If you need Angular bot protection with a familiar checkbox flow, the practical answer is: use a CAPTCHA widget on the client, but always validate the result on your server. That’s the part that actually stops abuse. Whether you’re working with reCAPTCHA v2 or a similar system, the implementation pattern is the same: render the challenge in Angular, collect the token, and verify it before allowing sensitive actions like sign-up, login, password reset, or checkout.
For teams that want a simpler integration path, CaptchaLa follows that same client-plus-server model and keeps the workflow straightforward for Angular and other front ends. It supports 8 UI languages, native SDKs for Web, iOS, Android, Flutter, and Electron, plus server SDKs for PHP and Go. The key is that your app remains in control of the trust decision, not the browser alone.
What Angular reCAPTCHA v2 implementation is really doing
The phrase “angular recaptcha v2” usually refers to the standard checkbox-style CAPTCHA pattern inside an Angular app. The widget is rendered in the browser, the user completes a challenge, and your app receives a short-lived token. That token is only useful if your backend verifies it against the CAPTCHA provider’s validation endpoint.
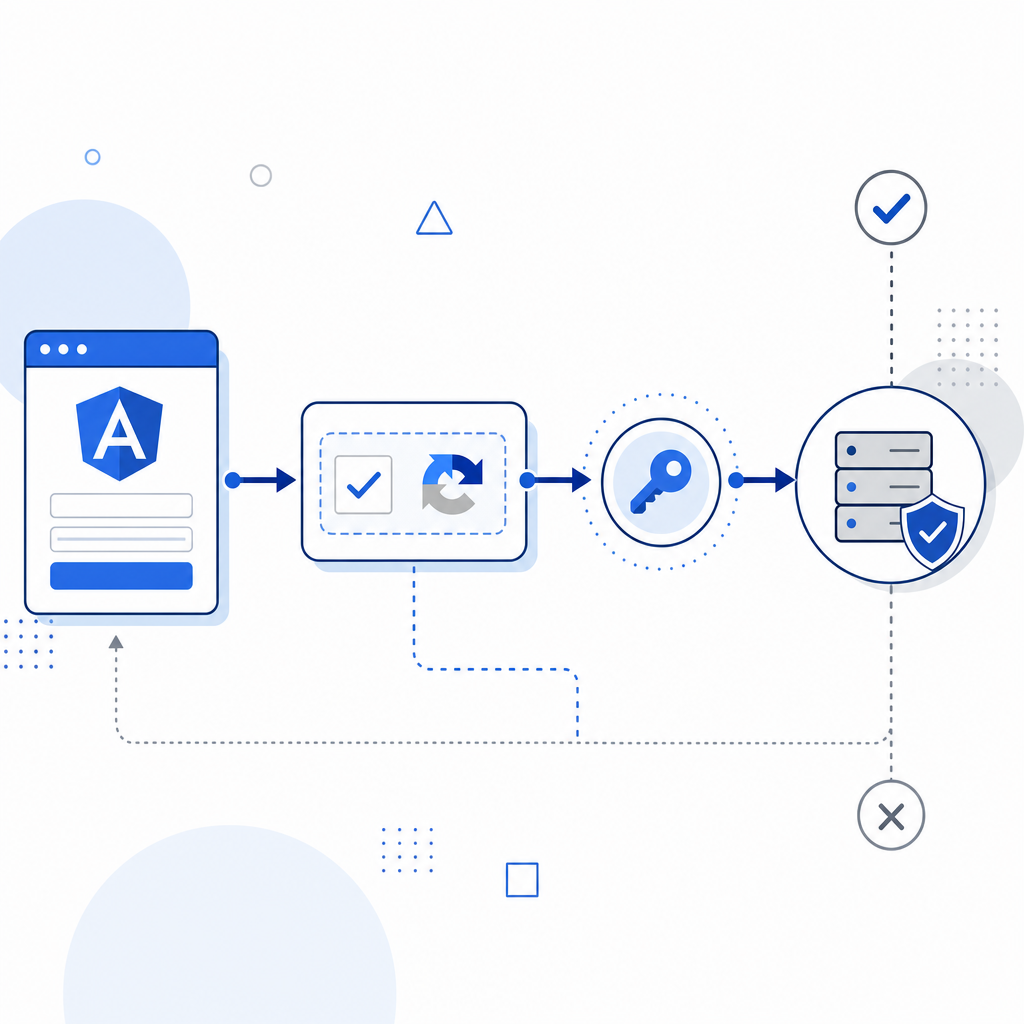
Here’s the practical architecture:
- Angular renders the widget in a component.
- The user completes the challenge and gets a pass token.
- Your Angular code sends that token to your backend with the request it protects.
- Your backend checks the token with the provider’s server API.
- Only then does the app proceed with the action.
That server-side step matters because client-side checks can be copied, replayed, or bypassed if they’re treated as the final gate. For most forms, you also want to bind the token to the user’s IP or session context if the provider supports it.
Where it fits in an Angular app
Typical places to place a CAPTCHA in Angular include:
- registration forms
- login endpoints after repeated failures
- password reset requests
- contact forms with spam pressure
- checkout or promo code submission
- API actions exposed through a public UI
For reCAPTCHA v2 specifically, the widget is usually embedded in a dedicated Angular component, and the completion callback is wired into your reactive form or submit handler. That keeps the UI clean and makes it easier to disable submission until a valid token exists.
A practical integration pattern
The good news is that Angular does not require a special CAPTCHA model. The front end just needs to capture a token, and the backend needs to validate it. If you are evaluating reCAPTCHA, hCaptcha, Cloudflare Turnstile, or CaptchaLa, the same general flow applies even if the widget details differ.
Here’s a simple implementation pattern you can adapt.
// Angular component logic
// Render the CAPTCHA widget and store the pass token
passToken: string | null = null;
onCaptchaSolved(token: string) {
// Save token returned by the CAPTCHA widget
this.passToken = token;
}
submitForm() {
if (!this.passToken) {
// Block submission until CAPTCHA is completed
return;
}
// Send form data and pass token to your backend
this.http.post('/api/signup', {
email: this.email,
password: this.password,
pass_token: this.passToken
}).subscribe();
}On the server, validation should happen before any privileged action. CaptchaLa’s validation endpoint is a good example of the pattern:
POST https://apiv1.captcha.la/v1/validate- body:
{ pass_token, client_ip } - headers:
X-App-KeyandX-App-Secret
That means your backend can check both the token and the client IP in one place, which is useful when you’re reducing automation from repeated form abuse. If you need to issue server tokens for challenge flows, there’s also POST https://apiv1.captcha.la/v1/server/challenge/issue.
Server-side validation example
A backend flow should look like this conceptually:
- Receive the form submission.
- Read the token from the request body.
- Validate the token with the CAPTCHA provider.
- Reject the request if validation fails.
- Continue with the business action only after success.
That sequence is what keeps CAPTCHA from becoming decorative. It is also where a lot of integrations go wrong: teams render the widget correctly in Angular, but forget to enforce the result on the server.
Comparing common CAPTCHA options for Angular apps
Different projects have different constraints. Some want minimal friction. Some want internationalization. Some want SDK coverage across mobile and desktop. Others want a cleaner first-party-data posture.
| Provider | Typical client integration | Server validation | Notes |
|---|---|---|---|
| reCAPTCHA v2 | Angular widget embed | Yes | Familiar checkbox flow, widely used |
| hCaptcha | Angular widget embed | Yes | Often chosen for privacy and flexibility |
| Cloudflare Turnstile | Lightweight widget | Yes | Designed to reduce friction for users |
| CaptchaLa | Web SDK plus native SDKs | Yes | Supports 8 UI languages and first-party data only |
This is not about declaring a universal winner. It’s about picking the tradeoff that fits your product. If you already rely on Google ecosystem tooling, reCAPTCHA may feel familiar. If you want a lightweight alternative, Turnstile or hCaptcha may be appealing. If you need a broader SDK surface, CaptchaLa offers Web JS/Vue/React, iOS, Android, Flutter, and Electron support, which can be helpful if your Angular app is part of a larger product family.
CaptchaLa also publishes server SDKs for captchala-php and captchala-go, plus package coordinates for mobile builds such as Maven la.captcha:captchala:1.0.2, CocoaPods Captchala 1.0.2, and pub.dev captchala 1.3.2. That can simplify teams that maintain multiple client stacks alongside Angular.
Implementation details that matter in production
A CAPTCHA integration is only as useful as the surrounding controls. If you’re protecting an Angular form, keep these specifics in mind.
Validate every sensitive action server-side.
Never trust a front-end “solved” state by itself.Use short-lived tokens.
A token should be consumed quickly, ideally once.Tie the token to context when possible.
Passingclient_ipduring validation can help detect mismatches.Rate limit the endpoint anyway.
CAPTCHA reduces abuse; rate limits catch what slips through.Log validation failures carefully.
You want enough detail to investigate abuse patterns without storing unnecessary personal data.Test fallback behavior.
Decide what happens if the CAPTCHA provider is unavailable. For example, do you fail closed on login but fail open on newsletter signup? That should be an explicit product decision.Support localization.
If your audience is global, UI language support matters. CaptchaLa includes 8 UI languages, which can reduce confusion in multilingual flows.

A note on UX, accessibility, and friction
The best CAPTCHA is the one users can complete without feeling blocked. That’s why the design of the challenge matters as much as the security model. Checkbox-style flows such as reCAPTCHA v2 are familiar, but they can still frustrate users on slow networks, high-latency devices, or assistive technologies.
A few practical suggestions:
- Place the widget near the submit button, not far above it.
- Disable submit until the challenge is complete, but show a clear reason.
- Provide accessible labels and error messaging around the widget container.
- Avoid stacking multiple friction points on the same form unless the risk is genuinely high.
- Use adaptive enforcement: a newsletter form may not need the same level of friction as account recovery.
That balance is one reason some teams evaluate alternatives alongside reCAPTCHA v2. Cloudflare Turnstile often comes up in low-friction discussions, while hCaptcha can be attractive when you want a familiar challenge model with different operational tradeoffs. The important part is not the brand name; it’s whether the chosen system fits your abuse profile and your user journey.
If you’re building on Angular and want a clean implementation with documented server validation and multiple SDK options, docs can help you map the flow quickly. For planning volume and environment fit, pricing is also straightforward to review.
Where to go next
If you’re adding Angular CAPTCHA protection for the first time, start with one form, validate tokens on the server, and confirm the user experience before rolling it out broadly. If you want a provider that supports web and native stacks while keeping the integration pattern simple, take a look at CaptchaLa and the implementation details in the docs.