An anti bot verification extension is useful when you want an extra layer between your app and automated abuse, but the real question is not “does it block bots?” — it’s “does it fit your stack, preserve user experience, and verify humans without creating new friction?” For most teams, the answer depends on where the extension runs, how it validates requests, and whether it can be paired with server-side checks instead of relying on the browser alone.
That distinction matters because a browser extension can observe, challenge, or enrich traffic at the client edge, but it should not be your only line of defense. If you’re protecting signups, logins, checkout flows, or credential-sensitive endpoints, the extension should be one piece of a layered verification workflow, not a magic shield.

What an anti bot verification extension actually does
At its core, an anti bot verification extension helps you decide whether a session looks human enough to continue. Depending on implementation, it may:
- Inject a challenge widget or risk check into the page.
- Request a token after the user completes a challenge.
- Pass that token to your backend for verification.
- Apply a policy decision: allow, rate-limit, step-up challenge, or block.
That last step is the part many teams miss. Client-side checks can be spoofed if the server accepts them at face value. The safer pattern is to treat the extension as a token producer and your backend as the final authority.
Extension-based versus embedded verification
There’s a meaningful difference between a standalone extension and an embedded widget or SDK:
- Standalone browser extension: useful for internal tooling, client-side inspection, or add-on workflow control. Harder to standardize across devices and browsers.
- Embedded verification SDK: lives in your app, is easier to version, and usually integrates better with backend validation.
- Managed challenge service: the verification logic is controlled by a provider; you integrate their script/SDK and server API.
For public-facing products, embedded verification is usually the more predictable choice. If you are evaluating providers, make sure the experience works across multiple browsers and degrades gracefully if JavaScript is limited or blocked.
The selection criteria that matter most
When comparing tools, focus on the parts that affect both security and conversion.
1) Verification depth
A meaningful anti bot verification extension should support server-side validation. Look for a flow where the client obtains a pass token and your server verifies it with the provider. CaptchaLa, for example, exposes a validation endpoint:
POST https://apiv1.captcha.la/v1/validate- Body:
{ pass_token, client_ip } - Headers:
X-App-KeyandX-App-Secret
That model is preferable because your backend can make the final call before creating accounts, issuing sessions, or accepting form submissions.
2) Integration surface
The broader the platform coverage, the easier it is to fit into a real product. Useful signals include:
- Web SDK support for JS, Vue, and React
- Native SDKs for iOS, Android, Flutter, and Electron
- Server SDKs for PHP and Go
- Clear loader script documentation
- Stable token issuance and validation endpoints
For teams with mobile and desktop apps, SDK parity is more important than a flashy browser-only experience. CaptchaLa also documents multilingual UI support across 8 UI languages, which helps if your audience is global.
3) User friction
The best verification system is the one legitimate users barely notice. Compare:
- Invisible or near-invisible checks
- Risk-based step-up challenges
- Hard puzzles that interrupt conversion
- Accessibility options for keyboard and assistive tech users
A verification layer that adds too much friction can hurt signup and checkout completion more than bots hurt your metrics. This is where solutions like Cloudflare Turnstile, hCaptcha, and reCAPTCHA are often compared: each takes a slightly different approach to balancing UX and abuse resistance.
4) Data handling and compliance
If your team has strict privacy constraints, pay close attention to what data is collected and how it’s processed. Some vendors lean heavily on cross-site signals or third-party telemetry. Others emphasize first-party data. CaptchaLa, for instance, is positioned around first-party data only, which may simplify internal reviews for privacy-sensitive applications.
How the common options compare
Below is a practical, defender-focused comparison. This is not about declaring a universal winner; it’s about matching the tool to the application.
| Option | Typical strength | Typical tradeoff | Best fit |
|---|---|---|---|
| reCAPTCHA | Familiar integration, broad adoption | Can feel familiar to bots too; UX and privacy concerns vary by deployment | General web forms and legacy stacks |
| hCaptcha | Strong abuse controls, customizable challenge flows | Some teams find the challenge path more noticeable | Sites needing flexible challenge policy |
| Cloudflare Turnstile | Low-friction verification, simple embed | Best when you already align with Cloudflare’s ecosystem | Teams prioritizing smooth UX |
| Managed SDK + server validation | Flexible, application-specific policy | Requires thoughtful backend integration | Apps with custom abuse patterns |
If you’re choosing an anti bot verification extension for an app with serious account abuse or checkout fraud, the practical winner is often the one that makes backend validation easy and reliable. If the integration is awkward, teams tend to “temporarily” skip server checks, and that’s where defenses erode.
A secure implementation pattern for defenders
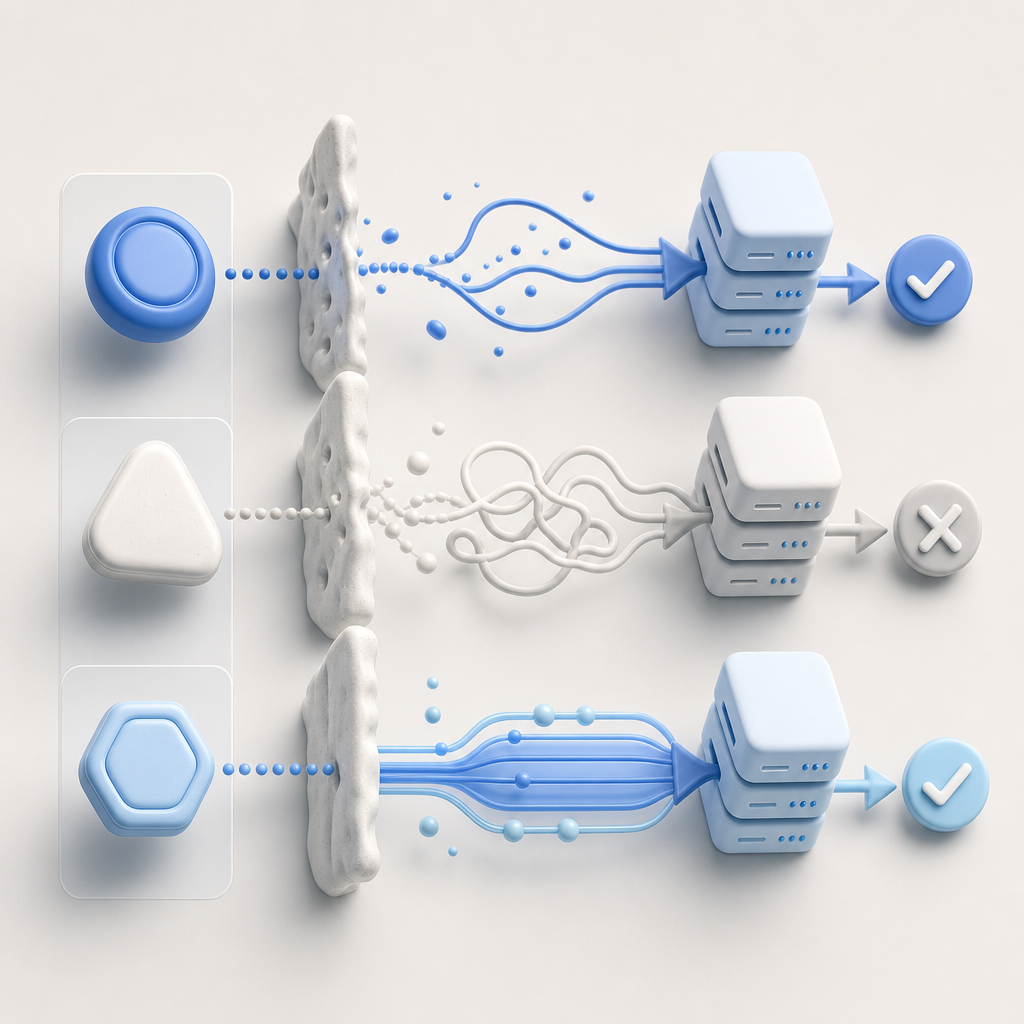
A robust pattern looks like this:
- Load the client script from the provider’s CDN.
- Issue or request a challenge token from the browser.
- Send the token to your backend alongside the user action.
- Verify the token server-side before continuing.
- Store the verification result only as long as needed for the current request or session step.
For CaptchaLa, the loader script is served from:
https://cdn.captcha-cdn.net/captchala-loader.js
And if you need to issue a server-side challenge token, the endpoint is:
POST https://apiv1.captcha.la/v1/server/challenge/issue
A simple server-side validation sketch might look like this:
// Example: verify a token before creating an account
async function verifyCaptcha(passToken, clientIp) {
const res = await fetch("https://apiv1.captcha.la/v1/validate", {
method: "POST",
headers: {
"Content-Type": "application/json",
"X-App-Key": process.env.CAPTCHALA_APP_KEY,
"X-App-Secret": process.env.CAPTCHALA_APP_SECRET
},
body: JSON.stringify({
pass_token: passToken,
client_ip: clientIp
})
});
// Only proceed if the provider confirms the token
const data = await res.json();
return data && data.valid === true;
}Two details matter here. First, include the client IP if your verification policy uses it. Second, keep secrets on the server only. The browser should never know your app secret.
For implementation specifics, the docs are the right place to check SDK setup, language-specific examples, and endpoint behavior. If you want to estimate usage tiers before rollout, the pricing page is the fastest reference.
When an extension is not enough
Even a well-designed anti bot verification extension can miss abuse if you rely on it alone. Defenders should also consider:
- Rate limiting on sensitive routes
- Device and session anomaly checks
- IP reputation and ASN-aware policies
- Email and phone verification for risky actions
- Behavioral thresholds for repeated failed attempts
This is especially important for credential stuffing, fake account creation, and coupon abuse. In those cases, the verification layer should feed a broader policy engine rather than act as the only barrier.
If you operate multiple surfaces — web, mobile, and desktop — choose tooling that stays consistent across them. CaptchaLa’s Web, iOS, Android, Flutter, and Electron SDK coverage is useful precisely because abuse rarely stays on one channel.
A practical choice for different team sizes
If you’re a small product team, the main question is whether you can ship quickly without overcomplicating the stack. A free tier with 1,000 monthly requests can be enough to validate the integration before committing to more traffic. For larger apps, tiers like Pro at 50K–200K and Business at 1M matter more because they let you plan around expected signups, forms, and transactional flows.
For defenders, the ideal setup is simple:
- Client challenge when needed
- Server verification every time
- Clear error handling for failed tokens
- Minimal user friction
- Privacy posture you can explain internally
That’s the core of a good anti bot verification extension strategy: not just stopping automation, but doing it in a way your product team, security team, and users can all live with.
Where to go next: review the integration details in the docs or compare plans on pricing to see what fits your traffic and risk profile.