An anti bot url shortener is a redirect service that checks traffic quality before it hands off the destination. Instead of letting every request hit the target link blindly, it filters suspicious automation, rate-limits abuse, and verifies real users only when the request pattern looks risky. That matters because short links are easy to share, but they are also easy to scan, scrape, brute-force, and weaponize.
If you run a shortener, you are not just managing redirects; you are managing abuse economics. Bots can burn link budgets, distort analytics, trigger partner blocks, and flood destination pages with junk traffic. A good defense keeps the happy path fast and only adds friction when it detects risk.

Why short links attract bots
Short links are attractive to automation for a few boring reasons: they are compact, predictable, and often reused across campaigns. That makes them easy to enumerate and test at scale. Bots may not even care about the final destination; they may only be probing for active links, affiliate patterns, expired promos, or redirect chains that expose metadata.
Common abuse patterns include:
- Enumeration: scanning sequential or guessable codes to discover valid links.
- Click fraud: inflating redirect counts on ad, affiliate, or attribution links.
- Preview abuse: hammering link preview endpoints and metadata fetchers.
- Destination stress: using the shortener as a distributed proxy into a third-party app.
- Analytics contamination: making traffic reports less trustworthy for campaign decisions.
A shortener that does nothing but 302 every request will eventually become a convenience layer for attackers. The goal is not to block all automation; it is to separate legitimate human traffic from obvious non-human traffic with minimal friction.
What an anti bot url shortener should check
The best place to defend is before the redirect completes. You want signal from the request path, headers, IP reputation, velocity, and whether the client can complete a verification challenge when needed.
A practical evaluation stack looks like this:
Edge request checks
- Request rate per IP, subnet, and token
- User agent consistency
- Referrer anomalies
- Headless/browser automation fingerprints
- Repeated misses on invalid or random link IDs
Decisioning
- Allow for low-risk requests
- Challenge for medium-risk requests
- Block or tarp for high-risk abuse
Verification
- Use a pass token that is validated server-side
- Bind validation to the originating IP when appropriate
- Keep the decision short-lived to prevent replay
Redirect
- Issue the final redirect only after verification succeeds
That approach keeps the shortener focused on first-party traffic quality. It is especially useful if your business depends on accurate campaign attribution, partner compliance, or paid-click integrity.
Example redirect flow
Client requests short URL
-> Edge scores request risk
-> Low risk: redirect immediately
-> Medium risk: show verification
-> Client receives pass token
-> Server validates token
-> If valid: redirect to destination
-> If invalid: deny or retry
-> High risk: block or rate-limit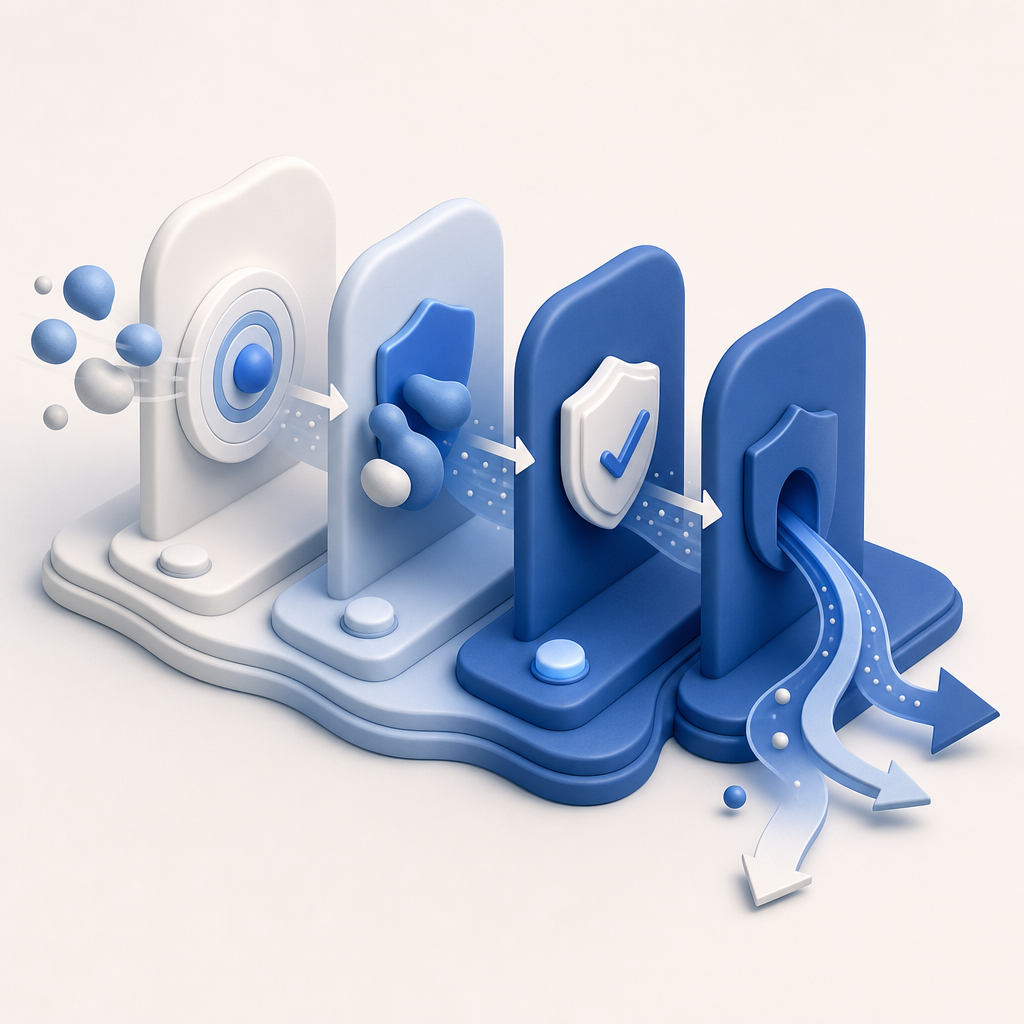
Implementation patterns that work
You do not need to turn every short link into a full security ceremony. The trick is to place verification only where it matters and keep the latency cost low.
1) Use server-side validation, not just client-side checks
Client-side checks are useful for UX, but they are not enough for abuse prevention. A stronger model issues a token on the client side and validates it on your server before redirecting. With CaptchaLa, that validation happens through a simple endpoint:
POST https://apiv1.captcha.la/v1/validateThe request body includes:
{
"pass_token": "token-from-client",
"client_ip": "203.0.113.10"
}And the call uses your X-App-Key and X-App-Secret. That server-side step is what makes the verification decision meaningful for a redirect service.
2) Keep the challenge short-lived
Shortener traffic is latency-sensitive. If the challenge takes too long, users feel it immediately. Make the pass token ephemeral and bind it to the current request context. For high-risk paths, you can require a fresh token for each redirect; for lower-risk flows, you can allow a brief reuse window.
3) Preserve first-party data
For link analytics, privacy and data ownership matter. Keep your decisioning based on first-party data only, so you are not dependent on opaque third-party profiles. That also simplifies compliance and helps you reason about what signal you actually control.
4) Instrument the redirect decision
You should log:
- short-link ID
- risk score or decision outcome
- validation success/failure
- client IP or proxy chain where allowed
- final redirect status
- challenge latency
That data makes it easier to tune thresholds without accidentally blocking real users.
Comparing common CAPTCHA options for shorteners
A shortener’s verification layer is not the same as a login wall or checkout form. You want low friction, reliable validation, and broad platform support.
| Option | Strengths | Trade-offs | Good fit for shorteners |
|---|---|---|---|
| reCAPTCHA | Familiar, widely deployed | Can feel heavier in some flows; product fit varies by use case | Works, but may add more friction than necessary |
| hCaptcha | Strong abuse controls, flexible deployment | Can introduce its own UX and integration choices | Good when you want configurable challenges |
| Cloudflare Turnstile | Lightweight user experience | Typically tied to Cloudflare-centric deployments | Useful if your stack already leans that way |
| CaptchaLa | Native SDKs, validation API, multiple platforms, first-party data only | Requires your own integration and decisioning | Well-suited for redirect gating and custom flows |
For a shortener, the main question is not “which CAPTCHA is most recognizable?” It is “which one lets me verify risk quickly without turning a redirect into a support ticket?” That’s where integration simplicity and server-side validation matter.
CaptchaLa supports 8 UI languages and native SDKs for Web (JS, Vue, React), iOS, Android, Flutter, and Electron, plus server SDKs for PHP and Go. If your shortener has web and mobile redirect surfaces, that coverage can simplify implementation. The docs are also straightforward if you want to wire it into a redirect service without building a custom challenge stack from scratch: docs.
A practical deployment model
A clean implementation usually has three pieces:
Challenge issuance
- Your app requests a server token when a request is risky.
- CaptchaLa exposes a server-token issuance endpoint:
POST https://apiv1.captcha.la/v1/server/challenge/issue
Client verification
- The client completes the challenge and gets a pass token.
Redirect decision
- Your backend calls the validation endpoint.
- If the token is valid, it emits the redirect.
Here is a simplified example in pseudocode:
<?php
// English comments only
// 1. Inspect request risk
$risk = evaluate_request($_SERVER);
// 2. Only challenge suspicious requests
if ($risk >= 70) {
// 3. Issue a challenge flow on the server
$challenge = issue_challenge($_SERVER['REMOTE_ADDR']);
// 4. Render challenge page and wait for pass token
$passToken = $_POST['pass_token'] ?? null;
// 5. Validate token server-side before redirect
$valid = validate_token($passToken, $_SERVER['REMOTE_ADDR']);
if (!$valid) {
http_response_code(403);
exit('Verification failed');
}
}
// 6. Redirect to destination
header('Location: ' . $destination, true, 302);
exit;
?>If you already run PHP or Go services, the server SDKs can fit neatly into this flow. If you are building a mobile-first shortener or a shared link product, the native app SDKs are useful for keeping the verification experience consistent across platforms.
When to challenge, and when to let traffic pass
A shortener should not challenge every visitor. That would create unnecessary friction and likely reduce legitimate engagement. Instead, use a tiered policy:
- Allow requests that look normal and are within expected velocity.
- Challenge requests with suspicious patterns, such as rapid bursts or odd browser fingerprints.
- Block requests that are clearly abusive, such as repeated invalid-link enumeration or impossible traffic patterns.
The thresholds should be tuned with live data, not guesswork. A small consumer shortener might only need verification for a tiny fraction of traffic. A marketing or affiliate platform may need stricter controls around campaign launches, where abuse tends to spike.
CaptchaLa has a free tier for 1,000 validations per month, with Pro bands around 50K-200K and Business around 1M, so it can fit a gradual rollout instead of forcing a big-bang migration. You can check pricing if you are estimating verification volume for redirects, campaign links, or partner traffic.
Closing the loop
An anti bot url shortener is really a traffic-quality system with a redirect at the end. The stronger the pre-redirect checks, the less abuse reaches your analytics and destination pages. The best setup stays invisible for real users, escalates only when risk is present, and validates tokens server-side so automation cannot replay a fake pass.
Where to go next: if you are planning the implementation, start with the docs and compare usage against pricing for your expected link volume.