If you’re asking what “anti bot opening chess” means, the short answer is: it’s the defender’s first few moves in an automated abuse game. The opening matters because bots usually reveal themselves early—through velocity, consistency, session reuse, impossible navigation paths, or other patterns that a human rarely produces at scale. Good bot defense doesn’t wait for damage; it sets the board so the first suspicious move triggers a challenge, a token check, or a quieter risk decision.
That opening should feel invisible to real users and expensive for automation. In practice, that means combining browser signals, request timing, challenge issuance, and server-side validation into one flow that can be tuned per route, per risk level, and per user journey.
Why the opening move matters
Most abuse programs don’t start with a dramatic attack. They start with “normal-looking” requests: signup attempts, login retries, coupon checks, inventory polling, scraping of public pages, or fake form submissions. The early stage is where defenders have the most leverage because a bot has to establish a session and prove behavior before it can scale.
A useful mental model is to split the opening into three layers:
- Surface signals: user agent consistency, request headers, navigation sequence, and timing.
- Challenge decisions: whether to issue a CAPTCHA, a friction step, or a pass-through.
- Verification: whether the token returned by the client matches what your server expects.
This is why anti bot opening chess is less about one “magic” challenge and more about making the first automated move cost something. If the bot can’t cheaply move from landing page to form submit to account creation, the abuse campaign loses efficiency.
What defenders usually watch first
Typical opening-phase indicators include:
- High request rate from a single IP, ASN, or device cluster
- Repeated submission attempts with small payload changes
- Fresh sessions that immediately jump to sensitive endpoints
- Client behavior that skips normal page assets or navigation steps
- Low entropy in interaction timing, mouse paths, or keystroke cadence
None of these prove malicious intent on their own. The point is correlation. Defenders score these early moves together, then decide whether to allow, challenge, or step up authentication.
Choosing the right defense pattern
There isn’t a single correct CAPTCHA strategy, and that’s especially true in the opening phase. The right choice depends on whether you’re protecting logins, registrations, checkout, scraping-sensitive content, or API-adjacent forms.
Here’s a practical comparison of common options:
| Solution | Strengths | Tradeoffs | Best fit |
|---|---|---|---|
| reCAPTCHA | Familiar, widely recognized | Can add user friction; tuning may be limited for some teams | General web forms, broad compatibility |
| hCaptcha | Flexible challenge model | Sometimes more visible to users | Sites wanting challenge diversity |
| Cloudflare Turnstile | Low-friction, often invisible | Works best in Cloudflare-aligned setups | Teams prioritizing lightweight flows |
| Custom risk checks + challenge | Highly tailored | More implementation and maintenance effort | Sensitive workflows with unique abuse patterns |
The “opening chess” part is not which brand you choose, but how you place the piece. You want the first challenge to land only when signals justify it, and you want the server to be the source of truth. That keeps client-side deception from becoming the whole security model.
A defender-friendly rule of thumb
A good opening flow usually does three things:
- Collects a small amount of client context
- Issues a token or challenge only when needed
- Validates the result server-side before trusting the request
That last step is non-negotiable. If the client says “I passed,” your server still has to check it.
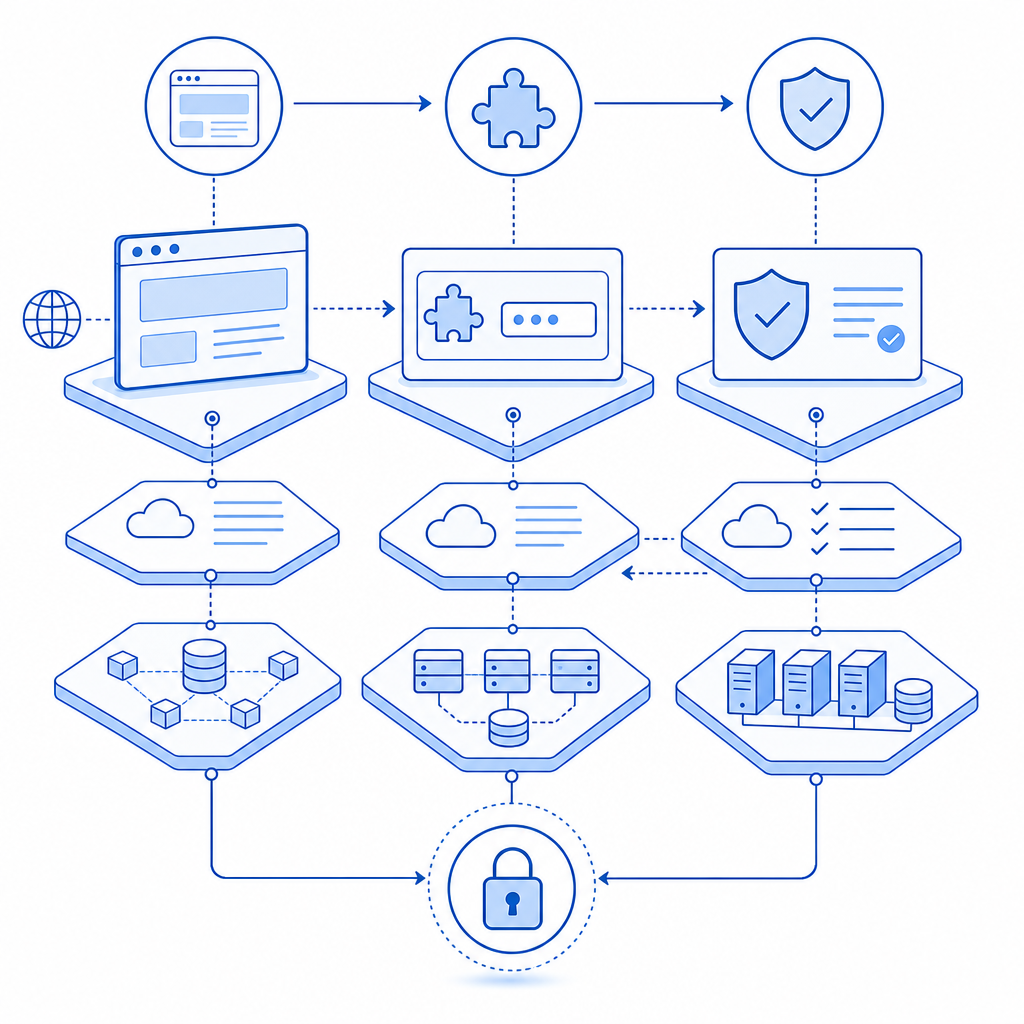
A practical implementation flow
Here’s a simple flow that works well for signup or login pages:
- Serve the page and load the challenge script only where needed.
- Observe request and interaction signals.
- Decide whether to render a challenge.
- Return a pass token if the user completes the step.
- Validate the token on your server before accepting the action.
For CaptchaLa, the loader is served from https://cdn.captcha-cdn.net/captchala-loader.js, and validation happens server-side with POST https://apiv1.captcha.la/v1/validate using pass_token, client_ip, plus X-App-Key and X-App-Secret. That separation keeps the trust boundary where it belongs. CaptchaLa also supports native SDKs for Web (JS/Vue/React), iOS, Android, Flutter, and Electron, which helps if your “opening” includes mobile or desktop app flows rather than only browser forms.
Here’s a minimal server-side example of the validation idea:
// English comments only
// Send the pass token and client IP to the validation endpoint
async function validateCaptcha(passToken, clientIp) {
const res = await fetch("https://apiv1.captcha.la/v1/validate", {
method: "POST",
headers: {
"Content-Type": "application/json",
"X-App-Key": process.env.CAPTCHALA_APP_KEY,
"X-App-Secret": process.env.CAPTCHALA_APP_SECRET
},
body: JSON.stringify({
pass_token: passToken,
client_ip: clientIp
})
});
if (!res.ok) return false;
const data = await res.json();
return data && data.valid === true;
}If you need a challenge issuance step for a higher-risk path, CaptchaLa also provides a server-token flow via POST https://apiv1.captcha.la/v1/server/challenge/issue. That’s useful when you want your backend to decide that a request deserves a challenge before the client ever sees it.
Designing for humans, not just stopping bots
The best anti bot opening chess move is one real users barely notice. If every first interaction becomes a puzzle, you’ll create the kind of friction attackers can afford but users won’t tolerate.
A few practical design choices help:
- Challenge late, not early, unless risk is high. Let low-risk traffic move through.
- Use contextual triggers. Login bursts and signup spikes should not be treated the same as a one-off page visit.
- Keep the challenge accessible. Multiple locales, clear text, and mobile-friendly interactions matter.
- Measure false positives. The opening is where over-blocking hurts most.
CaptchaLa’s 8 UI languages can help if you serve mixed audiences, and its pricing tiers may fit different volumes: free tier for 1,000 monthly requests, Pro for roughly 50K–200K, and Business for 1M. That volume spread matters because the right opening strategy often depends on whether you’re protecting a small product, a fast-growing app, or a high-traffic workflow.
How to tune your opening risk signals
A straightforward scoring model might assign points like this:
- New IP with no prior session history: +2
- Rapid form submission after page load: +2
- Multiple failed attempts on the same identifier: +3
- Headless-like browser behavior or missing expected assets: +3
- Known good session or trusted device history: -2
You can then choose thresholds:
- 0–2: allow
- 3–4: passive check
- 5+: challenge
- 7+: challenge plus rate limit
That kind of policy keeps the opening flexible. It also makes it easier to explain decisions internally, which is important when product, support, and security teams all need to understand why users are being challenged.
Building a defendable opening without overcomplicating it
You do not need a giant security stack to defend the first move. You need a clear boundary between client signals and server trust, plus enough flexibility to adjust when abuse patterns shift.
If you already use reCAPTCHA, hCaptcha, or Cloudflare Turnstile, the main question is whether your opening flow is configured to reflect your actual risk. Are you challenging the right route? Are you validating server-side? Are you measuring drop-off and abuse reduction? Those operational questions matter more than the logo on the widget.
For teams that want a straightforward implementation path, docs are the place to confirm endpoints, SDK options, and flow details. If you’re evaluating request volume or planning a rollout, pricing is the quickest way to map traffic to tier. And if you want to see how the pieces fit together in a real product, CaptchaLa is the starting point.
Where to go next: review the integration flow in the docs, or compare request volume against the pricing page before you wire up your first opening defense.