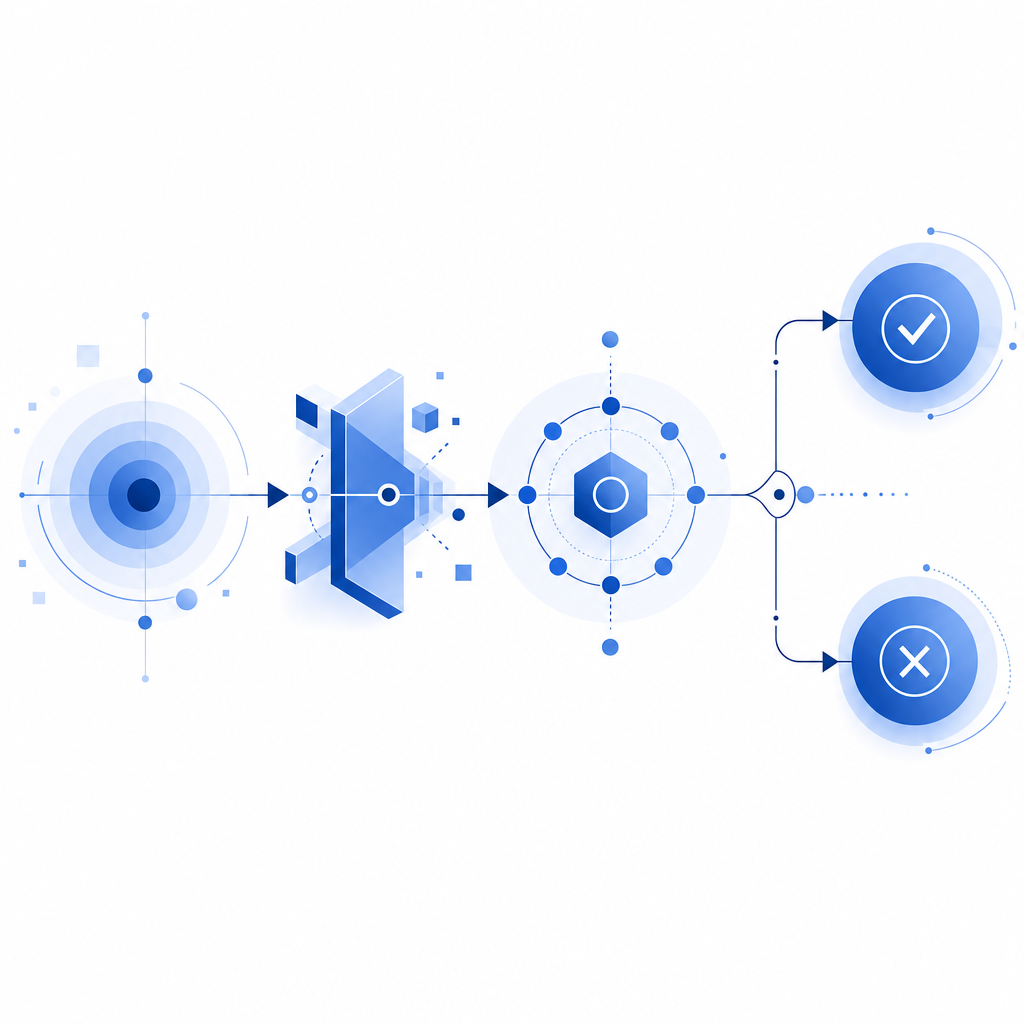
A captcha and challenge flow is a step-up verification pattern: when a request looks suspicious, the system asks for proof that a real user is present before allowing the action to continue. In practice, that means a risk signal triggers a challenge, the user completes it, and your server validates the result before trusting the request.
That sounds simple, but the details matter. A good implementation has to balance friction, fraud resistance, accessibility, privacy, and latency. It also needs to fit real products: signups, credential checks, checkout abuse prevention, scraping defense, and API protection. Done well, the challenge is invisible most of the time and only appears when the risk is worth the extra step.
What “captcha and challenge” actually means
People often use “captcha” as a generic term, but a modern captcha and challenge system usually includes two parts:
- A risk decision that determines whether to challenge.
- A verification step that proves the client passed the interaction.
Traditional CAPTCHAs mostly focus on the second part: puzzles, image selection, or checkbox-style verification. A broader challenge system includes other checks too, such as browser integrity, token issuance, device signals, and server-side validation.
How the flow works
A typical flow looks like this:
- The browser loads a lightweight script from your challenge provider.
- The provider evaluates the session and produces a pass token if the interaction is accepted.
- Your frontend submits the token with the protected form or API request.
- Your backend validates the token against the provider before taking action.
- If the token is invalid or missing, you block, step up, or retry.
This is the important part: the challenge is not the security control by itself. The security control is the server-side validation and the policy you attach to it.
# English comments only
client -> load challenge script
client -> receive pass token
client -> submit pass_token + client_ip to backend
backend -> POST validate request to provider
backend -> allow action only if validation succeeds
Where captcha and challenge protects you most
A challenge is most useful when an action is valuable enough to attract automation, but not so rare that a small amount of friction is acceptable.
Common examples include:
- account creation
- password reset requests
- login attempts after suspicious patterns
- checkout and coupon abuse
- scraping of public or semi-public content
- poll, vote, or form manipulation
- API abuse from low-trust clients
The best deployments do not challenge every request. They challenge only when the risk score, behavior pattern, or endpoint sensitivity suggests abuse.
A practical decision model
You can think of the policy like this:
- Low risk: allow silently.
- Medium risk: challenge.
- High risk: block, rate-limit, or require stronger verification.
That model keeps legitimate users moving while forcing automated traffic to do more work.
Comparing common challenge options
There are several well-known options in the market, and they differ more in ergonomics and ecosystem than in the basic idea.
| Provider | Typical strength | Common tradeoff | Notes |
|---|---|---|---|
| reCAPTCHA | Very familiar, broad adoption | Can add friction and may feel heavier depending on setup | Often used as a default choice |
| hCaptcha | Good abuse resistance focus | Some teams find tuning and UX more involved | Common in security-conscious deployments |
| Cloudflare Turnstile | Low-friction experience | Usually fits best when you are already in Cloudflare’s stack | Useful for many public forms |
| CaptchaLa | Lightweight challenge flow with native SDK coverage | You still need sensible policy design | Supports web, mobile, and server validation |
No option is universally right. The real decision is how well the tool fits your users, your stack, and your trust model.
If you are implementing a new system, CaptchaLa is worth reviewing alongside the more established names because it gives you both client-side and server-side building blocks without forcing a single integration style.
Implementation details that matter
A challenge system is only as good as the details around it: token transport, validation, expiration, and error handling.
Key facts to design around
- Use a short-lived pass token and validate it on the server.
- Send the client IP when your provider supports it, because it helps the risk decision.
- Keep your secret keys only on the backend.
- Make validation a required gate before the protected action runs.
- Treat validation failures as security events, not just UI failures.
With CaptchaLa, the server validation endpoint is:
POST https://apiv1.captcha.la/v1/validate
The body uses:
{
"pass_token": "token-from-client",
"client_ip": "203.0.113.10"
}And the request is authenticated with X-App-Key and X-App-Secret.
That separation is what keeps the front end from becoming a trust boundary.
Example backend flow
# English comments only
receive form submission
extract pass_token and client_ip
if pass_token is missing:
deny request
call provider validate endpoint with app key and secret
if validation fails:
deny request
continue with protected actionIf you need a server-issued challenge token for a custom flow, CaptchaLa also exposes:
POST https://apiv1.captcha.la/v1/server/challenge/issue
That is useful when your backend decides that a session should be challenged before the client renders the next step.
For implementation specifics, the docs are the right place to check exact request formats, SDK setup, and integration examples.
Choosing the right integration pattern
The best integration pattern depends on your product surface.
Web apps
For web, CaptchaLa supports JavaScript plus native SDKs for Vue and React. The loader is:
https://cdn.captcha-cdn.net/captchala-loader.js
That lets you add the challenge without building the client interaction from scratch.
Mobile and desktop
If your challenge has to live inside apps, native SDK support matters a lot. CaptchaLa supports:
- iOS
- Android
- Flutter
- Electron
That makes it easier to keep the same policy logic across browser and app surfaces, rather than maintaining separate vendors or one-off checks.
Server-side ecosystems
If your stack is PHP or Go, there are server SDKs available:
captchala-phpcaptchala-go
For JVM-based teams, Maven coordinates are available as la.captcha:captchala:1.0.2. For Apple platforms, CocoaPods is Captchala 1.0.2. For Flutter, pub.dev is captchala 1.3.2.
Supportable UX and accessibility
A challenge system should not punish legitimate users. A few practices help:
- Prefer step-up checks over always-on puzzles.
- Keep the challenge visually and behaviorally simple.
- Revalidate only when necessary, not on every click.
- Surface clear fallback messaging when validation fails.
- Test on mobile, low-bandwidth, and assistive-tech flows.
CaptchaLa offers 8 UI languages, which matters more than people expect when your traffic is international.
Privacy, data handling, and operational fit
Security tools often fail because they collect too much, retain too much, or are hard to reason about. A challenge system should be explainable to your team and acceptable to your privacy posture.
A few questions to ask any provider:
- What data is used for risk assessment?
- Is first-party data enough for normal operation?
- Where does validation happen?
- How are tokens scoped and expired?
- What happens when the provider is unavailable?
CaptchaLa’s approach is centered on first-party data only, which simplifies compliance conversations for teams that want tighter control over what leaves the browser and server.
That does not eliminate your responsibility, of course. You still need to define:
- which endpoints are protected,
- how long a token is trusted,
- when to block versus step up,
- and how to log failed validations without storing sensitive data unnecessarily.
How to start without overengineering
The cleanest rollout is usually incremental:
- Protect one high-abuse endpoint first.
- Validate on the backend only.
- Measure challenge frequency and abandonment.
- Tune risk thresholds.
- Expand to other surfaces once you know the user impact.
That approach avoids the common mistake of wrapping everything in a challenge on day one and then spending the next month undoing the friction.
If you want to see packaging, plan sizing, or rollout options before you implement, pricing is a straightforward place to compare tiers. CaptchaLa’s published tiers include a free option at 1,000 requests per month, Pro at 50K–200K, and Business at 1M, which is enough to prototype, test, and grow into a real deployment.
Where to go next: read the docs for integration details, then choose a tier that matches your traffic and validation needs at pricing.