Anti bot evasion is the set of tactics bots use to look human enough to slip past detection. If you defend a login, signup, checkout, scraping-sensitive, or abuse-prone flow, the practical answer is: reduce signals bots can imitate, verify server-side, and add friction only when risk is high.
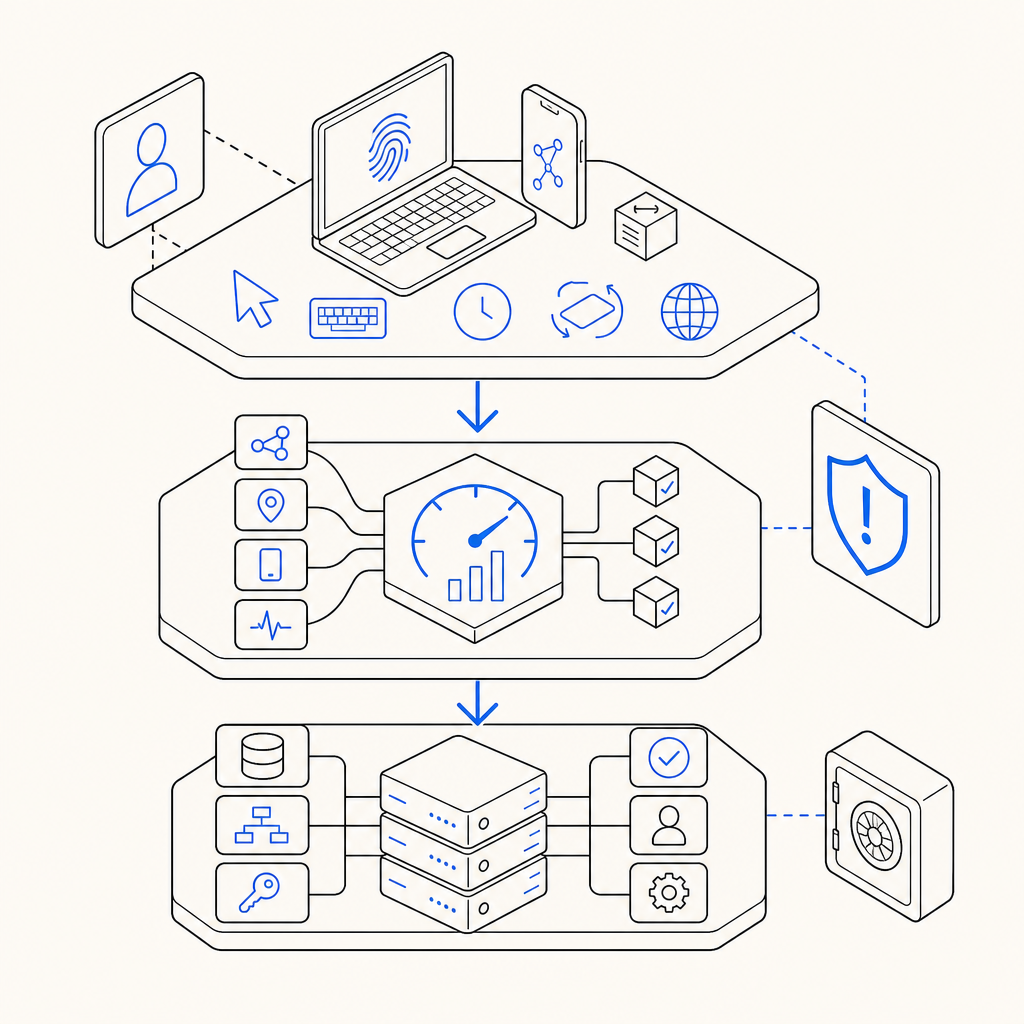
That sounds simple, but the details matter. Evasion is not just “rotate an IP and retry.” Modern automated traffic can vary fingerprints, pace requests, replay browser-like behavior, and even step around naive CAPTCHA checks. Defenders need layered controls that observe session behavior, challenge suspicious clients, and validate responses in a way the client cannot fake.
What anti bot evasion actually looks like
Anti bot evasion is any attempt to make automation appear legitimate enough to bypass bot detection. From a defender’s perspective, the important point is not the trick itself but the weakness it targets. If your checks depend on only one or two signals, evasive traffic will usually find a path around them.
Common evasion patterns include:
Fingerprint churn
Bots alter headers, user agents, WebGL values, or browser features to avoid clustering.Behavior shaping
They slow down, add jitter, move the mouse, or simulate typing to resemble real users.Proxy and network rotation
IP reputation becomes less useful when traffic is distributed across residential, mobile, or cloud networks.Challenge replay attempts
A client may try to reuse a token, race a request, or submit a proof from one session in another.Workflow probing
Automation tests where a form is least protected and sends requests only on the path that appears weakest.
This is why anti bot defense should not rely on a single checkbox on the front end. A client-side widget can help, but the real decision should happen on the server, where the token is validated, request context is inspected, and replay is rejected.
The defender’s playbook: reduce what bots can imitate
The most reliable strategy is to make evasion expensive without making legitimate use painful. That usually means combining browser signals, behavioral checks, and server-side proof.
1. Validate on the server, not just in the browser
Client-side checks are easy to observe and harder to trust on their own. A bot can load scripts, execute them, and still tamper with the request afterward. The safer pattern is:
- issue or collect a pass token in the client,
- send it to your backend,
- validate it against your anti-bot provider,
- decide whether to allow, challenge, or deny.
For CaptchaLa, validation happens with a server-to-server request to:
POST https://apiv1.captcha.la/v1/validate
The request body includes:
{
"pass_token": "token-from-client",
"client_ip": "203.0.113.42"
}And it is authenticated with X-App-Key plus X-App-Secret. That setup matters because the browser never gets the secret, which makes token forgery and casual replay much harder. CaptchaLa also supports a server-token issuance flow via:
POST https://apiv1.captcha.la/v1/server/challenge/issue
2. Make signals harder to spoof in combination
Any individual signal can be noisy. The key is correlation. For example:
- a stable browser fingerprint with impossible timing is suspicious,
- a realistic cursor path with fresh IP reputation may still be automation,
- a valid challenge token without matching session context may deserve rejection.
Here’s a simple defender-side policy model:
if token_invalid:
deny_request
else if token_valid and risk_score_high:
require_step_up
else if token_valid and risk_score_medium:
allow_with_logging
else:
allow_requestThis is intentionally boring, and that is good. Anti bot evasion becomes much less effective when a bot has to satisfy multiple checks at once rather than one brittle gate.
3. Use progressive friction
Not every request needs the same level of scrutiny. A signup form, password reset, card checkout, and public contact form do not carry the same abuse cost.
A practical sequence is:
- allow low-risk traffic through with minimal friction,
- challenge suspicious traffic,
- escalate if the same session keeps failing,
- rate-limit abusive patterns even after a successful challenge.
This prevents you from overreacting to every anomaly. Good defenses are selective, not dramatic.
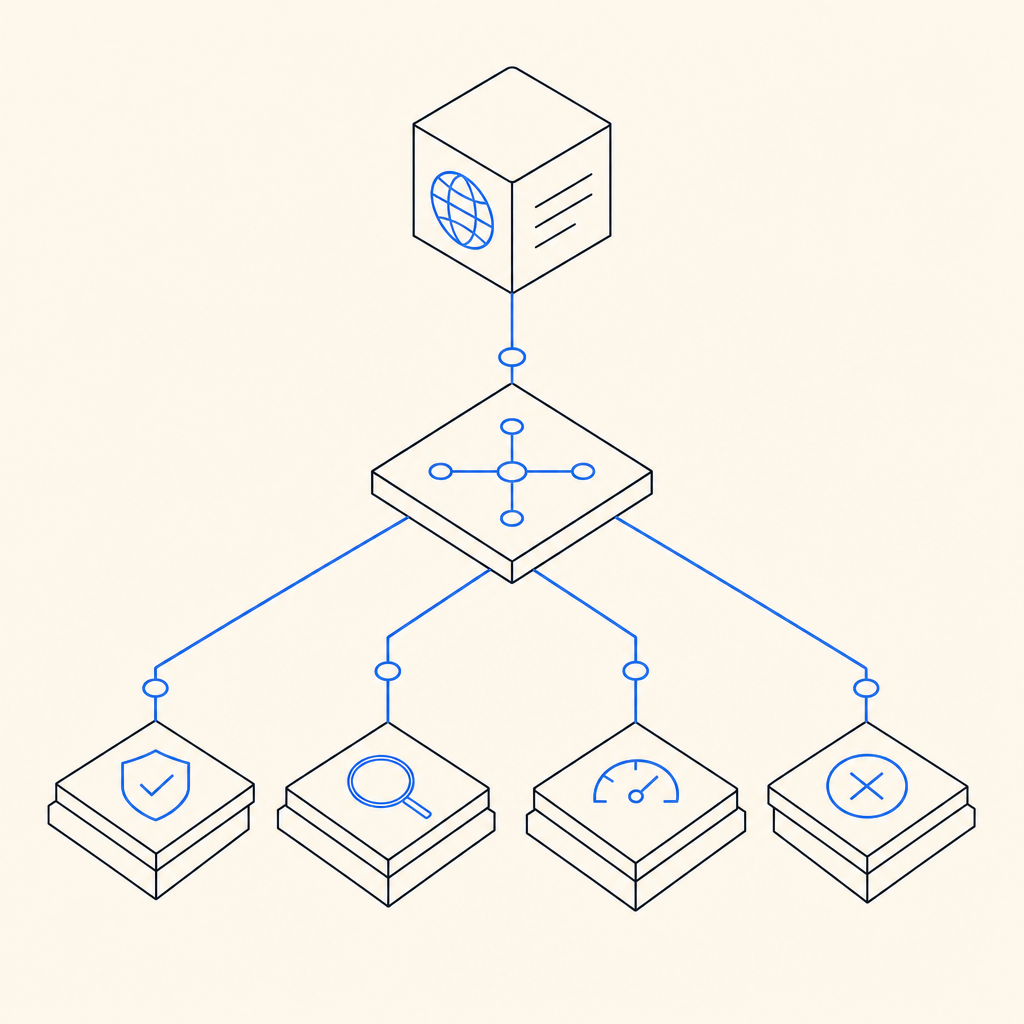
How CAPTCHA products differ in anti bot evasion resistance
CAPTCHA products overlap, but their architecture affects how well they hold up when adversaries adapt. The main questions are: how easy is the proof to spoof, where is validation performed, and how much context can the server use?
| Product | Typical strength | Common limitation | Defender takeaway |
|---|---|---|---|
| reCAPTCHA | Strong ecosystem and broad familiarity | Can become a high-friction step if overused; signals may be treated as opaque | Good for many sites, especially when paired with server checks |
| hCaptcha | Flexible challenge model | Still depends on correct integration and backend enforcement | Useful when you want visible challenge control |
| Cloudflare Turnstile | Low-friction user experience | Best when your traffic already passes through Cloudflare’s edge | Strong option for edge-centered deployments |
| CaptchaLa | First-party data only, server validation, native SDK coverage | Requires your own backend integration to get full value | Fits teams that want explicit validation control and multiple app platforms |
The big lesson is that anti bot evasion usually succeeds when a site treats the front-end challenge as the final authority. No matter which provider you use, the backend should verify the result and tie it to the current request.
CaptchaLa’s integration surface is broad enough to support that pattern across web and mobile: JavaScript, Vue, React, iOS, Android, Flutter, Electron, plus server SDKs like captchala-php and captchala-go. It also offers 8 UI languages, which is useful if you need to localize friction for real users while keeping the same risk logic underneath.
Integration details that make defenses sturdier
A lot of anti bot evasion risk comes from implementation gaps, not product choice. These are the points that tend to matter most:
Keep the challenge and the request bound together
If a token is generated for one session, it should only be accepted for that session or that immediate action. Do not let a token float around and get reused later.
Send the right context to validation
Include the client IP when you can. IP is not perfect, but it is still a useful context field when combined with other signals. For CaptchaLa validation, that means passing client_ip along with the token.
Verify before sensitive actions
Validate before creating accounts, sending OTPs, submitting checkouts, posting content, or triggering expensive downstream calls. If the action is costly, the validation should happen before the cost.
Log outcomes for tuning
Store whether a request passed, was challenged, failed, or was rate-limited. Over time, that helps you understand false positives and emerging evasion patterns.
Respect privacy boundaries
Use only the data you need. Some teams prefer first-party data only, which can simplify governance and reduce dependencies on third-party tracking assumptions.
If you are building the integration from scratch, the docs are the place to start. If you are sizing volume, the pricing page is useful for comparing the free tier at 1000 monthly validations, Pro at 50K-200K, and Business at 1M.
A practical checklist for teams defending against evasion
If you want a short implementation checklist, use this:
- Put the challenge on the specific high-risk action, not the whole site.
- Validate tokens on your backend with a secret that never reaches the browser.
- Bind validation to request context, including IP when available.
- Apply step-up friction only when risk rises.
- Rate-limit repeated failures and suspicious retries.
- Review logs regularly for patterns that suggest automation adaptation.
- Test with real traffic shapes, not just one browser and one network.
That checklist is intentionally broader than “add a CAPTCHA.” Anti bot evasion is a moving target, so the defense has to be layered and measurable.
Where to go next: if you want to see whether CaptchaLa fits your stack, start with the docs or compare usage tiers on the pricing page.