An anti afk bot is a system that detects and blocks automated inactivity farming, session abuse, or “stay-online” automation before it can distort analytics, consume resources, or unlock rewards. If you run an app with rewards, live presence, matchmaking, queues, or timed access, the real question is not whether bots will try to fake activity — it’s how reliably you can tell genuine engagement from scripted keep-alive behavior.
That distinction matters because AFK abuse is usually subtle. It may look like a user who is “present” but never interacts, or a script that taps, moves, or pings just enough to avoid simple idle timers. A practical anti afk bot strategy looks at behavior over time, not just one event. It combines challenge responses, client signals, session patterns, and server-side validation to decide when a session is legitimate.
What an anti afk bot actually defends against
AFK abuse usually shows up where “activity” has value. Common examples include:
- Reward loops that grant points for staying connected
- Queue systems that depend on active presence
- Multiplayer lobbies where idle accounts affect matchmaking
- Referral, watch-time, or ad exposure fraud
- Free-tier abuse where long-lived sessions consume backend resources
The defender’s job is not to punish every quiet user. Many legitimate users read, watch, or pause. Instead, the goal is to detect when a session’s behavior is mechanically consistent with automation. That means looking for patterns such as:
- Repeated input at fixed intervals
- Unrealistically stable pointer movement
- Long sessions with zero meaningful state changes
- Challenge tokens reused across IPs or sessions
- Device/browser fingerprints that don’t line up with the claimed environment
A good anti afk bot layer doesn’t need to “know” whether a user is at their keyboard. It only needs enough confidence to say, “This session is not behaving like a human-driven one.”
Detection signals that matter more than idle time
Idle time alone is too blunt. A user can be inactive and still legitimate. A bot can also simulate activity and look “awake.” That’s why useful defenses combine multiple signals.
1) Client-side behavior
The browser or app can observe high-level interaction patterns:
- Scroll cadence
- Focus and blur events
- Visibility changes
- Tap or click clustering
- Movement entropy over time
These signals are best treated as hints, not proof. A determined script can mimic some behavior, but it usually struggles to imitate natural variation across a long session.
2) Challenge-based verification
When a session crosses a risk threshold, issue a challenge and validate the response server-side. With CaptchaLa, the flow is designed around a token that your backend verifies by calling POST https://apiv1.captcha.la/v1/validate with pass_token and client_ip, authenticated using X-App-Key and X-App-Secret. This keeps trust decisions on your server rather than in the browser.
3) Session and network consistency
AFK abuse often exposes itself in the gaps between claimed behavior and actual transport context:
- IP churn during a single reward session
- Tokens reused in unexpected locations
- Very long “online” periods without state transitions
- Repeated validations at nearly identical intervals
That’s where a risk engine beats a single binary timer. A five-minute inactive session may be normal; a seven-hour “active” session with no entropy often isn’t.
A practical defense architecture
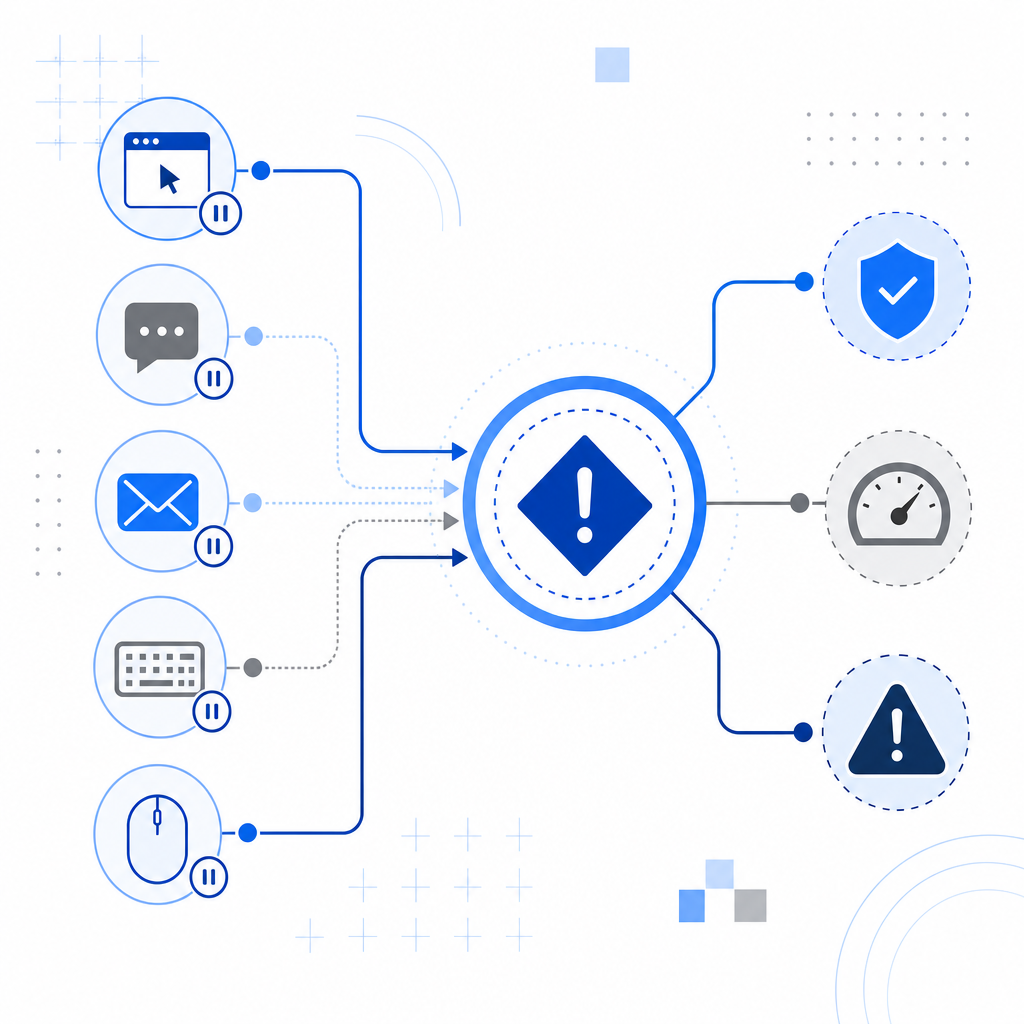
A clean anti afk bot setup usually has three layers: observe, challenge, and enforce.
1. Observe session behavior
- Collect lightweight client signals
- Track timing, focus, and interaction cadence
- Score risk server-side
2. Challenge when needed
- Serve a challenge only when risk is elevated
- Issue server tokens from backend if needed:
POST https://apiv1.captcha.la/v1/server/challenge/issue
3. Validate before granting value
- Verify pass_token + client_ip on your server
- Apply reward, access, or queue priority only after success
- Log outcomes for tuning and auditThat structure keeps friction low for normal users and raises the cost of scripted activity. It also makes tuning easier. If you’re seeing too many false positives, you can relax thresholds. If AFK abuse keeps slipping through, you can increase challenge frequency or tighten enforcement around high-value actions.
Where CAPTCHA fits
CAPTCHA should not be your only line of defense, but it is a useful checkpoint when behavior becomes suspicious. CaptchaLa supports native SDKs for Web (JS, Vue, React), iOS, Android, Flutter, and Electron, plus server SDKs like captchala-php and captchala-go. It also offers 8 UI languages, which matters if your audience is global and you want a consistent challenge experience.
If your stack already uses reCAPTCHA, hCaptcha, or Cloudflare Turnstile, the comparison is usually about operational fit rather than ideology. Each can help block automation. The main questions are:
| Product | Typical strength | Practical tradeoff |
|---|---|---|
| reCAPTCHA | Broad familiarity and ecosystem support | Can add friction depending on risk settings |
| hCaptcha | Strong bot filtering and configurable challenge flows | UX and integration decisions vary by site |
| Cloudflare Turnstile | Low-friction experience for many users | Best fit often depends on Cloudflare usage |
| CaptchaLa | Flexible bot-defense flow with server-side validation | You still need good risk logic on your side |
The point is not to pick a “winner” in abstract. It’s to match the tool to the abuse pattern and your tolerance for user friction.
Implementation details that reduce AFK abuse without annoying users
A robust anti afk bot system gets more accurate when it is specific. Here are the details that tend to matter most:
Trigger challenges on risk, not on a schedule
Don’t challenge every user every N minutes. Use behavioral thresholds, suspicious events, or privilege changes.Tie tokens to the session context
Validateclient_ipand short-lived pass tokens so one solved challenge can’t be stretched across many sessions.Make high-value actions require freshness
If a reward, queue entry, or entitlement is valuable, require a recent successful validation before granting it.Log decisions for tuning
Keep records of session risk score, challenge outcome, and enforcement action. This helps you distinguish genuine edge cases from abuse.Separate observation from enforcement
Watch quietly first. Only escalate when patterns persist or value at risk justifies it.
For teams that want a simple starting point, CaptchaLa’s loader is served from https://cdn.captcha-cdn.net/captchala-loader.js, and the free tier covers 1,000 validations per month. Pro tiers start around 50K–200K monthly volume, with Business scaling to 1M. That range is useful if you want to test behavior first and expand only after you have a measurable abuse baseline. CaptchaLa’s pricing and docs are straightforward starting points: pricing and docs.
Example policy logic
A defender-side rule set might look like this:
if session.age > 30 minutes and session.interaction_entropy < threshold:
score += 20
if reward_claims_per_hour > normal_band:
score += 30
if IP changed during active session:
score += 25
if score >= 40:
require challenge verificationThis is intentionally simple. Real systems can include device consistency, velocity checks, and reputation data, but the principle stays the same: score the session, then respond proportionally.

What to measure after deployment
Once your anti afk bot controls are live, measure whether they are actually reducing abuse rather than merely increasing friction.
Track:
- Challenge pass rate for normal users
- False positive rate by device and region
- Reward fraud before and after enforcement
- Average session length among flagged users
- Validation failure reasons and token reuse attempts
If your legitimate users are seeing too many challenges, move the challenge point later in the flow or raise the risk threshold. If abuse is still growing, look for patterns in session duration, repeated validations, or suspiciously regular activity timing. The best systems are iterative, not static.
You should also review support tickets and funnel drop-off. A defense that blocks bots but hurts conversions may be too aggressive. On the other hand, a defense that is invisible but ineffective is just decoration.
Where to go next
If you’re building an anti afk bot defense into a product with rewards, presence, or session value, start with server-side validation and a small, measurable challenge policy. The docs cover the integration flow, and pricing can help you size a rollout before you commit to a larger deployment.