A captcha buster is a tool or service designed to defeat CAPTCHA challenges, usually by automating human-like solving, relaying challenges to other parties, or abusing weak validation flows. If you’re defending a site, the practical response is not to make the puzzle harder; it’s to tighten validation, add server-side verification, and layer in bot signals so the challenge becomes only one part of the decision.
That matters because a CAPTCHA by itself is not a security boundary. It is one signal in a broader anti-abuse system. When a captcha buster is used against your forms, logins, checkout pages, or signup flows, the goal is usually simple: reduce friction for automated abuse while still appearing “human enough” to get through. The countermeasure is equally simple to state, if not always to implement: validate on the server, bind tokens to a session or action, and make replay expensive.
What a captcha buster actually targets
A captcha buster usually aims at one of four weak points:
Client-only checks
If a site trusts a JavaScript flag or hidden field without server validation, automation can submit directly.Predictable challenge lifetimes
Tokens that last too long can be replayed. Short, single-use validation narrows that window.Weak binding between challenge and action
If a token issued for a signup form can be reused on password reset or checkout, abuse becomes easier.Static or overexposed integration points
Public endpoints, leaked keys, or loose CORS rules can create shortcuts around the intended flow.
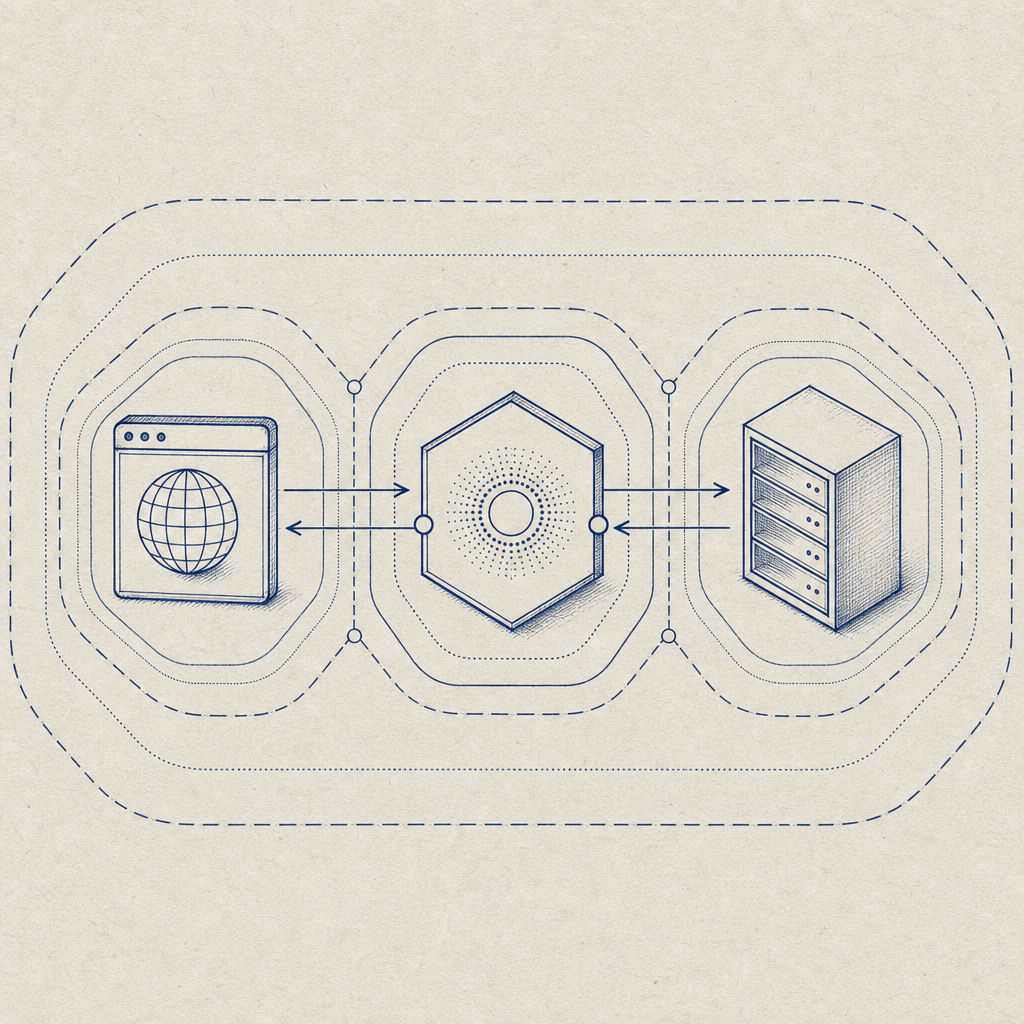
The practical takeaway is that “captcha buster” is less a single technique than a category of bypass attempts. Defenders should think in terms of trust boundaries: browser, challenge service, and server. If those layers don’t agree, the weakest one gets exploited.
Why modern bypass attempts work
Most successful bypasses don’t “solve” the challenge in a magical way. They exploit implementation mistakes.
Common failure patterns
- Token accepted without verification
- The app records a token from the client and never calls the validation endpoint.
- Verification done, but not checked carefully
- The response is logged but not enforced.
- Missing IP or session context
- A token issued on one connection is replayed elsewhere.
- No expiration discipline
- Old tokens remain usable after the user has moved on.
- Unprotected server-to-server issuance
- Challenge issuance endpoints are exposed without proper authentication.
A good defender mindset is to ask: “If an attacker can copy the browser request, what still stops them?” If the answer is nothing, the integration needs work.
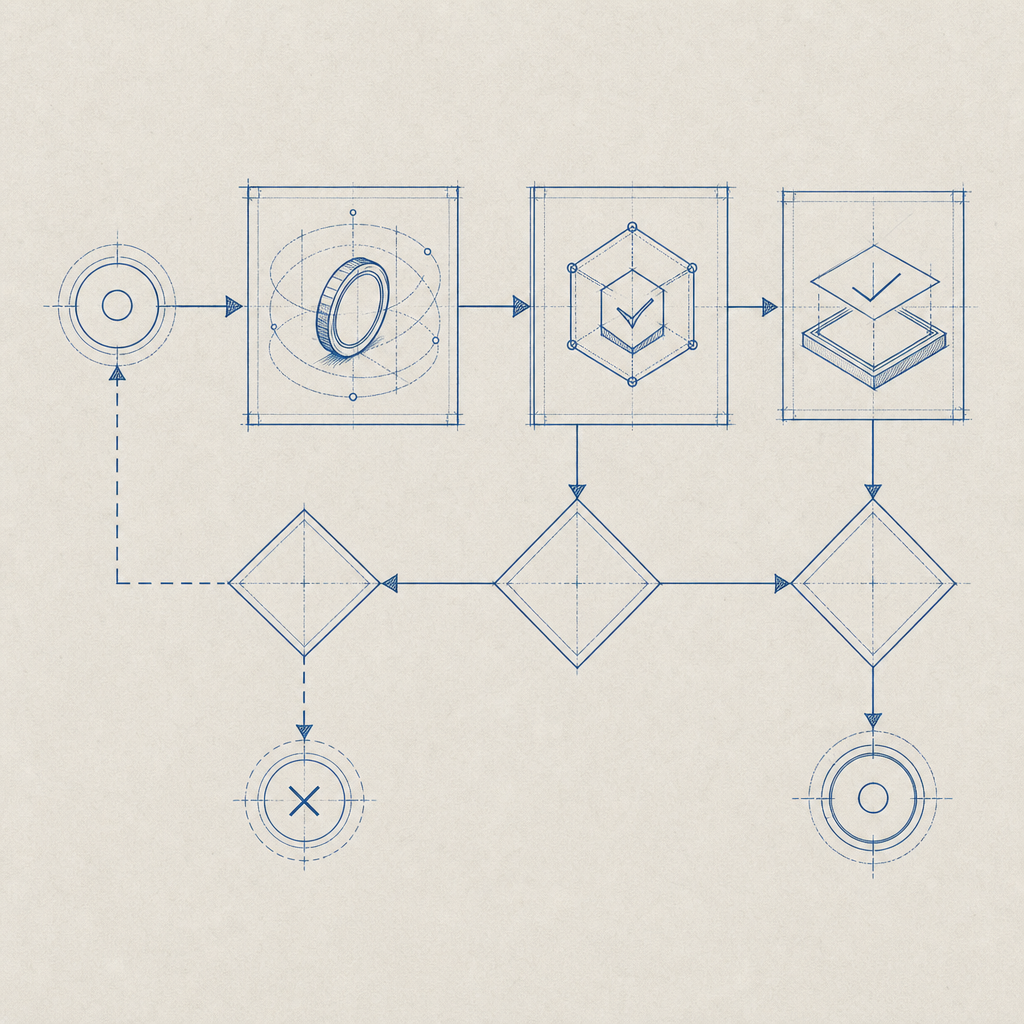
Here’s a simple way to think about it:
# English comments only
1. Browser loads challenge
2. Challenge returns pass_token
3. Client submits pass_token with the form
4. Server sends POST /v1/validate
5. Server checks:
- token exists
- token is fresh
- token matches the expected action
- token is tied to the right client_ip or session
6. Only then process the requestThis is why a captcha buster often succeeds against weaker deployments but not stronger ones. The challenge itself may be unchanged; the trust model is what breaks.
How to defend without frustrating real users
You do not need to make CAPTCHA more annoying to make it safer. Better defense usually comes from integration quality and risk-based design.
1) Validate server-side every time
The validation call should happen on your backend, not in the browser. CaptchaLa’s validation flow, for example, is a straightforward server check using POST https://apiv1.captcha.la/v1/validate with pass_token and client_ip, authenticated by X-App-Key and X-App-Secret. That pattern keeps secrets off the client and prevents users from self-approving their own requests.
2) Bind the token to the specific action
A signup token should not be reusable for password reset, and a login token should not authorize checkout. Even if your challenge provider returns a successful result, your app should verify that the token matches the expected action and route.
3) Keep issuance server-controlled where possible
If your flow requires server-issued challenge tokens, protect that endpoint carefully. CaptchaLa’s POST https://apiv1.captcha.la/v1/server/challenge/issue is meant to be part of a controlled backend flow, not a public shortcut. This matters because attackers often probe for any endpoint that generates a valid token path.
4) Add context, not just friction
Context can include:
- IP reputation
- velocity checks
- device or session consistency
- recent failed attempts
- unusual form timing
A CAPTCHA challenge is then only one gate in a larger policy. That makes it much harder for automation to scale.
5) Measure false positives
If legitimate users are failing challenges, the system is too aggressive or poorly integrated. The objective is to reduce abuse while preserving conversion. That is also where CaptchaLa tends to fit well for teams that want a clear server-side validation model without overcomplicating the flow.
Comparing common CAPTCHA approaches
Different products make different tradeoffs. Here’s a practical comparison from a defender’s perspective:
| Option | Typical strength | Operational notes | Good fit for |
|---|---|---|---|
| reCAPTCHA | Medium to high | Familiar, widely deployed; can add user friction depending on risk signals | General web forms |
| hCaptcha | Medium to high | Often used as an alternative with different privacy and monetization tradeoffs | Public forms, communities |
| Cloudflare Turnstile | Medium to high | Low-friction for many users; works well when paired with broader bot controls | Sites already using Cloudflare |
| Custom validation flow | Variable | Depends entirely on implementation quality | Teams with strong security engineering |
The important point is that no CAPTCHA should be treated as a complete defense on its own. A captcha buster succeeds when the integration assumes the challenge is the entire control. It rarely is.
Practical implementation details that close gaps
A solid deployment has a few non-negotiables:
- Use short-lived tokens
- Reduce replay value.
- Verify on the backend
- Never trust client-side success alone.
- Match token to request context
- Compare action, session, and IP where appropriate.
- Log outcomes
- Track validation success, failure, and timing anomalies.
- Fallback safely
- If validation is unavailable, fail closed for sensitive actions.
Here is a concise pattern you can adapt:
# English comments only
receive form submission
extract pass_token and client_ip
result = call_validate_api(pass_token, client_ip)
if result is valid and result.action == expected_action:
process_request()
else:
reject_request()
record_security_event()For teams building across platforms, broad SDK coverage can reduce integration mistakes. CaptchaLa supports 8 UI languages and native SDKs for Web (JS/Vue/React), iOS, Android, Flutter, and Electron, plus server SDKs like captchala-php and captchala-go. That helps keep the client experience consistent while keeping the decisive check on the server.
Where this leaves defenders
If your threat model includes automation, a captcha buster is just one of many pressures on the edge of your application. The defense is not to chase every solver technique individually. It is to make abuse expensive and validation unambiguous.
That means:
- server-side verification every time
- short-lived, single-use tokens
- action-specific binding
- layered signals beyond CAPTCHA
- monitoring for replay and unusual volume
For teams that want a cleaner path to that setup, docs show the integration flow and pricing outlines tiers from free usage to higher-volume plans. The goal is not more friction; it is better certainty.
Where to go next: review the implementation details in the docs or compare plans at pricing.