If you’re looking for an amazon captcha service, the short answer is: AWS does not offer a single, native CAPTCHA product that you can drop in and call “Amazon CAPTCHA.” Most teams that need CAPTCHA or bot defense on AWS pair their app with a third-party CAPTCHA provider and keep the deployment, logging, and validation logic in their own stack. That usually means putting the widget or challenge on the client, sending a pass token to your backend, and verifying it server-side before you allow signup, login, checkout, or scraping-prone actions.
The practical question is less “Does Amazon sell CAPTCHA?” and more “What should I use if my app runs on AWS?” That depends on your threat model, required platforms, and how much friction you can tolerate. For many teams, the answer is a provider with lightweight integration, solid SDK coverage, and a validation API that fits neatly into existing services.
What people usually mean by “Amazon CAPTCHA service”
When people search for an amazon captcha service, they’re often trying to solve one of four problems:
- Stop automated account creation on an AWS-hosted web app.
- Protect a public API or form that’s being abused.
- Add a challenge step to a login, signup, or password reset flow.
- Keep bot traffic from inflating costs on infrastructure running in AWS.
AWS gives you infrastructure, identity, edge services, and security tooling, but CAPTCHA itself is typically delivered by a specialist provider. That is a feature, not a flaw: it lets you choose the challenge style, analytics, and SDKs that match your product instead of forcing your app into a single opinionated flow.
If you already have CloudFront, ALB, or Lambda in the picture, CAPTCHA can still fit cleanly. The pattern is the same regardless of where your code runs: render the challenge on the client, receive a pass token, then validate it on the server before doing anything sensitive.
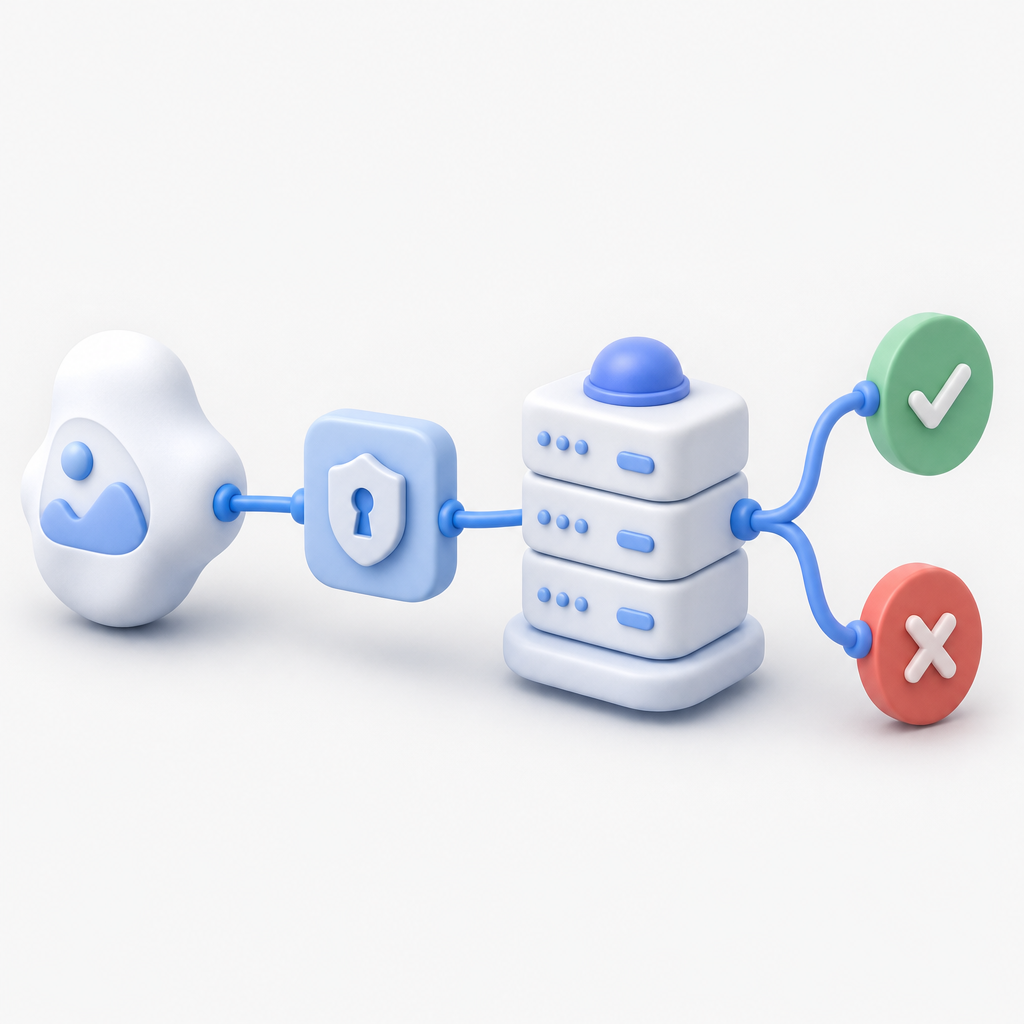
What a sane integration looks like
A basic implementation usually has four moving parts:
- Client widget or challenge loader
- Pass token returned to the browser or app
- Backend validation call
- Decision logic to accept, reject, or step up the request
That pattern works whether your frontend is React, Vue, plain JS, iOS, Android, Flutter, or Electron. It also works if your backend is PHP, Go, or another stack you already run on AWS.
How to evaluate a CAPTCHA provider for AWS-hosted apps
Not every provider is equally easy to wire into a cloud stack. If you want to avoid future pain, compare options on integration depth rather than marketing claims. Here’s a practical lens:
| Criteria | Why it matters | What to check |
|---|---|---|
| Client SDK coverage | Faster rollout across web and mobile | Web, iOS, Android, Flutter, Electron |
| Server validation | Prevents token replay and trust issues | Simple POST validation endpoint |
| Deployment fit | Works with your current AWS architecture | No special network hoops, straightforward secrets |
| Localization | Helps with global users | Multiple UI languages |
| Pricing tiering | Matches growth and abuse spikes | Free, Pro, Business tiers |
| Data handling | Affects compliance and privacy reviews | First-party data only |
Some teams default to reCAPTCHA because it’s familiar. Others prefer hCaptcha for a different tradeoff profile. Cloudflare Turnstile is attractive for low-friction flows, especially if you already use Cloudflare. None of these are universally “right”; the best choice depends on your risk tolerance, UX goals, and operational setup.
If you’re evaluating CaptchaLa, the relevant facts are straightforward: it supports 8 UI languages, offers native SDKs for Web (JS/Vue/React), iOS, Android, Flutter, and Electron, plus server SDKs for captchala-php and captchala-go. For teams that want a direct server-side check, validation is a POST to https://apiv1.captcha.la/v1/validate with {pass_token, client_ip} and X-App-Key / X-App-Secret.
The AWS-friendly integration pattern
The cleanest way to think about CAPTCHA in an AWS environment is to keep trust decisions on the server. The browser or mobile app can collect the token, but your backend should decide whether that token is valid. That keeps your security boundary where it belongs.
A typical flow:
- Render the CAPTCHA loader in the client.
- User completes the challenge.
- Client receives a
pass_token. - Client submits form data plus
pass_tokento your backend. - Backend calls the validation endpoint.
- Backend continues only if validation succeeds.
Here’s what that can look like in pseudocode:
// Client-side flow
loadCaptcha("https://cdn.captcha-cdn.net/captchala-loader.js")
onChallengeComplete(pass_token):
sendToBackend({
email: userEmail,
pass_token: pass_token
})
// Server-side flow
POST /v1/validate
Body: { pass_token, client_ip }
Headers: X-App-Key, X-App-Secret
if validation == true:
allowSignup()
else:
rejectRequest()A few implementation details matter a lot in production:
- Bind validation to the user’s IP when appropriate. That’s why the validation body includes
client_ip. - Keep secrets server-side only. Never ship
X-App-Secretto the client. - Treat the pass token as short-lived. Validate it immediately, not later in a background job.
- Log validation outcomes, not raw secrets. You want observability without leaking sensitive material.
- Use step-up challenges selectively. Don’t force every request through the same friction layer.
If your stack prefers a server-issued challenge token, there’s also POST https://apiv1.captcha.la/v1/server/challenge/issue, which can be useful when your backend needs to initiate the challenge lifecycle more explicitly.
Where the loader fits
The client loader is served from https://cdn.captcha-cdn.net/captchala-loader.js. In a web app, that makes integration similar to other third-party assets: include the script, initialize the widget, and handle the completion callback. For mobile and desktop apps, native SDKs remove a lot of glue code and help keep the user experience consistent.
Choosing between CAPTCHA and adjacent bot defenses
CAPTCHA is one layer, not the entire defense strategy. On AWS, a good setup often combines multiple controls:
- Rate limiting at the edge or application layer
- Behavioral checks for impossible interaction patterns
- Email and phone verification for risky onboarding
- Device or session reputation checks
- Abuse monitoring in logs and metrics
That’s important because some traffic should be blocked before a challenge is even shown, while other traffic should be challenged only after risk rises. If you make every visitor solve a puzzle, you’ll frustrate legitimate users. If you never challenge anyone, bots will eventually find the weak spots.
For smaller teams, starting with a straightforward provider can be enough. CaptchaLa’s free tier covers 1,000 validations per month, which is useful for staging or low-volume products, while Pro and Business tiers are aimed at higher usage ranges like 50K-200K and 1M. The main thing is to align cost with actual abuse exposure instead of guessing.
For implementation details, docs are the place to confirm platform setup, and pricing helps if you’re estimating monthly volume.
A practical recommendation
If your app runs on AWS and you need an “Amazon CAPTCHA service,” don’t wait for a single AWS-branded answer. Pick a provider that fits your platforms, verify tokens server-side, and keep the deployment model simple. That approach scales from a single signup form to a broader anti-abuse program without forcing a rewrite later.
If you already know your frontend and backend stack, the decision becomes much easier: check SDK coverage, confirm the validation path, and make sure the provider handles the languages and devices you actually ship.
Where to go next: review the integration guide in the docs or compare plans on pricing.