK consistency: use one integration pattern across web and mobile to reduce support load.
- Validation latency: keep the server call fast and fail closed for sensitive actions.
- Error handling: distinguish “captcha invalid” from “validation service unavailable.”
- Abuse analytics: compare challenge rates against blocked attempts to tune thresholds.
You should also think about how the captcha extension interacts with your other defenses. Rate limiting, IP reputation, email verification, device fingerprinting, and bot scoring are complementary, not redundant. CAPTCHA is strongest as one layer in a broader anti-abuse stack.
If you’re evaluating implementation cost, pricing can help you map expected volume to the right tier. CaptchaLa’s published tiers include a Free tier at 1,000 validations per month, Pro at 50K–200K, and Business at 1M, which is a useful way to estimate rollout across a staging environment, a single product surface, or a larger production funnel.
Conclusion: use the extension where friction earns its keep
A captcha extension is worth using when automation threatens a specific action and your backend needs a simple, reliable proof that a real user was involved. The best setups are not the most visible ones; they are the ones that quietly raise attacker cost while staying predictable for legitimate users.
If you’re mapping out where CAPTCHA fits into your stack, start with the forms and endpoints that absorb the most abuse, then add validation on the server side before you expand coverage. For implementation details and SDK examples, see the docs, or review CaptchaLa if you want to compare the web, mobile, and backend integration paths in one place.
Where to go next: check the pricing page for volume planning, or jump into the docs to wire up your first validation flow.