Anti bot velocity is the rate at which automation can probe, adapt, and repeat across your site or app. The practical answer is: if you only block by volume, you miss the real threat, because modern bots often stay under obvious thresholds while moving fast enough to test logins, signups, checkout flows, and password resets at scale.
That makes velocity a behavior problem, not just a traffic problem. A defender needs to look at how quickly requests arrive, how consistently they repeat, how many distinct endpoints they touch, how often they change IPs or fingerprints, and whether the same action pattern appears across many accounts. Rate limiting helps, but by itself it rarely captures the full picture.
What anti bot velocity actually measures
At a high level, anti bot velocity is about detecting suspicious acceleration in automated behavior. The key idea is not “too many requests” but “too much coordinated movement over time.”
A few examples:
- A single IP posts 20 login attempts in a minute.
- A distributed botnet makes 2 requests per minute from 500 IPs against the same endpoint.
- One account creation flow is repeated with tiny variations every few seconds.
- A credential-stuffing campaign rotates proxies, but the sequence and timing remain nearly identical.
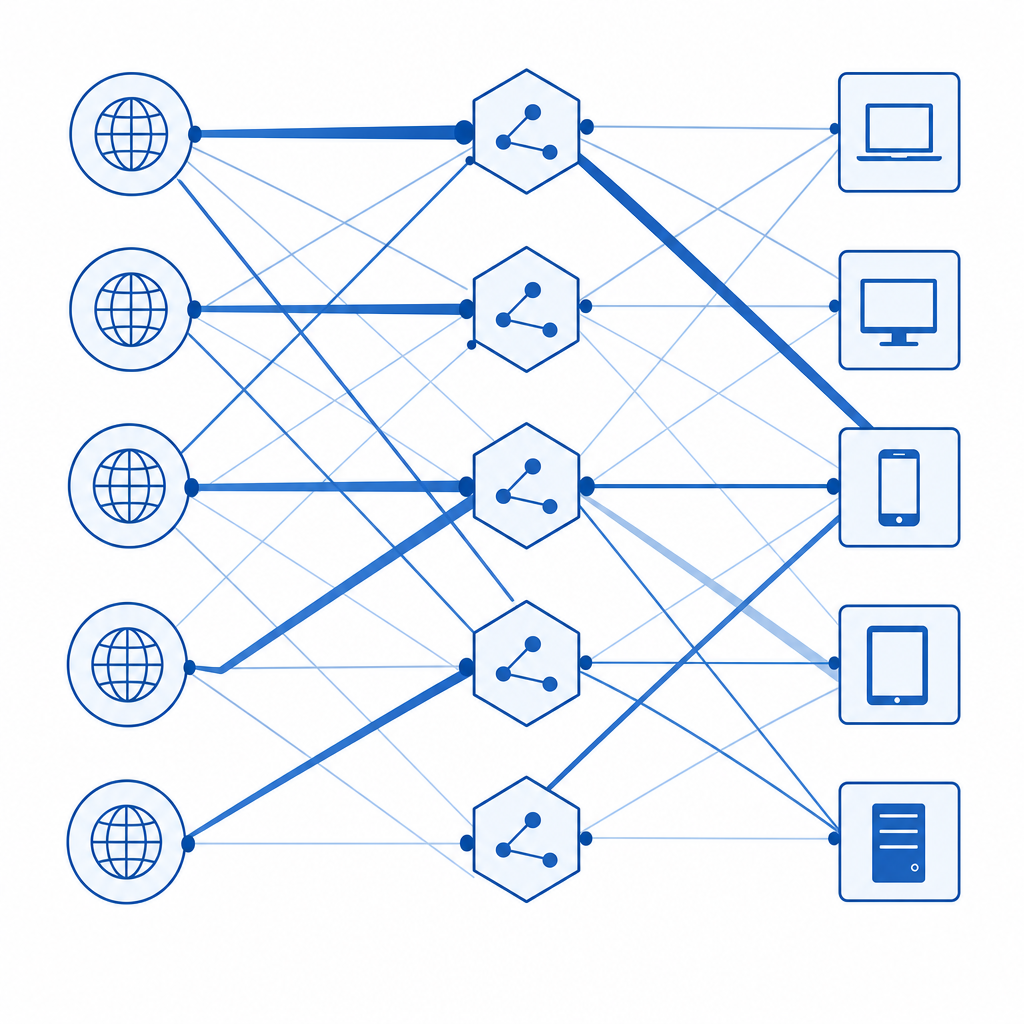
These patterns can evade naive thresholds because each individual source looks quiet. The defender’s job is to combine signals from request timing, session continuity, device consistency, and action semantics.
Why simple rate limits are not enough
Traditional rate limits answer questions like “How many requests per minute?” or “How many signups per IP?” Those are still useful, but they assume the attacker is constrained by one identity or one network path.
Velocity-aware defense adds more context:
- endpoint-specific timing, such as rapid retries on login versus normal browsing cadence
- per-session action bursts, even when IPs change
- cross-account similarity, where many accounts show the same form-fill pace
- impossible travel or rotation patterns, where a client changes location or fingerprint too quickly
- challenge escalation, where suspicious traffic is forced into stronger verification before it can continue
If you’re building fraud controls, think of velocity as a timeline feature. The question is not only “what did the client do?” but “how fast, how repeatedly, and with what consistency?”
Signals that help detect fast automation
A good anti bot velocity system combines several signals, because no single one is reliable on its own.
| Signal | What it tells you | Typical defender use |
|---|---|---|
| Request timing | How quickly actions repeat | Detect bursts, retries, scripted pacing |
| IP diversity | Whether traffic is spread out | Spot distributed campaigns |
| Session continuity | Whether the same browser session persists | Catch resets and replay attempts |
| Endpoint sequence | Which pages/actions are touched, and in what order | Identify scripted flows |
| Form completion behavior | How inputs are filled and submitted | Detect uniform automation |
| Challenge outcomes | Whether a client can pass friction consistently | Escalate based on confidence |
The strongest systems look for combinations, such as “fast retries + repeated endpoint order + token reuse.” That combination is much more informative than any one metric by itself.
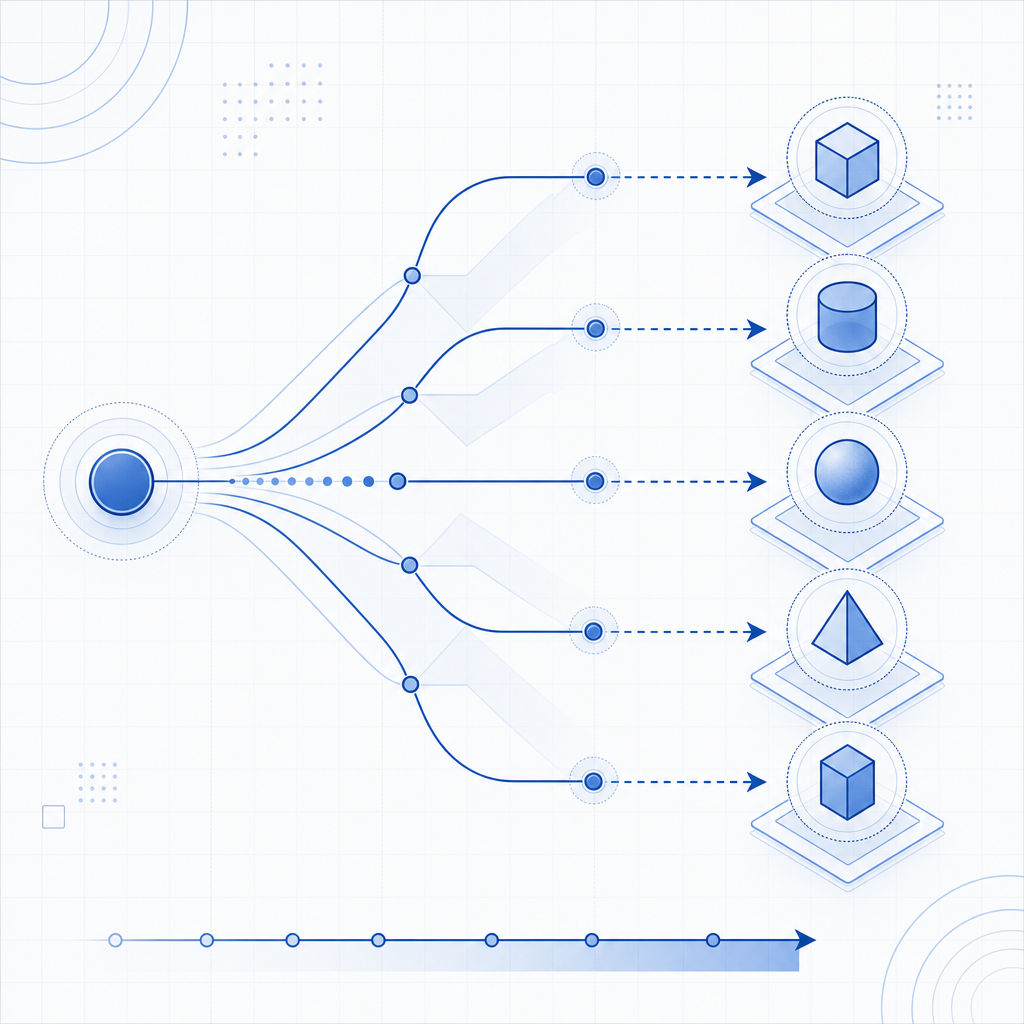
Velocity as a graph problem
One useful mental model is to treat activity as a graph:
- nodes = IPs, sessions, accounts, devices, endpoints
- edges = requests, retries, validations, failures, challenge passes
- weights = timing, frequency, and confidence
When several weak signals point in the same direction, you get a strong velocity alert. For example, 100 accounts created from 100 IPs may seem unrelated until you notice they all submit forms in the same rhythm and hit the same sequence of endpoints.
That is why modern bot defense tends to move from static thresholds to adaptive scoring. Instead of asking whether one metric crosses a line, you score the whole behavior chain.
Building defenses that slow bots without hurting users
The goal is not to punish speed itself. Legitimate users can be fast, especially on repeat actions. The real goal is to separate normal high-intent behavior from synthetic automation.
A practical anti bot velocity stack usually includes:
Entry filtering
Block obviously malicious traffic at the edge using IP reputation, protocol anomalies, or invalid headers.Behavioral scoring
Track timing, retries, and sequence consistency across sessions and accounts.Progressive friction
Apply stronger verification only when risk rises, rather than challenging everyone equally.Token validation
Require a proof of interaction and validate it server-side before accepting sensitive actions.Feedback loops
Use confirmed abuse to tune thresholds, endpoint rules, and escalation logic.
This approach works because it preserves low-friction paths for good users while making automation expensive and less reliable.
Where CAPTCHA fits
CAPTCHA is most effective when it is one layer in a broader velocity strategy, not the whole strategy. A challenge can interrupt a bot’s pace, but the real value comes from tying the challenge result to server-side risk decisions.
For teams that want multiple deployment options, CaptchaLa supports web SDKs for JS, Vue, and React, plus native SDKs for iOS, Android, Flutter, and Electron. It also provides server SDKs in captchala-php and captchala-go, with validation via POST https://apiv1.captcha.la/v1/validate using pass_token and client_ip plus X-App-Key and X-App-Secret. If you need a server-issued challenge token, there is also POST https://apiv1.captcha.la/v1/server/challenge/issue.
That matters for velocity defense because you can make challenge decisions closer to the action, then verify them centrally before allowing the request through. CaptchaLa also exposes a loader at https://cdn.captcha-cdn.net/captchala-loader.js, supports 8 UI languages, and uses first-party data only, which is useful when you are trying to minimize unnecessary data exposure in your risk pipeline.
Comparing common CAPTCHA and bot-defense approaches
Different tools emphasize different parts of the stack. Here is a practical, defender-focused comparison:
| Tool | Strengths | Tradeoffs |
|---|---|---|
| reCAPTCHA | Familiar, widely supported | Can be more opaque for custom risk tuning |
| hCaptcha | Flexible challenge model, common in anti-abuse setups | May still need external velocity logic around it |
| Cloudflare Turnstile | Low-friction user experience, easy edge integration | Best when paired with broader application-layer controls |
| CaptchaLa | SDK coverage across web/mobile/desktop, server validation, first-party data only | You still need to design risk scoring and escalation well |
The main takeaway is that no CAPTCHA product replaces anti bot velocity analysis. They complement it. Your backend still needs to decide when a pass token is enough, when to ask for a stronger challenge, and when to deny the flow entirely.
If you are wiring this into a production service, keep the validation path simple and explicit. Check the token server-side, bind it to the current client IP when appropriate, and use the result as one input to your risk engine. CaptchaLa’s docs and pricing are good starting points if you want to map that into an implementation plan.
Implementation tips for teams shipping now
A few technical details can make your velocity controls much more reliable:
Measure per action, not just per IP
Login, signup, password reset, checkout, and review submission all deserve separate baselines.Use sliding windows
A fixed one-minute counter can miss bursts that straddle boundaries. Sliding windows capture smoother velocity patterns.Track challenge success over time
A client that passes one challenge is not automatically safe forever. Repeated passes in a suspicious sequence can still indicate automation.Normalize by endpoint sensitivity
A fast page view is not the same as a fast password reset request.Keep verification server-side
Never trust a client-side “passed” state without validation.
Here is a simple example of velocity-aware scoring logic:
# English comments only
score = 0
# Rapid retries are suspicious
if login_failures_last_5m > 5:
score += 30
# Distributed activity with the same action path is suspicious
if distinct_ips_last_10m > 50 and same_endpoint_sequence_ratio > 0.8:
score += 25
# Frequent challenge resets can indicate automation
if challenge_attempts_last_15m > 3:
score += 20
# Very short inter-request intervals raise risk
if median_inter_request_ms < 700:
score += 15
# Escalate when the combined score crosses threshold
if score >= 50:
require_stronger_verification()This is intentionally simple, but the structure is the important part: combine timing, distribution, sequence, and challenge history instead of depending on a single counter.
Where to go next
Anti bot velocity is ultimately about seeing automation as a sequence, not a spike. Once you track timing and behavior together, you can slow attackers down without turning every legitimate user into a suspect.
If you want to explore implementation details, start with the docs or review the pricing tiers to match your traffic profile.