A captcha box is the challenge container your site uses to tell humans from automated traffic. In practice, it’s the visible checkpoint a user sees when a form, login, signup, or sensitive action needs an extra layer of verification.
That sounds simple, but the design choices around a captcha box matter a lot: when it appears, how much friction it adds, whether it works on mobile, and how easily it fits into your stack. A good implementation reduces abuse without turning legitimate users away.
What a captcha box actually does
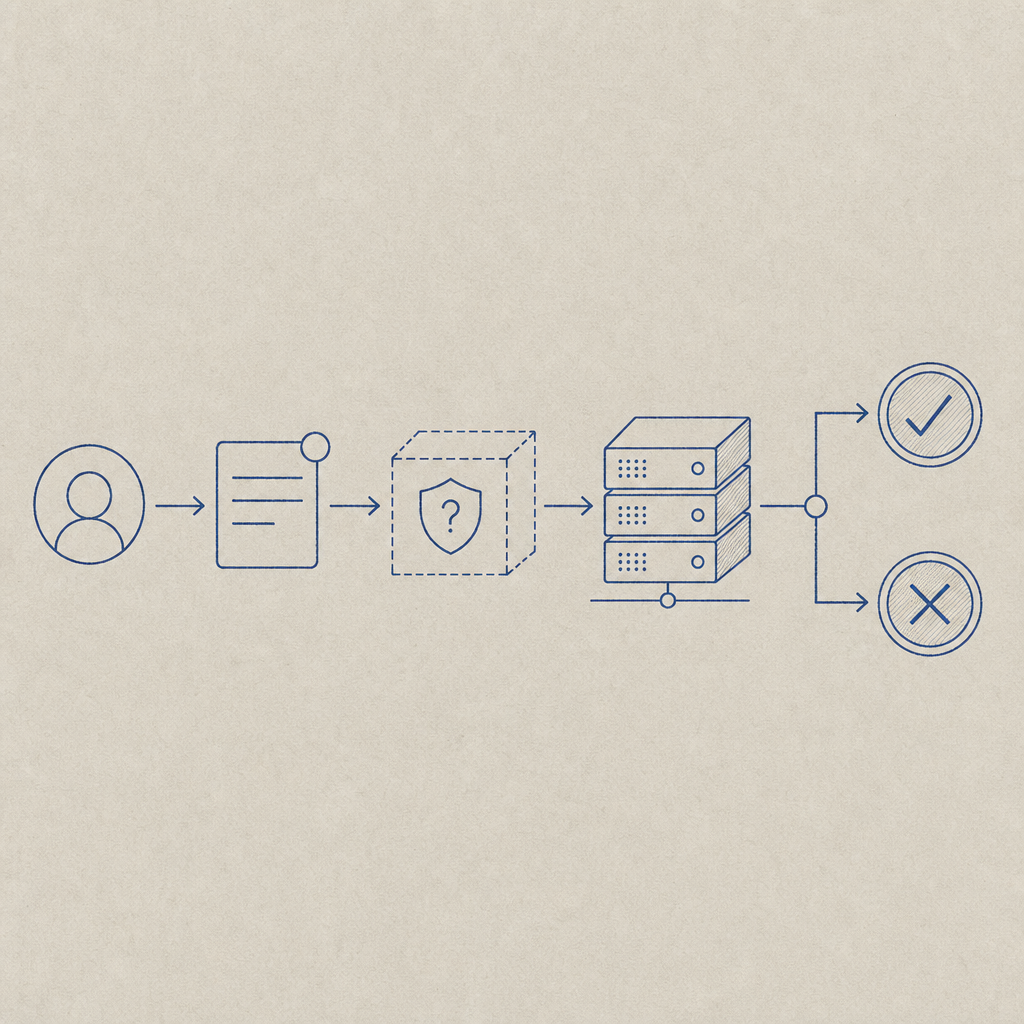
At a high level, a captcha box helps answer a single question: “Is this interaction likely coming from a real person?”
A modern captcha box can do more than display distorted text or a puzzle. It may coordinate client-side signals, a server-issued challenge, and a validation step that confirms the interaction before you accept the request. That means the box is only one part of the system; the backend verification is what gives it security value.
For teams building a signup flow, checkout form, or password reset page, the captcha box is usually a gate, not the entire defense. You still want rate limiting, abuse monitoring, device risk checks, and sensible business rules. The box is most useful when it protects high-value endpoints and only appears when needed.
When to show a captcha box
Not every request deserves a challenge. If you show a captcha box too early or too often, you create friction. If you never show it, you invite abuse. The sweet spot is usually risk-based.
Here are common moments when a captcha box makes sense:
- Account creation, especially if disposable email abuse is a problem.
- Login attempts after repeated failures or unusual behavior.
- Password reset requests, where abuse can become noisy quickly.
- Comment posting, contact forms, and lead forms that attract automated spam.
- Promotional or inventory-sensitive actions such as coupon redemption, waitlists, or ticketing.
A useful rule of thumb: if the action is low-friction for a human but expensive for you to abuse at scale, consider a captcha box. If the action is high-stakes, pair it with additional controls rather than relying on the box alone.
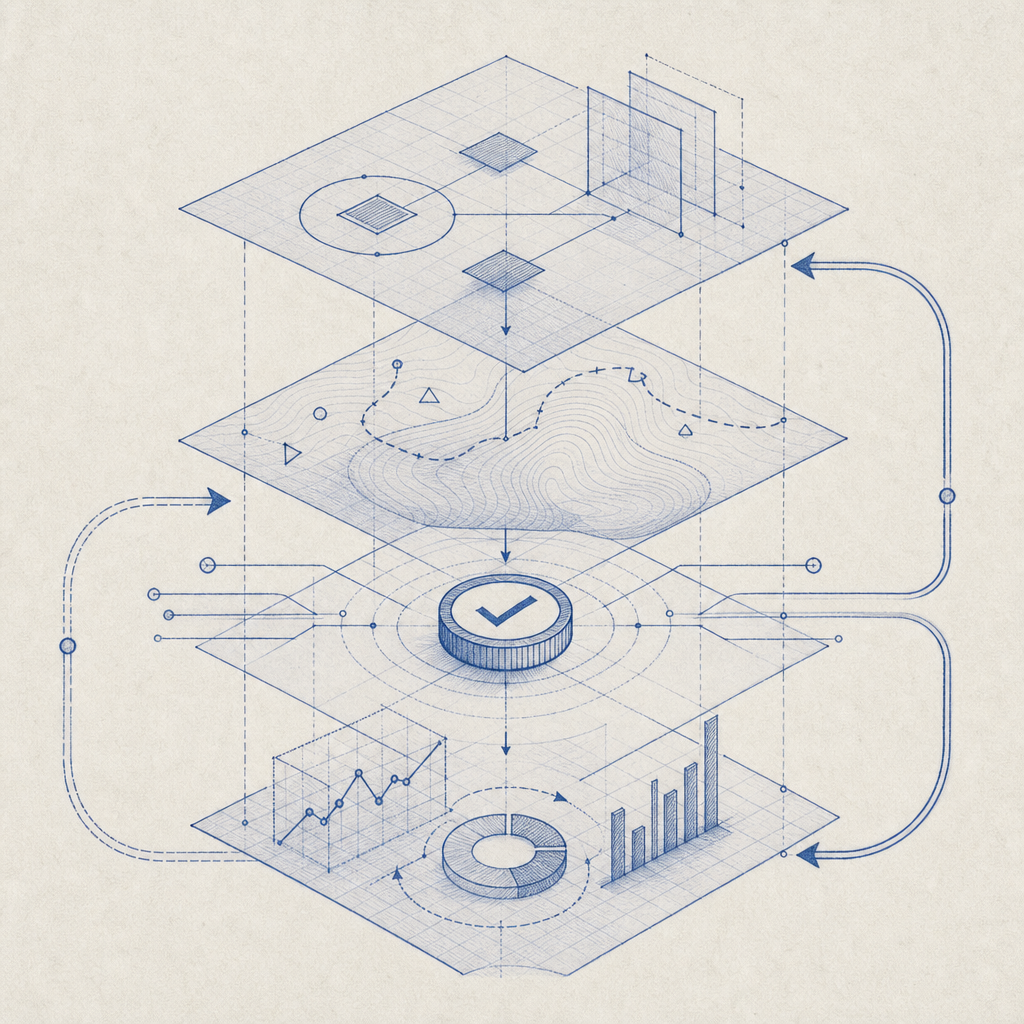
A practical decision flow
- Measure abuse volume on the endpoint.
- Decide whether you need unconditional challenge or risk-based challenge.
- Choose when the captcha box appears: before submit, after a suspicious signal, or only for repeated attempts.
- Validate server-side every time.
- Log outcomes so you can tune the policy later.
That last step matters more than most teams expect. If you can’t see pass/fail rates by route, region, or device type, you’re guessing.
Comparing common captcha box approaches
Different providers handle the captcha box differently. The right choice depends on your product, platform mix, and tolerance for friction.
| Provider | Typical style | Strengths | Tradeoffs |
|---|---|---|---|
| reCAPTCHA | Familiar checkbox / adaptive challenges | Widely recognized, easy for many teams to start with | Can feel opaque; tuning and privacy review may take effort |
| hCaptcha | Challenge-oriented, often used as a drop-in alternative | Strong anti-abuse focus, flexible deployment | Some users find the challenges more intrusive |
| Cloudflare Turnstile | Mostly non-interactive verification | Low-friction experience, simple for many sites behind Cloudflare | Less of a “box” in the classic sense; fit depends on your architecture |
| CaptchaLa | Flexible CAPTCHA / bot-defense flow | Native SDKs, multiple platforms, server validation, first-party data only | You still need to design the right policy for your app |
If your product spans web, mobile, and desktop, the implementation details become more important than the visual style of the captcha box. CaptchaLa supports Web JS/Vue/React plus iOS, Android, Flutter, and Electron, which helps keep the same verification logic across surfaces.
How to integrate a captcha box without annoying users
The best captcha box feels almost invisible until it’s needed. That comes down to three choices: loading, triggering, and verification.
1) Load it only where it belongs
Don’t put the challenge logic on every page. Load it on routes that actually need protection, such as signup, payment, or recovery flows. If you’re using a client SDK or loader, keep the integration local to the form rather than global.
For web, one possible pattern is to load the challenge script only when the protected view mounts:
// Load the captcha box only on sensitive forms
function loadCaptchaBox() {
const script = document.createElement('script');
script.src = 'https://cdn.captcha-cdn.net/captchala-loader.js';
script.async = true;
document.head.appendChild(script);
}2) Validate on the server, always
The client experience is just the front end of the trust chain. Your server must verify the pass token before accepting the action.
A typical validation call looks like this:
POST https://apiv1.captcha.la/v1/validate- body includes
pass_tokenandclient_ip - headers include
X-App-KeyandX-App-Secret
If you need a server-issued challenge token first, there’s also:
POST https://apiv1.captcha.la/v1/server/challenge/issue
That separation is useful because the server can decide whether a challenge is warranted, then validate the result against your own application rules. CaptchaLa’s docs show the request/response shape clearly, which is helpful when you’re wiring this into an existing auth or form pipeline.
3) Match the box to the user’s context
A captcha box that works on desktop can still fail in real use if it ignores mobile UX, localization, or accessibility. Useful details include:
- 8 UI languages
- responsive placement near the form submit action
- clear retry states
- keyboard-friendly interaction
- fast timeout handling for flaky mobile networks
If you support native apps, the same concept should behave consistently there too. CaptchaLa provides native SDKs for Web, iOS, Android, Flutter, and Electron, plus server SDKs such as captchala-php and captchala-go, so your frontend and backend can stay aligned.
What to evaluate before you ship
Before you treat a captcha box as “done,” test it like a production control, not a UI widget.
- Pass rate by device type: Compare desktop, mobile web, and app traffic.
- Challenge frequency: Too many boxes usually means the policy is too aggressive.
- Abuse reduction: Track the targeted metric, such as spam submissions or account creation fraud.
- Latency: Measure the time added to your critical path, including network and validation delays.
- Localization: Check that the challenge copy is understandable in every supported language.
- Fallback behavior: Decide what happens if validation fails due to network problems or expired tokens.
- Privacy posture: Confirm whether the provider uses first-party data only, third-party tracking, or a mix.
That last point is especially relevant for teams with strict compliance requirements. Some providers rely more heavily on cross-site or broader telemetry than others, so it’s worth checking your review criteria before you commit. Keep the architecture aligned with your own data policies rather than assuming every captcha box works the same way.
Choosing the right level of friction
A captcha box is not a universal anti-bot answer. It’s a selective friction mechanism. If you use it everywhere, you’ll frustrate legitimate users. If you never use it, you’ll leave obvious abuse paths open.
A better framing is this: use the captcha box where the cost of abuse exceeds the cost of a small pause. That’s why many teams deploy it on signup, login recovery, forms, and high-value actions, then let analytics decide where to tighten or relax the policy.
For teams evaluating implementation options, pricing can also matter because traffic patterns change quickly. CaptchaLa has a free tier at 1000 monthly validations, with Pro in the 50K-200K range and Business at 1M, which makes it easier to start small and scale as your protection needs grow. You can compare plans on pricing without needing to redesign your flow later.
Where to go next: if you’re planning a rollout, start with the integration guidance in the docs and then map your protected endpoints before you ship.