If you need anti bot telegram protection, the core idea is simple: verify that the person or automation behind a Telegram-linked action is genuine before you let the action succeed. That usually means adding a challenge at the moment of risk, then validating the result server-side so scripts, headless clients, and replayed requests do not get through.
Telegram itself is not the problem; it is often the gateway. Teams use Telegram for login links, account recovery, support intake, referral campaigns, lead capture, and community actions. Those are exactly the flows attackers automate because they are fast, low-friction, and often high-value. A good defense does not try to “ban bots” globally. It places friction only where abuse starts to outweigh convenience.
Where Telegram flows get abused
Telegram-related abuse usually shows up in a few repeatable patterns:
Mass signup or referral spam
Attackers create many accounts or trigger many invite actions using scripts, disposable identities, and repeated device fingerprints.OTP or verification abuse
If Telegram is part of a verification step, attackers may try to flood the flow, resubmit tokens, or automate retries until something sticks.Support and contact spam
Bots submit forms, open support threads, or DM a branded Telegram account with low-quality or malicious content.Token replay and session abuse
When a front-end “proof” is accepted without strong server-side checks, an attacker can replay a captured token or reuse a response in a different context.
The mistake many teams make is assuming that a CAPTCHA on the page is enough. It is not. The protection has to be tied to your backend decision, not just your UI.
What a strong anti bot telegram flow looks like
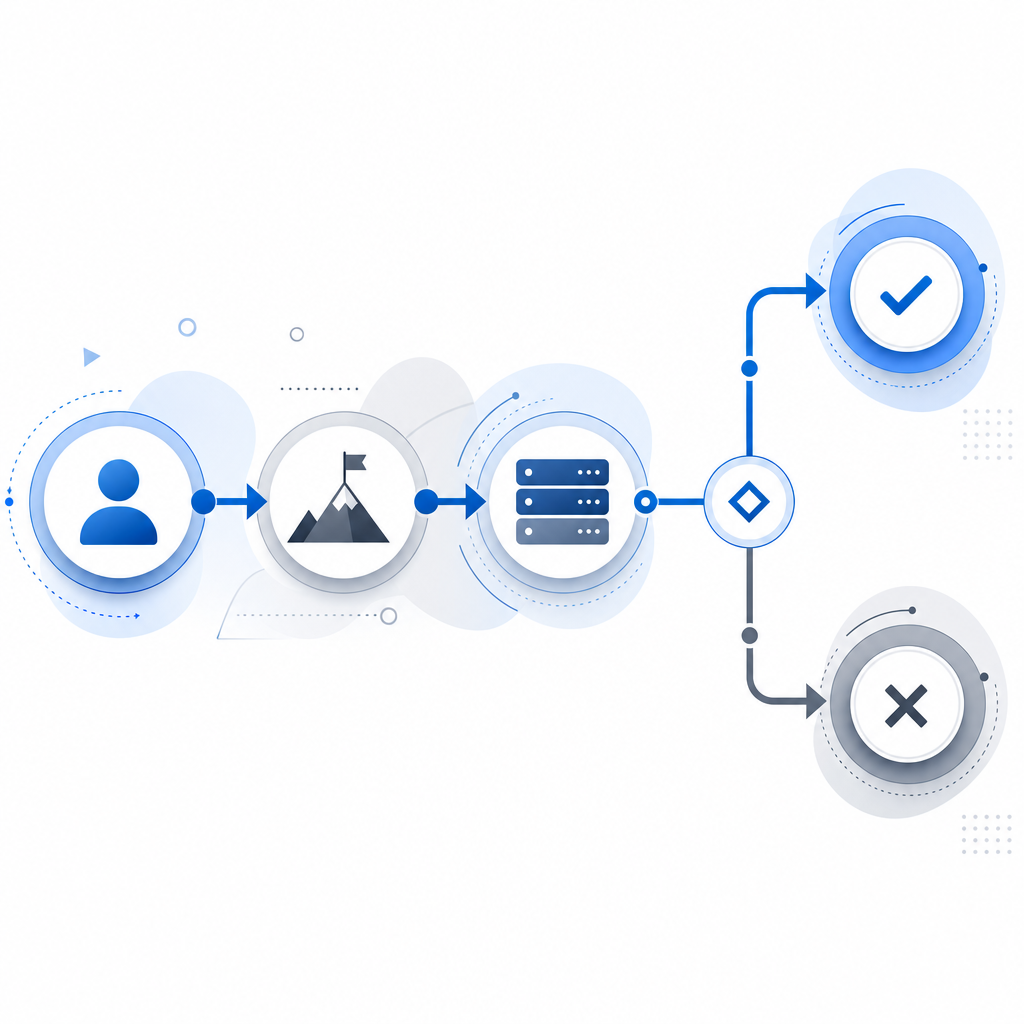
The most reliable pattern is: challenge first, validate second, act third.
Here is the defender-side sequence:
- The user reaches a Telegram-connected action, such as “Continue with Telegram,” “Join,” “Request link,” or “Send support message.”
- Your frontend loads a challenge widget or token provider.
- The challenge completes and returns a pass token.
- Your server sends that token to a validation endpoint along with the client IP.
- Only after validation succeeds do you create the Telegram-linked session, send the invite, or accept the message.
That server step matters because it lets you enforce context. You can bind the token to the request path, the action type, the time window, and the originating IP. If the token does not match the live request, you reject it.
A compact example:
// English comments only
async function verifyTelegramAction(passToken, clientIp) {
const res = await fetch('https://apiv1.captcha.la/v1/validate', {
method: 'POST',
headers: {
'Content-Type': 'application/json',
'X-App-Key': process.env.CAPTCHALA_APP_KEY,
'X-App-Secret': process.env.CAPTCHALA_APP_SECRET
},
body: JSON.stringify({
pass_token: passToken,
client_ip: clientIp
})
});
if (!res.ok) return false;
const data = await res.json();
return data?.success === true;
}For challenge issuance, the server can also request a token via POST https://apiv1.captcha.la/v1/server/challenge/issue when you want the backend to control when a challenge appears. In practice, that helps on high-risk Telegram endpoints where you want tighter gating.
CaptchaLa supports this kind of flow with native SDKs for Web, iOS, Android, Flutter, and Electron, plus server SDKs for PHP and Go. It also offers 8 UI languages, which is useful when your Telegram audience spans regions and devices. If you want to inspect implementation details, the docs are the place to start.

Comparing common bot-defense options for Telegram-linked flows
Different tools solve different problems. For Telegram-adjacent protection, the useful question is not “which CAPTCHA is famous?” but “which approach gives me reliable server-side verification without breaking conversion?”
| Option | Strengths | Tradeoffs | Good fit for Telegram flows |
|---|---|---|---|
| reCAPTCHA | Widely recognized, familiar to many teams | Can be intrusive depending on score and UI; Google dependency | Basic signup gating and legacy stacks |
| hCaptcha | Strong bot-defense focus, flexible integration | May require tuning for user experience | High-abuse forms and account creation |
| Cloudflare Turnstile | Low-friction, often smooth for users | Best when you already use Cloudflare infrastructure | Lightweight web flows and edge-managed sites |
| CaptchaLa | Server-validated flows, SDK coverage across web/mobile/desktop, first-party data only | Requires normal integration work like any auth control | Telegram login, invite, support, and verification flows |
A few practical observations:
- If your Telegram workflow is just a web form, a lightweight challenge may be enough.
- If it includes app login, mobile handoff, or desktop clients, native SDK coverage matters more.
- If you need regional language support for a broad audience, the 8 UI languages can reduce drop-off.
- If you care about keeping verification data first-party, that should influence your vendor choice as much as raw friction.
For teams that want to keep the moving pieces simple, CaptchaLa can sit between the Telegram-facing action and the backend decision. You can also check pricing to see where a given traffic level fits.
Implementation details that reduce false positives
Telegram-linked flows are especially sensitive to false positives because users often arrive from a chat, a QR scan, or a mobile deep link. That context is fragile. You want controls that are strict enough to stop scripts but forgiving enough for real users.
A few technical practices help:
Validate on the server, not in the browser alone
The browser token is only a claim. Your server should confirm it before granting access.Bind verification to the current request
Use the client IP where available, and make sure the token is consumed for one action only.Time-box every challenge
Short validity windows reduce replay risk and keep “stale token” abuse down.Apply step-up friction only on risky actions
Do not challenge every message or click. Reserve the challenge for signup, invite, recovery, and rate-sensitive actions.Log validation outcomes
Store the result, timestamp, route, and request metadata so you can detect abuse patterns and tune thresholds later.Treat Telegram as one identity signal, not the whole identity
A Telegram-linked account may still need email, phone, or device checks depending on your risk profile.
If you are building in PHP or Go, the server-side piece can stay straightforward with the dedicated SDKs. If you are shipping mobile or cross-platform clients, the native SDK options make it easier to keep the user experience consistent across surfaces.
A practical architecture for Telegram protection
A clean anti-bot setup for Telegram-linked actions usually has three layers:
- Client layer: show a challenge only when the flow enters a sensitive step.
- API layer: require a pass token and the client IP before performing the Telegram action.
- Policy layer: decide when to challenge based on risk, rate limits, and action type.
That arrangement helps with several real-world cases:
- Login with Telegram: challenge only when login velocity spikes or the device looks suspicious.
- Telegram invite links: validate before generating the invite or joining the user to a restricted group.
- Support intake via Telegram: require verification before sending the message into a human queue.
- Campaign landing pages that redirect to Telegram: challenge before handing out a link or referral reward.
The main goal is to ensure the verification result is consumed immediately and cannot be reused elsewhere. If you design around that principle, you reduce the value of automation without making the path miserable for legitimate users.
Conclusion
Anti bot telegram protection works best when it is contextual, server-validated, and limited to the actions that matter most. You do not need to challenge every person; you need to stop automation at the point where it becomes expensive to your business.
If you want to see how this fits into a real stack, start with the docs or review pricing to match the right tier to your traffic.