If you’re looking for an alternative of captcha, the short answer is: you usually want a defense layer that verifies users with less friction, better accessibility, and stronger control over your own data. That often means moving from a one-size-fits-all challenge to a combination of risk checks, server-side validation, and adaptive step-up verification.
That doesn’t mean CAPTCHA is “bad.” It means the old pattern of forcing every visitor through the same puzzle is often a poor fit for product teams that care about conversion, accessibility, and maintainability. A modern alternative should still stop automated abuse, but do it in a way that aligns with your app’s workflow rather than interrupting it.

What makes a real alternative to CAPTCHA?
A serious alternative has to do more than “look less annoying.” It needs to meet the same security goals while improving the parts users and developers feel every day.
At a minimum, a practical replacement should:
- Reduce friction for legitimate users
- Support server-side verification
- Work across web and mobile clients
- Handle accessibility and localization cleanly
- Give you observability into abuse patterns
- Avoid excessive dependence on third-party data sharing
That last point matters more than it used to. Many teams now want first-party data only, especially when security checks are tied to signup, checkout, or account recovery flows.
A useful way to think about the space is to separate “challenge providers” from “defense systems.” Some tools simply present a widget. Others give you an API-driven workflow: issue a token, validate it on the server, and decide whether the request should proceed. That second model is usually the better alternative of captcha if you want flexibility.
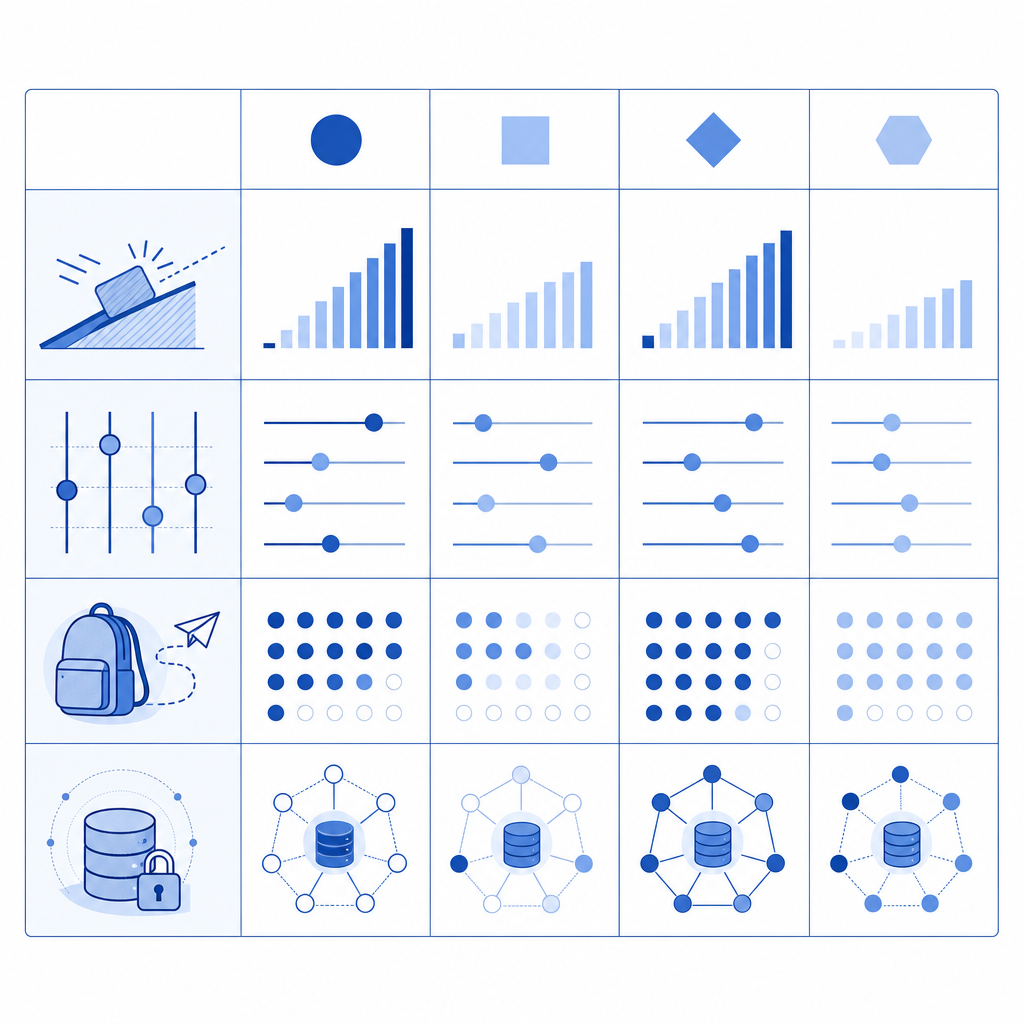
Common options and how they differ
| Option | UX friction | Server control | Mobile support | Data posture | Typical fit |
|---|---|---|---|---|---|
| reCAPTCHA | Medium | Good | Good | Depends on configuration | Broad web forms |
| hCaptcha | Medium | Good | Good | Privacy-oriented positioning | General bot defense |
| Cloudflare Turnstile | Low | Good | Limited to app architecture | Strong privacy stance | Fast web experiences |
| Custom risk engine | Low to medium | Excellent | Excellent | Fully first-party | Mature security teams |
| API-first CAPTCHA alternative | Low to medium | Excellent | Excellent | First-party only | Product teams needing control |
The right choice depends on whether your pain is mostly conversion loss, false positives, bot volume, or engineering complexity. If your team is tired of brittle front-end scripts and opaque rules, a server-verified, first-party approach is often the cleanest path.
Why teams replace old CAPTCHA flows
The main reason teams search for an alternative of captcha is not just user annoyance. It’s that old challenge flows often create hidden costs that show up everywhere else in the product.
1. Accessibility and localization
Visual puzzles can be awkward for users with disabilities, low-bandwidth connections, or assistive technologies. Even when a provider offers audio or fallback modes, the experience can still be inconsistent. If your app serves multiple regions, localization matters too. A defense layer should work in the user’s language, not force a one-language security checkpoint.
2. Conversion and abandonment
Every extra challenge is another opportunity to lose a user. This is especially visible on signup, login, and checkout pages where urgency matters. If a legitimate user is delayed by a challenge, the cost is not abstract: it’s a lost account, lead, or order.
3. Engineering complexity
Modern apps rarely live in one place anymore. You may have a web app, native iOS and Android clients, a Flutter app, and even an Electron desktop app. A defense system that only really fits one surface becomes a maintenance burden. Teams often end up building one-off workarounds instead of a consistent security flow.
4. Data and trust concerns
Many companies prefer a first-party posture for security telemetry. That means keeping the validation logic and decision-making close to their own backend. With the right APIs, you can verify a token, inspect the client IP, and apply your own policy without handing over unnecessary data.
For teams exploring CaptchaLa, this is the core design idea: challenge where needed, then validate on your own server with a simple API flow rather than relying on opaque client-side decisions.
What a modern integration can look like
A modern bot-defense flow is usually simpler than people expect. The client gets a token or challenge result, then your backend validates it and decides whether to allow the request.
Here’s a straightforward pattern:
// Client side
1. Load the challenge script from the CDN.
2. Render the verification step when needed.
3. Receive a pass token after the user succeeds.
// Server side
4. Send the pass token and client IP to the validation endpoint.
5. Check the response against your business rule.
6. Allow, rate-limit, or step up the request.The concrete API shape matters because it keeps the logic auditable. For example, a server validation request can be a POST to https://apiv1.captcha.la/v1/validate with {pass_token, client_ip} and headers like X-App-Key and X-App-Secret. If you need server-generated challenge issuance, there’s also POST https://apiv1.captcha.la/v1/server/challenge/issue.
That flow is useful across client types. CaptchaLa supports native SDKs for Web (JS/Vue/React), iOS, Android, Flutter, and Electron, plus server SDKs like captchala-php and captchala-go. It also ships in 8 UI languages, which helps when your product is international but your security flow still needs to feel local.
A deployment-minded checklist
When comparing your options, ask these technical questions:
- Can the client retrieve the challenge with minimal page weight?
- Can the backend validate the result without trusting the browser?
- Do you get a pass token that expires and is bound to a request context?
- Can you attach the client IP or other request metadata at validation time?
- Can the same model work in SPA, native, and desktop clients?
- Can you instrument failure rates and retry behavior cleanly?
If the answer to several of these is “no,” you may not have a real alternative of captcha so much as a different widget.
Comparing popular providers objectively
reCAPTCHA, hCaptcha, and Cloudflare Turnstile are all valid choices depending on your constraints. The differences are usually about tradeoffs, not absolute quality.
- reCAPTCHA is familiar and widely supported. It fits many web stacks, but some teams dislike the user friction and the way it can feel tightly coupled to Google’s ecosystem.
- hCaptcha is often chosen for privacy-oriented positioning and broad web support. It’s a common option when teams want a different vendor relationship from Google.
- Cloudflare Turnstile has a low-friction reputation and can be attractive for web-heavy properties already using Cloudflare infrastructure.
- API-first alternatives are attractive when you want more ownership over validation and policy, especially if you need the same security logic across mobile and desktop clients.
The important thing is to decide what you are optimizing for. If your objective is lowest possible interruption, a low-friction challenge may be enough. If you need uniform policy across app surfaces, more explicit validation primitives usually win.
If you want to compare plans or expected traffic volume against your own abuse profile, pricing can help frame the discussion. And if your team needs implementation details, docs is the right place to start.
Choosing the right path for your app
The best alternative of captcha is not necessarily the one with the fanciest challenge. It’s the one that fits your product’s traffic patterns, user base, and engineering model.
A sensible decision process is:
- Map the flows that are being abused: signup, login, password reset, contact forms, checkout, or scraping targets.
- Measure where friction hurts most: abandonment, false positives, or support tickets.
- Decide whether your team needs web-only support or true cross-platform coverage.
- Prefer server-side validation over “trust the browser” approaches.
- Keep the data model first-party where possible.
- Run a small rollout before replacing every challenge on day one.
For many teams, the real win is not removing verification entirely. It’s making verification invisible when risk is low and explicit when risk is high. That is a much better fit for modern applications than a universal puzzle.
If you’re evaluating CaptchaLa specifically, the free tier starts at 1000 requests per month, with Pro tiers around 50K-200K and Business at 1M. That makes it practical to test in a single high-value flow before expanding.
Where to go next
If you’re planning a migration or just comparing options, start with the docs to see the API and SDK flow, then check pricing to match the rollout to your traffic.