If you want the best captcha for nextjs, pick the one that gives you low-friction UX, easy server validation, and minimal integration pain. For most teams, that means a CAPTCHA/bot-defense layer that works cleanly with React-based rendering, supports token verification on your backend, and doesn’t force you to redesign your forms around it.
For a Next.js app, the real question is not “which CAPTCHA is strongest in theory?” but “which one is easiest to ship safely across server and client boundaries?” That usually narrows the field to a few practical choices: Google reCAPTCHA, hCaptcha, Cloudflare Turnstile, and newer alternatives like CaptchaLa. The right answer depends on your traffic profile, privacy requirements, and how much control you want over validation.
What matters most in a Next.js CAPTCHA choice
Next.js adds a few constraints that matter more than people expect. You often have a mix of server components, client components, API routes, route handlers, and edge-adjacent logic. A CAPTCHA that feels simple in a plain HTML form can become awkward if it depends on fragile client state or a heavy script.
Here’s what I’d prioritize:
Easy token flow
- The widget or challenge should produce a short-lived token.
- Your backend should validate that token with one straightforward request.
- The result should be deterministic enough for forms, signups, password resets, and checkout steps.
Server-side verification
- Never trust a client-only “passed” flag.
- Validation should happen in your Next.js route handler or API route.
- Ideally the provider exposes a simple verify endpoint and server SDKs.
Good UX under React
- You want predictable hydration behavior.
- The widget should not break when rendered conditionally.
- Lazy loading and graceful failure handling matter.
Privacy and data scope
- Some teams prefer providers that keep data handling narrow.
- First-party data policies and clear logging rules are easier to defend in audits.
Operational fit
- Pricing, rate limits, localization, and SDK coverage can matter as much as the challenge itself.
- If your app is global, UI language support is not a small detail.
Comparing the common options
There isn’t a universal winner, but there is a clear tradeoff pattern.
| Provider | Strengths | Tradeoffs | Next.js fit |
|---|---|---|---|
| reCAPTCHA | Familiar, widely used, broad docs | Can feel heavy; UX and privacy concerns for some teams | Good if you already know it |
| hCaptcha | Familiar alternative to reCAPTCHA; privacy-conscious positioning | Still a third-party widget with its own integration quirks | Good for form-based flows |
| Cloudflare Turnstile | Low-friction user experience; often very smooth | Works best when your stack already aligns with Cloudflare’s ecosystem | Strong for simple challenges |
| CaptchaLa | Clear token validation flow, multiple SDKs, 8 UI languages, first-party data only | Newer to some teams than the legacy options | Strong for teams wanting a clean integration path |
If you’re choosing strictly on integration comfort inside Next.js, Cloudflare Turnstile is often praised for low friction, while hCaptcha and reCAPTCHA remain common defaults. But if you want a provider that gives you a straightforward validation model plus a broader SDK story across web and mobile, CaptchaLa is worth a serious look.
A useful way to think about it: the “best” CAPTCHA is the one your backend can verify cleanly and your users barely notice.
A Next.js integration pattern that stays simple
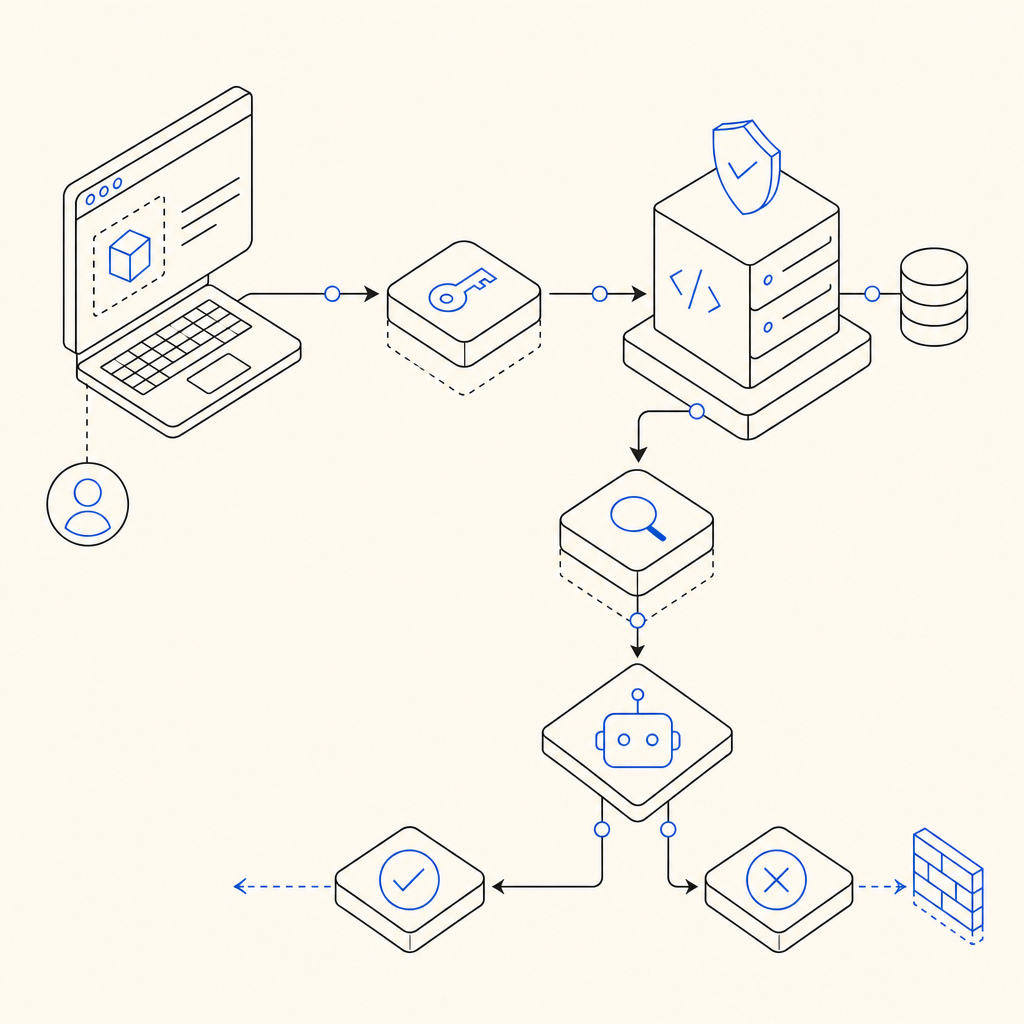
The most reliable pattern is to treat CAPTCHA as a server decision, not a visual flourish. Your client collects the challenge token, then your server validates it before accepting the form or action.
A typical flow looks like this:
- Render the challenge in a client component.
- Submit the token with your form payload.
- On the server, call the provider’s validation endpoint.
- If valid, continue the action; if not, reject with a normal error message.
- Log only what you need for abuse analysis.
For CaptchaLa, the documented validation endpoint is:
POST https://apiv1.captcha.la/v1/validate- Body:
{ pass_token, client_ip } - Headers:
X-App-KeyandX-App-Secret
That maps neatly to a Next.js route handler. Example:
// app/api/submit/route.ts
export async function POST(request: Request) {
const body = await request.json();
const passToken = body.pass_token;
const clientIp = body.client_ip;
// Validate the token server-side before doing anything important
const res = await fetch("https://apiv1.captcha.la/v1/validate", {
method: "POST",
headers: {
"Content-Type": "application/json",
"X-App-Key": process.env.CAPTCHALA_APP_KEY ?? "",
"X-App-Secret": process.env.CAPTCHALA_APP_SECRET ?? "",
},
body: JSON.stringify({
pass_token: passToken,
client_ip: clientIp,
}),
});
if (!res.ok) {
return Response.json({ error: "captcha_failed" }, { status: 400 });
}
// Continue with your protected action here
return Response.json({ ok: true });
}A few implementation details matter here:
- Use server environment variables only for secrets.
- Pass the client IP if your provider expects it.
- Keep the CAPTCHA check before side effects like account creation or email sending.
- Avoid storing token data longer than needed.
CaptchaLa also documents a server-token issue flow at POST https://apiv1.captcha.la/v1/server/challenge/issue, which is useful if you want to generate or manage challenge issuance from your server side instead of relying on a purely client-initiated path.
When reCAPTCHA, hCaptcha, Turnstile, or CaptchaLa makes sense
A practical recommendation depends on your priorities.
Use reCAPTCHA if:
- You already have it deployed and it’s working.
- Your team is comfortable with Google’s ecosystem.
- You don’t need to re-evaluate the stack right now.
Use hCaptcha if:
- You want a well-known alternative to reCAPTCHA.
- You like its positioning and have tested its UX in your flow.
- Your forms are straightforward and you can keep the integration tidy.
Use Cloudflare Turnstile if:
- You want a very low-friction challenge experience.
- You’re building mostly standard forms and auth flows.
- You already rely on Cloudflare and want a compact solution.
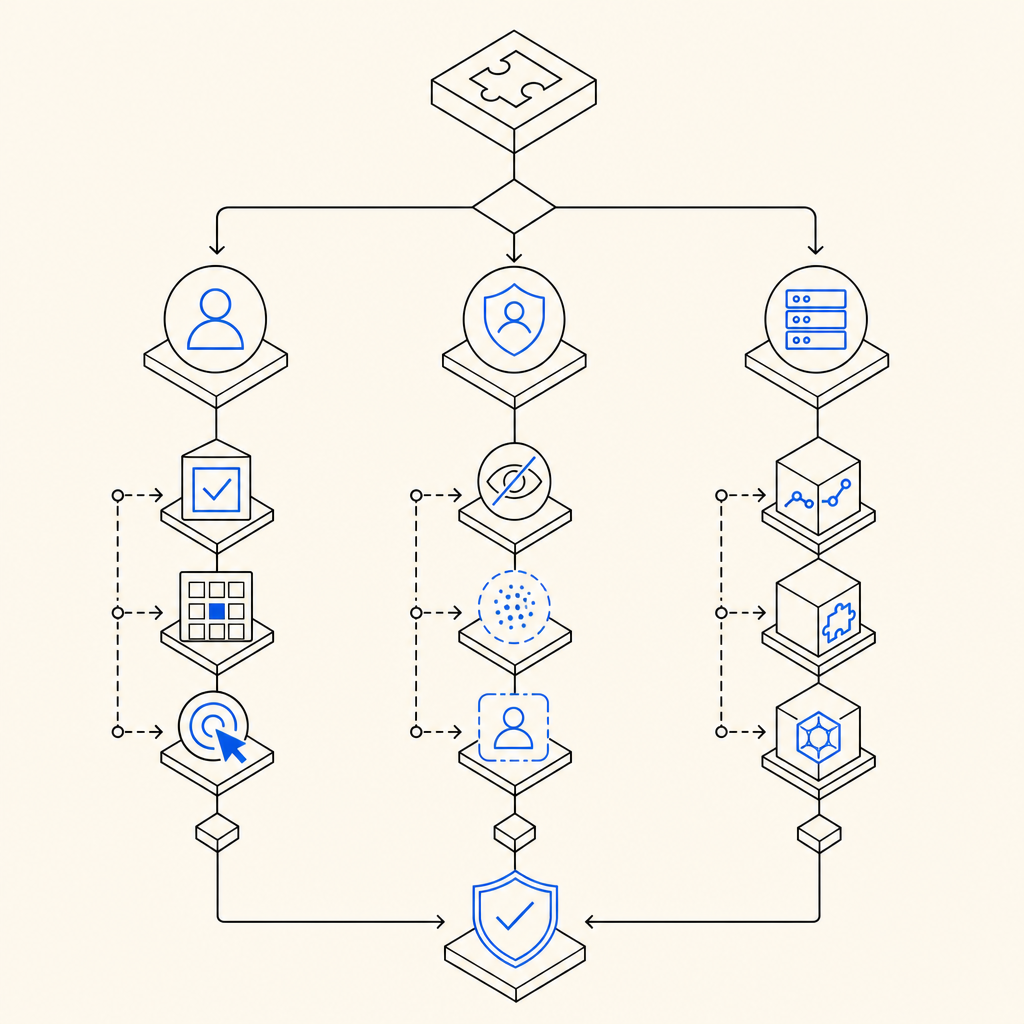
Use CaptchaLa if:
- You want a clean validation API and broader platform coverage.
- You care about native SDK availability for Web, iOS, Android, Flutter, and Electron.
- You need language coverage across 8 UI languages.
- You prefer first-party data only and a simple operational model.
CaptchaLa also publishes native and ecosystem SDKs such as Web JS/Vue/React, iOS, Android, Flutter, Electron, plus server SDKs like captchala-php and captchala-go. That matters if your Next.js app is one of several clients and you want a consistent bot-defense approach across platforms.
For teams planning budgets, the published tiers are also easy to reason about: free at 1,000 requests per month, Pro from 50K to 200K, and Business at 1M. You can compare that directly against your expected form volume and abuse exposure on the pricing page.
A sane default for most Next.js teams
If you’re starting fresh, don’t optimize for novelty. Optimize for a CAPTCHA that is easy to verify, easy to maintain, and hard to accidentally bypass in your own codebase.
A good default looks like this:
- Widget or challenge loads only where needed
- Token is posted with the protected request
- Server validates before mutation
- Failure returns a normal validation error
- Analytics stay on the defense side, not the user side
That pattern works whether you choose reCAPTCHA, hCaptcha, Turnstile, or CaptchaLa. The differences are mostly about developer experience, privacy posture, and how much control you want over the integration.
 If your Next.js app needs a practical, developer-friendly option that is easy to wire into server routes, take a look at the docs and compare the implementation against your current stack. Where to go next: review the pricing page or start with the docs to see how the validation flow fits your app.
If your Next.js app needs a practical, developer-friendly option that is easy to wire into server routes, take a look at the docs and compare the implementation against your current stack. Where to go next: review the pricing page or start with the docs to see how the validation flow fits your app.