If you need an angular form captcha, the practical answer is: add it at the point where a form becomes expensive to abuse, and validate it server-side before you trust the submission. In Angular, that usually means rendering a lightweight challenge in the form, capturing a pass token, and sending that token with the rest of the payload so your backend can verify it before creating accounts, sending OTPs, or accepting contact requests.
The key idea is simple: the captcha should help your form distinguish real users from automated abuse without turning the experience into a puzzle box. That matters because Angular forms often power the exact endpoints bots love most: signups, password resets, lead forms, checkout steps, and feedback pages. The best integration pattern is one that keeps the UI calm and the security decision on the server.
Why Angular forms need CAPTCHA at the right moment
Angular makes it easy to build rich, reactive forms, which is great for users and also convenient for attackers. A bot does not care whether your form is elegant; it cares whether it can submit 10,000 attempts with low cost. The usual result is spam, credential stuffing, fake signups, disposable email abuse, and inflated analytics.
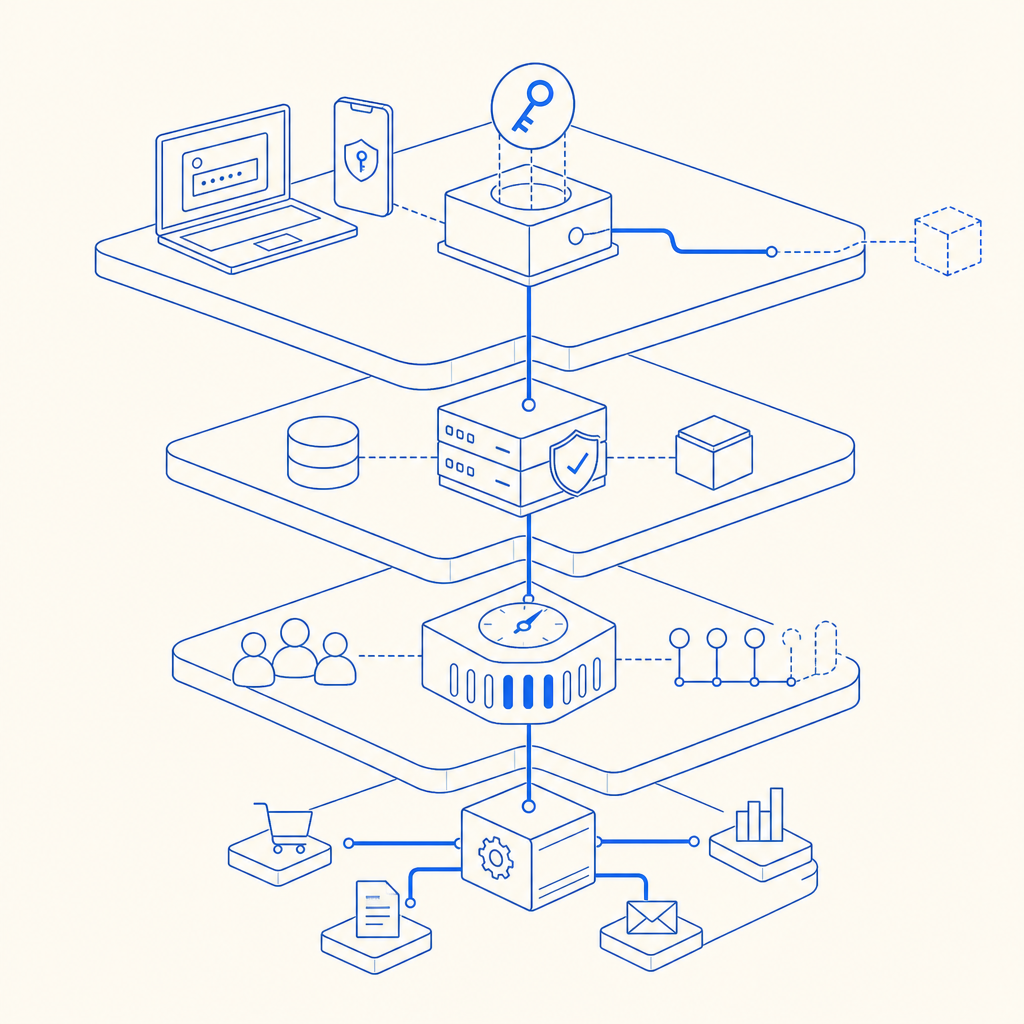
A good angular form captcha is not just a visual widget. It is part of a broader abuse-control strategy. You want it to:
- Trigger when the form is valuable enough to protect.
- Produce a short-lived token tied to the interaction.
- Be checked by your server before the action is accepted.
- Avoid leaking trust decisions to the browser alone.
- Support graceful fallbacks for accessibility and international users.
That last point matters more than people think. If your form is global, a challenge should not assume one language or one device class. CaptchaLa, for example, supports 8 UI languages and native SDKs across Web, iOS, Android, Flutter, and Electron, which helps keep the integration consistent across product surfaces. If your app is primarily web-based, the browser SDK plus a server check is usually enough.
The server-side requirement is not optional. Client-side checks can improve UX, but they are not where you enforce trust. A bot can script the browser, intercept requests, or replay payloads. The real decision belongs on your backend.
Choosing the right CAPTCHA style for an Angular form
There are a few common options, and the right one depends on your risk level, UX goals, and operational constraints.
| Option | UX impact | Implementation | Server verification | Notes |
|---|---|---|---|---|
| reCAPTCHA | Medium | Moderate | Yes | Familiar, widely used, but can feel intrusive depending on mode |
| hCaptcha | Medium | Moderate | Yes | Similar pattern, often chosen for privacy or policy reasons |
| Cloudflare Turnstile | Low | Moderate | Yes | Often very low friction, good for many forms |
| CaptchaLa | Low to medium | Moderate | Yes | Supports first-party data only and multiple SDKs |
For an Angular form captcha, the most important choice is not branding; it is behavior. If your form is a simple newsletter signup, a low-friction solution is usually enough. If it is account creation, password reset, or a high-volume lead form, you may want stronger signals and stricter validation logic.
A practical defender’s lens helps here:
- Use friction-light checks on low-risk forms.
- Escalate for suspicious patterns, repeated attempts, or high-value actions.
- Keep rate limiting, IP reputation, and form validation in the backend.
- Treat the CAPTCHA as one signal, not the whole security stack.
If you are evaluating implementation overhead, the server verification flow is also worth checking before you commit. CaptchaLa exposes a validation endpoint at POST https://apiv1.captcha.la/v1/validate with a body containing pass_token and client_ip, authenticated using X-App-Key and X-App-Secret. That means your Angular app can stay focused on collecting the token, while your server makes the trust decision.
A clean Angular integration pattern
A solid Angular integration is usually built around a small service, a form component, and a backend endpoint that validates the token before processing the submission.
Here is a minimal pattern:
// English comments only
import { Component } from '@angular/core';
import { FormBuilder, Validators } from '@angular/forms';
import { HttpClient } from '@angular/common/http';
@Component({
selector: 'app-signup-form',
templateUrl: './signup-form.component.html'
})
export class SignupFormComponent {
form = this.fb.group({
email: ['', [Validators.required, Validators.email]],
name: ['', Validators.required],
captchaToken: ['']
});
constructor(private fb: FormBuilder, private http: HttpClient) {}
onCaptchaSuccess(token: string) {
// Store the token so it can be submitted with the form
this.form.patchValue({ captchaToken: token });
}
submit() {
if (this.form.invalid) return;
// Send the full payload to your backend
this.http.post('/api/signup', this.form.value).subscribe();
}
}The important architectural detail is that the Angular app should not call the provider’s validation API directly from the browser. Your backend should receive the form data, then validate the token using your secret credentials. That protects the secret and keeps the verification authoritative.
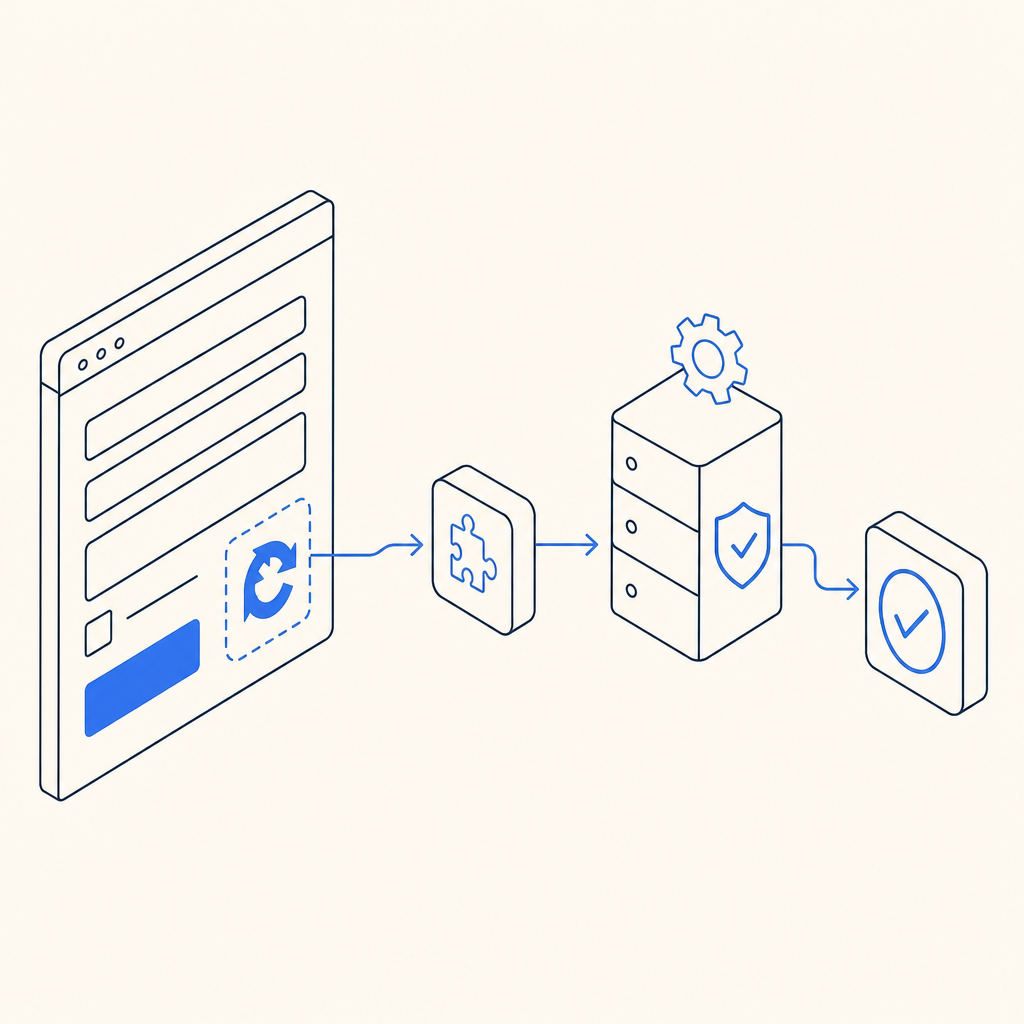
A typical backend flow looks like this:
- Angular submits
{ email, name, captchaToken }to your server. - Your server reads the requester’s IP address.
- Your server sends
pass_tokenandclient_ipto the captcha validation endpoint. - The validation response is checked before any account is created or email is sent.
- If validation fails, the request is rejected and logged.
If you are using CaptchaLa, the loader script is served from https://cdn.captcha-cdn.net/captchala-loader.js. On the server side, CaptchaLa also provides SDKs such as captchala-php and captchala-go, which can reduce the amount of glue code you need to write. There are also platform-specific package options like Maven la.captcha:captchala:1.0.2, CocoaPods Captchala 1.0.2, and pub.dev captchala 1.3.2 for mobile and cross-platform builds.
What to validate beyond the token
A token check is necessary, but it should not be your only control. For a more resilient form, validate:
- token freshness
- IP consistency where appropriate
- request rate over time
- email domain quality for signup flows
- duplicate submissions
- user-agent anomalies
- failed attempts per session
This layered approach matters because bots often rotate inputs faster than humans can notice. A captcha alone is a speed bump; combined with rate limits and sane backend rules, it becomes much more effective.
Operational tradeoffs: UX, privacy, and scale
If you are choosing an angular form captcha for production, operational details matter just as much as the widget itself.
Privacy is a good example. Some teams prefer first-party data only because it simplifies compliance reviews and reduces dependency concerns. CaptchaLa’s product positioning around first-party data only may matter if your legal or security team is strict about data handling. For teams that want a predictable cost model, the available plans are also straightforward: free tier at 1000/month, Pro at 50K-200K, and Business at 1M. You can compare those against your actual submission volume on pricing.
Scale is another consideration. If a form receives only a few hundred submissions a month, a simpler deployment is fine. If it sits on a high-traffic landing page, even a small amount of friction can affect conversions. That is why low-friction options like Cloudflare Turnstile are often considered alongside reCAPTCHA and hCaptcha. The right answer is usually not “the most aggressive defense”; it is “the defense that preserves legitimate completion rates while blocking automated abuse.”
For Angular specifically, two integration habits are worth keeping:
- Render the challenge only when needed, not on every page load.
- Make the form submission resilient if the captcha widget fails to load, especially on poor networks.
The first habit reduces unnecessary noise. The second avoids turning a temporary asset issue into a broken conversion path.
Putting it all together
The safest angular form captcha setup is a small, boring pipeline: Angular collects the token, your server validates it, and your backend decides whether the submission is allowed. That keeps trust on the server, keeps secrets out of the browser, and gives you room to add more controls later if abuse increases.
If you are implementing this now, start with one form that is frequently abused, wire in token capture, and validate it server-side before expanding to the rest of the app. If you want implementation details, the docs are the best next stop. If you want to test fit for your traffic, check CaptchaLa and compare it with your current signup or lead flow.
Where to go next: review the docs for integration steps, or look at pricing if you are planning for a specific submission volume.