Amasty Invisible Captcha can work with Hyvä, but it is not always a drop-in experience. The key question is less “does it install?” and more “does it load, render, and validate cleanly inside a modern Hyvä storefront without breaking checkout or forms?” If you’re running Magento with Hyvä, you should test the extension’s frontend hooks, script loading, and server-side verification before assuming parity with Luma.
Hyvä changes the frontend assumptions that many older Magento extensions rely on. That matters for invisible CAPTCHA because the protection is usually tied to JavaScript bootstrapping, form submission events, and backend validation. If any of those steps are too tightly coupled to legacy Magento UI widgets, you can get inconsistent behavior on contact forms, customer registration, password reset, or checkout flows.
What “invisible captcha” means in a Hyvä storefront
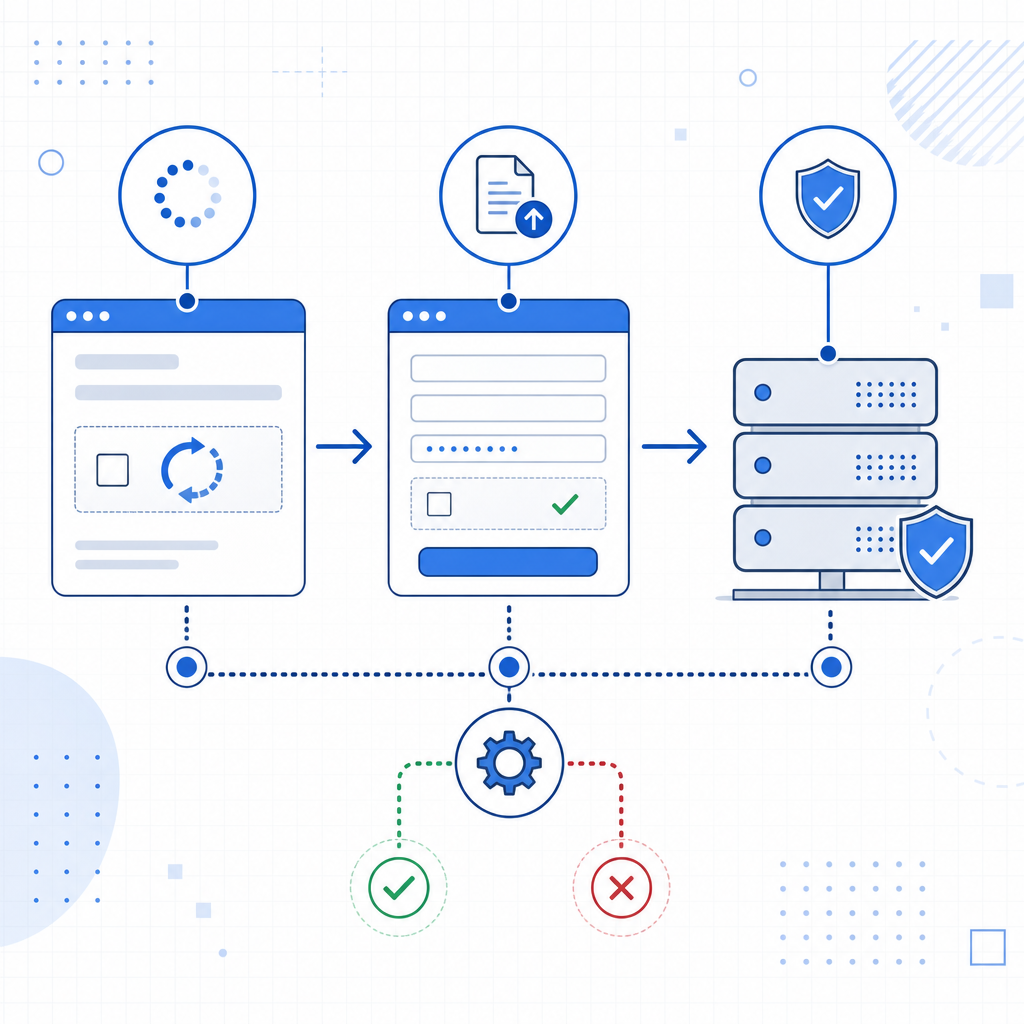
Invisible CAPTCHA is designed to avoid the extra friction of a visible challenge until risk signals justify it. In practice, that means the protection layer usually attaches to a form, initializes a client-side widget or token generator, and then validates a token server-side when the form is submitted.
On Hyvä, this flow has to fit a leaner frontend architecture. That creates three common compatibility checkpoints:
- Script loading: the challenge script must load once, in the right place, without conflicting with Alpine.js behavior or page caching.
- Event binding: submit handlers and token refresh logic need to work with Hyvä’s markup and form patterns.
- Server validation: the backend must verify the token reliably, even when requests come from AJAX, custom controllers, or checkout endpoints.
If any extension says “Hyvä supported,” it is still worth checking whether it means native support, partial compatibility, or support through a compatibility module.
How to evaluate Amasty Invisible Captcha on Hyvä
Before rolling it out site-wide, validate the extension in the exact places where bots tend to probe. Contact forms are usually easy; checkout, account creation, and password reset are where subtle integration issues show up.
A practical review usually looks like this:
Confirm the integration path
- Is it using a Hyvä-specific module, or the same frontend logic as Luma?
- Does it require RequireJS components that Hyvä no longer depends on in the same way?
- Are there documented caveats for custom themes or checkout overrides?
Check form coverage
- guest checkout
- customer registration
- login
- newsletter signup
- contact form
- password reset
Test caching and page re-use
- Make sure the captcha token is not stale after back/forward navigation.
- Confirm that cached pages do not reuse challenge state across users.
- Verify that the widget survives partial reloads if you use them.
Review failure behavior
- What happens when the challenge script is blocked?
- Does the form fail closed or fail open?
- Are there clear error messages for legitimate users?
Inspect server-side trust
- Token validation must happen on the server, not only in the browser.
- Make sure the backend checks the token before accepting the form payload.
A helpful way to think about it: Hyvä compatibility is not only about UI rendering. It is about whether the security signal survives the whole request lifecycle.

Comparison: Amasty Invisible Captcha vs other common options
If you are choosing or re-evaluating CAPTCHA behavior for a Hyvä store, it helps to compare the common approaches objectively.
| Option | Frontend experience | Integration style | Notes for Hyvä |
|---|---|---|---|
| Amasty Invisible Captcha | Usually low-friction | Extension-based | Check whether the module includes Hyvä-friendly frontend handling |
| Google reCAPTCHA | Familiar to many users | Google-hosted verification | Works widely, but privacy and loading considerations matter |
| hCaptcha | Similar challenge model | Third-party verification | Often chosen for alternate risk posture and user experience |
| Cloudflare Turnstile | Lightweight and mostly invisible | Cloudflare-hosted | Good fit for low-friction flows; verify theme compatibility |
For Hyvä specifically, the best choice often comes down to two constraints: how much frontend JavaScript the solution adds, and how much dependence you want on third-party verification services. Some merchants are comfortable with external risk engines; others prefer a smaller surface area and more predictable data handling.
If you need a cleaner integration pattern
Even when an extension works, teams sometimes prefer a simpler implementation path that is easier to reason about in a custom theme. The basic architecture is straightforward: load a lightweight challenge script, capture a pass token, and validate it on the server before trusting the request.
A minimal validation flow looks like this:
<?php
// Validate the captcha token server-side before accepting the form submission.
// 1. Collect the token and client IP from the request.
$passToken = $_POST['pass_token'] ?? '';
$clientIp = $_SERVER['REMOTE_ADDR'] ?? '';
// 2. Send both values to the validation endpoint with your app credentials.
$payload = [
'pass_token' => $passToken,
'client_ip' => $clientIp,
];
// 3. Reject the request if validation fails.For CaptchaLa, the validation endpoint is POST https://apiv1.captcha.la/v1/validate with pass_token and client_ip in the body, plus X-App-Key and X-App-Secret headers. If you need a server-side issued challenge token instead, the issue endpoint is POST https://apiv1.captcha.la/v1/server/challenge/issue.
That sort of pattern is useful when your Hyvä project has custom forms, GraphQL-driven UI, or special checkout logic that you want to keep explicit. CaptchaLa also provides native SDKs for Web, iOS, Android, Flutter, and Electron, plus server SDKs like captchala-php and captchala-go, which can make cross-stack implementation more consistent. The loader script is https://cdn.captcha-cdn.net/captchala-loader.js, and the service includes 8 UI languages if you need localized presentation.
What to test before launch
If you are deploying Amasty Invisible Captcha on Hyvä, run a staging checklist rather than relying on a single happy-path form test. The problems that matter most often appear under real traffic patterns.
Use this order:
Test a logged-out form submit
Verify that token generation and verification work from a cold browser session.Test repeated submissions
Submit the same form twice and confirm that token reuse is handled properly.Test with JS disabled or partially blocked
Decide whether the form should submit, block, or show a fallback.Test under cached HTML
Ensure the token or challenge state is not embedded in a way that causes cross-user leakage.Test on mobile browsers
Hyvä often performs well on mobile, but any external script or event timing issue can show up there first.Test backend logging
Capture failed validation reasons so you can distinguish bot traffic from integration errors.Test localized storefronts
If your store has multiple languages, confirm the challenge copy and error messages remain understandable.
This is also where a first-party data approach can matter. Some merchants prefer to keep signal collection and verification tightly scoped to their own domain and server processes instead of depending heavily on third-party behavioral telemetry.
When to consider another route
If your current Amasty setup behaves inconsistently in Hyvä, that does not automatically mean the idea is wrong. It may simply mean the extension was built around assumptions that fit Luma better than Hyvä. In that case, you can either adapt the integration or choose a solution whose validation flow is easier to align with your frontend architecture and privacy requirements.
Where to go next: if you want to compare deployment options or review implementation details, see docs or check pricing.