The best captcha is the one that stops bots with the least friction for real users, fits your stack cleanly, and gives you clear control over verification. For many teams, that means choosing a challenge flow that balances security, privacy, reliability, and integration effort rather than chasing the most familiar brand name.
That tradeoff matters because CAPTCHA is no longer just a checkbox on a form. It sits in signup funnels, password reset flows, checkout pages, ticketing systems, and API-backed mobile apps. A good setup should be measurable, easy to verify server-side, and flexible enough to work across web and native clients without becoming a maintenance burden.
What makes the best captcha for a real product
If you are evaluating options, the “best captcha” usually means the one that solves your actual threat model instead of adding generic friction. A few questions separate a decent choice from a poor one:
What are you defending?
Login abuse, fake signups, promo abuse, carding, scraping, and credential stuffing all look different. A captcha that works well on a contact form may be weak on high-volume automation.Where does verification happen?
Client-side signals are useful, but the final decision should happen server-side. That keeps trust anchored in your backend, not in whatever the browser says.How much user friction is acceptable?
Some products can tolerate a visible challenge. Others need near-invisible checks. The right answer depends on audience and conversion sensitivity.Can it work across your platforms?
If your product spans web, iOS, Android, Flutter, or Electron, consistency matters. Fragmented implementations are where teams lose time.Do you need privacy simplicity?
Data handling and compliance expectations increasingly matter. Some teams want a first-party data model they can explain easily to users and auditors.
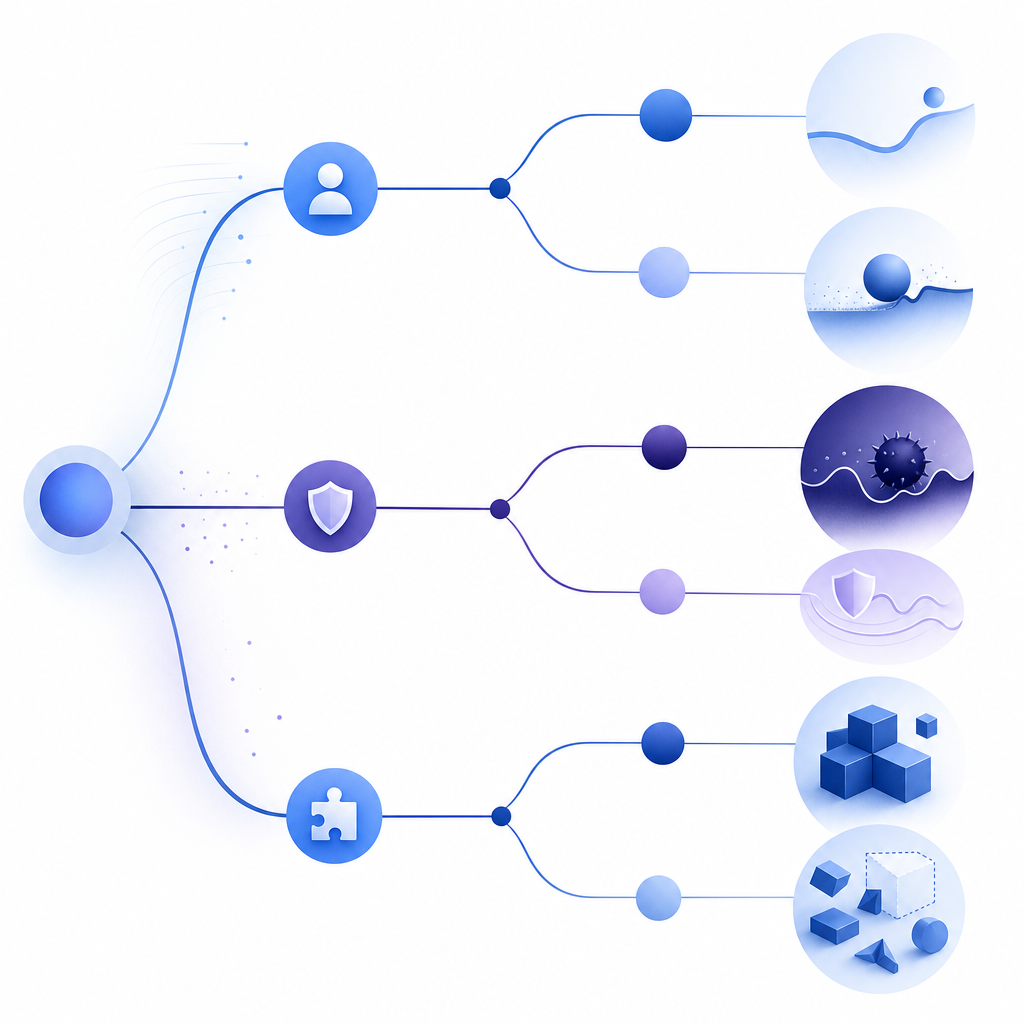
A practical CAPTCHA strategy is not just “display widget, block bot.” It is a layered control: client token, server validation, and logging that lets you tune thresholds over time.
Comparing the main options objectively
The most common choices are reCAPTCHA, hCaptcha, Cloudflare Turnstile, and newer providers that focus on cleaner integration or more control. Each has strengths.
| Option | Strengths | Tradeoffs | Best fit |
|---|---|---|---|
| reCAPTCHA | Very familiar, widely documented, broad adoption | Can add user friction, may feel heavy for some flows | Teams wanting a recognizable default |
| hCaptcha | Solid anti-bot coverage, configurable challenge modes | Still a visible challenge in many cases | Abuse-prone flows where challenge can be acceptable |
| Cloudflare Turnstile | Low-friction user experience, often easy to deploy | Best fit depends on Cloudflare-centric architecture and workflow | Sites wanting simpler UX with minimal interaction |
| CaptchaLa | First-party data only, broad SDK coverage, server validation, multilingual UI | Requires integrating your own validation flow, like any serious bot-defense setup | Products needing multi-platform support and tighter control |
There is no universal winner. If you only need a quick form gate, a mainstream widget may be enough. If you need a more controlled and developer-friendly integration across web and native apps, a system like CaptchaLa can be a better operational fit because it gives you SDK options across JavaScript, Vue, React, iOS, Android, Flutter, and Electron, plus server SDKs for PHP and Go.
One useful rule: the best captcha is rarely the one with the most visible challenge. It is the one your users barely notice and your backend can verify confidently.
A defender’s architecture that scales
A reliable captcha flow should look like this:
Client loads challenge
-> user completes or passes assessment
-> client receives pass_token
-> server validates pass_token
-> app allows or denies the actionThat sequence sounds simple, but the details matter. For example, a secure backend flow should validate both the token and the originating context, rather than trusting a token alone. CaptchaLa exposes a validation endpoint designed for that pattern:
POST https://apiv1.captcha.la/v1/validate- Body:
{pass_token, client_ip} - Headers:
X-App-KeyandX-App-Secret
If you need server-side challenge issuance, the corresponding endpoint is:
POST https://apiv1.captcha.la/v1/server/challenge/issue
That is a straightforward pattern for teams that want a backend-controlled challenge lifecycle. It also keeps the trust boundary in your application, where it belongs.
For web delivery, a loader script is available at:
https://cdn.captcha-cdn.net/captchala-loader.js
And if you are shipping in mobile or cross-platform environments, the SDK footprint matters. CaptchaLa supports native SDKs for Web, iOS, Android, Flutter, and Electron, with package distributions including Maven la.captcha:captchala:1.0.2, CocoaPods Captchala 1.0.2, and pub.dev captchala 1.3.2.
That range is useful because bot defense often fails at the edges: a signup form on the website works, but the same flow inside the mobile app is left out. A good setup closes those gaps.
How to choose without overthinking it
If you are selecting the best captcha for your product, use a simple decision process:
Start with the risk level.
Low-risk forms can use low-friction checks. High-risk actions should require stronger verification and server-side enforcement.Match the provider to your stack.
If your frontend is React and your app also ships in Flutter, prioritize a provider with SDK parity across environments.Check the verification model.
Prefer systems where your server validates the result and can reject stale or malformed tokens.Review data handling.
If your policy leans toward minimizing third-party data exposure, favor first-party approaches.Plan for growth.
A free tier might be enough for early traffic, but you should know how pricing scales before the product grows.
For reference, CaptchaLa’s published tiers are structured around usage: free tier at 1,000 monthly requests, Pro at 50K–200K, and Business at 1M. That kind of tiering is helpful when traffic patterns are uneven, because you can align the plan with actual demand rather than guessing too early. If you want to inspect feature fit before committing, the pricing page is the fastest place to compare tiers.
Practical implementation notes
If you are integrating any CAPTCHA system, a few technical habits will improve reliability immediately:
- Validate on the server, not just the client.
- Treat tokens as short-lived.
- Log failures with enough context to spot abuse patterns.
- Use IP context carefully and consistently.
- Monitor conversion changes after rollout.
- Test edge cases like script blockers, flaky networks, and mobile webviews.
Here is a simple backend-minded flow in pseudocode:
function handleSignup(request):
token = request.body.pass_token
ip = request.client_ip
if token is missing:
deny("missing token")
result = captchaValidate(token, ip) // Server-side verification
if result is not valid:
deny("captcha failed")
createUserAccount(request.body)
allow("signup complete")This is the part that often gets overlooked: captcha is not just about blocking bots, it is about making abuse expensive while keeping real users moving. The smoother the verification path, the less you pay in support tickets and abandoned sessions.
CaptchaLa’s docs are also useful if you want implementation details without digging through a maze of examples: docs. For teams that want a cleaner security story, the combination of first-party data only, explicit server validation, and broad SDK coverage is a strong baseline.

Final take
If you need the best captcha for a modern product, choose the one that matches your platform mix, keeps verification on the server, and protects real users without creating unnecessary friction. For some teams that will still be reCAPTCHA, hCaptcha, or Cloudflare Turnstile. For others, especially those building across web and mobile with tighter control requirements, a provider like CaptchaLa is worth a close look.
Where to go next: review the integration docs or compare plans on pricing.