A true captcha alternative open source is usually not a single drop-in product; it’s more often a stack of components you assemble, operate, and maintain yourself. If you want the control and transparency of open source, that can work well — but it also means you own uptime, tuning, abuse response, and the long tail of bot evolution.
For teams that need less operational overhead, managed bot-defense platforms are often the practical middle ground: you still get strong controls and API-driven validation, without having to run the whole challenge pipeline yourself. The right choice depends on whether you optimize for control, privacy, maintainability, or speed of rollout.
What “open source” really means for CAPTCHA alternatives
When people search for a captcha alternative open source, they usually want one or more of these things:
- Transparency — the challenge logic is visible and auditable.
- Self-hosting — data stays under your control.
- Customization — you can adapt difficulty, UX, and risk rules.
- Lower vendor dependence — fewer external services in the critical path.
Those goals are valid. The tradeoff is that bot defense is not a static problem. Attackers adapt quickly, and the value of a challenge system depends on how well it can be updated, monitored, and integrated into your product. Open source can help with trust and flexibility, but it doesn’t automatically solve maintenance, abuse analytics, or global delivery.
A useful way to think about it: an open-source CAPTCHA component can be a building block, while a managed platform is an operational service. If your team has security engineering bandwidth, you may prefer building and hosting. If not, you may prefer a platform that exposes clean validation APIs and SDKs, like CaptchaLa.
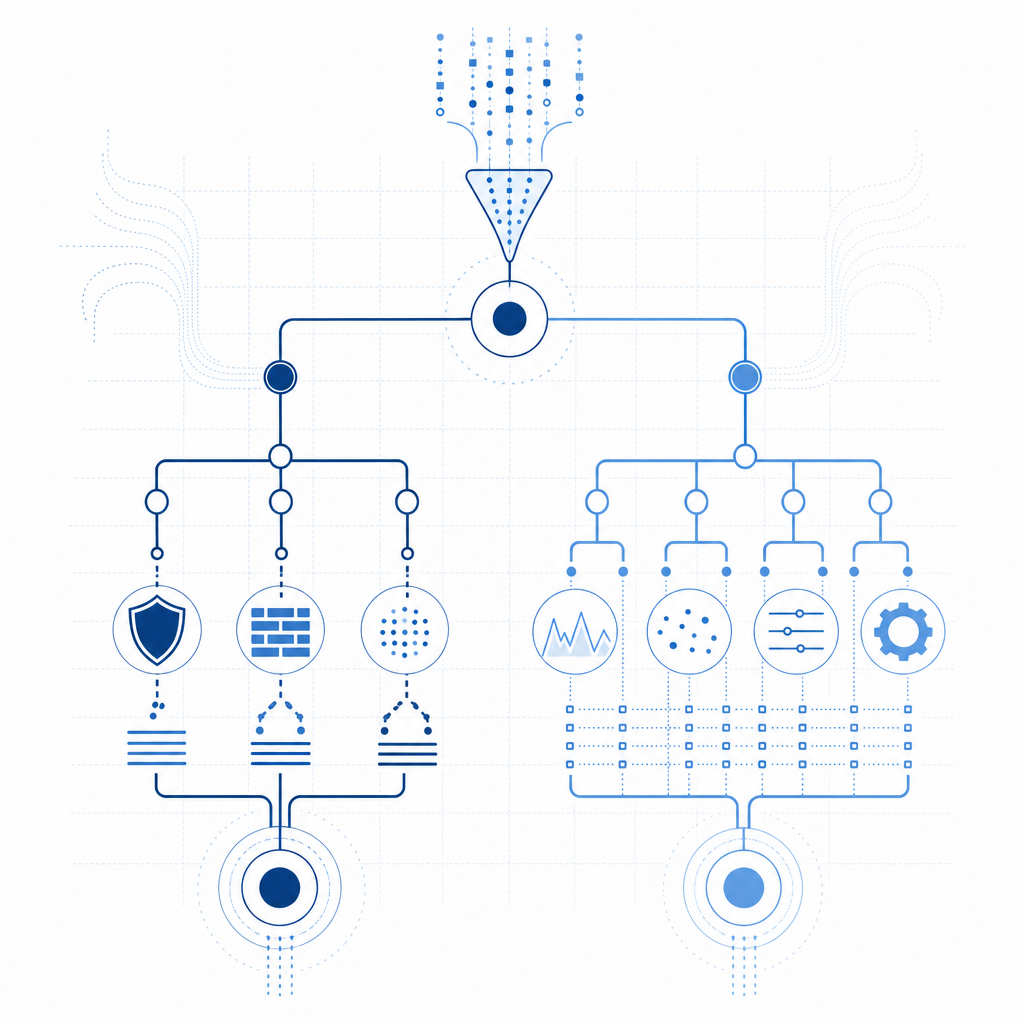
Comparing common options: open source, managed, and edge-based
Different tools solve different parts of the problem. Here’s a simple comparison across the three names most teams evaluate: reCAPTCHA, hCaptcha, and Cloudflare Turnstile, plus the open-source/self-hosted route.
| Option | Primary strength | Main tradeoff | Best fit |
|---|---|---|---|
| Open source/self-hosted | Maximum control and auditability | You maintain the system, infra, and updates | Teams with security engineering capacity |
| reCAPTCHA | Familiar ecosystem and broad adoption | Google dependency and UX/privacy considerations | Sites already standardized on Google tooling |
| hCaptcha | Strong abuse focus and flexible deployment | Still a third-party dependency | Teams wanting an alternative to reCAPTCHA |
| Cloudflare Turnstile | Low-friction UX and edge integration | Best when your traffic already passes through Cloudflare | Cloudflare-centric stacks |
| Managed independent platform | API-based integration, less ops burden | Vendor dependency, but often less than ad-tech CAPTCHAs | Teams wanting a clean, purpose-built bot-defense layer |
This isn’t about one tool being universally “better.” For some products, the real issue is not challenge design at all — it’s privacy, user experience, and how quickly you can adapt to new abuse patterns.
If you are evaluating a vendor, ask practical questions:
- Does it support server-side verification?
- Can it be used across web and mobile?
- How much user data is required to validate a challenge?
- What happens if the provider is slow or unavailable?
- How difficult is it to rotate keys and enforce abuse thresholds?
CaptchaLa is one example of a managed approach that keeps the integration surface narrow while supporting multiple clients and server-side validation. It also offers 8 UI languages and native SDKs for Web (JS, Vue, React), iOS, Android, Flutter, and Electron, which matters if you are protecting both browser and app traffic.
Technical factors that matter more than marketing
If you are choosing between an open-source implementation and a hosted service, the details matter. A security layer should fit into your existing auth and fraud pipeline, not fight it.
1) Validate server-side, always
Challenge completion should be verified on the backend, not trusted from the client alone. A typical server flow looks like this:
1. User completes challenge in the client
2. Client sends pass_token to your backend
3. Backend calls the validation API
4. Backend accepts or rejects the actionWith CaptchaLa, validation is performed with a POST request to:
https://apiv1.captcha.la/v1/validate
The request body includes:
pass_tokenclient_ip
And the request uses:
X-App-KeyX-App-Secret
That pattern is important because it keeps secret material off the browser and lets you make the trust decision where it belongs: on your server.
2) Prefer first-party data
Many teams now care more about data minimization than they did a few years ago. That’s another reason a captcha alternative open source is attractive: fewer external trackers, fewer opaque data flows. If privacy is central to your decision, first-party collection should be part of the evaluation from day one.
Managed platforms can still be privacy-conscious, but the question is whether they rely on broad telemetry or can operate with narrow verification signals. CaptchaLa’s published positioning is first-party data only, which can simplify compliance conversations.
3) Plan for multiple platforms
If your app is web-only, a simple client widget may be enough. But if you ship mobile, desktop, and embedded apps, you want one verification model across surfaces.
CaptchaLa’s client support includes:
- Web JS, Vue, React
- iOS and Android
- Flutter and Electron
For native Android and mobile cross-platform work, the package ecosystem is also practical:
- Maven:
la.captcha:captchala:1.0.2 - CocoaPods:
Captchala 1.0.2 - pub.dev:
captchala 1.3.2
That sort of consistency can reduce integration drift across product teams.
When an open-source route is a good idea
Open source is a strong choice when you have one or more of the following:
- Strict hosting requirements — regulated environments, air-gapped systems, or internal-only deployments.
- A dedicated security team — people who can tune thresholds, review telemetry, and patch logic quickly.
- Very specific UX needs — custom challenge behavior or deep application integration.
- Long-term platform ownership — you want to control the full lifecycle, not just the front-end widget.
It’s worth being realistic, though. Even a solid open-source CAPTCHA component still needs:
- challenge generation
- state management
- server verification
- rate limiting
- abuse monitoring
- bot adaptation over time
If any of those are under-resourced, the “free” option can become expensive in engineering time.
For teams that want a middle path, CaptchaLa’s server-side interfaces are simple enough to slot into existing auth flows. For example, issuing a server token can be done via:
POST https://apiv1.captcha.la/v1/server/challenge/issue
And for implementation details, the docs are the best place to confirm request formats and SDK behavior.
A practical selection framework
Here’s a simple way to decide.
Choose open source/self-hosted if:
- you need full source-level control
- your policy prefers internal hosting
- you can operate the service reliably
- you want to avoid third-party challenge dependencies
Choose a managed platform if:
- you want to ship faster
- you need both web and app coverage
- you want a cleaner validation API
- you’d rather spend time on product logic than bot-infra upkeep
Choose an edge-native tool if:
- your traffic already sits behind an edge platform
- you want challenge handling to be tightly coupled to CDN/WAF controls
- your team values operational simplicity over portability
A quick integration checklist can help either way:
- Decide whether validation happens after login, signup, or high-risk actions
- Define which signals are passed to the backend
- Store secrets only on the server
- Add fallback behavior for validation outages
- Log challenge failures for abuse analysis
- Re-test after client or SDK upgradesIf you are pricing out the build-vs-buy decision, it can also help to compare expected volume with support and maintenance effort. CaptchaLa’s pricing includes a free tier of 1000 requests per month, with Pro tiers around 50K–200K and Business at 1M, which is useful context when planning traffic growth.

Conclusion: control, privacy, and ops are the real decision
A captcha alternative open source can be a great fit if your team wants maximum control and has the engineering capacity to maintain it. But the choice is not only about source code. It’s about how much operational burden you want to own, how much user data you’re willing to process, and how quickly you need to adapt as abuse patterns change.
For many teams, the sweet spot is a managed platform with strong server-side validation, multi-platform SDKs, and data-minimizing design — enough control to fit your stack, without turning CAPTCHA into another subsystem you have to run.
Where to go next: review the implementation details in the docs or compare tiers on the pricing page.